Table of Contents
- Executive Overview
- Why Enterprise Leaders Must Act Now
- The Business Impact of Quantum Risk
- Enterprise Readiness Snapshot
- The Enterprise Roadmap to PQC Adoption
- Key Operational Challenges for U.S. Enterprises
- Vendor and Cloud Ecosystem Readiness
- Strategic Recommendations for CISOs and Boards
- Conclusion
- References
Executive Overview
The business leaders find themselves at an important turning point for their approach to cybersecurity as the technology of post-quantum cryptography moves out of theory and into enterprise practice.
Important changes include:
According to Gartner, advancements in quantum computing may make certain asymmetric encryption technologies vulnerable to attacks within ten years. This may hasten the adoption of post-quantum cryptography by enterprises.
Deloitte Insights – Quantum Computing and Cybersecurity states that significant quantum systems could start appearing in the next five to ten years. This increases pressure on businesses to begin planning their transitions now.1
According to the McKinsey Quantum Technology Monitor 2025, quantum computing companies earned between $650 million and $750 million in 2024, and their revenues are forecasted to exceed $1 billion per year by 2025.2
NIST IR 8547 – Transition to Post-Quantum Cryptography estimated that moving to post-quantum cryptography for non-national security systems might cost more than $7.1 billion in upgrades. This highlights the large-scale changes needed in both public and private sectors. 3
NIST NCCoE – Crypto-Agility Considerations for Migrating to Post-Quantum Cryptographic Algorithms warns that attackers are already performing “harvest now, decrypt later” operations. They are collecting encrypted information today, expecting that future quantum systems may be able to decrypt sensitive data. 4
New enterprise priorities are:
– Cryptographic visibility throughout the enterprise environment
– Algorithmic flexibility and crypto-agility
– Hybrids in cryptographic implementation
– Migrations in phases
– Quantum resilience among vendors
– Preparedness for regulatory compliance
Why Enterprise Leaders Must Act Now
Post-quantum cryptography (PQC) has become a major enterprise modernisation priority following NIST’s release of finalised post-quantum cryptography standards in August 2024.
Source:5
Key Enterprise Developments
- Adversaries are already conducting “harvest now, decrypt later” attacks by collecting encrypted data today with the expectation of future quantum decryption capabilities.6
- According to the industry analysis, quantum technology related to cryptography may emerge within five to ten years, which will significantly shorten the period necessary for organizations to adopt quantum-resistant technology.7
- Quantum computing firms earned profits between $650 million and $750 million in 2024 as quantum-resistant infrastructure and cryptography agility gained momentum. 8
- The world’s most prominent tech players are scaling up their investments in hybrid cryptography, quantum-safe networks, and crypto-agility technology. For example, IBM presented its plan for constructing fault-tolerant quantum computers by 2029 9
- NIST provided ML-KEM, ML-DSA, and SLH-DSA algorithms, providing companies with practical frameworks that can withstand any quantum-powered attacks.10
Enterprise Risks
Disclosing long-term information, such as private information about health care, financial services, intellectual property, and even governmental contracts
Vulnerabilities are exposed in APIs, cloud-native applications, IoT networks, and software supply chain components.
Attacks on digital signatures, authentication schemes, and PKI implementations utilizing RSA and ECC cryptosystems
Regulatory pressure from the United States federal organizations and industry compliance guidelines
According to NIST, the draft guidelines for migration suggest that RSA- and ECC-dependent systems be gradually decommissioned starting from 2030 and further restricted by 2035.
For enterprise leaders, PQC migration is increasingly viewed as a broader business transformation initiative affecting governance, procurement, cloud strategy, software development, vendor risk management, and long-term enterprise resilience planning.
The Business Impact of Quantum Risk
The financial ramifications of delaying action are gaining importance for companies in the United States.
Sectors that require data storage for extended periods, such as banking, healthcare, aerospace, energy, defense, and government industries, have greater risks, as any confidential data that is breached will still be valuable for many years.
Business Risks Increasingly Include
Regulatory and Compliance Exposure
Federal agencies and government contractors are expected to align rapidly with NIST’s post‑quantum standards, as mandated by recent federal directives and the NIST PQC transition roadmap. 11
Brand and Customer Trust Risks
A future decryption event involving regulated or sensitive customer information could create severe reputational and legal consequences.
Operational Disruption
Many enterprises still lack centralised visibility into:
- Certificates
- Encryption libraries
- APIs
- Key management systems
- Embedded cryptography
- Legacy application dependencies
Without cryptographic visibility, enterprise-scale migration planning becomes difficult to operationalise.
Cost Escalation
A U.S. government assessment estimated that migration to post‑quantum cryptography for non‑national security systems could exceed $7.1 billion in modernisation costs between 2025 and 2035 (in 2024 dollars). 12
Industry analysis also suggests that more than 100 million businesses could adopt PQC technologies by 2035, although this would still represent only a fraction of global organisations.13
Enterprise Readiness Snapshot
|
Enterprise Priority |
Current Market Reality |
|
Cryptographic Visibility |
Limited across many large enterprises |
|
PQC Deployment Maturity |
Early-stage testing and pilots |
|
Hybrid Cryptography Adoption |
Increasing among hyperscalers |
| Regulatory Pressure |
Rapidly increasing |
| Vendor Ecosystem Readiness |
Uneven across platforms |
| Enterprise Skills Availability |
Significant shortage |
Enterprise Reality Check
Even as vendor investment in this domain is increasing rapidly, the uptake of post-quantum cryptographic measures by enterprises is still at an early stage.
Most organizations do not yet have any centralized view of their cryptographic assets, dependencies, and external risks. Therefore, any successful strategy for transition would probably focus more on governance than speed.
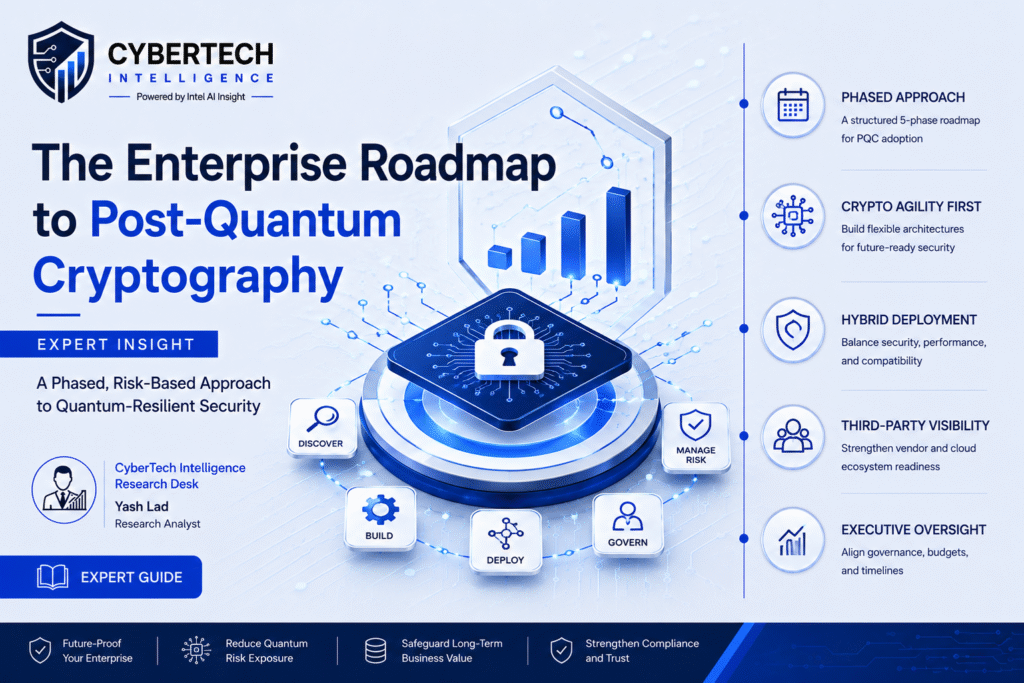
The Enterprise Roadmap to Post-Quantum Cryptography Adoption
Enterprise Roadmap for PQC Adoption
An enterprise transition to post-quantum cryptography must involve a phased and risk-based approach consistent with the infrastructure modernization process.
NIST’s NCCoE suggests that an enterprise consider its cryptography discovery capability, crypto-agility, hybrid approaches, and third-party risks before migrating to PQC.14
Phase 1: Cryptography Discovery
Enterprises should first identify:
- RSA and ECC dependencies
- TLS certificates and PKI systems
- VPNs and secure communication platforms
- Cloud-native encryption services
- Embedded cryptography in OT and IoT systems
NIST identifies cryptographic inventory visibility as the foundation of migration planning.15
Phase 2: Build Crypto-Agility
Organisations should adopt flexible architectures capable of supporting future algorithm replacement without major redesign.
Key priorities include:
- Modular cryptographic services
- Centralised key management
- Hybrid cryptographic support
- Automated policy enforcement
Phase 3: Hybrid Deployment Models
Most enterprises will initially adopt hybrid environments combining classical and Post-quantum cryptography algorithms to:
- Maintain legacy compatibility
- Reduce migration risk
- Validate performance impacts
Major cloud providers are already testing hybrid TLS and quantum-safe encryption pilots.16
Phase 4: Third-Party Risk Management
Enterprises should integrate PQC readiness into:
- Vendor risk assessments
- Procurement reviews
- Security questionnaires
- Cloud governance programs
This is especially important for organisations supporting critical infrastructure and federal contracts.
Phase 5: Governance and Executive Oversight
Post-quantum cryptography migration is now a board-level issue requiring involvement from CISOs, CIOs, legal teams, procurement leaders, and enterprise architects.
Governance priorities should include:
- Migration timelines
- Budget allocation
- Workforce readiness
- Vendor accountability
- Regulatory tracking
Rise of New Enterprises
Over the next five years, post-quantum preparedness may evolve from being purely a cybersecurity program to being a requirement in procurements and vendor governance.
Organizations that cannot demonstrate cryptographic visibility and crypto-agility may be subject to closer review in cyber-insurance reviews, government procurements, mergers and acquisitions, and third-party assessments.
Operational Challenges for U.S. Enterprises
Despite advances made in recent years, there are some major operational challenges for enterprises considering PQC implementation.
Key Operational Challenges
|
Challenge |
Enterprise Impact |
|
Legacy Infrastructure |
Difficult-to-upgrade embedded cryptography |
|
Hybrid TLS Overhead |
Increased latency and bandwidth usage |
|
Certificate Sprawl |
Limited cryptographic visibility |
| HSM Compatibility |
Potential hardware replacement costs |
| Skills Gap |
Limited internal PQC expertise |
| Vendor Maturity Variability |
Uneven support across platforms |
Enterprise Technical Realities
Post-quantum cryptography transition is not merely an encryption upgrade.
Many enterprise authentication mechanisms, APIs, certification frameworks, embedded systems, and native-cloud applications were built on the precepts of RSA and ECC, which have been around for many decades.
Replacing these dependencies may introduce:
- Interoperability challenges
- Certificate lifecycle complexity
- Hybrid TLS latency impacts
- Application compatibility risks
- Increased operational overhead across distributed enterprise environments
Recent research evaluating Kyber and Dilithium implementations indicates that hardware acceleration and cryptographic optimisation will play a major role in enterprise scalability.
Source:17
Vendor and Cloud Ecosystem Readiness
Readiness of Vendors and Cloud Ecosystem
The vendor ecosystem of the enterprise is transitioning at lightning speed towards quantum-safe technology and crypto-agile security.
IBM has publicly disclosed its progress toward realizing fault-tolerant quantum computing by 2029 and further pursuing quantum-resistant cryptography implementations and hybrid systems.18
Major cloud providers have started integrating quantum-resistant experiments into their cloud native security infrastructure, hybrid TLS, and crypto-agile architectures.
Enterprise Investment Focus Areas
- Hybrid TLS implementations
- Quantum-safe key exchange pilots
- Crypto-agile cloud services
- Secure software-signing modernisation
- Quantum risk assessment tooling
Cybersecurity vendors are also expanding investments into:
- Crypto-discovery platforms
- PQC-enabled VPN architectures
- Identity modernisation
- Hybrid certificate management
Industry analysis suggests the global quantum‑computing market could grow at more than 20% annually through 2030. 19
Recommendations for CISOs and Boards
Here are the priorities for enterprise executives to focus on in the next 12-24 months.
- Start Quantum Readiness Assessment
Conduct a risk assessment regarding cryptographic exposure of infrastructure, applications, cloud environments, and third-party ecosystems.
- Invest in Crypto-Agility
Ensure architectural agility instead of point algorithm replacements.
- Embed PQC in Enterprise Risk Management
Make quantum risks an integral part of cyber-resilience and long-term strategic plans.
- Ensure Vendor Readiness for Post-quantum cryptography
Embed quantum-safety into contract requirements for vendors.
- Create Long-Term Migration Roadmap
Develop phased implementation roadmaps as part of infrastructure and digital transformation initiatives.
Conclusion
Implementing post-quantum cryptography appears to be the most significant cybersecurity initiative of the upcoming decade.
While implementing post-quantum cryptography, US companies face a lot more aspects than mere algorithm replacements in their efforts.
Based on finalised standards from NIST, vendor adoption and enterprise investments, the transition process has been initiated already20
The key challenges for CISOs, CIOs, and board members at the moment are not related to full cryptographic replacements, but to developing the necessary capabilities of:
- Cryptographic visibility
- Crypto-agility
- Vendor accountability
- Phased migration roadmap
References
- Deloitte Insights – Quantum Computing and Cybersecurity (2025)
- McKinsey & Company – Quantum Technology Monitor 2025
- NIST IR 8547 – Transition to Post-Quantum Cryptography
- NIST NCCoE – Crypto-Agility Considerations for Migrating to Post-Quantum Cryptographic Algorithms
- NIST – First Finalized Post-Quantum Encryption Standards (August 2024)
- NIST NCCoE – PQC Migration and Harvest Now Decrypt Later Guidance
- Deloitte Insights – Quantum Threat Timeline Analysis
- McKinsey Quantum Technology Monitor – Market Revenue Forecasts
- IBM Quantum Roadmap 2029
- NIST PQC Algorithms – ML-KEM, ML-DSA, and SLH-DSA Standards
- NIST IR 8547 – Federal PQC Transition Roadmap
- PostQuantum– Post-Quantum Cryptography (PQC) Regulatory Framework in 2026
- Juniper Research – Post-quantum Cryptography (PQC)
- NIST NCCoE – Enterprise PQC Migration Guidance
- NIST NCCoE – Cryptographic Inventory and Discovery Guidance
- AWS Security Blog – Hybrid Post-Quantum TLS Guidance
- arXiv – Research on Kyber and Dilithium Scalability Optimisation
- IBM – Quantum Computing and Quantum-Safe Roadmap
- McKinsey – The Rise of Quantum Computing
- NIST – Finalized PQC Standards Announcement
🔒 Login or Register to continue reading