With the revolution of quantum computing technologies, conventional cryptographic techniques like Rivest-Shamir-Adleman (RSA) and Elliptic Curve Cryptography (ECC) are anticipated to be less secure than before.
RSA is a foundational, asymmetric public-key cryptography algorithm used to securely transmit data. Whereas ECC is a technique offering high security with smaller key sizes compared to RSA.
PQC (Post-Quantum Cryptography) readiness refers to the capacity of an organization to ensure that its data is safe from future attacks using quantum computing through the adoption of quantum-proof algorithms.
With NIST developing standards (FIPS 203, 204, 205), and regulatory bodies requiring compliance by 2030 to 2035, action needs to start. Right away.
Why the Market Is Paying Attention Now
Over the last 24 months, quantum readiness has shifted from research labs into enterprise strategy conversations.
The projected market value for PQC is expected to range from $2.4 billion to $3.4 billion before plateauing. 1
Organizations are beginning to realize that migrating cryptography is not a quick software patch. It is a multi-year transformation effort involving applications, vendors, cloud providers, hardware systems, and identity infrastructure.
Large enterprises are now investing in cryptographic discovery programs because many do not fully understand where encryption exists across their own ecosystems.
Source: Palo Alto Networks
For CISOs, this is no longer just a technical cryptography discussion. It is becoming a long-term resilience issue tied directly to operational continuity, compliance, customer trust, and data survivability.
Trend 1. Cryptographic Visibility Is Poor
One of the biggest enterprise challenges is simply identifying where vulnerable cryptography exists.
- Large organizations may manage more than 20,000 active certificates and encryption keys.
- Enterprise applications often contain embedded cryptographic libraries that have not been updated in years.
- Cloud migration has significantly increased cryptographic complexity and sprawl.
For many organizations, the first phase of PQC readiness is not migration. It is discovery.
Trend 2. “Harvest Now, Decrypt Later” is Driving Urgency
Security leaders are increasingly concerned about threat actors stealing encrypted information today to decrypt it in the future once quantum capabilities mature.
This is especially concerning for industries handling long-retention data.
- Healthcare records can retain intelligence value for more than 20 years.
- Intellectual property in aerospace, defense, and pharmaceuticals may remain valuable for decades.
- Government archives and classified communications represent long-term intelligence targets.
- Ransomware operators are increasingly targeting backup repositories and long-term storage systems.
For organizations managing sensitive customer or national-security-related data, waiting for quantum systems to fully mature may already be too late.
Case Example: Cloudflare’s Post-Quantum TLS Rollout
The Cloudflare post-quantum cryptography (PQC) initiative aims at ensuring that traffic on the internet will be safe from any attacks by cybercriminals through quantum computing by employing quantum-resistant encryption on its platforms.
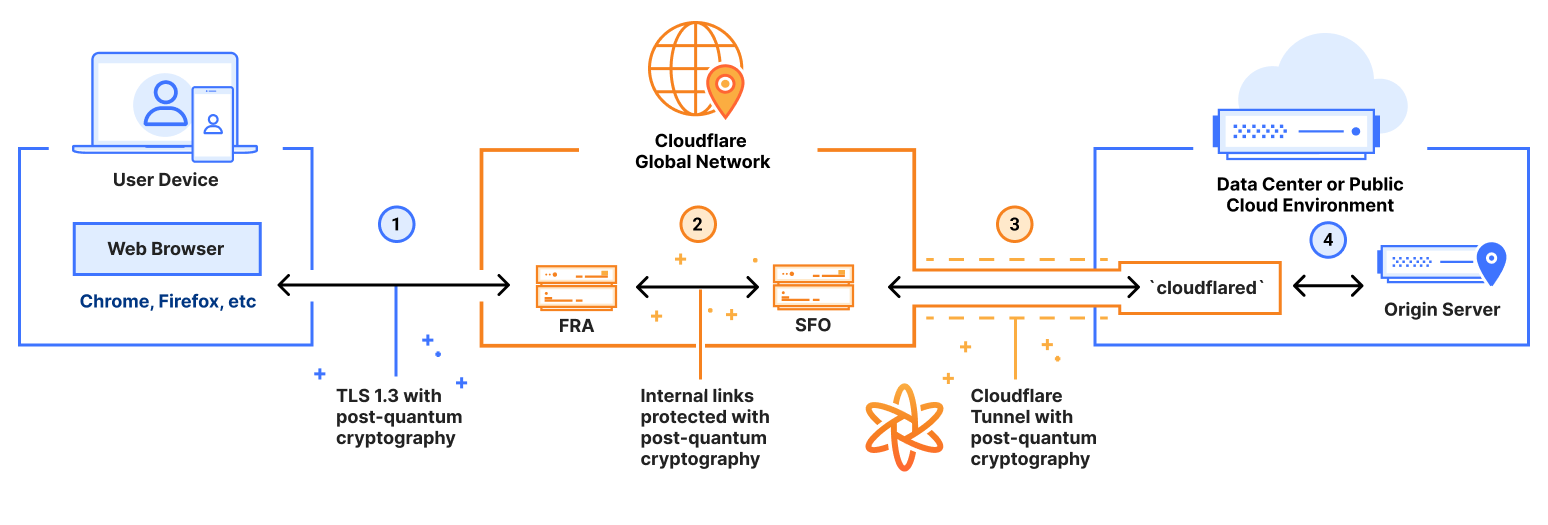
Source: Cloudflare
Cloudflare has been developing PQC and aims at attaining post-quantum security by 2029 on all its platforms.
The firm has incorporated post-quantum cryptography to secure key agreements in TLS 1.3.
The technology enables the Cloudflare network to counter the “harvest now, decrypt later” attacks in which the hackers use quantum computing powers in the future to decrypt data that was captured when quantum computing was not yet available.
It is worth noting that Cloudflare uses post-quantum cryptography on over one-third of human traffic on its network.
Which Industries Are Moving First?
Not every sector faces the same level of urgency. Industries with long data-retention cycles and strict regulatory requirements are moving faster than others.
However, telecom companies are anticipated to experience the greatest rise in market share for quantum communications, predicted to rise from 16% to 26% in 2035. 2
Financial Services
Banks rely heavily on public-key cryptography for secure transactions, payment processing, authentication, and digital trust.
- Global financial institutions process billions of encrypted transactions every day.
- Banking environments often contain decades-old legacy systems with hardcoded cryptographic dependencies.
- Financial regulators are increasingly discussing quantum-safe preparedness frameworks.
- Major U.S. financial institutions have already launched internal PQC testing programs.
For banks, the concern is not just future decryption risk. It is the operational challenge of modernizing massive interconnected infrastructures.
Healthcare
Healthcare organizations face a difficult combination of sensitive patient data, aging infrastructure, and expanding IoT ecosystems.
- Healthcare remained one of the most targeted ransomware sectors globally in 2025.
- Medical records contain personally identifiable and insurance-related information with long-term value.
- Many medical devices were not designed for rapid cryptographic upgrades.
- Hospital networks often operate with fragmented security visibility across vendors and systems.
Healthcare CISOs increasingly view PQC readiness as part of broader cyber resilience planning.
Government and Defense
Federal agencies and defense contractors are among the earliest adopters of quantum-safe planning initiatives.
- National security communications represent high-value targets for future quantum decryption.
- Government agencies are aligning with the emerging NIST PQC migration guidance.
- Defense ecosystems rely heavily on long-lifecycle infrastructure and encrypted communications.
- Supply chain dependencies significantly complicate migration timelines.
Why This Matters to CISOs and Security Leaders
Many organizations still assume PQC migration is a future compliance project. In reality, the challenge is operational.
Modern enterprises run thousands of applications, APIs, cloud workloads, identities, certificates, and third-party integrations that rely on cryptography. Replacing vulnerable algorithms across those environments may take years.
Enterprise Risks CISOs Cannot Ignore
Legacy Infrastructure
Older systems often cannot support modern cryptographic standards without redesign.
Vendor Fragmentation
Third-party vendors may adopt quantum-safe standards at different speeds.
Cloud Complexity
Hybrid and multi-cloud environments increase cryptographic visibility gaps.
Compliance Pressure
Regulatory expectations around quantum readiness are evolving rapidly.
Source: Palo Alto Networks
- 60% or more enterprise applications may contain embedded cryptographic dependencies. 3
- Large enterprises often rely on hundreds of third-party software providers.
- Identity systems remain one of the highest-risk migration areas.
- Cryptographic modernization costs may rise significantly for organizations delaying preparation.
Security leaders are beginning to realize that crypto-agility, the ability to quickly replace cryptographic standards, may become as important as vulnerability management over the next decade.
Cyber Tech Intelligence Analysis

Cyber Tech Intelligence assesses that organizations approaching PQC solely as an encryption replacement project are underestimating the scale of the challenge.
The larger issue is resilience. Enterprises need visibility into where cryptography exists, how quickly systems can adapt, and which business operations depend on vulnerable algorithms.
Cyber Tech Intelligence Analysis Framework
Cyber Tech Intelligence identifies five operational areas enterprises should prioritize.
1. Cryptographic Discovery
Identify where cryptographic mechanisms operate across applications, devices, APIs, and cloud workloads.
2. Data Longevity Mapping
Determine which datasets remain valuable long enough to face future decryption risk.
3. Migration Complexity Assessment
Evaluate operational barriers tied to legacy systems and third-party environments.
4. Quantum Threat Exposure Analysis
Assess exposure to “harvest now, decrypt later” collection strategies.
5. Crypto-Agility Readiness
Measure how quickly the organization can transition to cryptographic standards without disruption.
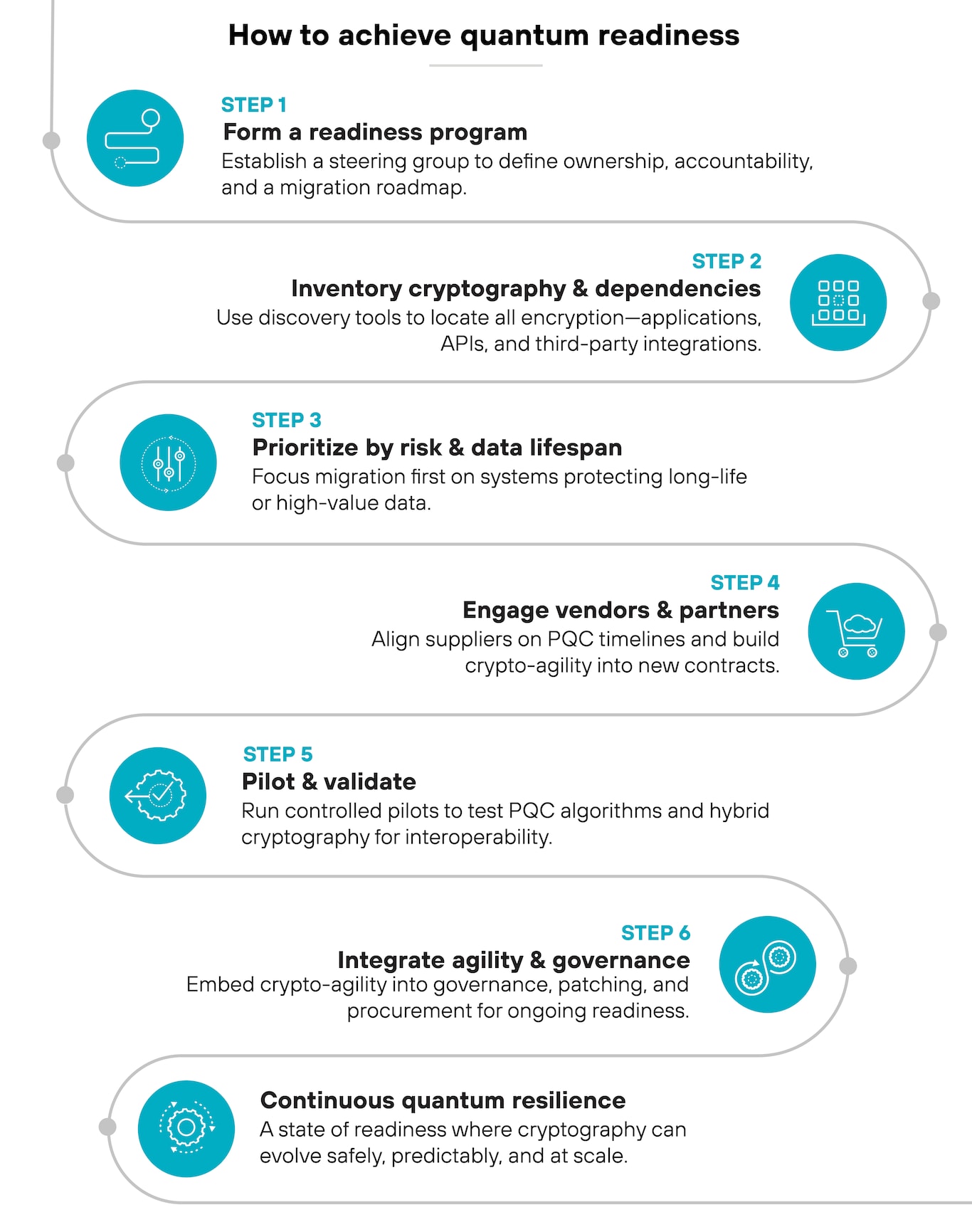
What Enterprises Should Do Next
Organizations do not need to replace all encryption immediately. But they do need to begin preparing now.
Immediate Priorities
Build a Cryptographic Inventory
Understand where encryption exists across systems and environments.
Prioritize High-Risk Data
Focus first on sensitive long-lifecycle information.
Evaluate Vendor Readiness
Assess whether suppliers support emerging PQC standards.
Improve Crypto-Agility
Design systems that can transition cryptographic algorithms more efficiently.
Launch Controlled PQC Pilots
Test interoperability before large-scale deployment begins.
Conclusion
PQC readiness is quickly becoming one of the most important long-term cybersecurity initiatives facing enterprises today.
The enterprises most likely to succeed will not necessarily be the first to deploy post-quantum cryptography. They will be the organizations that start building visibility, crypto-agility, and migration governance early.
Cyber Tech Intelligence research indicates that the organizations most prepared for the quantum transition will not necessarily be those deploying PQC algorithms first, but those establishing crypto-agility, governance maturity, and enterprise-wide cryptographic visibility early.
As quantum computing capabilities continue to evolve, PQC readiness is becoming a foundational requirement for sustaining long-term cyber resilience, protecting high-value data assets, and preserving operational trust across regulated and mission-critical sectors.
FAQs
1. Is quantum computing an immediate threat to enterprise security?
Not immediately for most organizations. However, enterprises storing sensitive long-term data should begin preparing now because migration programs may take several years.
2. Which sectors face the highest urgency?
Financial services, healthcare, defense, telecommunications, and critical infrastructure sectors currently face the greatest pressure because of data longevity and regulatory exposure.
3. Will PQC replace all current encryption systems?
No. Most organizations will operate hybrid cryptographic environments during transition periods while gradually replacing vulnerable algorithms.
4. What is the biggest challenge in PQC migration?
Visibility. Many enterprises do not fully understand where cryptography exists across applications, devices, cloud platforms, and vendor ecosystems.
5. What should CISOs prioritize first?
Security leaders should begin with cryptographic discovery and crypto-agility planning before attempting full-scale migration initiatives.
References
- McKinsey & Company. Quantum Technology Monitor. (Accessed: 11 May 2026).
- Obsidian Security. Security for AI Agents: Protecting Intelligent Systems in 2025. (2025) Obsidian Security, 23 October. Available at: https://www.obsidiansecurity.com/blog/security-for-ai-agents (Accessed: 11 May 2026).
🔒 Login or Register to continue reading