Executive Summary
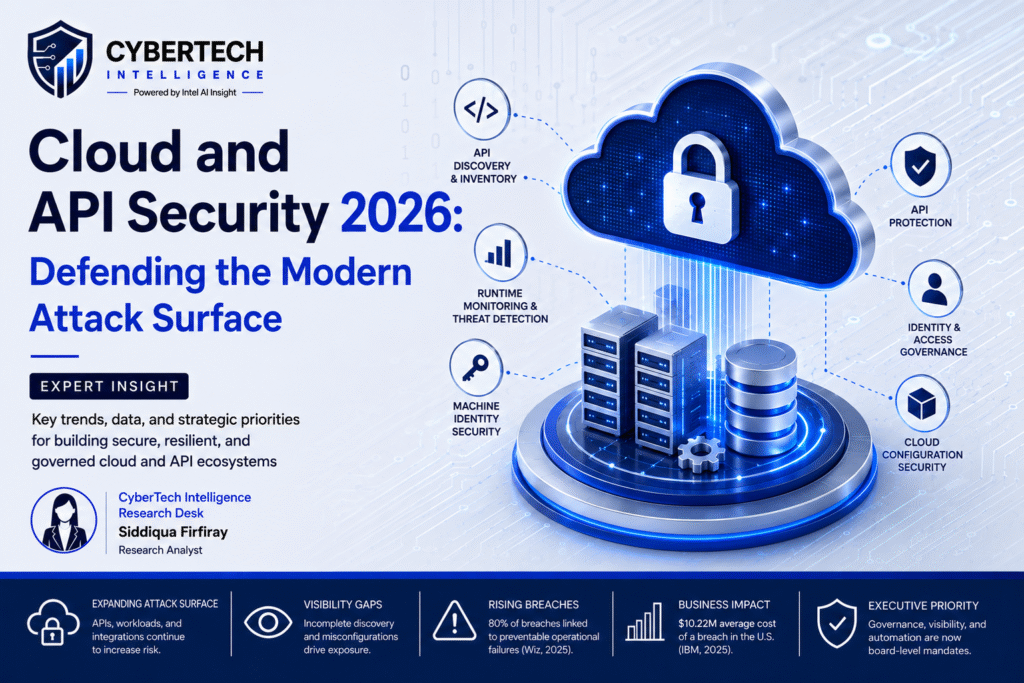
Cloud architectures in the enterprise setting have become highly distributed, API-powered, and intricate to operate. Enterprises today run hybrid combinations of public clouds, private clouds, SaaS networks, Kubernetes stacks, AI-powered services, and third-party integrations, where information is exchanged consistently via APIs and machine identities.
Such rapid evolution has drastically transformed the contemporary attack surface. APIs are now fundamental to digital business processes that help integrate cloud native applications, artificial intelligence, customer support, DevOps processes, and data streams within enterprises.
Recent Deloitte research forecasts that more than 50% of enterprise workloads will operate across private or sovereign cloud environments by 2028 as organizations pursue resilience, compliance, and operational control. 1
At the same time, Gartner notes that APIs now represent the majority of dynamic internet traffic, significantly increasing exposure to authorization abuse, runtime attacks, credential compromise, and third-party integration risk. 2
Conventional perimeter-focused security approaches are becoming increasingly obsolete in such scenarios since runtime exposure varies constantly.
APIs are launched more rapidly than governance teams can catalog them, machine identities abound within workloads, and AI-powered services create fresh forms of autonomous risks.
The following represents today’s priority for CISOs, cloud architects, and API platform administrators:
- continuous runtime visibility
- API governance modernization
- machine identity security
- telemetry-driven detection
- zero-trust enforcement
- AI-aware operational resilience
Organizations that advance their capabilities for runtime discovery, governance orchestration, and cloud-native security operations will be more adept at mitigating unmanaged risk exposure, shortening detection times, and becoming resilient to automated attacks.
By the Numbers
| Key Metric | Industry Insight |
| 50%+ | Enterprise workloads expected to operate across private or sovereign cloud environments by 2028 |
| Majority | Share of dynamic internet traffic now represented by APIs |
| 57% | Employees using personal generative AI accounts for work-related activities |
| 33% | Employees entering sensitive data into unapproved AI tools |
| 42% | Reduction in policy drift achieved through governance-aware API orchestration |
| 500:1 | Potential machine-to-human identity ratio in enterprise ecosystems |
Sources: As per references shown above, Cyber Tech Intelligence Analysis
Visibility and Runtime Intelligence
Visibility continues to be one of the most important operational needs in contemporary cloud and API ecosystems.
It is often difficult for security teams to ensure proper visibility into:
- exposed APIs
- active integrations
- machine identities
- cloud workloads
- AI-driven services
- third-party access paths
The problem of insufficient visibility grows even more acute in scenarios where deployment speed outstrips governance.
Emerging Trends in Enterprise Security
Security approaches are rapidly moving toward continuous visibility, runtime telemetry, and intelligence-driven governance models.
Traditional perimeter-based security models are proving to be inadequate in dynamic ecosystems that involve APIs, workloads, AI services, and machine identities.
Among other security priorities, today’s decision makers are:
- runtime visibility
- telemetry correlation
- zero trust enforcement
- behavioral analysis
- AI governance
- resilience metrics
Enterprise Cloud Security Trends
| Trend Area | Enterprise Impact |
| API-First Architectures | Increased integration exposure |
| AI-Driven Automation | Expanded runtime complexity |
| Multi-Cloud Operations | Fragmented governance |
| Machine Identity Growth | Credential-management pressure |
| Zero Trust Adoption | Continuous verification models |
| Runtime Monitoring Expansion | Faster anomaly detection |
According to Gartner’s study into cybersecurity trends, more and more enterprises are worried about their operational risks due to AI and unregulated data sharing with external systems.
The adoption of cloud-native technologies requires increasingly flexible security approaches that go beyond mere static control models.
Executive Security Challenges
The current cloud/API environment brings about operational risks that go beyond the realm of security for infrastructure.
The coming together of APIs, AI, machine identity, and software delivery has brought about new governance issues that organizations are not yet able to cope with.
Enterprise Security Risk Landscape
| Security Challenge | Business Impact | Operational Consequence |
| API Sprawl | Unmanaged exposure | Incomplete inventories |
| Hybrid Cloud Fragmentation | Governance inconsistency | Visibility gaps |
| Machine Identity Growth | Credential abuse risk | Authentication complexity |
| AI Integration Expansion | Sensitive-data exposure | Runtime uncertainty |
| Third-Party API Dependencies | Supply-chain exposure | Reduced governance control |
| Decentralized Development | Inconsistent enforcement | Configuration drift |
Security leaders increasingly recognize that visibility gaps represent one of the most significant operational risks in modern environments. APIs deployed temporarily for testing frequently remain active in production. Third-party integrations bypass centralized governance. Machine identities accumulate faster than organizations can govern them.
The result is a continuously evolving attack surface where security teams often lack accurate runtime awareness of:
- exposed APIs
- active machine identities
- external integrations
- cloud workloads
- AI-driven data exchanges
- shadow services
Cyber Tech Intelligence positions cloud and API security as a data-backed operational resilience challenge requiring continuous visibility, governance modernization, and runtime intelligence rather than isolated infrastructure protection.
1. The Modern Attack Surface
Enterprise cloud transformation has accelerated rapidly over the last several years. Organizations now operate across increasingly distributed ecosystems composed of:
- public cloud infrastructure
- private cloud environments
- SaaS platforms
- Kubernetes deployments
- AI orchestration services
- edge infrastructure
- third-party APIs
While these architectures improve agility and scalability, they also expand operational complexity significantly.
Deloitte research forecasts that more than half of enterprise workloads will run within private or sovereign cloud environments by 2028 as organizations attempt to improve resilience and regulatory alignment. 3
At the same time, APIs have become foundational to modern digital operations. APIs now connect customer applications, cloud-native workloads, AI systems, mobile services, DevOps pipelines, and enterprise automation workflows.
Gartner’s API protection guidance states that APIs now account for the majority of dynamic internet traffic, dramatically increasing dependency on API ecosystems. 4
Identity growth is compounding this challenge. Machine identities such as service accounts, certificates, API keys, and tokens increasingly outnumber human identities across enterprise environments.
Industry analysis suggests machine identities may outnumber human users by ratios approaching 500:1 in some enterprise ecosystems. 5
Key Drivers Expanding the Attack Surface
| Attack Surface Driver | Operational Challenge | Security Risk |
| Hybrid Cloud Adoption | Distributed governance | Visibility fragmentation |
| API Proliferation | Inventory complexity | Shadow APIs |
| AI Services | Autonomous integrations | Data leakage |
| Machine Identity Growth | Credential management | Unauthorized access |
| SaaS Expansion | External dependencies | Third-party compromise |
| DevOps Velocity | Rapid deployments | Governance lag |
AI adoption has further accelerated operational risk. Gartner’s 2026 cybersecurity trends research found that 57% of employees used personal generative AI accounts for work-related activities, while 33% admitted to entering sensitive information into unapproved tools. 6
This fusion of cloud-native infrastructure, APIs, AI services, and machine identities has radically shifted how organizations need to think about their security operations.
Key Takeaways
- APIs now represent a primary enterprise attack surface
- Runtime exposure changes continuously across cloud-native environments
- Machine identity governance is becoming increasingly critical
- AI integrations are introducing new operational visibility gaps
2. Why API Sprawl and Multi-Cloud Complexity Matter
API sprawl has emerged as one of the defining operational security challenges of modern enterprise environments.
The adoption of APIs is taking place at a much quicker pace than that of governance frameworks in corporate environments within internal systems, client software, SaaS integration, artificial intelligence processes, mobile apps, and automation services.
A major contributor to this challenge is decentralized deployment. APIs are often created independently by development teams, platform engineers, third-party vendors, and business units without centralized ownership or inventory management.
Over time, enterprises accumulate:
- shadow APIs
- deprecated endpoints
- duplicate services
- unmanaged integrations
- orphaned development environments
- unsecured webhooks
These assets frequently remain exposed in production environments long after projects conclude.
API Sprawl Risk Categories
| Risk Area | Example Exposure | Business Consequence |
| Shadow APIs | Undocumented endpoints | Unauthorized access |
| Zombie APIs | Deprecated active services | Unpatched vulnerabilities |
| Third-Party Integrations | External webhook exposure | Supply-chain compromise |
| Policy Drift | Inconsistent enforcement | Security gaps |
| CI/CD Expansion | Rapid deployment growth | Governance delays |
Gartner’s API protection guidance emphasizes that APIs now constitute the majority of dynamic internet traffic, increasing operational dependency on API ecosystems while expanding exposure risk. 7
Visibility gaps become especially dangerous because organizations cannot protect assets they cannot identify. Runtime exposure frequently changes faster than traditional inventory-management processes can track.
Distributed multi-cloud environments intensify these problems further.
Multi-Cloud Operational Challenges
| Operational Area | Security Impact | Common Outcome |
| Identity Management | Inconsistent access policies | Privilege escalation risk |
| Logging & Telemetry | Fragmented monitoring | Delayed investigations |
| Policy Enforcement | Configuration drift | Visibility gaps |
| Kubernetes Visibility | Ephemeral workloads | Runtime blind spots |
| Third-Party APIs | External dependencies | Reduced governance control |
Machine identities create additional operational complexity. API keys, service accounts, certificates, and OAuth tokens continuously authenticate workloads and integrations across environments.
Industry analysis suggests only 12% of organizations have implemented fully automated lifecycle management for machine identities despite their rapidly expanding footprint. 8
Recent governance-aware API gateway research demonstrated measurable operational improvements, including a 42% reduction in policy drift and a 31% improvement in configuration synchronization compared to manual governance approaches. 9
According to Cyber Tech Intelligence, the issue of API sprawl is a visibility and governance challenge. Companies need continuous discovery, telemetry, and centralized policy orchestration to decrease their exposure.
Cyber Tech Intelligence Analysis
The development of native cloud architecture, API-based ecosystems, and AI-powered services is changing the nature of enterprise security operations. Traditional APIs are no longer auxiliary tools used for integration.
They have become the core component of the modern digital environment, integrating various workloads, applications, machine identities, third-party systems, and self-governing services across highly distributed infrastructure.
Many companies still use security governance structures and architectures that are designed for static environments in their dynamic runtime-based ecosystems.
The Cyber Tech Intelligence analysis reveals that multiple trends are leading to growing operational exposure at the same time:
- API proliferation
- multi-cloud and hybrid ecosystem expansion
- increasing machine identities
- decentralized software deployment
- automations powered by AI
- integration with third parties
Quality Assurance and Governance Framework
Efficient cloud and API security strategies call for validation procedures that will guarantee proper governance, accurate runtime visibility, and resiliency in any distributed environment.
Given the continuous transformation of APIs, machine identities, artificial intelligence, and cloud-based workloads, modern businesses require a well-established quality assurance strategy to ensure integration of security and governance policies and compliance with regulatory requirements.
Where constant changes in runtime happen on a regular basis, periodic review is no longer enough. Instead, enterprises must introduce quality assurance practices that will allow validating the efficiency of security controls in near-real time.
Cyber Tech Intelligence recommends using a governance-oriented quality assurance framework that includes:
- runtime visibility validation
- accurate API inventory management
- governance of machine identities
- consistent telemetry
- integrity of policy enforcement
- continuous compliance checking
Enterprise Security QA Framework
| QA Domain | Validation Objective | Operational Outcome |
| API Discovery Validation | Confirm inventory accuracy | Reduced unmanaged exposure |
| Runtime Telemetry QA | Validate monitoring consistency | Improved operational visibility |
| Identity Governance QA | Audit credential lifecycle controls | Reduced unauthorized access |
| Policy Enforcement QA | Detect governance drift | Improved configuration consistency |
| AI Governance QA | Validate autonomous-system oversight | Reduced AI-related exposure |
| Incident Readiness QA | Assess response maturity | Faster remediation timelines |
Contemporary QA practices continue to adopt automation-driven validation through:
- CI/CD pipelines
- runtime monitoring platforms
- cloud-security solutions
- API gateways
- SIEM environments
- identity-security solutions
- AI governance controls
This will allow companies to spot their operational weaknesses early on while enhancing consistency in their governance efforts.
Continuous Security Validation Model
| Validation Area | Continuous QA Capability |
| API Exposure | Runtime inventory reconciliation |
| Cloud Configurations | Automated drift detection |
| Machine Identities | Credential lifecycle auditing |
| Runtime Activity | Behavioral anomaly validation |
| Third-Party Integrations | Access governance verification |
| Compliance Controls | Continuous evidence collection |
Companies are beginning to see the need for dynamic security governance in today’s world of continuous API evolution, workload development, and integration.
Hence, continuous validation through QA is critical to ensuring operational resilience.
Cyber Tech Intelligence recommends adopting a QA approach that is synchronized with operational KPIs, including:
- API inventory accuracy
- runtime visibility coverage
- policy drift rate
- credential rotation compliance
- mean time to detect
- mean time to remediate
QA Maturity Benchmark Model
| Maturity Level | Operational Characteristics |
| Reactive QA | Manual audits and periodic reviews |
| Transitional QA | Partial automation and telemetry integration |
| Operational QA | Continuous runtime validation |
| Adaptive QA | AI-assisted governance and anomaly detection |
| Resilient QA | Autonomous policy orchestration and remediation |
With continued growth in cloud-native ecosystems, companies that have the ability to continuously ensure quality and validate governance will be well-suited to enhance their resilience capabilities, improve their preparedness for detection, and minimize operational exposure.
About Cyber Tech Intelligence
Cyber Tech Intelligence provides cybersecurity intelligence solutions, cloud security services, and operational resilience consulting for enterprise security leaders.
Cyber Tech Intelligence specializes in the provision of cybersecurity intelligence, cloud security, and operational resilience services through:
- cloud security modernization
- maturity of API governance
- visibility in cyber risks
- operations in runtime security
- readiness in artificial intelligence security
- decision-making in executive cybersecurity
Cyber Tech Intelligence utilizes:
- research in cybersecurity
- threat intelligence analysis
- benchmarking in governance
- visibility in runtime
- operational risks assessment
Core Intelligence Areas
| Intelligence Focus | Strategic Outcome |
| API Security Intelligence | Reduced unmanaged exposure |
| Cloud Risk Visibility | Improved operational awareness |
| Governance Benchmarking | Security maturity alignment |
| Runtime Threat Intelligence | Faster detection readiness |
| AI Security Analysis | Improved autonomous-system oversight |
| Executive Security Reporting | Better strategic decision-making |
Strategic Priorities for Security Transformation
Companies undergoing cloud and API security transformation realize more and more that their security infrastructure needs improvement due to its reliance on the outdated concept of perimeters.
With an increase in complexity related to APIs, machine identities, AI tools, cloud resources, and integration with other third parties, it is crucial to prioritize approaches that enable constant adaptation to runtime environments.
Cyber Tech Intelligence suggests that organizations concentrate on a number of strategic priorities within their modernization programs.
Enterprise Security Transformation Priorities
| Strategic Priority | Security Objective | Operational Outcome |
| Continuous Runtime Visibility | Improve operational awareness | Reduced unmanaged exposure |
| API Governance Modernization | Standardize policy enforcement | Improved governance consistency |
| Machine Identity Security | Strengthen credential governance | Reduced unauthorized access |
| Behavioral Analytics | Improve anomaly detection | Faster threat identification |
| Zero Trust Enforcement | Reduce implicit trust | Lower lateral movement risk |
| AI Governance Integration | Govern autonomous systems | Improved AI-risk visibility |
The need for organizations to have visibility that can correlate APIs, workloads, identities, telemetry streams, cloud infrastructure, AI services and third-party integrations is growing more critical each day for ensuring consistent governance and preventing disjointed security operations.
Security Modernization Outcomes
| Operational Capability | Business Value |
| Unified Runtime Monitoring | Improved threat detection |
| Automated Governance | Reduced configuration drift |
| Continuous Discovery | Stronger attack-surface visibility |
| Identity Lifecycle Management | Lower credential-abuse risk |
| Telemetry Correlation | Faster investigation workflows |
| Adaptive Security Operations | Improved cyber resilience |
The Cyber Tech Intelligence analysis suggests that organizations able to implement continuous visibility and governance alignment are more likely to enhance their resilience to ever-growing threats involving automation and artificial intelligence.
Future Projections for Cloud and API Security
Cloud-based ecosystems will undergo further rapid development as companies continue to adopt artificial intelligence, automate processes, and depend more on APIs as basic infrastructure.
This will speed up some key cybersecurity developments, such as:
- increased machine identities
- autonomous system interactions
- artificial intelligence-led runtime
- decentralized application structure
- integration dependency on third parties
- increasing telemetry complexities
Given the highly dynamic nature of these ecosystems, it will be necessary for security operations to operate consistently without interruptions.
Accenture’s cybersecurity analysis highlights that adversaries are already using AI-enabled tooling to compress attack timelines significantly, increasing pressure on enterprise security operations to respond at machine speed. 10
Future-proof security solutions would need to leverage:
- run-time discovery of threats
- governance models that adapt
- operations driven by telemetry
- AI-based detection of threats
- orchestration of policies through automation
- security awareness of clouds and APIs
The view at Cyber Tech Intelligence is that companies would fare much better by implementing modern security operations with a foundation of continuous visibility and intelligence-driven governance and resilience.
References
- Deloitte Sovereign Cloud
Deloitte. (2026) Sovereign Cloud | Deloitte, ServiceNow, and STACKIT. Available at: https://www.deloitte.com/global/en/alliances/servicenow/about/sovereign-cloud.html - Gartner Market Guide for API Protection
Gartner. (2025) Market Guide for API Protection. Published 28 August 2025. Available at: https://www.gartner.com/en/documents/6893766 - Deloitte Sovereign Cloud
Deloitte. (2026) Sovereign Cloud | Deloitte, ServiceNow, and STACKIT. Available at: https://www.deloitte.com/global/en/alliances/servicenow/about/sovereign-cloud.html - Gartner Market Guide for API Protection
Gartner. (2025) Market Guide for API Protection. Published 28 August 2025. Available at: https://www.gartner.com/en/documents/6893766 - ITPro Machine Identities Analysis
ITPro. (2026) How Machine Identities Are Changing Cyber Defense. Available at: https://www.itpro.com/security/how-machine-identities-changing-cyber-defense - Gartner Top Cybersecurity Trends for 2026
Gartner. (2026) Gartner Identifies the Top Cybersecurity Trends for 2026. Published 5 February 2026. Available at: https://www.gartner.com/en/newsroom/press-releases/2026-02-05-gartner-identifies-the-top-cybersecurity-trends-for-2026 - Gartner Market Guide for API Protection
Gartner. (2025) Market Guide for API Protection. Published 28 August 2025. Available at: https://www.gartner.com/en/documents/6893766 - ITPro Machine Identities Analysis
ITPro. (2026) How Machine Identities Are Changing Cyber Defense. Available at: https://www.itpro.com/security/how-machine-identities-changing-cyber-defense - ArXiv Secure and Governed API Gateway Architectures
Punniyamoorthy, V., Kannan, K., Deshpande, A., Butra, L., Agarwal, A.K., Parthasarathy, A., Malempati, S. and Kumar, B. (2025) Secure and Governed API Gateway Architectures for Multi-Cluster Cloud Environments. arXiv. Available at: https://arxiv.org/abs/2512.23774 - Accenture AI-Driven Cybersecurity Operations
Accenture. (2026) Accenture and Anthropic Team to Help Organizations Secure, Scale AI-Driven Cybersecurity Operations. Available at: https://newsroom.accenture.com/news/2026/accenture-and-anthropic-team-to-help-organizations-secure-scale-ai-driven-cybersecurity-operations
🔒 Login or Register to continue reading