In the NFL, elite defenses don’t rely on brute strength alone. They read formations, anticipate plays, and adjust in real time. The game is won through awareness, coordination, and speed of response.
Enterprise cloud environments are facing a similar shift.
Traditional security models were built for a static field. Defined perimeters, predictable traffic, controlled endpoints.
However, today’s cloud ecosystems are fluid. Workloads spin up and down in seconds. Identities move across systems. Data flows far beyond what legacy architectures were designed to track.
What worked as a strong defense even a few years ago now struggles to keep pace.
The US Cloud Reality: Scale Has Outgrown the Security Model
Cloud migration in the United States has seen significant momentum and even fragmentation at times.
As reported by Gartner, around 85% of businesses are embracing cloud first, yet less than 50% can afford a robust security framework for this purpose.
“There is no business strategy without a cloud strategy,” said Milind Govekar, distinguished vice president at Gartner.
“The adoption and interest in public cloud continues unabated as organizations pursue a “cloud first” policy for onboarding new workloads. Cloud has enabled new digital experiences such as mobile payment systems where banks have invested in startups, energy companies using cloud to improve their customers’ retail experiences or car companies launching new personalization services for customer’s safety and infotainment.”
Additionally, according to IBM Security, the average cost of a data breach in the United States has reached $9.48 million, which is the largest sum globally.
Why?
- Rapid multi-cloud adoption without consistent governance.
- Heavy dependency on old perimeter defense systems.
- Misconfigurations in dynamic cloud ecosystems.
- Identity issues across users, applications, and APIs.
Essentially, dynamic cloud environments no longer lend themselves to static security solutions.
Threat Detection via Artificial Intelligence on a Massive Scale
CrowdStrike is one example of how cloud-native systems are revolutionizing threat detection.
By emphasizing AI-based security operations, CrowdStrike demonstrates a trend towards:
- Rapid threat intelligence.
- Automation of incident response.
- Lower dwell time and alert fatigue.
From a SecOps perspective, this supports the importance of intelligent security architectures, not disparate point solutions.
Network and Security Convergence
The emergence of SASE and ZTNA has seen firms such as Cloudflare demonstrate the merging of networks and security.
The benefits include:
- No need for VPN with secure access.
- Security delivered at the edge.
- Combining performance and security.
This is part of an important architectural shift. The access strategy has shifted from being location-based to policy-based.
Continuous Risk and Exposure Management
Rapid7 identifies yet another important facet of cybersecurity. Continuous visibility of risks.
With growing attack surfaces due to the cloud and Internet of Things, companies are focusing on:
- Scalable vulnerability management.
- Managed detection and response (MDR).
- Prioritization based on risk.
This is due to the increasing requirement for continuous security posture management.
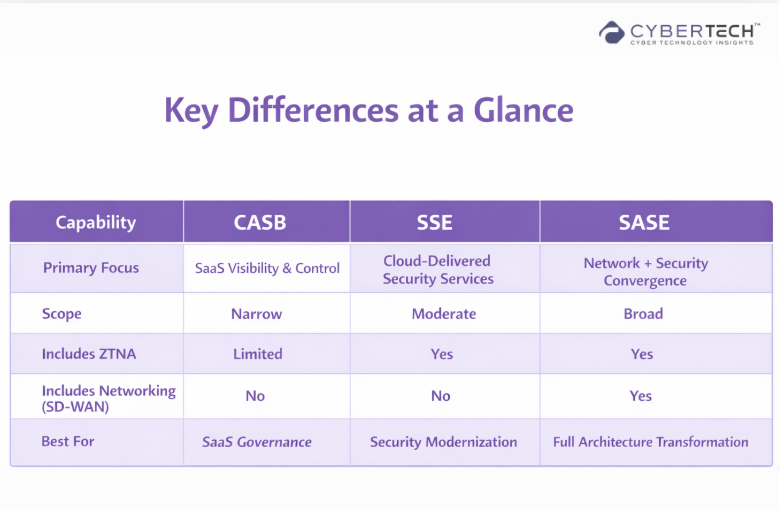
Decoding the Modern Cloud Security Stack
As cloud environments have evolved, so has the security stack designed to protect them. For many U.S. enterprises, the challenge is no longer whether to adopt new security models.
It is understanding how frameworks like CASB, SASE, and SSE fit into a cohesive cloud security architecture, rather than becoming yet another layer of fragmented tooling.
CASB: The First Line of Cloud Defense
CASB became one of the first security solutions developed to protect cloud-based applications.
The main concerns are:
- Visibility of cloud app usage.
- Security of data and policy enforcement.
- Protection against threats to both authorized and unauthorized apps.
As companies started using Microsoft 365 and Salesforce, CASB became indispensable for security teams managing cloud access.
But CASB was designed for a time when SaaS dominated the market and not for today’s complex cloud landscape.
SASE: Convergence of Networking and Security
The Secure Access Service Edge (SASE) architecture reflects an evolution beyond traditional methods. It combines networking and security in a single, cloud-based solution.
According to Gartner’s definition, SASE consists of:
- Software-defined WAN (SD-WAN)
- Secure web gateway
- Cloud Access Security Broker (CASB)
- Zero Trust Network Access (ZTNA)
The aim is to provide secure and optimized access to applications, regardless of where the user is located.
In the United States, SASE is now considered a cornerstone technology for enterprise access management.
SSE: Security, but No Network Layer
The Security Service Edge (SSE) can be viewed as a part of SASE that provides security services exclusively.
This involves the following solutions:
- CASB
- Secure Web Gateway (SWG)
- Zero Trust Network Access (ZTNA)
SSE is especially beneficial for companies that possess existing network infrastructure and seek a way to enhance their security without changing their network connectivity.
Perimeter to Identity: Architectural Transition
Today’s security architecture for cloud computing no longer revolves around protecting perimeters. Instead, it constantly verifies trust in every action taken.
It is at this stage that the transition of the ZTA architectural model from concept to requirement happens.
According to the National Institute of Standards and Technology, Zero Trust implies a model where all requests are considered untrusted, irrespective of where they come from.
Key Aspects of the Architecture:
- Identity becomes the new perimeter.
- Context, behaviors, and risks determine access.
- Everything, be it an entity, workload, or API, is constantly verified.
In terms of the U.S.-based enterprises, such a transition is crucial due to increasing identity and credential-based attacks.
Complexity of Multi-Cloud: Why Architecture Trumps Tools
Most companies in the United States today are not “cloud-first.” Rather, they are inherently multi-cloud.
Every cloud vendor brings along:
- Customized security setup.
- Distinct identity paradigm.
- Diverse compliance mechanism.
Without an architecture, such a multi-cloud environment can develop vulnerabilities.
Hence, modern cloud security architecture must emphasize:
1. Policy Standardization
Security policies are standardized in all cloud systems
2. Unified Visibility
Unified views on posture, risks, and potential threats
3. Automation
AI-based detection and response to minimize manual actions
Architecture without tools creates gaps. Tools without architecture lead to complexity. Hence, both are necessary.

Data Security and Compliance
Cloud security is not shaped by a single, unified regulatory framework. It is driven by a layered and often fragmented compliance landscape, where federal mandates, industry-specific regulations, and state-level privacy laws intersect.
Organizations must comply with:
- Healthcare – HIPAA.
- SaaS and service provider – SOC 2.
- Privacy at the state level – CCPA.
It demands an architecture capable of offering end-to-end data encryption, fine-grained access control, and continuous compliance monitoring.
What This Means for Enterprise Architecture
For cybersecurity leaders in the U.S., there is no need to choose a framework. Instead, they must find ways to orchestrate these capabilities into an architecture that will be scalable and supportive of the business’ needs regardless of its transition to remote work, multi-cloud deployments, and other challenges.
It is precisely when it comes to creating an architecture for enterprise cybersecurity that businesses tend to struggle the most.
Designing cloud security architecture today requires an intentional approach in which identity is at the center of control; security policies are consistent across all environments; and security measures adapt dynamically depending on user behavior, data exchange, and external threats.
Within that framework, CASB, SSE, and SASE technologies cease being mutually exclusive options and instead turn into essential elements of a robust enterprise architecture.

FAQs
1. Describe the current state of cloud security architectures for businesses.
Cloud security architecture is a modern enterprise-level framework characterized by the identity-first approach, cloud-first mentality, and implementation of Zero Trust principles along with automation and integration of security solutions.
2. Explain how Zero Trust works within the cloud.
Within cloud computing, Zero Trust works by implementing authentication checks, enforcing least-privilege access principles, and applying security policies consistently across all apps, networks, and data.
3. Define CASB, SSE, and SASE, and explain their differences.
CASB stands for Cloud Access Security Broker, SSE is Secure Service Edge, and SASE is Secure Access Service Edge. They all differ in that CASB offers visibility into SaaS applications, SSE provides security services, and SASE is a combination of both.
4. Explain why multi-cloud security poses a problem for U.S.-based enterprises.
The reason for the difficulty in implementing cloud security in a multi-cloud environment is inconsistency in configuration, lack of visibility, and various compliance regulations.
5. List the major elements of a cloud security architecture framework.
The main elements of the cloud security framework include identity and access management, Zero Trust architecture, CSPM (cloud security posture management), workload protection, DevSecOps, and compliance.
To participate in upcoming interviews, please reach out to our CyberTech Media Room at info@intentamplify.com.
🔒 Login or Register to continue reading











