Adversaries are no longer relying on broad-based attacks. They are executing targeted, identity-driven, and AI-assisted campaigns against revenue-critical systems. The result is a compression of threat detection and response timelines that traditional security models cannot match.
Across large enterprise environments, telemetry shows a consistent pattern. Low-signal exposures are being chained into high-impact incidents faster than teams can triage them.
What Is Threat Detection?
At its core, threat detection is the continuous process of identifying malicious activity, abnormal behavior, and exploitable risk conditions across an organization’s digital environment before they result in business impact.
Traditionally, threat detection focused on identifying known indicators of compromise, malware signatures, or suspicious network activity.
That model assumed attacks were slower, more predictable, and easier to isolate. That assumption no longer holds.
Assess Your Threat Detection Maturity
Get a quick, executive-level view of where your detection strategy stands today.
Access the 2-minute Self-Assessment
Why Threat Intelligence Is Now a Detection Multiplier
Research signal: Detection alone cannot keep pace with evolving attack strategies.
The World Economic Forum notes that cyber resilience increasingly depends on anticipating threats, not just responding to them.
Platform insight: When detection signals are enriched with intelligence, prioritization accuracy improves significantly, and false positives drop as alerts are mapped to known adversary behaviors.
See How Intelligence Improves Detection Accuracy
Explore how leading security teams reduce false positives and improve prioritization using intelligence-driven detection.
Non-Negotiable Shifts for 2026
The scale and speed of modern attacks have rendered traditional detection models insufficient. Security leaders must now make structural shifts that prioritize business risk, not just a technical signal.
1. From Alert Volume to Risk Precision
Insight: Enterprise security teams are overwhelmed by signals, not protected by them.
- IBM Security reports that the average organization takes 200+ days to identify a breach, largely due to signal fragmentation.
- Internal telemetry shows that a significant share of high-severity alerts lack asset criticality context, reinforcing broader industry findings that the majority of alerts fail to drive action.
What this means: Detection systems that prioritize severity over business impact are structurally flawed.
Executive shift: Move to risk-weighted detection, where alerts are automatically enriched with asset value, identity exposure, and operational impact.
2. From Detection to Continuous Response
Insight: The attack lifecycle is now shorter than human response cycles.
- Mandiant reports that the median attacker dwell time has dropped significantly, with some intrusions escalating within hours, not days.
- CrowdStrike highlights breakout times as low as 7 minutes in hands-on keyboard attacks.
What this means: Detection without immediate response is operationally irrelevant.
Executive shift: Build closed-loop detection-response systems, where high-confidence threats trigger automated containment within minutes.
3. From Technical Metrics to Business Risk Outcomes
Insight: Boards are shifting from security posture to financial exposure.
- Verizon shows that over 80% of breaches involve compromised credentials or identity misuse.
- World Economic Forum identifies cyber incidents as a top global business risk, driven by operational disruption and regulatory penalties.
What this means: Security effectiveness is now measured in terms of revenue protection, downtime avoidance, and compliance exposure.
Executive shift: Align detection to business-critical assets, workflows, and regulatory risk zones.
Benchmark Your Detection Strategy Against 2026 Priorities
Understand how your current approach compares to emerging enterprise standards.
Download the Executive Checklist
Detection as “Risk in Motion”
Threat detection today is not just about identifying attacks. It is about identifying risk in motion across identities, assets, and workflows.
- NIST defines detection as part of the “Detect” function within its Cybersecurity. Framework. It focuses on identifying events in a timely manner.
- MITRE emphasizes behavioral detection. This means mapping attacker techniques across the full attack lifecycle, not just initial compromise.
What has changed:
- Attacks are multi-stage and identity-driven.
- Signals are low-noise but highly distributed.
- Exploitation happens within hours, not days.
Implication for CISOs: Detection must evolve from event monitoring to continuous, context-aware risk identification.
The Three Layers of Effective Threat Detection
To understand how modern detection systems operate, it helps to break them into three functional layers:
1. Signal Collection
This includes telemetry from across the environment:
- Endpoints, networks, cloud workloads.
- Identity systems and access logs.
- SaaS applications and APIs.
Challenge: Most organizations collect vast amounts of data but lack meaningful correlation.
2. Context and Correlation
This is where detection becomes intelligent:
- Mapping signals to asset criticality.
- Linking identity behavior to access risk.
- Correlating weak signals into attack patterns.
Research insight: Gartner notes that lack of context is one of the primary reasons security alerts fail to drive timely action.
3. Decision and Response
The final layer determines impact:
- Prioritizing threats based on business risk.
- Triggering alerts, workflows, or automated containment.
- Feeding insights into incident response and governance.
Modern requirement: Detection must be tightly coupled with response. A detected threat that is not acted upon is operationally equivalent to a missed threat.
Why Traditional Detection Models Fall Short
Legacy detection models were built for a different threat landscape.
- Signature-based systems struggle with novel and AI-generated threats.
- Static rules fail in dynamic cloud environments.
- Disconnected tools create fragmented visibility.
According to IBM Security, delays in detection remain one of the largest contributors to breach cost and impact.
Capability Mapping for Decision-Makers
Understand how different solution categories align with your detection strategy and operational goals.
This comparison helps identify capability gaps, integration strengths, and where true risk reduction is achieved.
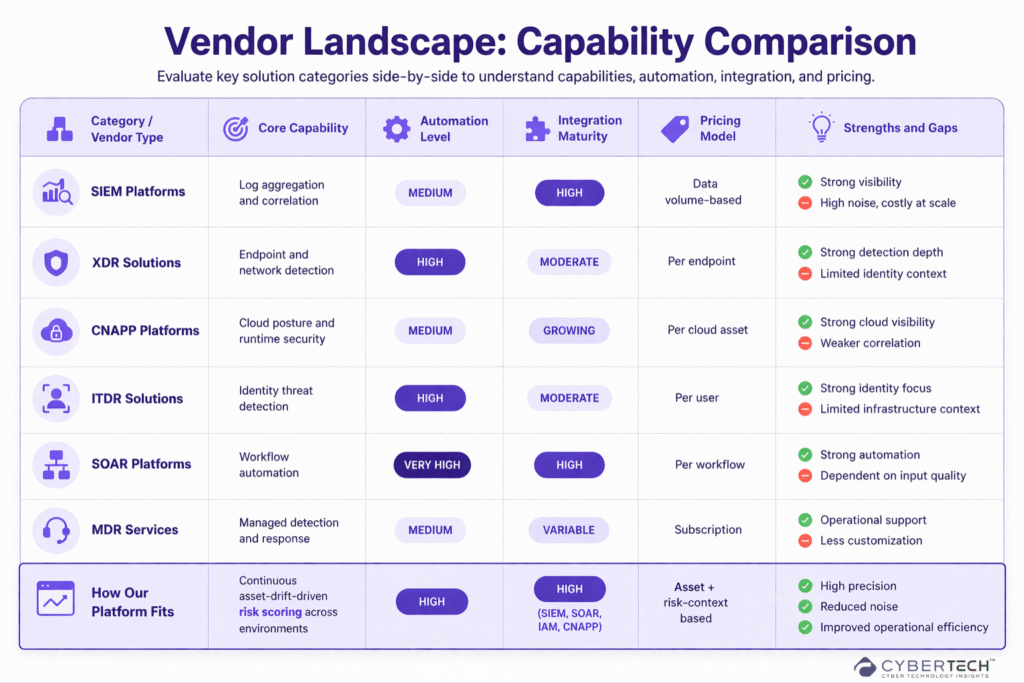
Compare Detection Capabilities Across Vendors
Get a structured view of how leading solutions stack up across automation, integration, and risk coverage.
Access the Full Comparison Guide
What “Good” Threat Detection Looks Like Today
A modern threat detection capability should:
- Continuously monitors changes across environments, not just events.
- Prioritizes threats based on business-critical exposure.
- Detects identity misuse and privilege escalation in real time.
- Correlates signals across cloud, on-prem, and SaaS.
- Triggers automated response for high-confidence threats.
Executive Takeaway
Threat detection is a real-time business risk identification system. Organizations that treat detection as a reactive alerting layer will continue to face delayed response, higher breach costs, and increased regulatory exposure.
Those who evolve toward continuous, risk-aligned detection will gain a measurable advantage in both security posture and operational resilience.
FAQs
1. What is the biggest gap in modern threat detection strategies?
The biggest gap is the lack of business context in detection systems. Most tools generate alerts based on technical severity, not business impact, making it difficult for leaders to prioritize risks tied to revenue, operations, or compliance.
2. How should CISOs measure the effectiveness of threat detection?
Effectiveness should be measured through business-aligned metrics, including mean-time-to-detect (MTTD), mean-time-to-respond (MTTR), reduction in false positives, and the percentage of threats tied to critical assets that are detected and contained early.
3. Why is identity now central to threat detection?
Identity has become the primary attack vector because attackers increasingly exploit credentials, access privileges, and session tokens to move laterally and access sensitive systems without triggering traditional security controls.
4. What role does automation play in modern threat detection?
Automation is essential to reduce response time and operational load. High-confidence threats should trigger automated containment actions, minimizing reliance on manual triage and enabling faster disruption of active attacks.
5. How can organizations reduce false positives in detection systems?
False positives can be reduced by implementing context-aware, risk-based detection, where alerts are enriched with asset criticality, identity context, and behavioral patterns to prioritize only meaningful threats.
Don’t let cyber attacks catch you off guard – discover expert analysis and real-world CyberTech strategies at CyberTechnology Insights.
To participate in upcoming interviews, please reach out to our CyberTech Media Room at info@intentamplify.com.
🔒 Login or Register to continue reading












