The threat of ransomware has evolved into a threat to organizational sustainability.
The most recent study on the cost of a data breach by IBM revealed that the average cost of a breach rose to $4.88 million in 2024, with U.S. companies incurring costs greater than $10 million per breach, ranking first in the world.
For CISOs, CIOs, and risk professionals, this shifts the discussion. Security is no longer only about perimeter defenses and detection speed. It is about containment, recovery, and, in some circumstances, complete isolation.
It is in this context that air-gapped networks make a comeback.
Once thought outdated in the era of cloud computing, air-gapped designs are currently undergoing a resurgence among U.S. corporations, particularly those committed to critical infrastructure initiatives outlined by the Cybersecurity and Infrastructure Security Agency.
What Are Air-Gapped Networks?
An air-gapped network design isolates systems from unsecured networks, including the internet.
More concretely, this involves:
- Complete isolation from external internet connectivity.
- Strictly controlled and minimal data transfer mechanisms.
- Deep segmentation that extends beyond software-defined boundaries.
Unlike other modern security frameworks, which presume breaches, air-gapped systems aim to completely avoid outside access, making them highly effective for safeguarding mission-critical assets.

Importance of Air-Gapped Networks in America
The importance of air-gapped networks emerges when considering the perspective of the risks faced by the United States. According to the Cybersecurity and Infrastructure Security Agency, there are 16 critical infrastructure sectors, such as:
- Energy and utilities.
- Financial services.
- Healthcare systems.
- Defense and governmental supply chains.
They all have something in common: failure is not an option.
On the other hand, there is an aggravating threat situation. The U.S. leads the world in terms of breach costs, with an average of over $10.22 million. The average costs of breaches in industrial sectors amount to over $5.5 million due to operational downtime.
The most common type of attacks are associated with human factors and credential compromise that lead to breaches. In such circumstances, regular security measures are not enough.
Therefore, air-gapping acts as the last defense line. It eliminates threats rather than monitors them.
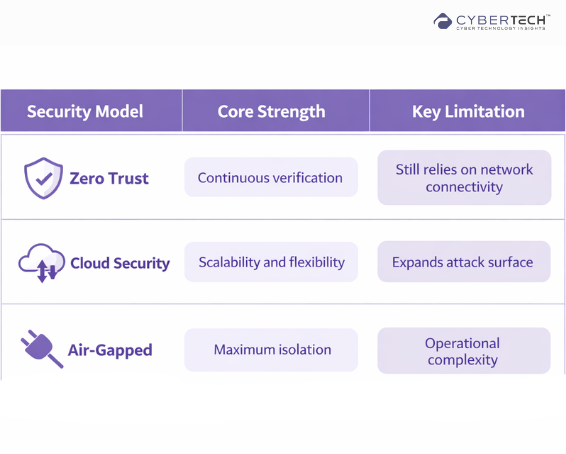
Air-Gapped Networks vs Modern Security Architectures
Today’s enterprise security stack is layered and complex. Solutions from companies like CrowdStrike and Cloudflare focus on detection, response, and Zero Trust access.
But these approaches share one underlying assumption. Connectivity exists.
Enterprise Use Case Highlights
Air-gapped networks are strategically deployed to protect an organization’s most critical assets where compromise is not an option.
They enable enterprises to isolate high-risk systems, ensuring resilience against advanced threats, ransomware, and insider-driven breaches.
1. Safeguarding of Sensitive Corporate Assets
Critical intellectual property, defense information, and financial systems are commonly air-gapped to avoid outside manipulation.
2. Identity and Compliance Isolation
A separation of identity governance systems is needed to comply with standards such as SOX, HIPAA, and GDPR.
3. SecOps and Threat Analysis
Air-gapped environments can be used for malware analysis and incident investigation.
4. Insider Threat Mitigation
The use of air-gapped solutions minimizes the threat of data exfiltration, even with credential hacking.
5. Critical Infrastructure Protection
ICS and SCADA infrastructures commonly depend on air-gapped systems to avoid remote manipulation.
Benefits of an Air-Gapped Network
Air-gapped networks significantly reduce the attack surface by eliminating external connectivity, making them highly effective against ransomware and remote exploits.
1. Virtually No Exposure to Attacks from Outside Sources
Organizations eliminate internet access, which is typically the preferred attack vector for most attackers.
2. Robust Ransomware Protection
Lateral movement within networks is critical for ransomware to spread and thrive.
3. Enhanced Compliance Readiness
Isolation makes it easier to comply with regulatory mandates in industries such as healthcare and banking.
4. Limited Blast Radius
In the event of any attack, air-gapped devices will not be impacted.
Trade-offs and Limitations
Air-gapping is a formidable concept, but it is not an easy one.
1. Operational Challenges
The management of isolated systems necessitates stringent data exchange and update policies.
2. Poor Scalability
Air-gapping is not as easily integrated into contemporary cloud-based infrastructures.
3. Lack of Real-Time Data Availability
Instantaneous processing and analysis of information is more challenging on isolated systems.
For any decision-maker, it serves as a reminder of a crucial concept. Air-gapping is not the default setting. It is a strategic measure to protect critical infrastructure.
Threats and Myths
One of the worst misconceptions surrounding air-gapping is that isolation means security. It does not.
Isolated systems can still fall victim to:
- Malicious insider actions.
- Contaminated portable devices.
- Malware embedded in supply chain deliveries.
As illustrated by IBM’s findings, malicious insiders cause some of the costliest breaches, costing over $5 million per occurrence. It serves as an important reminder. Isolation minimizes risk. It does not remove it.
Best Practices for Deployment
Effective air-gapped security requires strict control over data transfer points, continuous monitoring of isolated systems, and clearly defined access governance.
For CISO/CIOs
- Classify valuable resources.
- Match the air-gapping approach to the business continuity strategy.
- Establish guidelines for air-gap environment governance.
For SecOps Managers
- Watch every point of entry/exit.
- Protect transmission channels of information.
- Ensure visibility in isolated networks.
For Compliance and Risk Managers
- Integrate air-gapped solutions into compliance regulations.
- Establish auditability.
For IT & Infrastructure Managers
- Consider practicality and security equally.
- Prepare for maintenance and updates.
Organizations adopting identity management solutions such as SailPoint Technologies can continue enforcing governance and access control through segmentation.
The Future: Air-Gapped Security in a Cloud First World
Cybersecurity’s future cannot be either all connected or entirely disconnected; it will be both.
Some of the trends on the horizon are:
- Air-gapping selected workloads.
- One-way data transfers (data diodes).
- AI-powered monitoring of air-gapped environments.
However, there are new threats from AI itself.
According to IBM’s findings, 97% of businesses affected by an AI breach did not have adequate access control measures in place.
“The data shows that a gap between AI adoption and oversight already exists, and threat actors are starting to exploit it,” said Suja Viswesan, Vice President, Security and Runtime Products, IBM.
The smarter and more connected systems are, the more significant disconnection becomes as a strategy.
Conclusion
Isolation Is Not a Step Backwards, It Is a Strategic Step Forward
With ever-expanding attack surfaces across the cloud, artificial intelligence, and distributed networks, the existing “detect and respond” paradigm is coming up against its limits.
Even some of the most cutting-edge detection technologies offered by leading companies, such as CrowdStrike and Cloudflare were conceived and developed specifically for an environment where connections are constant.
Yet, that same connectivity opens up organizations to modern, sophisticated cyberattacks.
The air gap network is an answer to that very challenge.
This is not to say that air gaps represent any form of retreat from innovative technology or a rejection of the cloud-first approach.
Rather, air gaps represent an introduction of intentional isolation as another layer of security control, one that ensures that critical assets remain safe in a highly interconnected world.
When it comes to cybersecurity sectors relevant to CISA priorities, the issue at hand is not whether an attack can be detected but whether certain systems should even be accessible.
If your security strategy still assumes everything should be connected, it may be time to rethink your architecture.
Start by identifying where isolation can create the greatest reduction in risk and the highest level of certainty.
FAQs
1. Explain what an air-gapped network is, and how it enhances the security posture of an enterprise.
An air-gapped network is the separation of critical systems from any other connected network, which reduces vulnerability to remote attacks, ransomware, etc.
2. Under what conditions do you recommend U.S. enterprises adopt air-gapped networks?
U.S. enterprises should adopt air-gapped networks in cases that involve critical systems, sensitive information repositories, and critical operations where downtime could have serious repercussions.
3. Which security architecture offers more protection against cyber attacks: an air-gapped network or Zero Trust architecture?
Air-gapped networks ensure isolation, whereas Zero Trust focuses on controlled access. Both security architectures are usually used simultaneously by enterprises.
4. What are the difficulties in adopting air-gapped systems?
Difficulties associated with their adoption include complexity, scaling issues, controlled data exchange processes, and the need for visibility in an isolated environment.
5. Is it possible to breach an air-gapped system?
Although it is extremely difficult, it is not impossible to break into an air-gapped system due to several factors, such as insider threats.
To participate in upcoming interviews, please reach out to our CyberTech Media Room at info@intentamplify.com.
🔒 Login or Register to continue reading












