Threat intelligence has shifted from a technical input to a strategic control point for enterprise risk.
According to IBM Security, the global average cost of a data breach exceeded $4 million, with detection and containment time being the single largest cost driver.
The implication for CISOs is clear. Speed determines impact.
Threat intelligence, when operationalized effectively, reduces time-to-detect, improves prioritization, and directly lowers financial exposure.
Why Threat Intelligence Is a Business-Critical Function
Cyber risk is now enterprise risk.
The World Economic Forum highlights cyber insecurity as one of the top global business risks, particularly as digital ecosystems expand and interdependencies increase.
For executive leaders, this means breaches are not unpredictable events. They are increasingly anticipatable outcomes of known exposure.
Threat intelligence provides the lens to see those exposures before attackers exploit them.
The Problem with Traditional Threat Intelligence Approaches
Despite widespread adoption, most threat intelligence programs fail to deliver measurable risk reduction.
According to Tenable co-CEO, Stephen Vintz, “A “responsibility gap” over AI governance has emerged over the last three years and is now one of the most pressing challenges facing organizations.”
Intelligence Without Context
Frameworks like MITRE provide structured knowledge of adversary behavior. However, without mapping this to internal assets, organizations struggle to prioritize effectively.
Fragmented Visibility
According to Gartner, tool sprawl remains one of the biggest barriers to effective security operations. Intelligence signals often remain siloed across EDR, SIEM, identity, and cloud platforms.
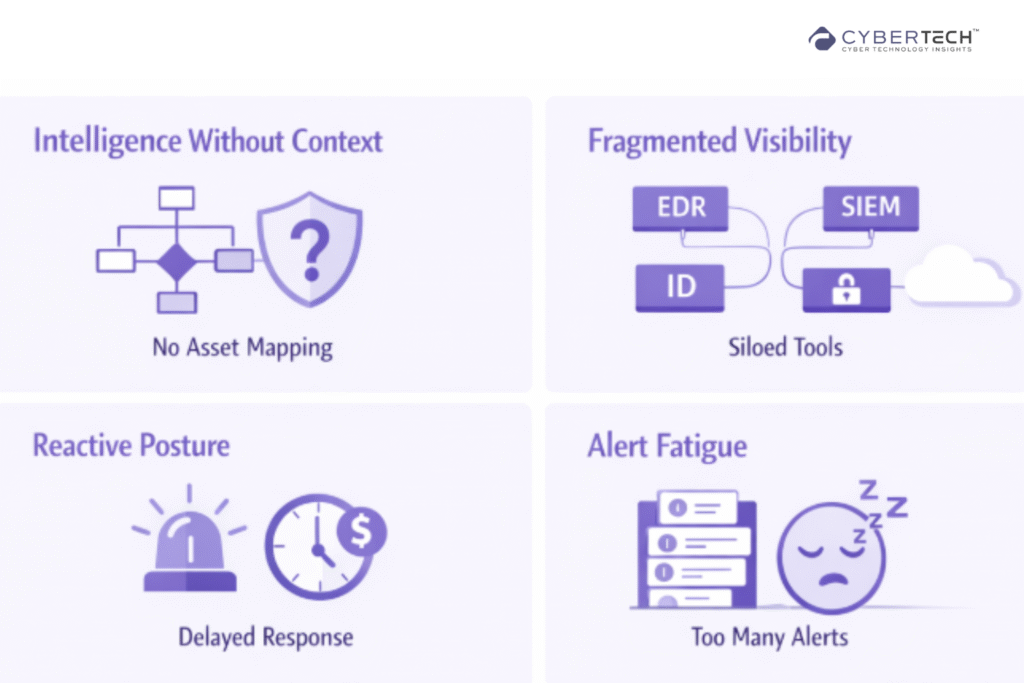
Reactive Posture
Many organizations still rely on intelligence after an incident has already occurred. This is increasingly risky.
According to IBM Security, breaches that take longer to identify and contain result in significantly higher costs, reinforcing that delayed detection directly amplifies business impact.
Alert Fatigue
The volume of alerts continues to rise, while actionable insights remain scarce. This leads to slower response and missed high-risk signals.
Assess Your Threat Intelligence Gaps
Identify where your current approach is slowing detection and increasing risk.
What Modern Threat Intelligence Looks Like
Modern threat intelligence is defined not by volume, but by relevance and actionability.
Leading organizations align with four principles:
- Contextualized intelligence, mapped to business-critical assets.
- Operational integration, embedded into detection and response workflows.
- Predictive focus, leveraging attacker behavior patterns.
- Continuous adaptation, evolving with the threat landscape.
This aligns closely with guidance from Gartner, which emphasizes risk-based prioritization and exposure management as the future of security operations.
What Enterprise Telemetry Reveals About Modern Attacks
Across thousands of enterprise environments, telemetry analysis reveals consistent attack dynamics:
- Internet-facing vulnerabilities are often exploited within 48 hours.
- High-value assets are disproportionately targeted.
- Lateral movement begins rapidly after initial compromise.
These findings align with broader industry observations from Verizon and Mandiant.
The takeaway is not just speed. It is predictability at scale.
Threat intelligence must therefore prioritize:
- Exposure visibility.
- Attack path prediction.
- Real-time response enablement.
Turning Intelligence Into Action: The Operational Framework
To deliver measurable outcomes, threat intelligence must integrate into four operational layers:
1. Collection
Internal telemetry combined with external intelligence sources.
2. Correlation
Mapping threats to vulnerabilities, identities, and assets.

3. Prioritization
Risk-based scoring aligned with business impact.
4. Action
Automated or guided response across security controls.
This model reflects the shift toward continuous threat exposure management, a concept strongly advocated by Gartner.
Benchmark Your Intelligence Maturity
See how your organization compares across reactive, proactive, and adaptive stages.
Intelligence Without Integration Fails
Industry research consistently shows that fragmented security architectures reduce effectiveness.
- IBM Security links longer breach lifecycles to delayed detection and poor integration.
- Gartner highlights integration as critical to reducing operational friction.
- Mandiant demonstrates that early correlated signals significantly reduce attacker dwell time.
The conclusion is clear. Intelligence must be embedded into workflows, not layered on top.
Where Most Security Investments Go Wrong
Security investments often fail due to misalignment with actual risk drivers.
According to Gartner:
- Organizations over-invest in tools rather than outcomes.
- Detection capabilities outpace response maturity.
- Metrics fail to reflect business risk reduction.
A more effective model focuses on:
- Intelligence-driven prioritization.
- Reduction of attack paths.
- Alignment with business-critical systems.
What to Look for in a Threat Intelligence Platform
The right platform should move beyond raw data aggregation and deliver contextual, actionable intelligence that aligns security operations with business priorities.
| Capability | Basic Tools | Advanced Platforms |
| Data Sources | External feeds only | Internal and external telemetry |
| Contextualization | Limited | Asset and business context |
| Automation | Manual workflows | Automated prioritization |
| Integration | Siloed tools | Embedded architecture |
| Predictive Insights | Low | High |
Evaluate the Right Intelligence Platform
Get a checklist to choose solutions that actually reduce breach risk.
How to Evaluate Your Current Posture
Understanding your current posture is the first step toward reducing breach risk. Without a clear baseline, even the best investments fail to deliver measurable impact.
Leaders should assess how effectively threat intelligence informs decisions, accelerates response, and aligns security efforts with business-critical priorities.
1. Business Alignment
- Is intelligence mapped to revenue-critical systems?
- Can you quantify financial risk reduction?
2. Operational Efficiency
- Are analysts spending time on low-value alerts?
- Is intelligence accelerating the response?
3. Decision Impact
- Does intelligence inform board-level decisions?
- Is it used proactively or reactively?
How to Prioritize Investments
Focus Now
- Integrate intelligence across existing tools.
- Enable real-time correlation.
- Automate high-confidence responses.
Invest Next
- Predictive analytics based on attacker behavior.
- AI-driven prioritization.
- Exposure management capabilities.
Avoid
- Standalone intelligence feeds without context.
- Tool sprawl without integration.
- Metrics disconnected from business outcomes.
What to Ask Vendors in an Request for Proposal (RFP)
Data & Coverage
- What telemetry sources are integrated natively?
- How is external intelligence validated?
Context & Prioritization
- How is intelligence mapped to my environment?
- How are high-risk threats identified?
Operationalization
- How is intelligence embedded into workflows?
- What level of automation is supported?
Measurable Outcomes
- How do you reduce MTTD and MTTR?
- What evidence demonstrates breach risk reduction?
Threat Intelligence Scorecard
The Threat Intelligence Scorecard provides a quick, executive-level view of how effectively intelligence is driving real security outcomes.
It helps leaders move beyond activity metrics and assess whether intelligence is truly aligned with business risk, operationalized in workflows, and delivering measurable impact.
Used consistently, it becomes a practical benchmark to identify gaps, prioritize improvements, and track maturity toward a more proactive, intelligence-driven security posture.
Strategy
- Intelligence aligned with business risk.
- Clear ownership.
Data and Visibility
- Unified telemetry.
- External intelligence integrated.
Operations
- Embedded in workflows.
- Automated prioritization.
Outcomes
- Reduced response time.
- Lower alert fatigue.
- Improved risk posture.
Final Perspective: From Intelligence to Advantage
The organizations that outperform in cybersecurity are not those with the most data. They are those who operationalize intelligence effectively.
As reinforced by the World Economic Forum and Gartner, resilience now depends on anticipating threats, not just responding to them.
Threat intelligence, when aligned with business risk and embedded into operations, becomes a strategic advantage.
It enables leaders to see earlier, decide faster, and act with precision. In today’s threat landscape, that is what stops breaches.
Stop Reacting. Start Preventing.
Get a tailored view of how intelligence can reduce your breach risk today.
FAQs
1. How does threat intelligence reduce business risk?
Threat intelligence reduces business risk by identifying likely attack paths before exploitation. It enables organizations to prioritize defenses around critical assets, reducing breach likelihood and financial impact.
2. What makes threat intelligence actionable for security teams?
Actionable threat intelligence is contextualized to an organization’s environment. It connects external threats with internal assets, vulnerabilities, and identities, enabling faster and more precise response decisions.
3. Why do most threat intelligence programs fail to deliver ROI?
Most programs fail due to a lack of integration and context. Intelligence remains siloed, reactive, and disconnected from business priorities, limiting its ability to influence decisions or reduce risk.
4. How should CISOs evaluate a threat intelligence platform?
CISOs should evaluate platforms based on integration, contextualization, automation, and measurable outcomes such as reduced detection time and improved risk prioritization. Data volume alone is not a success metric.
5. What is the difference between threat intelligence and threat exposure management?
Threat intelligence focuses on understanding adversaries and attack patterns. Threat exposure management applies that intelligence to continuously identify, prioritize, and reduce real-world attack paths across the environment.
Don’t let cyber attacks catch you off guard – discover expert analysis and real-world CyberTech strategies at CyberTechnology Insights.
To participate in upcoming interviews, please reach out to our CyberTech Media Room at info@intentamplify.com.
🔒 Login or Register to continue reading












