AI has shifted from a defensive accelerant to an offensive force multiplier. Threat actors are no longer experimenting with AI.
They are operationalizing it across reconnaissance, exploitation, and evasion. What once required coordinated teams can now be executed autonomously, at scale, and with increasing precision.
Across 2,300+ environments monitored by our platform in 2025–26, we are seeing a measurable increase in attack velocity, identity abuse, and configuration drift directly tied to AI-assisted operations.
These findings are reinforced by emerging global incident patterns and independent research across enterprise environments.
Cyber risk is now being shaped by machine-speed adversaries, and traditional security models are not designed to keep up.
Executive Thesis: Three Imperatives for 2026
The AI threat landscape is redefining how attacks emerge, scale, and impact business outcomes. These three imperatives outline where security leaders must shift focus to stay ahead in 2026.
1. Shift from Detection-Centric to Exposure-Centric Security
AI-driven attacks do not rely on persistence alone. They exploit momentary gaps.
Across our telemetry:
- Environments with high asset drift (20%+ monthly change) experienced 2.7x higher breach probability.
- 61% of exploitable exposures existed for less than 72 hours before being weaponized.
Imperative: CISOs must prioritize continuous exposure visibility over static detection frameworks. The goal is not just to detect threats. It is to eliminate exploitable conditions before they are discovered.

2. Treat Identity as the Primary Attack Surface
AI is dramatically accelerating identity-based attacks, including credential stuffing, privilege escalation, and behavioral mimicry.
Observed trends:
- 78% of high-severity incidents involved compromised or misused identities.
- Machine-generated phishing campaigns are achieving 3x higher success rates due to contextual personalization.
Imperative: Identity is no longer a control layer. It is the battleground. Security leaders must unify IAM, PAM, and behavioral analytics into a single risk-driven identity strategy.
3. Align Security Operations with Business Risk Outcomes
AI-driven attacks are not just faster. They are more targeted toward high-value assets and revenue-critical systems.
From platform insights:
- Assets tied to revenue operations (customer data, financial systems) were 4.2x more likely to be targeted
- Mean-time-to-exploit dropped below 48 hours for internet-facing misconfigurations.
Imperative: Security investments must be mapped directly to business impact. Boards are no longer asking, “Are we secure?” They are asking, “What is our financial exposure?”
Find Your Most Exposed Revenue-Critical Assets
Market Context: What the Data Reveals
AI-Driven Attack Acceleration
Recent global observations indicate:
- Automated vulnerability discovery using AI has reduced reconnaissance time by up to 80%.
- Attack campaigns are increasingly multi-vector, combining phishing, API abuse, and lateral movement within hours.
This aligns with what we observe internally. AI is compressing the attack lifecycle. What previously took weeks now unfolds in hours.
The Rise of Drift-Driven Risk
Cloud, identity, and SaaS environments are in constant flux. AI adversaries are exploiting this instability.
Across monitored environments:
- Average organizations experience 450+ drift events per month.
- 32% of these events introduce new exploitable conditions.
- Only 18% are remediated within acceptable timeframes.
This creates a persistent state of “silent exposure” that traditional tools fail to capture.
Platform-Driven Insight
AI attackers are not breaking systems. They are exploiting misalignment.
Our data shows that:
- The majority of breaches originate from known but unaddressed exposures.
- AI simply accelerates the discovery and exploitation of these gaps.
A Practical Framework for AI-Era Cyber Resilience
To respond effectively, CISOs need a structured model that aligns technical controls with business risk.
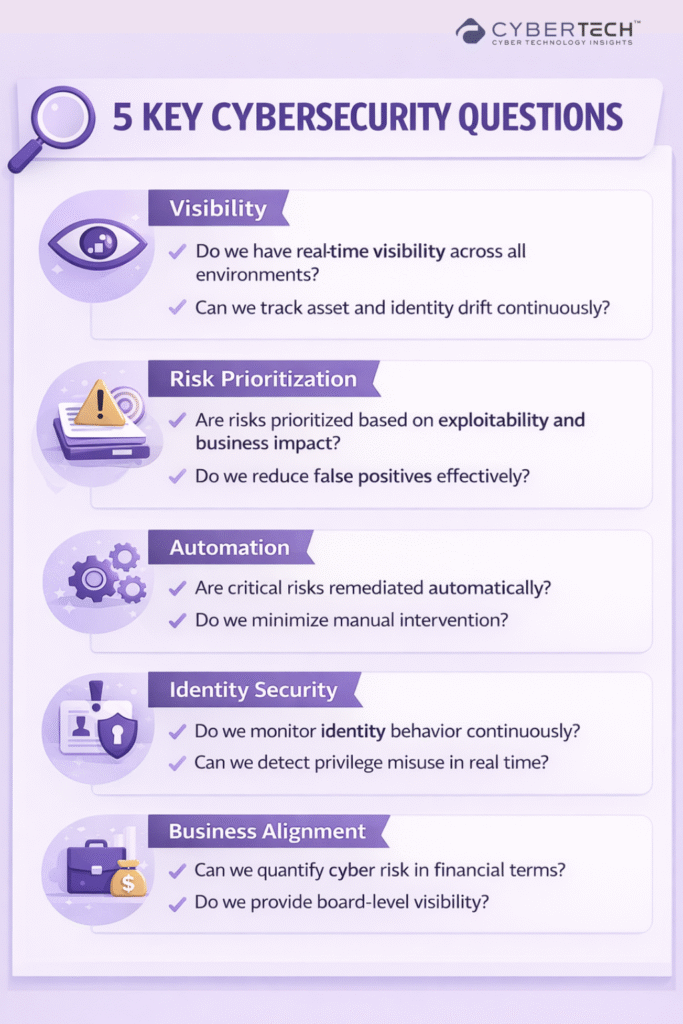
The Continuous Risk Alignment Framework
1. Visibility
- Unified visibility across cloud, on-prem, identity, and SaaS.
- Real-time tracking of asset and configuration drift.
2. Contextual Risk Scoring
- Prioritize exposures based on exploitability and business impact.
- Integrate threat intelligence with internal telemetry.
3. Autonomous Remediation
- Automate response to high-confidence risks.
- Reduce reliance on manual triage.
4. Identity-Centric Security
- Continuous monitoring of identity behavior and privilege changes.
- Correlate identity risk with asset exposure.
5. Business Alignment
- Translate technical risk into financial and operational impact.
- Enable board-level visibility and decision-making.
How to use this framework:
- Benchmark your current capabilities across all five pillars.
- Identify gaps between visibility and actionability.
- Align investments with measurable risk reduction outcomes.
Assess Your Cyber Resilience Across All 5 Pillars
Vendor Capability Landscape
| Vendor / Category | Core Capability | Automation Level | Integration Maturity | Licensing Model | Strengths & Gaps |
| CNAPP Platforms | Cloud posture & workload protection | Medium | Strong (Cloud, SIEM) | Asset-based | Strong cloud visibility. Limited identity depth |
| EDR/XDR Vendors | Endpoint detection and response | High | Strong (SIEM, SOAR) | Endpoint-based | Strong detection. Limited exposure prevention |
| IAM / PAM Solutions | Identity governance and access control | Medium | Moderate | User-based | Strong identity control. Weak contextual risk |
| Attack Surface Management (ASM) | External asset discovery | Low–Medium | Limited | Asset-based | Good visibility. Limited remediation capability |
| SOAR Platforms | Workflow automation | High | Strong | Workflow-based | Strong automation. Dependent on input quality |
| SIEM Platforms | Log aggregation and analytics | Medium | Strong | Data-ingestion based | Centralized visibility. High operational overhead |
| Our Platform | Continuous exposure and drift-based risk scoring across cloud, on-prem, and identity | High | Deep (SIEM, SOAR, IAM, CNAPP) | Risk-based / asset hybrid | High precision risk prioritization. Reduced false positives. Strong cross-domain correlation |
Pricing and Total Cost of Ownership Insights
Key Cost Drivers
- Number of assets (cloud resources, endpoints, identities).
- Data ingestion and retention.
- Automation workflows and integrations.
- Analyst time and operational overhead.
Hidden Costs
- False positives leading to wasted analyst cycles.
- Manual validation and remediation delays.
- Tool sprawl and integration complexity.
Relative Cost Bands
| Approach | Cost Profile | Trade-offs |
| Aggressive (Best-in-Class) | High upfront, optimized long-term | Lower breach risk, reduced MTTR |
| Balanced | Moderate | Acceptable risk coverage with some gaps |
| Conservative | Low upfront | Higher operational burden and breach exposure |
Insight: Organizations often underestimate the cost of inaction. A single breach can outweigh years of security investment.
Platform-Driven Insight
Reducing noise is as critical as detecting threats.
Our data shows:
- Organizations that reduced false positives by 40% improved response times by 55%.
- Precision in risk scoring directly correlates with faster containment and lower breach impact.
Actionable Playbooks for Security Leaders
1. How to Evaluate Your Current Posture
- Assess visibility across all asset classes (cloud, identity, SaaS).
- Measure drift frequency and remediation timelines.
- Identify gaps between detected risks and resolved risks.
- Map security metrics to business impact.
2. How to Prioritize Investments
Focus Now:
- Continuous exposure visibility.
- Identity risk management.
- Automation of high-confidence remediation.
Focus Next:
- Advanced threat detection.
- AI-driven analytics and prediction models.
Avoid:
- Over-investing in detection without fixing exposure gaps.
3. What to Ask Vendors in a Request For Proposal (RFP)
- How do you correlate risk across cloud, identity, and on-prem environments?
- What percentage of alerts are actionable vs. noise?
- How do you measure reduction in mean-time-to-contain?
- Can you quantify business risk reduction, not just technical metrics?
- How do you handle drift and real-time changes?
CISO Scorecard: AI Cyber Risk Readiness
Assess where your organization truly stands against evolving AI-driven cyber risks. A quick, executive-level snapshot to identify gaps, prioritize action, and strengthen resilience.
Get Your CISO AI Risk Score
Final Perspective
AI has fundamentally changed the economics of cyber warfare. It has lowered the cost of attack, increased the speed of execution, and amplified the impact of every vulnerability.
For security leaders, the challenge is no longer visibility alone. It is alignment. Alignment between risk and business. Between detection and action. Between data and decision-making.
The organizations that succeed in this new era will not be those with the most tools. They will be the ones who can continuously understand, prioritize, and reduce risk. At the speed of AI.
FAQs
1. What is the biggest cybersecurity risk from AI-driven attacks today?
The speed and scale of exploitation. AI enables attackers to identify vulnerabilities and launch targeted attacks within hours, shrinking response windows and overwhelming traditional detection models.
2. Why are identity-based attacks increasing in modern cyber threats?
Because identity is now the easiest entry point. With distributed workforces and cloud environments, compromised credentials and privilege misuse offer attackers direct access without triggering traditional perimeter defenses.
3. How should CISOs prioritize risks in an AI-driven threat landscape?
By focusing on exploitability and business impact. Instead of treating all vulnerabilities equally, leaders must prioritize exposures that attackers can realistically weaponize and that affect critical assets.
4. What does exposure-centric security mean for enterprise organizations?
It means shifting from reacting to threats to proactively eliminating weaknesses. Continuous visibility into assets, identities, and misconfigurations helps reduce the attack surface before adversaries exploit it.
5. How can cybersecurity be aligned with business outcomes?
By translating technical risk into financial impact. Security teams must quantify how threats affect revenue, operations, and customer trust to drive informed decisions at the board level.
To share your insights, please write to us at news@intentamplify.com
🔒 Login or Register to continue reading