Global enterprises across finance, healthcare, and manufacturing have reported multi-million dollar disruptions triggered by malware strains that evaded detection for days.
Nation-state actors are blending espionage-grade implants with commercial malware frameworks. Meanwhile, cyber insurance firms are tightening coverage, citing rising claims tied to malware-driven breaches.
“From malware development to social engineering, adversaries are weaponizing AI to accelerate every stage of attacks, collapsing the defender’s window of response,” said Elia Zaitsev, Chief Technology Officer at CrowdStrike.
Anti-malware has become the first line of defense because it is the only control operating at the speed of attack execution.
What is Anti-Malware?
Ransomware, viruses, spyware, and many other forms of malicious software exist. Anti-malware capabilities are operational when your computer is active, monitoring any suspicious behavior. Software such as Microsoft Defender provide robust features that allow you to safeguard your system from these active malware.
Anti-Malware Trends Reshaping Cyber Defense
The current wave of malware innovation did not emerge overnight. It is the result of three converging forces.
- Ransomware-as-a-Service Economies
As per Palo Alto Networks’ Unit 42, almost 80% of all ransomware attacks have been associated with RaaS operations, where affiliates carry out ransomware attacks using built tools.
CrowdStrike recognizes more than 20 ransomware families running as a Ransomware-as-a-Service (RaaS) platform, along with affiliates.
- AI-assisted Code Generation
AI technology is making malware development faster and helping attackers to adapt instantly while attacking.
According to Microsoft, over 600 million cyberattacks happen every day, with attackers using AI automation in malware creation.
- Deep Access to Enterprise Infrastructure
The modern corporate landscape has created more opportunities for attacks from the cloud, identity, and endpoint perspectives. This has enabled hackers to speed up their malware infections.
As per IBM X-Force Zero-Day Case Study, cyber criminals are now exploiting zero-day vulnerabilities within 24 hours of their discovery, which is among the shortest adoption timelines ever noted.
Top Companies Affected
Some of the large firms that have been attacked in the past are JBS (ransomware attack in 2021 for $11 million), Colonial Pipeline (ransomware attack in 2021 for $4.4 million), Norsk Hydro (attack in 2019), and Maersk ($300 million losses due to ransomware attack).
Some recent attacks include those on Snowflake and Ticketmaster in 2024
Below is a snapshot of these high-profile incidents:
Snowflake
Mandiant detected a breach in April 2024 when its customer’s Snowflake installation was breached after the first stage of intrusion was carried out using login credentials obtained via infostealer malware.
The threat actor did not resort to complicated exploits but simply used existing stolen credentials to penetrate into the victim’s cloud environment and exfiltrate its confidential data.
The crucial vulnerability that allowed for intrusion into the target company’s cloud environment was not some advanced zero-day exploit.
This critical failure consisted of the lack of multi-factor authentication on an account with significant privileges.
Had it not been for the lack of detection of the infostealer malware at the endpoint, the attack chain would have failed from the very start.
The lack of malware detection at its earlier stages led to the use of valid credentials against the perimeter and cloud defenses completely. Only anti-malware can prevent credential-harvesting malware before it results in identity theft.
Ticketmaster
According to a report by BBC News about the Ticketmaster hacking incident, the hackers who were associated with the group called ShinyHunters said that they had compromised data belonging to hundreds of millions of people.
Having harvested it through datasets that had been stolen from cloud-based services, before selling them on the dark web. It was an attack against a number of companies using centralized database systems.
The perpetrators used credentials that were obtained earlier, and usually through malware infection. After accessing the network, the intruders moved laterally into valuable data areas. Ultimately, there was a massive extraction of data for millions of users.
It highlights a change in the threat environment. Large-scale attacks are becoming secondary to earlier malware infection campaigns.
Cyber Tech Intelligence delivers unfiltered intel decision-makers demand.
Huge Anti-Malware Failures Across Major Enterprises
Manufacturing and Industry
JBS (2021): The largest meat processor worldwide paid a ransom of $11 million to a Russian-affiliated criminal group REvil due to ransomware attacks.
Norsk Hydro (2019): Sustained a devastating LockerGoga ransomware attack, which led to a shift in operations to manual, causing a financial loss of more than a million dollars.
Honda (2020): Experienced a ransomware attack on its internal systems, leading to a halt in global production.
‘It looks like a case of Ekans ransomware being used,’ said Morgan Wright, Chief Security Advisor at Sentinel One. Ekans, or Snake ransomware, is designed to attack industrial control systems networks.
Brunswick Corporation (2023): Operations were disrupted for nine days due to a cyberattack.
Infrastructure and Energy
Colonial Pipeline (2021): Ransomware attacks from the cybercriminal group, DarkSide, paralyzed America’s largest fuel pipeline, creating gas shortages across the nation.
Maersk (2017): The multinational container shipping company experienced a crippling NotPetya malware attack, resulting in a loss of approximately a million dollars.
Information Technology and Data
23andMe (2023): Credential stuffing attacks compromised the data of about 6.9 million users, containing their genetic data.
Yahoo (2013-2014): Witnessed unprecedented data breaches where malware and unauthorized access affected 3 billion Yahoo accounts.
Why Anti-Malware Should Be Your Initial Layer of Protection
Modern attack vectors do not start from the cloud or the network edge; they start from the endpoint itself, where malware creates its first point of entry in order to eventually launch a complete takeover.
In this light, it becomes clear that anti-malware is no longer just an auxiliary component but the key component itself.
Malware is Just the Door; It’s Not the Prize
It’s now possible for attackers to stage multi-step attacks using malware.
- Infostealer malware gets credentials early in the process
- Loader malware maintains persistence
- An access broker uses credentials to monetize the breach
When investigating incidents for Mandiant, it was discovered that attackers were able to leverage stolen credentials from malware to break into Snowflake.
Speed is Now the Security Perimeter
Security is now based on how fast you detect an attack. According to IBM X-Force, breakouts occur within 2 hours. The attackers take action within minutes, but detection takes hours. Anti-malware works to block attacks while they’re still being executed.
Downstream Security Is Only Secure If Upstream Security Works
There are many assumptions around cloud and identity security. Malware breaks that assumption.
- Credentials get stolen and bypass identity-based security
- Legitimate tools hide attacks from detection
- Attacks get executed in legitimate sessions
Only anti-malware prevents attacks before these steps.
Anti-Malware Blueprint
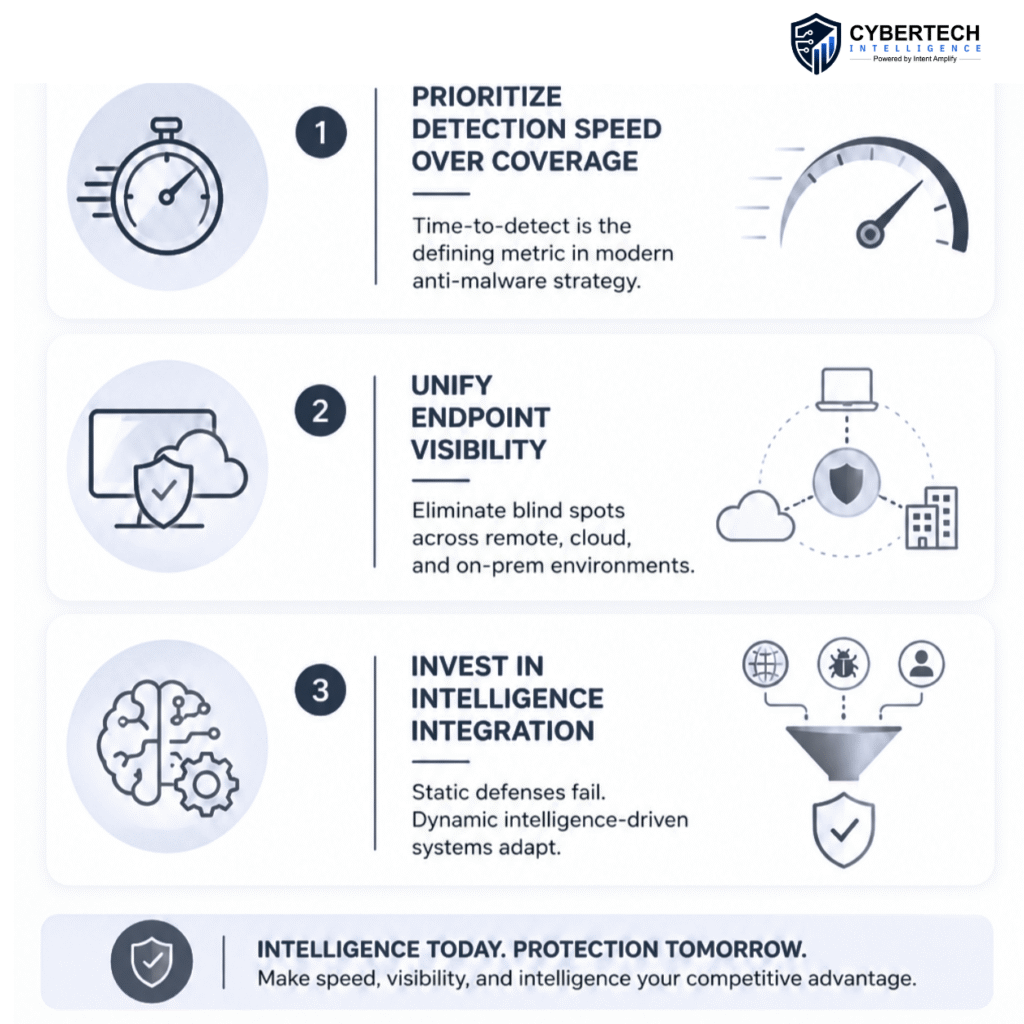
Organizations that have successfully contained malware threats are not relying on incremental upgrades. They are redesigning their defense architecture around speed, intelligence, and integration.
Speed of Detection Has Direct Implications for Financial Gain
Businesses employing the use of AI and automation can detect and manage breaches in 80 days quicker at a reduced breach cost of $1.9 million (34%), according to IBM.
Shailendra Upadhyay, Senior Research Principal at Gartner said, “Organizations are currently assessing their endpoint protection platform (EPP) and endpoint detection and response (EDR) needs and making adjustments to boost their operational resilience and incident response.”
The Generative AI Effect on Cyberattacks
According to Gartner, within the next few years, 17% of all cyberattacks and data breaches would be associated with generative AI technology.
Experts suggest that due to this trend, a considerable amount of money is going to be spent on software that addresses cybersecurity threats like application and data security and privacy.
Shadow AI is Emerging at a Great Expense
One out of every five companies analyzed (20%) suffered breaches associated with shadow AI, which refers to the use of AI systems without organizational authorization or oversight from the IT department.
This contributed up to $670K per breach and was responsible for the exposure of PII and intellectual property.
Conclusion
Malware is evolving faster than traditional defenses can adapt. Organizations that treat anti-malware as a foundational control rather than a strategic priority are already behind.
The first line of defense is an active, intelligence-driven system that determines whether an attack succeeds or fails in its earliest stages.
The gap between detection and impact is shrinking. The organizations that close that gap will define the next phase of cybersecurity resilience.
Command the narrative. Subscribe to Cyber Tech Intelligence for real-time dispatches that keep you three moves ahead.
FAQs
1. What makes anti-malware technology the first line of defense in today’s cybersecurity?
Anti-malware technology detects and mitigates threats right at their moment of occurrence, such as infostealer and loader infections, preventing escalation into credential stealing, lateral movements, and exfiltrations. In the case of lacking anti-malware, downstream solutions become purely reactive in nature.
2. How is the increasing trend toward artificial intelligence impacting the evolution of anti-malware technologies?
The rapidly growing rate of malware creation and evasion via artificial intelligence requires enterprises to implement behavior-based and AI-enabled anti-malware solutions since static and signature-based detections are no longer effective.
3. How can the effectiveness of anti-malware software in preventing ransomware attacks be demonstrated?
Anti-malware software identifies and thwarts attempts to launch ransomware, detecting such activities as payload download, privilege escalation, and file staging. As a result, full encryption is prevented, minimizing damage done.
4. What are the limitations of using traditional endpoint security products against contemporary malware?
Such products require updating in advance and rely upon known malware signatures, making them unable to detect rapidly morphing, fileless, and self-spreading threats that use legitimate system utilities to hide from detection.
5. What recommendations can be made for CISOs about enhancing modern anti-malware capabilities?
Among other issues, CISOs need to pay attention to timely detection, endpoint visibility and coordination, and threat intelligence correlation.
To share your insights, please write to us at news@intentamplify.com
🔒 Login or Register to continue reading