Executive Summary
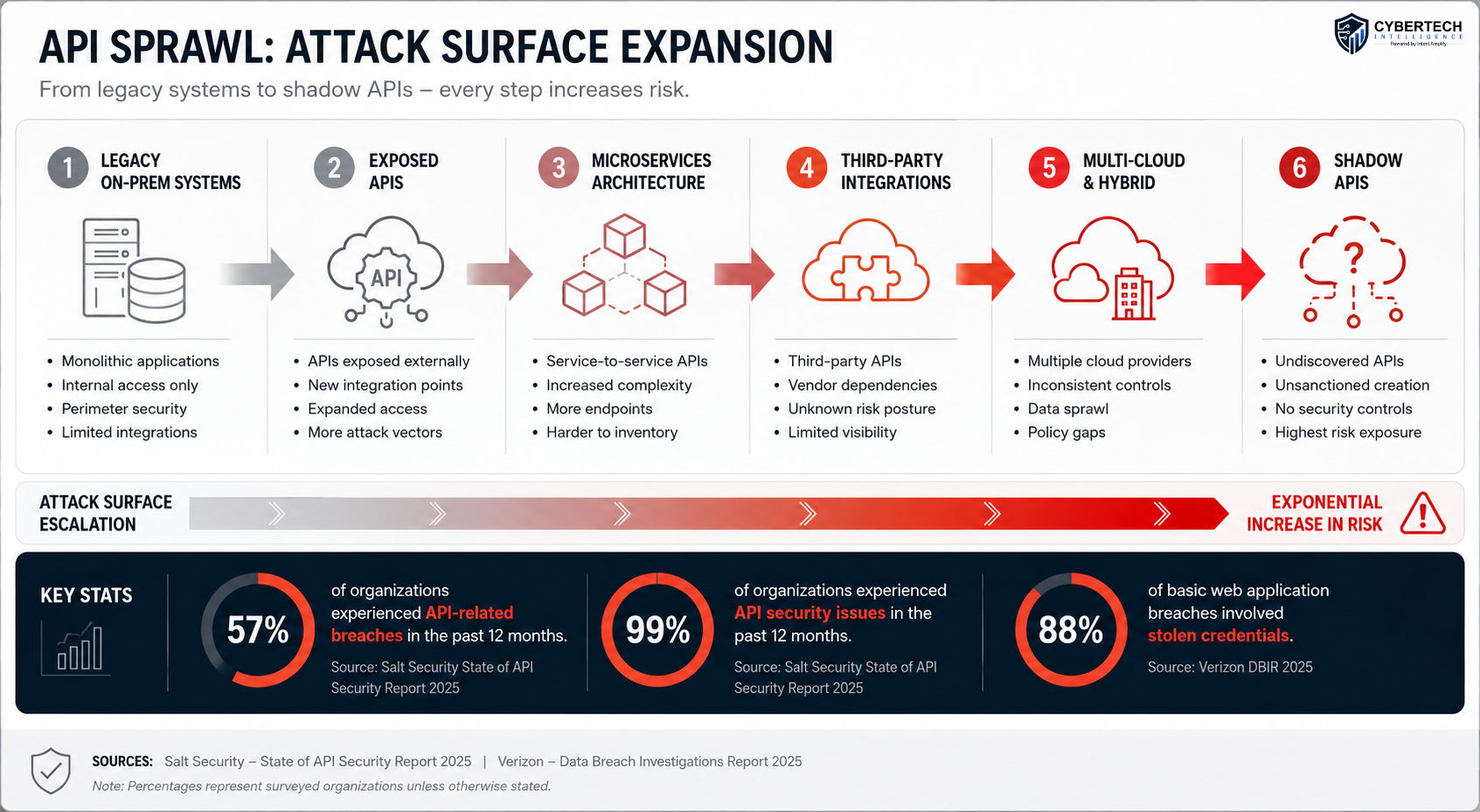
Most security professionals continue to regard APIs as an application-layer issue. However, today, APIs form the connective tissue within hybrid IT ecosystems encompassing cloud services, partner connections, AI offerings, internal microservices, and older technologies not originally meant to be accessed at internet scale.
The magnitude of the challenge can no longer be overlooked.
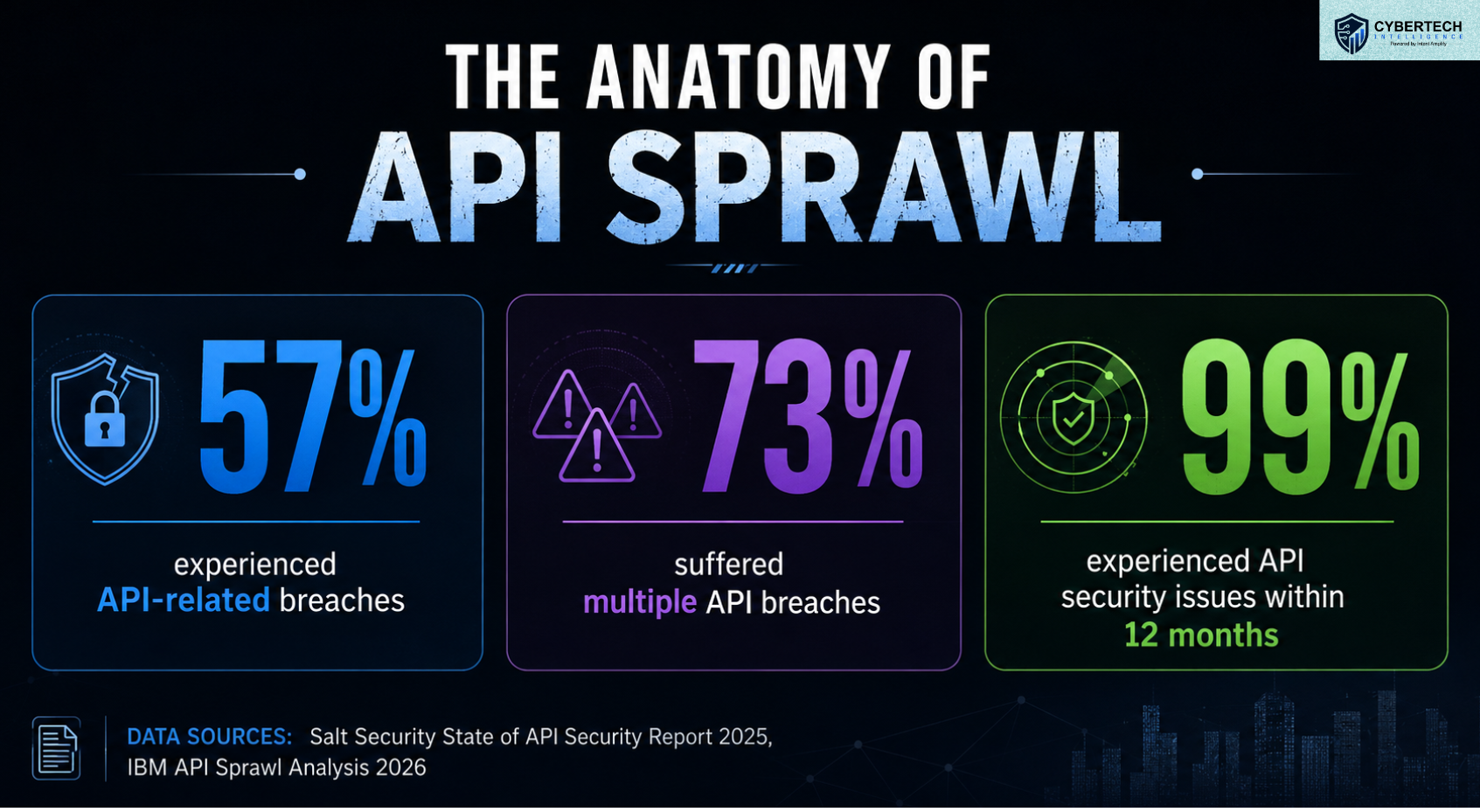
- 99% of respondents had experienced API security incidents during the last year 1
- 57% reported data breaches due to API vulnerabilities during the past two years. At the same time 1
- 88% of simple web application attacks that resulted in data breaches exploited credentials of users or access to paths revealed via public-facing applications and APIs 2
It’s hard for most companies to track the number of their APIs, which API exposes sensitive information, or even what shadow endpoints were developed outside governance processes.
The API Inventory Problem
The first question we ask during architecture reviews is deceptively simple: “How many APIs do you actually have?” In most enterprises, nobody can answer with confidence.
Security teams typically provide one number. Platform engineering provides another. Development teams often maintain undocumented internal APIs that never appear in governance inventories. Acquisitions introduce inherited integrations.
Third-party SaaS deployments generate unmanaged connections. Before long, the organization is operating hundreds or thousands of API endpoints that no single team fully understands.
Salt Security’s State of API Security Report 2025 found that API sprawl continues to accelerate across enterprise environments, with organizations struggling to inventory and monitor undocumented APIs.
IBM’s 2026 analysis of API sprawl reported that 57% of organizations suffered API-related breaches within two years, and 73% of those experienced multiple incidents. 3
This is where most conversations about “visibility” become dangerously superficial.
The OWASP API Security Top 10 continues to identify broken object-level authorization (BOLA), broken authentication, excessive data exposure, and improper asset management as dominant API risks.
Public-facing APIs effectively function as continuously exposed attack surfaces. If the inventory process fails, the defending side will be unable to differentiate between genuine integration traffic and reconnaissance activity.
One of the largest myths that we hear is the idea that an API gateway solves all discovery issues. They do not.
Gateways only govern traffic that actually passes through them. Shadow APIs created outside standard CI/CD workflows frequently bypass centralized inspection entirely.
In practice, the inventory problem is not just technical. It is organizational.
Development teams prioritize deployment speed. Infrastructure teams focus on uptime. Security teams focus on control. Business units prioritize integration velocity.
The result is fragmented ownership over a rapidly expanding API ecosystem.
How Hybrid Architecture Amplifies Exposure
Hybrid infrastructure has fundamentally changed the economics of attack surface management.
Ten years ago, most enterprise APIs lived inside relatively centralized environments. Today, APIs move across public cloud platforms, Kubernetes clusters, SaaS integrations, edge deployments, and AI-driven application pipelines simultaneously.
The average enterprise environment now contains a mix of:
- Legacy on-prem applications
- Multi-cloud workloads
- SaaS business platforms
- Internal microservices
- Third-party partner APIs
- External developer ecosystems
- AI and automation services
Each integration layer introduces additional trust dependencies.
This is where hybrid complexity becomes an adversarial advantage.
The IBM X-Force Threat Intelligence Index 2025 documented a continuing shift toward identity-focused attacks and credential abuse.
Simultaneously, IBM’s 2026 threat research identified a 44% increase in attacks targeting public-facing applications and APIs. 4
This is a dominant pattern in architecture assessments. Security teams often apply strong controls to internet-facing production systems while overlooking east-west API communication inside hybrid environments. Attackers understand this asymmetry extremely well.
Once adversaries compromise one identity or workload, APIs frequently provide the fastest path for lateral movement.
NIST SP 800-204 on microservices security specifically warns that distributed service architectures create expanding trust boundaries requiring continuous authentication, authorization, and monitoring controls.
Unfortunately, many enterprises still treat internal APIs as inherently trusted.
Deloitte’s cyber and cloud transformation research continues to show that enterprises are accelerating hybrid cloud deployments faster than governance programs can mature.
The operational reality is that security architectures designed for centralized infrastructure rarely scale cleanly into distributed API ecosystems.
Attackers do not need to breach every control layer. They only need to identify the least governed integration point.
The 2025 DBIR additionally highlighted growing third-party involvement in breaches. That matters enormously for API security because APIs increasingly represent the connective tissue between enterprises and external ecosystems.
Shadow APIs: The Adversary’s Favourite Entry Point
Attackers consistently discover undocumented APIs before defenders do.
That is the uncomfortable reality most enterprises still underestimate.
Shadow APIs emerge through abandoned development projects, rushed integrations, forgotten staging environments, deprecated mobile application versions, and temporary business workflows that quietly become permanent.
Unlike officially managed APIs, shadow endpoints rarely receive:
- Runtime monitoring
- Security testing
- Schema validation
- Authentication reviews
- Asset ownership assignment
- Logging oversight
From an attacker’s perspective, they are ideal targets.
The Salt Labs State of API Security Report Q1 2025 reported that organizations continue to struggle with API governance and runtime visibility, despite increased investment in API security tooling.
At the same time, Verizon DBIR 2025 reinforced that stolen credentials and exposed application interfaces remain dominant breach enablers.
Cyber Tech Intelligence has observed that attackers identify forgotten APIs through simple reconnaissance techniques, including:
Attackers have demonstrated a marked shift towards stealth-based attack techniques focused on authentic credentials and noiseless persistence.
APIs are highly desirable for such an offensive approach since requests from a compromised system often mimic legitimate application requests.
Contemporary attackers do not seek out malware execution at all times.
They want authenticated access, persistence in trusted workflows, and lateral movement that does not alarm perimeter defenses.
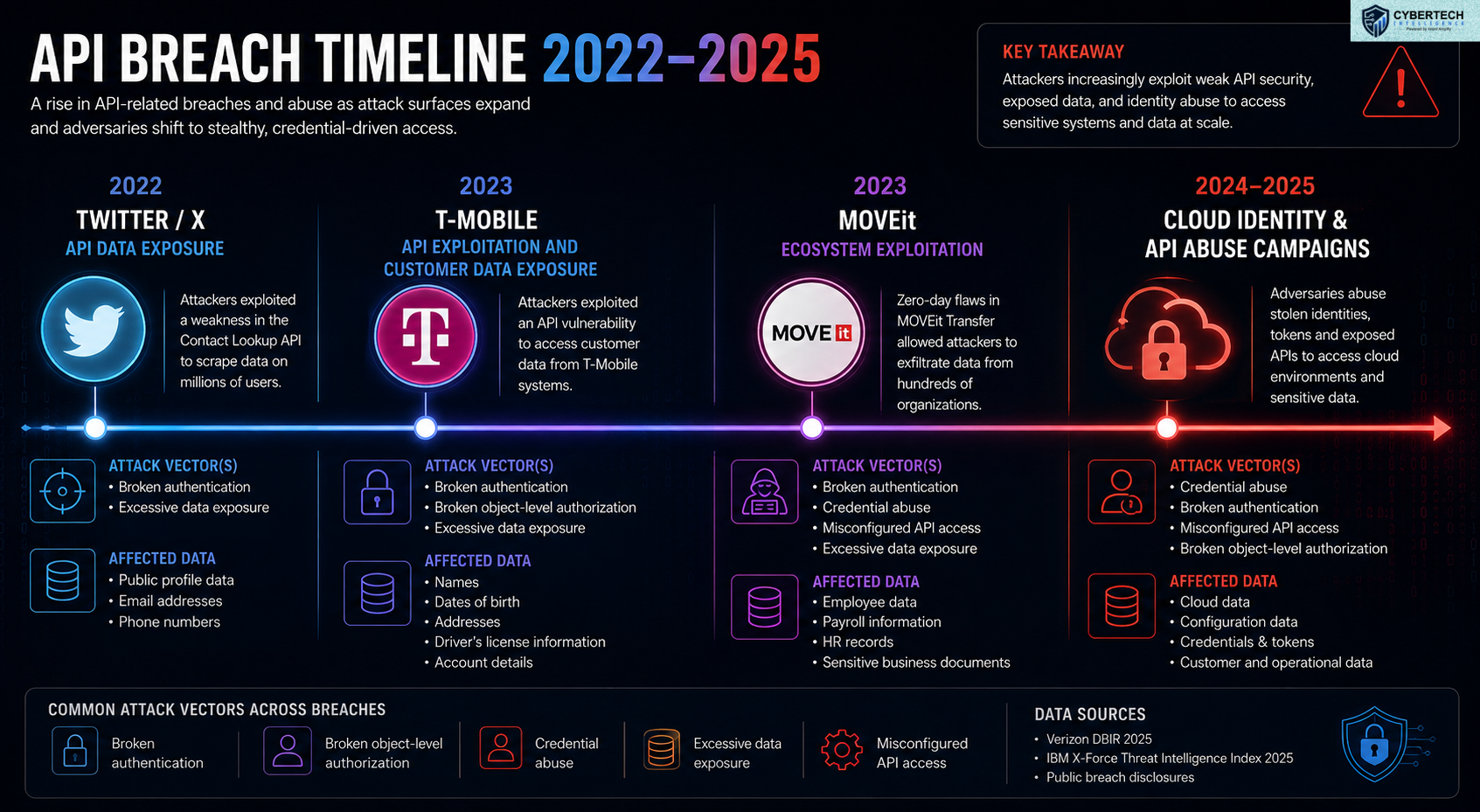
Reconnaissance against shadow APIs can be performed using public GitHub repositories, exposed Swagger documentation, JavaScript code analysis, mobile app reverse engineering, certificate transparency logs, and endpoint enumeration. None of these approaches requires advanced capabilities.
That is precisely what many organizations are unaware of. An undocumented API is not unseen by attackers. It is unseen by defenders alone.
What Real API Security Should Look Like
The modern enterprise perimeter has shifted towards API-centricity.
Accordingly, the OWASP API Security Top 10 continues to prioritize broken object-level authorization, broken authentication, unrestricted resource consumption, and improper asset management as the greatest API-related security risks faced by enterprises.
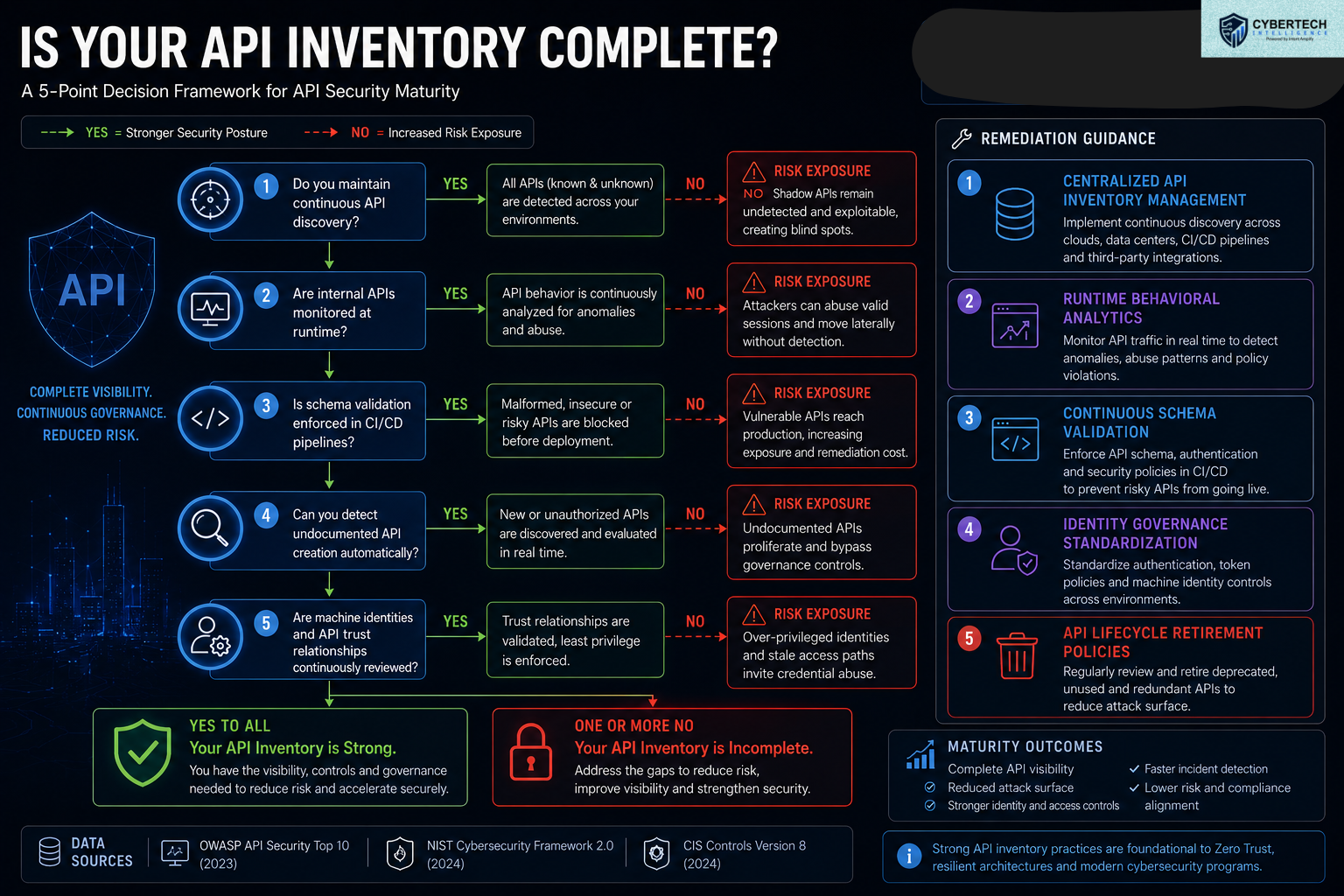
NIST CSF 2.0 and CIS Controls 8.0 further emphasize the importance of operational continuity of API inventory visibility, identity governance, and monitoring.
The organizations operating most efficiently tend to embrace all five of the following:
1. Continuous API Discovery
Static inventories quickly become irrelevant.
Good practices require continuous discovery of all relevant APIs across cloud-based systems, CI/CD pipelines, Kubernetes clusters, third-party partner ecosystems, and shadow API stacks.
Continuous discovery is required since APIs are increasingly found outside central API governance processes.
When you can’t keep your inventory updated continuously, it’s out of date from day one.
2. Runtime Behavioral Monitoring
Classical approaches to perimeter monitoring fail for modern API environments.
Hackers have moved to operating through authenticated sessions and normal traffic. The following anomalies can be found by using runtime behavioral analysis:
- Abnormal authentication activities
- Too much object enumeration
- Geographic anomalies in access attempts
- Anomalies in data extraction routines
- Privilege escalation attempts
Such anomalies cannot be found through static testing.
3. Identity-Centric Security Architecture
Almost all breaches via APIs include identity misuse.
- Hacked tokens
- Inadequate authentication controls
- Over-privileged accounts
- Overprivileged machines
It is therefore not surprising that identity governance plays an important role in today’s API security practices.
The most advanced organizations standardize on authentication frameworks and minimize credentials and machine privileges.
4. Schema Enforcement in Shift-Left
DevSecOps frameworks are increasingly embedding schema enforcement within their CI/CD processes. OpenAPI specs, automated testing, policy enforcement on authentication, and configuration scanning can significantly limit exposure before release.
This minimizes shadow API creation.
5. Data-Centric API Segmentation
Some APIs are riskier than others. Those companies that classify their APIs based on data sensitivity, trust levels, and business significance tend to react much faster to security events.
APIs providing access to sensitive customer information, financial, medical, or highly trusted system access need stricter monitoring and segmentation policies.
Another operational transformation that I think companies undervalue today is API lifecycle management.
The best companies proactively decommission APIs when no longer needed, decommission zombie APIs, continuously rotate machine credentials, and enforce proper trust level relationships. They view API minimization as a means to shrink the attack surface.
AI APIs and the Emerging Exposure Economy
The fast adoption of generative AI systems is causing API sprawl at a much higher rate than most companies can manage.
The result is a whole new form of operational exposure.
AI systems are built to use APIs. Large language models, copilots, orchestration tools, vector databases, retrieval systems, software-integrated AI services, and self-governing AI agents are all designed to interface via APIs.
With each new integration of AI systems within the company, new machine-level trust relationships and authentication requirements emerge.
The predominant measure of AI security is model risk assessment.
As IBM’s X-Force Threat Intelligence Index 2025 states, intruders are increasingly utilizing identities, tokens, and exposed application interfaces for stealthier cyberattacks at the same time.
More than 80% of enterprises will have adopted generative AI APIs or developed generative AI applications by 2026 4
Third-Party Integration and Supply Chain Risk
Enterprise systems no longer exist as standalone islands. They now exist as interconnected API ecosystems.
Each new external integration increases capabilities while at the same time exposing trust boundaries beyond the organization’s control.
Software vendors, SaaS platforms, payment processors, logistics systems, customer analytics tools, cloud providers, AI, development ecosystems, and other third parties interact via APIs.
This level of interconnectivity has completely changed the face of supply chain risk.
Verizon DBIR 2025 reported continued growth in third-party participation in data breaches for enterprise organizations. 2
Similarly, the IBM X-Force report noted the growing tendency for hackers to use trusted external connections as gateways to broader ecosystems.
Hackers target the weakest link in the chain, and not the main objective itself. The reason is the lack of consistent governance evaluation when dealing with third parties.
The 2023 MOVEit attacks are an example of the fast expansion of security issues throughout the software ecosystem. An API-based ecosystem makes such a spread even faster since machine-level trust scales much faster than manual governance review processes. 8
The NIST Cybersecurity Framework version 2.0 increasingly focuses on supply chain governance, continuous monitoring, and identity-driven security architectures, since the concept of trust is not scalable anymore.
The most successful companies in minimizing risks related to third-party APIs actively use:
- Mapping of vendor APIs
- Access recertification processes
- Machine identity management practices
- Runtime third-party traffic inspection
- Integration segmentation
- API lifecycle based on contracts
That is becoming vital, since cybercriminals have recognized something that most companies underestimate: Trusted integrations provide the fastest route to high-value environments.
API Governance Maturity for Operational Resilience
Most companies continue to assess cybersecurity maturity based on the purchase of defensive tools.
Operational resilience no longer relies primarily on how many cybersecurity products an organization deploys. The pace of change within API environments makes it impossible for fragmented governance strategies to succeed.
Organizations that best cope with increasing attack surfaces are those that streamline their operational control frameworks drastically.
Such organizations embrace:
- A centralized approach to identity governance
- API discovery
- Consistent telemetry standards
- Behavioral analysis during runtime
- Machine identity lifecycle management
- Policy enforcement
- Rapid API decommissioning
CIS Controls v8, NIST CSF 2.0, and OWASP all consistently emphasize the following operational reality:
You cannot protect assets you cannot govern continuously.
This operational reality is increasingly becoming an underpinning for resilience planning in enterprises today.
Those who embrace this early on will minimize their exposure to breaches, increase efficiency in incident response management, optimize compliance processes, and enhance their operational resilience all at once.
Those who ignore this will keep expanding their blind spots for attacks faster than they can possibly defend them.
Why Do Traditional Security Architectures Struggle with APIs?
Most traditional security architectures assumed an operational environment that no longer exists.
Security was built on static perimeters, centralized applications, predictable network boundaries, and relatively stable ownership models for infrastructure. APIs have shattered all of these assumptions.
Traditional perimeter security simply cannot adapt to that world.
In the 2025 Verizon DBIR report, we see that adversaries continue to target intrusions via credentials precisely because authenticating a user bypasses many traditional defense mechanisms.
APIs increase that challenge by ensuring that malicious traffic frequently mirrors valid application activity.
It results in a critical visibility gap.
Traditional security architectures have been built for detecting malicious activities that occur outside well-defined boundaries.
APIs have largely obfuscated those traditional boundaries. Many internal APIs operate across distributed cloud environments, containers, SaaS, and orchestration pipelines at the same time.
Autonomous API Security is the Future
Today’s API landscape is quickly outgrowing human capacity for governance. It is the challenge that companies must address head-on going forward.
Most major corporations already deploy thousands of APIs within their cloud environments, partner ecosystems, AI-based services, mobile apps, SaaS platforms, and internal microservices.
With increasing rates of AI-assisted software engineering, API proliferation will only continue to rise over the coming years.
Human-scale governance will no longer be sufficient.
Based on Gartner’s API security research and wider trends in enterprise automation, many businesses are turning towards automated API security, AI-based anomaly detection, and continuous identity management for managing distributed applications in today’s enterprise environment.
The future of API security governance will be determined by autonomous functions such as:
- Continuous API inventory
- Behavioral analysis in real-time
- Automated schema management
- Machine identity management
- Adaptive authentication controls
- Automated policy management
- Continuous trust relationship mapping
Credential stuffing attacks, API discovery techniques, token exploitation, endpoint scanning, and vulnerability probing all happen using automation. It is impossible to respond using purely manual security measures against an automated threat.
Regulatory Pressure Has Redefined API Governance
The discussion on API security has moved beyond purely technical considerations.
Regulation is now exerting equal pressure.
In recent years, authorities have made a turn from evaluating cybersecurity as a compliance topic to calling for tangible evidence of effective governance of data access, identity, incidents, and supply chains.
APIs play a prominent role here since they act as conduits for sensitive data exchange within enterprise architectures.
This has become relevant due to the transformation of APIs from purely engineering artifacts.
They are now regulated channels of data exchange.
IBM’s report, ‘Cost of a Data Breach,’ states that data breaches related to customer PII data and distributed cloud environments result in a much higher cost of remediation and increased compliance expenses. 3
Meanwhile, various regulatory frameworks like GDPR, SEC requirements on cybersecurity reporting, NIS2 Directive, etc., call for greater transparency regarding data exchanges.
APIs Are Now the Enterprise Attack Surface
Today’s enterprises leverage APIs for every business layer they possess. Their cloud infrastructure, SaaS ecosystem, artificial intelligence platforms, mobile apps, partner integrations, customer platforms, internal microservices, and machine identities – all of these business layers rely on APIs operating 24/7.
That operational dependency is shifting cybersecurity risk in fundamental ways.
What security executives need to recognize is that API security isn’t a specialization in application security anymore.
It is enterprise infrastructure security.
While today’s most vulnerable enterprises aren’t necessarily the ones with poor perimeter defense mechanisms, they do increasingly become those that operate rapidly growing and unmanaged API ecosystems.
References
- Salt Security. State of API Security Report Q1 2025. February 2025.
- Verizon Communications. 2025 Data Breach Investigations Report (DBIR). April 2025.
- IBM. What Is API Sprawl? 2026.
- Gartner. Emerging Tech Impact Radar: Generative AI Security. 2025.
- IBM. X-Force Threat Intelligence Index 2025. April 2025.
🔒 Login or Register to continue reading












