A new era of cyber threats is rising with sophisticated malware facilitated by artificial intelligence (AI) capabilities. By improving the identification and reaction to emerging threats, the integration of AI into malware analysis is transforming the cybersecurity landscape. Advanced analytical techniques are becoming crucial as cybercriminals use AI technologies to develop more dynamic and complicated malware.
Major vulnerabilities within businesses result from the inability of traditional signature-based detection techniques to recognize new and polymorphic malware outbreaks. Major vulnerabilities within businesses result from the inability of traditional signature-based detection techniques to recognize new and polymorphic malware outbreaks.
Since traditional methods struggle against increasingly complex and sophisticated malware, this makes AI-enhanced malware analysis essential. Unlike traditional malware, which depends on fixed and defined attack methods, AI-enhanced malware can modify, adapt, and learn from its environment. Furthermore, due to its flexibility, it may alter its tactics, methods, and procedures (TTPs) in real time to avoid being discovered by traditional security measures, making it incredibly elusive. By applying machine learning (ML) and deep learning approaches, AI-enhanced malware analysis can improve detection rates and provide deeper insights into the traits of potential threats.
Understanding AI-Enhanced Malware
Malicious software that uses AI technology to increase its efficacy and evasion skills is referred to as AI-enhanced malware. This kind of malware is far more advanced than traditional malware since it can change, adapt, and learn from its surroundings. These technologies have the potential to greatly increase detection rates and offer a more in-depth understanding of the traits of possible threats.
Recommended: Magentai Launches AI-Powered Cybersecurity for Businesses
AI-enhanced malware’s ability to adapt, automate, and customize attacks makes it a serious cybersecurity threat. AI-enhanced malware poses a significant cybersecurity risk due to its ability to adapt, automate, and modify assaults. Organizations must understand their characteristics to develop effective defenses that can adapt to these evolving threats. Protecting sensitive data and preserving operational integrity will require a proactive and flexible strategy for cybersecurity as cybercriminals use AI technology more and more.
Key Characteristics of AI-Enhanced Malware
AI-enhanced malware is a major development in cyber threats, utilizing cutting-edge technologies to increase efficacy and circumvent conventional security protocols. Understanding its characteristics and implications is crucial for developing effective defenses.
Here are a few characteristics of AI-enhanced malware:
1. Polymorphic Behavior
Malware produced by AI frequently demonstrates variability in form, which enables it to continuously alter both its appearance and code. It is more difficult to detect and prevent thanks to this capacity, which allows it to avoid detection by conventional antivirus programs that use static signatures.
2. Autonomous Learning and Adaptation
Unlike conventional malware, AI-enhanced variants can autonomously learn from their environment. They analyze network configurations and user behaviors to modify their attack strategies in real-time, becoming more efficient and dangerous with each iteration.
Recommended: Top 10 Emerging Cybersecurity Technologies for 2025
3. Targeted Attacks
Malware using AI capabilities can carry out extremely focused attacks by examining user information and system weaknesses. This personalization increases the chance of a successful infection, as the malware can craft attacks specifically suited to particular users or systems.
4. Automation and Scalability
AI makes it possible to automate various stages of a cyberattack, from planning to carrying it out in a sophisticated manner. Eventually, this makes it possible for attackers to launch several targets at once, thereby expanding the scope and impact of their operations.
5. Speed and Evasion Techniques
AI-generated attacks operate at machine speed, executing actions in milliseconds to minimize detection windows. Additionally, they employ advanced evasion techniques, such as mimicking legitimate processes or altering their behavior based on real-time analysis of defenses.
Types of AI Malware
1. Adaptive Malware
Adaptive malware can change its appearance or behavior automatically to avoid detection. To make consistent detection efforts more difficult, it might, for example, link to an AI service to create new code or alter its execution procedures.
2. Intelligent Ransomware
This type of malware maximizes its impact while reducing the amount of time available for reaction by identifying the most valuable assets within a network before encrypting them. Their complexity puts conventional anti-ransomware systems to the test, making them useless against changing cybercriminals’ strategies.
3. Deepfake Social Engineering
Through the use of AI, attackers may produce realistic impersonations via various means, such as text messages, audio, or video, enhancing the effectiveness of social engineering attacks.
Recommended: Cybersecurity Simplified: What is Cybersecurity in 2025?
AI’s Role in Malware Detection
The integration of AI into malware detection has played a crucial role in addressing the limitations of traditional detection methods. Machine learning methods allow systems to learn from large data sets and spot trends that could be signs of criminal activity.
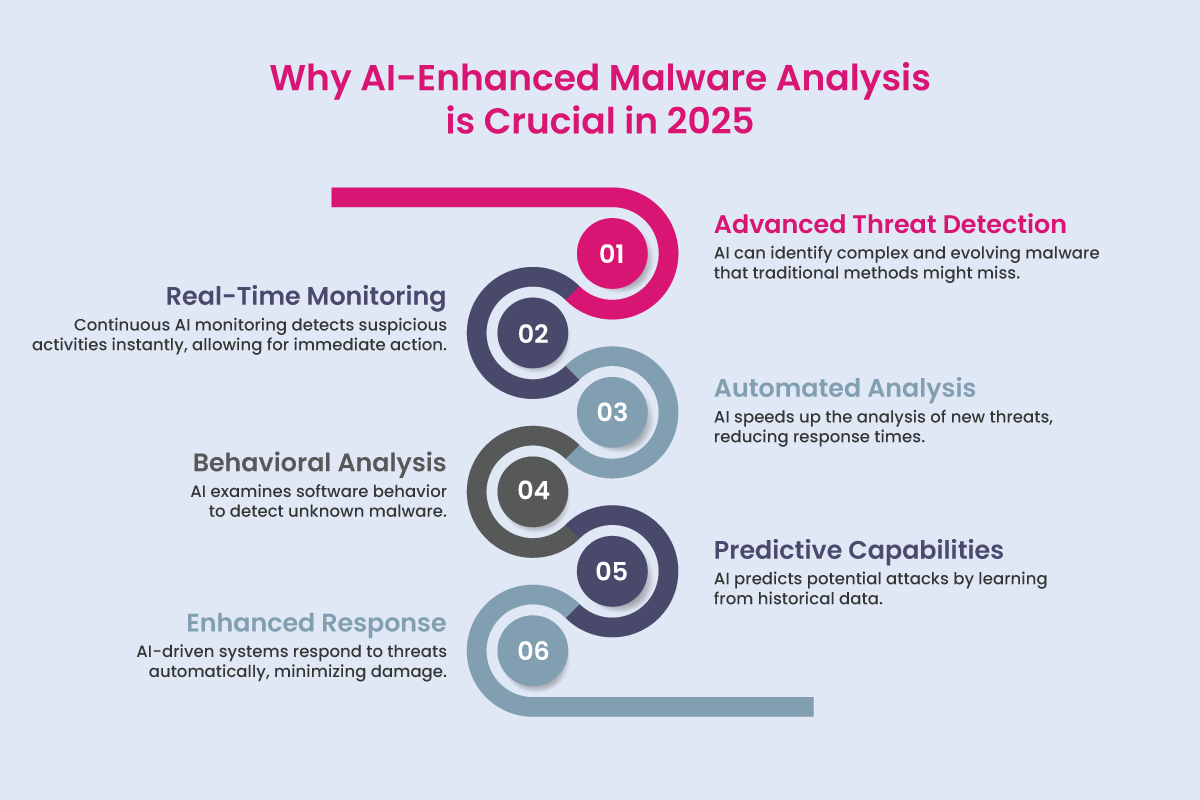
By using many crucial strategies, AI greatly enhances malware analysis’s detection capabilities:
1. Anomaly-Based Detection
AI uses anomaly detection, unlike conventional signature-based techniques that depend on known malware signatures to find departures from typical behavior. This method is effective when it comes to defeating zero-day attacks and polymorphic malware that can elude conventional defenses.
2. Machine Learning Techniques
Numerous machine learning techniques, including Support Vector Machines (SVMs), Random Forests, Neural Networks, and improved Intrusion Detection Systems (IDS), are utilized in artificial intelligence (AI). By employing learned patterns to identify new, unknown data, these systems can increase the accuracy of detection.
3. Deep Learning Applications
For both static and dynamic malware analysis, sophisticated deep learning models such as Convolutional Neural Networks (CNNs) and Recurrent Neural Networks (RNNs) are used. These models detect malicious activity in real-time by analyzing system calls and binary files.
Recommended: Cybersecurity Simplified: LLMjacking Attacks
Challenges with AI-Generated Malware
The emergence of AI-generated malware presents unique challenges:
1. Autonomous Adaptation: Malware with AI capabilities might change its strategies automatically in response to security measures, making it more difficult to identify. This feature enables it to tailor attacks according to the surroundings it comes into contact with.
2. Polymorphism and Obfuscation: These malicious programs frequently display polymorphism characteristics, changing their code automatically with every replication. As traditional signature-based methods cannot keep up with the volume of variants produced, this constant mutation makes detection efforts more difficult.
Organizations can identify anomalies that point to the existence of malware by monitoring user and system behavior patterns. AI improves this process by continuously improving its comprehension of typical vs. abnormal activity.
Strategies for Mitigating AI Threats
Businesses are using more proactive tactics to counteract changing cyber threats. Instead of only reacting to accidents after they happen, these tactics emphasize prevention and early detection.
Here are some key strategies for mitigating AI threats:
1. Behavioral Analytics: By monitoring user and system behavior patterns, organizations can identify anomalies indicative of malware presence. AI enhances this process by continually updating its understanding of normal versus suspicious activity.
2. Predictive Modeling: Implementing AI-driven threat prediction models allows organizations to anticipate potential attack vectors and evasion tactics based on emerging trends in malware behavior.
3. Automated Incident Response: AI plays a crucial role in automating incident response processes, enabling rapid identification and mitigation of threats as they arise.
Recommended: Cyber Insurance: Risks and Trends 2025
Implications for Cybersecurity
The rise of AI-enhanced malware presents significant implications for cybersecurity and necessitates a shift in cybersecurity strategies. Moreover, it fundamentally alters the threat landscape.
- Businesses need to implement sophisticated detection systems that make use of behavioral analytics and machine learning.
- Anticipating and mitigating such attack vectors requires proactive protection tactics.
- Security measures must be continuously adjusted to keep up with the constantly changing nature of these threats.
Organizations can improve their cybersecurity posture and better address changing threats by implementing proactive strategies like behavioral analytics and predictive modeling. Using cutting-edge detection methods and adjusting to ever-changing threats can help organizations greatly strengthen their defenses against more complex malware.
Conclusion
A significant shift in the cybersecurity environment is marked by the emergence of AI-enhanced malware, which poses serious obstacles to conventional defenses. Modern cybersecurity tactics must include AI-enhanced malware analysis. Static signature-based techniques are useless against AI-enhanced malware because of their real-time learning and evolution capabilities, which enable them to avoid detection. This flexibility not only makes spotting these threats more difficult, but also raises the potential impact of successful strikes.
Recommended: Data Quality: The Unseen Barrier to AI’s ROI and Sustainability in 2025
As cybercriminals use AI technology to develop dynamic and complex malware, organizations need to modify their tactics to combat these new threats. To address these issues, businesses need to use sophisticated analytical methods that make use of deep learning and machine learning (ML). Malware and detection technologies are always evolving, which emphasizes the necessity of constant innovation in cybersecurity procedures.
It is crucial to comprehend AI-enhanced malware to create strong defenses against its complex strategies. A proactive and flexible approach will be essential for protecting sensitive data and preserving operational integrity in an increasingly digital world as the landscape of cyber threats continues to change.
FAQs
1. How are AI-driven cyberattacks different from traditional cyber threats?
AI-driven attacks adapt in real time, automate decision-making, and scale rapidly across targets. Unlike traditional threats that follow fixed patterns, they evolve during execution, making detection and response significantly harder.
2. Why are phishing attacks becoming harder to detect in 2026?
Modern phishing leverages AI to generate highly personalized, context-aware messages using real user data. These attacks mimic communication styles and workflows, bypassing traditional filters and reducing human suspicion.
3. What makes AI-powered ransomware more dangerous for enterprises?
AI-powered ransomware identifies high-value assets, adapts encryption strategies, and minimizes detection windows. This increases operational disruption and financial impact, especially in sectors like healthcare and financial services.
4. How can organizations defend against AI-enhanced malware and attacks?
Organizations need behavior-based detection, AI-assisted security tools, zero-trust architecture, and continuous threat modeling. Static, signature-based defenses are no longer sufficient against adaptive threats.
5. What are the biggest cybersecurity risks of AI adoption for US enterprises?
Key risks include data poisoning, model manipulation, automated attack scaling, and supply chain vulnerabilities. Without governance and visibility, AI systems can introduce new attack surfaces across the enterprise.
To share your insights, please write to us at news@intentamplify.com
🔒 Login or Register to continue reading












