Executive Summary
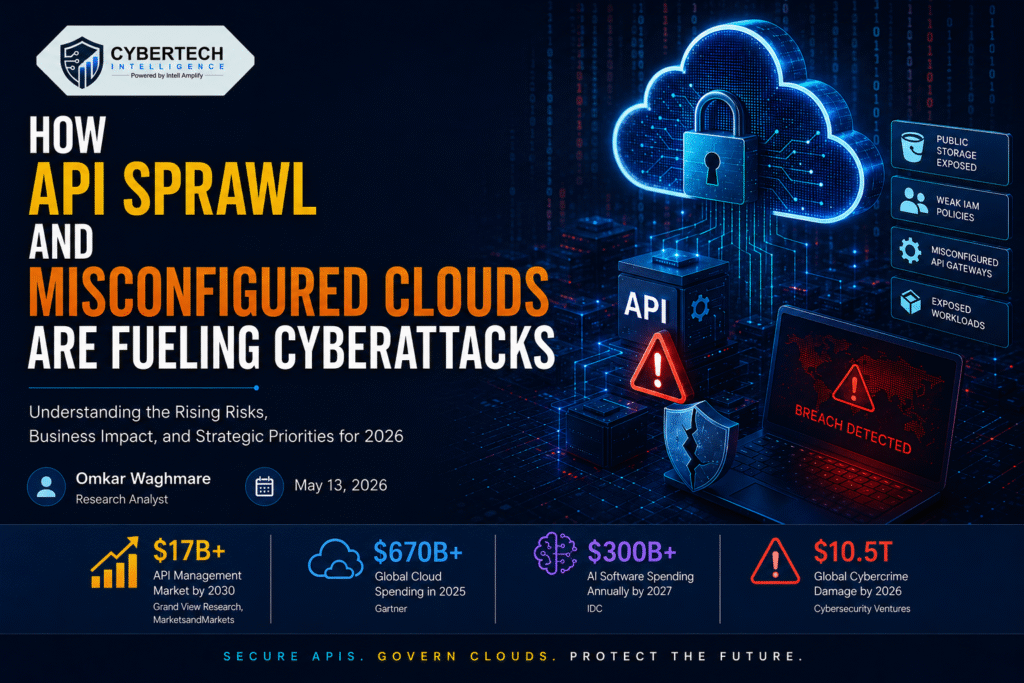
The enterprise attack surface has been growing at an unprecedented pace as companies expedite their use of APIs, cloud-native architecture, software-as-a-service (SaaS) solutions, and artificial intelligence (AI)-powered applications. By 2026, API sprawl and cloud misconfigurations will emerge as the two most exploited cybersecurity vulnerabilities.
As per IBM, 82% of businesses rely on internal APIs, whereas 71% depend on external APIs (1)
However, the reality is that cloud security professionals still struggle with inadequate identity policies, public storage buckets, faulty API gateways, and poorly governed workloads.
The increasing adoption of APIs alongside inadequate cloud governance is providing malicious actors with an opportunity to penetrate enterprise networks at an accelerated pace.
In this exclusive insight report, we explore the implications of API sprawl and cloud misconfigurations on the cyber threat landscape, the reasons behind the escalating attacks against cloud-native architectures, and the measures that enterprise decision-makers should take in 2026.
Economic Growth That Has Fueled the API Economy
The global API economy has seen significant growth in the past five years owing to rapid digital transformation investments.
According to market research estimates from Grand View Research and MarketsandMarkets, the global API management market was estimated at around $5.1 billion in 2023. (9)
And it is projected to grow beyond $17 billion by 2030, driven by cloud-native applications, AI integrations, fintech ecosystems, and SaaS implementations. (10)
Moreover, enterprise spending on cloud infrastructure has grown aggressively.
According to the enterprise spending forecast by Gartner and IDC, industry cloud investments have crossed $670 billion globally in 2025. (11)
Whereas enterprise spending related to AI-powered software products is forecasted to reach over $300 billion annually by 2027 due to growing investment in AI and automation. (12)
This growth has been driving massive development of APIs.
Nowadays, financial institutions, healthcare providers, retailers, telecom companies, and manufacturers depend on APIs to support:
- Customer engagements
- Payment systems
- AI-powered analytics
- Supply chain visibility
- SaaS integrations
- Real-time transaction processing
- Autonomous business workflows
The monetization value tied to APIs is also increasing.
Large technology providers now generate billions of dollars annually from API-driven ecosystems.
Cloud providers continue to report strong enterprise growth linked directly to API and AI consumption models.
For instance:
- Microsoft indicated that its cloud services revenue was $77.7 billion and increased 18%. (13)
- AWS Net income increased to $77.7 billion in 2025. (14)
- Google Cloud’s revenue exceeded $43 billion in 2025. (15)
The massive growth in cloud and API dependency is significantly expanding the enterprise attack surface.
The Rise of API-Centric Enterprises
APIs have become the digital backbone of modern enterprises. Every mobile application, cloud platform, AI service, fintech integration, healthcare portal, and customer-facing application now depends on APIs to exchange data and enable real-time connectivity.
According to IBM, most of today’s dynamic traffic on the Internet is created using APIs rather than traditional web applications. (1)
The transition to microservices, multi-cloud architectures, and artificial intelligence (AI) has driven tremendous growth in APIs from 2020 to 2026. Companies are implementing more APIs than security teams can track, monitor, or manage.
API sprawl is described by Akamai as the unrestricted spread of APIs within organizations without centralized management, governance, or security controls. (2)
This problem has intensified due to several enterprise trends:
- Rapid cloud migration programs
- Increased SaaS adoption
- AI integration into enterprise workflows
- Expansion of partner ecosystems
- Multi-cloud and hybrid cloud architectures
- DevOps and agile software delivery cycles
- Remote workforce enablement
With innovation taking priority over security, organizations are struggling to govern their API usage effectively.
Companies now have thousands of APIs deployed in cloud-based infrastructures, legacy IT systems, third-party platforms, and internally developed software. Many of these APIs are undocumented, outdated, idle, or insecure
Security teams are increasingly dealing with:
- Shadow APIs
- Zombie APIs
- Unauthenticated endpoints
- Inconsistent API authentication controls
- Exposed API keys
- Weak rate limiting
- Broken object-level authorization
- Poor API inventory visibility
This lack of centralized visibility creates ideal conditions for attackers.
Why APIs Have Become Prime Cyberattack Targets
Cybercriminals are aggressively targeting APIs because APIs directly expose sensitive business logic and valuable enterprise data.
Unlike traditional web applications, APIs often:
- Operate continuously
- Handle sensitive transactions
- Communicate machine-to-machine
- Bypass conventional user interfaces
- Receive less security testing
- Have inconsistent authentication enforcement
But per the OWASP API Security Project, some of the most significant API threats are broken authentication, Broken object level authorizationSecurity Misconfiguration. (3)
While most of the companies are fighting to establish their footing on the periphery, APIs are continuously spreading beyond the periphery governed from above.
Hackers capitalize on that.
Akamai finds that deploying unmanaged APIs exposes the risk of security breaches, leaking information, and exposing infrastructure to threats. (2)
In cloud-native use cases where APIs are used to connect workloads spanning several clouds, this challenge is even more constraining.
By 2026, cybercriminals will leverage automation and advanced reconnaissance tools enabled by AI to discover:
- Publicly exposed APIs
- Weak authentication tokens
- Hardcoded credentials
- Misconfigured API gateways
- Exposed cloud storage services
- Vulnerable cloud functions
- Unpatched containers
AI-powered cyberattacks will enable hackers to exploit vulnerabilities more rapidly than their defenses. (4)
The use of artificial intelligence is significantly lowering the time difference between the detection of a vulnerability and its exploitation.
Cloud Misconfiguration Is Growing the Attack Surface
Cloud computing usage is expanding rapidly worldwide.
All industries, including banks, hospitals, manufacturers, retailers, telecommunication providers, and governments, are rapidly transitioning to cloud platforms.
However, cloud management and oversight are inconsistent.
Misconfigurations of cloud settings are now one of the most common sources of modern data breaches.
Palo Alto Networks points out that cloud security misconfiguration is one of the top API security risks and arises when cloud infrastructures, APIs, applications, or security configurations are improperly configured. (5)
Common cloud security misconfigurations in 2026 include:
- Publicly exposed cloud storage buckets
- Weak IAM policies
- Excessive access permissions
- Exposed Kubernetes dashboards
- Open cloud management ports
- Misconfigured API gateways
- Improper encryption settings
- Unrestricted serverless functions
- Insecure CI/CD pipelines
- Weak secret management practices
The complexity of multi-cloud environments is worsening the issue.
Today, many companies are operating within the confines of AWS, Microsoft Azure, Google Cloud, Oracle Cloud, and even the private cloud.
This has resulted in policy contradictions and oversight problems.
In a study analyzing the trends of cloud attacks, it was found that attackers are increasingly using cloud vulnerabilities involving identity rather than the traditional approach of malware-induced intrusions. (6)
Credential abuse, cloud token thefts, and abuse of APIs have become more common since these provide a covert entry point for attackers into what would otherwise be legitimate environments.
This is a clear strategic paradigm shift in cybercrime.
Rather than forcefully breaking through the defenses, attackers are increasingly taking advantage of cloud trust, cloud identities, and cloud APIs.
The Consequences for Businesses of Failed API/Cloud Security
The business implications of cybersecurity risks arising from APIs and cloud-based services are becoming increasingly dire.
Studies from the IMF report that cybercrime will cost the world $23 trillion in 2027, an increase of 175% from 2022. (16)
Businesses suffering from API-based cyber-attacks now have increasing costs of recovery as a result of:
- Regulatory fines
- Customer compensation
- Legal exposure
- Incident response spending
- Revenue disruption
- Cloud downtime
- Third-party remediation costs
Large-scale breaches involving cloud environments have already resulted in settlements and losses worth hundreds of millions of dollars globally between 2023 and 2026.
Cloud outages and API failures also create a direct sales impact.
E-commerce, fintech, and SaaS companies can lose millions in transaction revenue within hours when APIs fail or become compromised.
Research across enterprise cloud environments indicates that organizations with major API disruptions often experience:
- Reduced customer retention
- Increased operational recovery costs
- Delayed digital transformation programs
- Higher cyber insurance premiums
- Declining investor confidence
As enterprise revenue streams become increasingly dependent on cloud-connected digital services, cybersecurity resilience is becoming directly linked to long-term business valuation.
The financial and operational consequences of API and cloud security failures are escalating rapidly.
When APIs are compromised, attackers can gain direct access to:
- Customer records
- Financial transactions
- Healthcare information
- Authentication systems
- Internal business logic
- Supply chain platforms
- Cloud workloads
- AI systems and datasets
This exposure creates both immediate operational disruption and long-term reputational damage.
Enterprises today face multiple layers of risk:
Regulatory Risk
Global data protection regulations are becoming stricter.
Organizations operating across regions must comply with frameworks such as:
- GDPR
- HIPAA
- PCI DSS
- DORA
- India’s Digital Personal Data Protection Act
- SEC cybersecurity disclosure rules
Misconfigured APIs and cloud services can directly trigger compliance violations.
Wiz highlights that API compliance failures often emerge due to weak authentication, poor encryption controls, insufficient logging, and inadequate access governance.(7)
Financial Risk
Cloud and API incidents can lead to:
- Revenue disruption
- Ransomware exposure
- Incident response costs
- Regulatory fines
- Customer churn
- Brand damage
- Business downtime
The average financial impact of cloud-related breaches continues to rise as organizations centralize critical operations in cloud-native ecosystems.
Operational Risk
API outages and cloud misconfigurations can disrupt entire digital ecosystems.
Modern enterprises depend on APIs for:
- Customer authentication
- Payment processing
- Mobile applications
- AI integrations
- Supply chain visibility
- SaaS connectivity
- Partner collaboration
Even minor API security failures can create cascading operational disruptions across multiple business units.
AI Is Intensifying the API Security Crisis
Artificial intelligence is accelerating both innovation and cyber risk.
Organizations are rapidly integrating generative AI and autonomous AI agents into enterprise workflows.
This transition is creating entirely new API dependencies.
AI systems depend heavily on APIs to:
- Access enterprise datasets
- Connect cloud services
- Interact with external platforms
- Automate workflows
- Trigger business actions
- Integrate large language models
As AI adoption increases, the number of machine-to-machine interactions is expanding dramatically.
Trend Micro predicts that AI-driven attack automation will continue to evolve throughout 2026, allowing cybercriminals to identify vulnerabilities and execute attacks at a significantly greater scale. (4)
This trend creates major challenges for enterprise defenders.
Security teams are now dealing with:
- AI-generated phishing campaigns
- Automated vulnerability discovery
- AI-assisted credential attacks
- API abuse automation
- Synthetic identity fraud
- Autonomous attack chains
At the same time, many enterprises lack mature API discovery and cloud governance capabilities.
This creates a dangerous imbalance where attackers can scale faster than defensive teams.
Why Traditional Security Models Are Failing
Perimeter-based approaches to enterprise security were made for centrally located premises. Nonetheless, APIs, cloud-based applications, and artificial intelligence-based applications have reshaped enterprise architecture.
Today’s enterprises function within dispersed cloud infrastructure, SaaS-based ecosystems, serverless platforms, and integration with third parties.
While APIs may evade detection by typical inspection processes, many firms lack a comprehensive API portfolio.
IBM, based on an analysis of findings, revealed that, on average, firms employ 83 security products from 29 providers, resulting in operational challenges and slow threat response times. (8)
Furthermore, the study indicated that dispersed security systems took 72 days longer to discover threats and 84 days to mitigate attacks. (8)
In other words, attackers get extra time to use vulnerabilities in APIs, identities, and the cloud.
Strategic Priorities for Enterprise Leaders in 2026
The executives of enterprises cannot afford to ignore API security and cloud governance anymore.
These risks now directly influence:
- Business continuity
- Customer trust
- Regulatory exposure
- AI governance
- Digital transformation success
- Enterprise valuation
Organizations must adopt a proactive and unified security strategy.
Key priorities include:
1. Establish Comprehensive API Discovery
Organizations must continuously identify and inventory all APIs across cloud, SaaS, and internal environments.
This includes:
- Shadow APIs
- Legacy APIs
- Third-party APIs
- Partner integrations
- AI service APIs
Without visibility, effective security is impossible.
2. Implement Zero-Trust Access Controls
Enterprises should enforce:
- Least privilege access
- Strong identity verification
- Continuous authentication
- API token governance
- Granular authorization policies
Identity has become the new security perimeter.
3. Strengthen Cloud Configuration Governance
Organizations must continuously monitor cloud environments for:
- Misconfigurations
- Excessive permissions
- Exposed workloads
- Insecure storage services
- Unpatched cloud assets
Automated cloud security posture management is becoming essential.
4. Secure AI and Machine-to-Machine Interactions
AI systems must be treated as high-value attack surfaces.
Security teams should monitor:
- AI APIs
- Model access permissions
- AI data pipelines
- Autonomous agent activity
- Third-party AI integrations
5. Consolidate Security Visibility
Security fragmentation is increasing operational risk.
Organizations should prioritize:
- Unified telemetry
- Centralized visibility
- Cross-cloud monitoring
- Integrated threat detection
- Real-time API analytics
Reducing complexity is becoming a competitive security advantage.
Conclusion
API sprawl and cloud misconfigurations are now major drivers of enterprise cyber risk.
The rapid growth of APIs, AI integrations, and cloud-native applications has created a larger attack surface than many organizations can effectively secure.
Attackers are increasingly exploiting unmanaged APIs, exposed workloads, weak identities, and security misconfigurations to access sensitive enterprise environments.
At the same time, AI-driven attack automation is accelerating the scale and speed of cyberattacks.
Organizations that fail to modernize API governance and cloud security strategies will face increasing exposure to:
- Data breaches
- Regulatory penalties
- Operational disruption
- Financial losses
- Customer trust erosion
The enterprises most prepared for 2026 will be those that treat API security, identity governance, cloud visibility, and AI risk management as core business priorities.
Cybersecurity is no longer defined only by endpoints and firewalls.
It is increasingly defined by APIs, cloud identities, and machine-to-machine trust relationships.
References
- What Is API Sprawl? – IBM – 2026
- What Is API Sprawl? – Akamai – 2026
- OWASP API Security Project – OWASP Foundation – 2026
- The AI-fication of Cyberthreats: Trend Micro Security Predictions for 2026 – Trend Micro – 2026
- Security Misconfiguration – Palo Alto Networks – 2026
- Cloud Attack Trends Report – Red Canary – 2026
- API Compliance and API Security – Wiz – 2026
- Security Capturing the cybersecurity dividend – IBM – 2025
- API Management Market Size & Trends Analysis Report – Grand View Research – 2025
- API Management Market Global Forecast to 2030 – MarketsandMarkets – 2025
- Worldwide Public Cloud End-User Spending Forecast – Gartner – 2025
- Worldwide Artificial Intelligence Spending Guide – IDC – 2025
- FY2026 Q1 Earnings Report – Microsoft Investor Relations – 2025
- AWS Annual Revenue Performance – Amazon Investor Relations – 2025
- Google Cloud Financial Results – Alphabet Investor Relations – 2025
- Cybercrime Damages Predicted to Reach $10.5 Trillion Annually by 2026 – Cybersecurity Ventures – 2025
🔒 Login or Register to continue reading