The development of quantum computer technology has turned into a major cybersecurity problem for the government, cloud service providers, banks, and critical infrastructure services in the country.
With further advancements in quantum computing technology, the traditional cryptography systems, which have been used for asymmetric cryptography like RSA, are no longer safe and will soon be vulnerable to quantum attacks in the near future.
The evolution of post-quantum cryptography (PQC) could be considered one of the most significant milestones in the field of cryptography after the introduction of public key cryptography.
Rather than posing the question of whether quantum attacks will happen, we now have to deal with the challenge of how soon we can be ready for them.
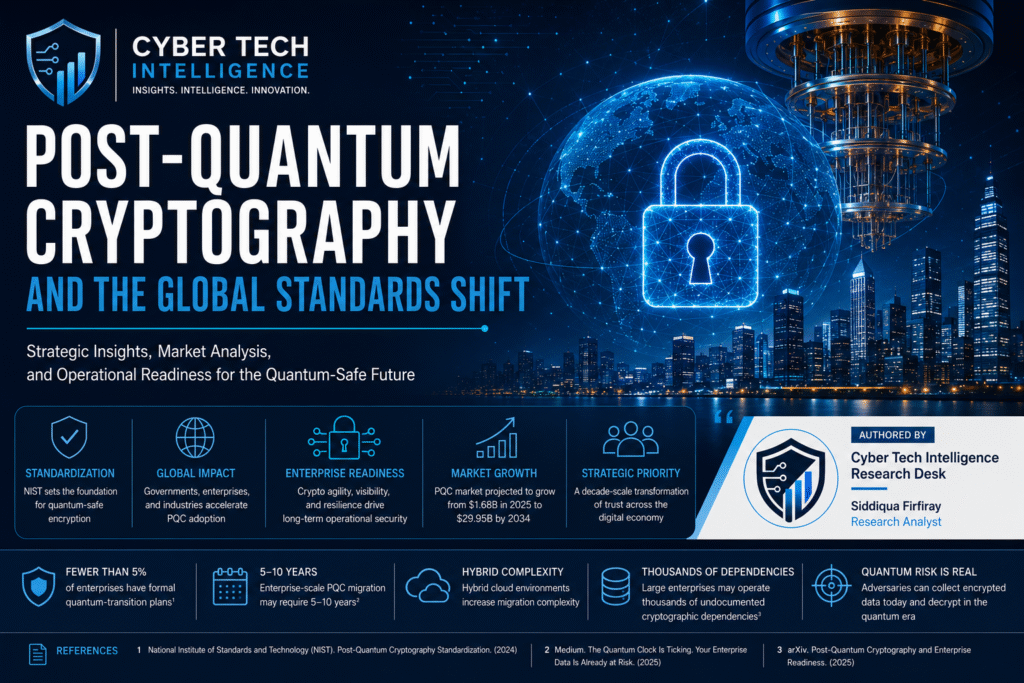
Key Market Indicators
- National Institute of Standards and Technology (NIST) completed the first set of PQC encryption standards in 2024, which includes ML-KEM and ML-DSA¹
- IBM predicts that cryptographically relevant quantum computers could emerge in the coming decade
- McKinsey & Company estimates that migration timelines for large enterprises may exceed 5–10 years, depending on infrastructure complexity
- Gartner projects that by 2029, most conventional asymmetric cryptography used for secure communications could become unsafe against quantum-enabled attacks
Strategic Observation
PQC migration is not just about upgrading the technology. This is a strategic move that takes into account infrastructure upgrade, cryptographic agility, vendor alignment, compliance, and cryptographic visibility across the enterprise organization.
Global Standards Adoption Takes Off
The release of PQC algorithms by international organizations has made enterprises think in terms of planning cycles. Governments, hyperscale organizations, and cybersecurity companies have been fast-tracking their adoption of quantum-safe cryptography.
Why Does Standardization Matter?
Historically, the adoption of any new cryptography system depended largely on standardization and interoperability issues. Without standards, no enterprise could consider adopting new encryption techniques.
The formalization of PQC standards by NIST fundamentally changed market confidence levels.
Key Industry Developments
- NIST standardized:
- ML-KEM (formerly CRYSTALS-Kyber) for encryption
- ML-DSA (formerly CRYSTALS-Dilithium) for digital signatures
- SLH-DSA for backup signature resilience
- Major cloud providers, including IBM, Google Cloud, and Cloudflare have expanded Post-Quantum Cryptography testing initiatives

- Financial regulators in North America and Europe have begun assessing quantum resilience readiness in critical financial systems
- Government agencies across the US, UK, and EU are introducing migration timelines tied to national cybersecurity modernization programs
Cyber Tech Intelligence Perspective
Cyber Tech Intelligence assesses that standardization is acting as the primary catalyst for enterprise mobilization. Before NIST formalization, quantum security remained largely experimental. After standardization, PQC became a procurement, governance, and board-level resilience issue.
Market Activity and Enterprise Adoption Trends
PQC adoption is increasingly visible across highly regulated and high-risk sectors.
Industries Leading Post-Quantum Cryptography Readiness
Financial Services
Banks and payment ecosystems face heightened exposure due to:
- Long-term financial records
- Cross-border encrypted transactions
- Regulatory obligations
- Critical trust infrastructure
Healthcare
Healthcare systems store highly sensitive data with long retention periods, making them attractive targets for “harvest now, decrypt later” operations.
Defense and Government
National security environments are prioritizing:
- Secure communications
- Classified intelligence protection
- Supply-chain cryptographic resilience
- Satellite and military encryption modernization
Telecommunications
Telecom providers are integrating crypto agility into:
- 5G infrastructure
- Secure routing environments
- IoT ecosystems
- Edge computing platforms
Cyber Tech Intelligence recommends that enterprises begin with cryptographic discovery assessments before evaluating replacement algorithms. Organizations that fail to identify encryption dependencies risk operational fragmentation during migration phases.
Why This Matters to Security Leaders
PQC readiness directly impacts enterprise resilience, compliance posture, and long-term operational continuity.
Security leaders are increasingly expected to answer:
- Which systems use vulnerable cryptographic algorithms?
- How quickly can cryptographic infrastructure be replaced?
- Which vendors support crypto agility?
Executive-Level Risks
1. Long-Term Data Exposure
Sensitive data stolen today may remain encrypted until quantum capabilities mature.
2. Supply Chain Vulnerabilities
Third-party software and embedded devices may contain hardcoded cryptographic dependencies that are difficult to replace.
3. Compliance and Governance Pressure
Emerging quantum-readiness frameworks may become mandatory within regulated industries.
4. Operational Complexity
Migration efforts will require:
- Certificate replacement
- Key management redesign
- Protocol modernization
- Vendor coordination
- Infrastructure testing
Enterprise Readiness Metrics
- The worldwide post-quantum cryptography market is predicted to grow at an amazing rate of 37.72%, from $1.68 billion in 2025 to reach an astounding $29.95 billion in 2034 2
- Large enterprises may operate thousands of undocumented encryption dependencies
- Migration costs are expected to rise substantially for organizations delaying crypto modernization
Cyber Tech Intelligence Analysis
Cyber Tech Intelligence has developed a five-layer analytical framework designed to help enterprises evaluate operational readiness for post-quantum migration.
1. Cryptographic Discovery Layer
Identify where cryptographic functions exist across:
- Applications
- APIs
- Cloud workloads
- Endpoint systems
- Identity infrastructure
2. Data Longevity Mapping
Determine which datasets remain sensitive long enough to face future quantum exposure.
3. Crypto Agility Assessment
Evaluate whether systems can:
- Replace algorithms rapidly
- Rotate certificates dynamically
- Support hybrid cryptographic models
4. Third-Party Dependency Analysis
Assess vendor readiness and inherited cryptographic risks across supply chains.
5. Quantum Threat Exposure Scoring
Prioritize migration based on:
- Sensitivity
- Business criticality
- Regulatory impact
- Adversarial attractiveness
Cyber Tech Intelligence Strategic Findings
Cyber Tech Intelligence assesses that the greatest enterprise weakness is not algorithm vulnerability itself, but the absence of cryptographic visibility and migration agility.
Organizations with decentralized IT environments, legacy infrastructure, and unmanaged third-party integrations are likely to face the highest transition complexity.
Strategic Enterprise Risk Indicators
- Industry estimates indicate that fewer than 5% of enterprises currently maintain formal quantum-transition readiness plans 3
- McKinsey estimates that enterprise-scale Post-Quantum Cryptography migration initiatives could require 5–10 years due to infrastructure modernization complexity
- Legacy infrastructure continues to be identified as one of the largest operational barriers to crypto modernization efforts
Intelligence Statistics
- Enterprises with mature crypto inventories can reduce migration complexity significantly compared to organizations lacking cryptographic governance
- Hybrid cloud environments increase PQC migration complexity due to inconsistent encryption implementations
- Operational downtime risk rises substantially when cryptographic modernization lacks phased migration planning
Operational Recommendation
Cyber Tech Intelligence recommends that enterprises treat Post-Quantum Cryptography readiness as a resilience modernization initiative rather than a narrow cryptographic upgrade project.
- Large enterprises may operate thousands of undocumented cryptographic dependencies across hybrid environments
- Industry research indicates that fewer than 5% of enterprises currently maintain formal quantum-transition plans 3
Security Leaders Should Align
- Architecture teams
McKinsey estimates that enterprise-scale cryptographic modernization initiatives may require 5–10 years due to infrastructure complexity.
- Compliance leaders
Gartner projects that by 2029, conventional asymmetric cryptography used in enterprise communications may become increasingly vulnerable to quantum-enabled attacks.
- Infrastructure operations
Quantum-safe VPN and TLS pilot deployments expanded significantly during 2024–2025 following NIST standardization.
- Vendor governance programs
Hybrid cloud environments significantly increase cryptographic governance challenges due to inconsistent encryption implementations.
- Incident response functions
Incident response and cyber resilience teams must begin incorporating quantum-related threats into long-term security planning, threat modeling, and breach impact assessments.
Conclusion
Post-Quantum Cryptography is becoming a foundational cybersecurity priority across global enterprise environments. The convergence of NIST standardization, increasing quantum investment, and rising concern over long-term data exposure is accelerating the global standards shift.
Cyber Tech Intelligence assesses that enterprises adopting crypto agility and cryptographic visibility early will be substantially better positioned to manage the operational realities of the quantum era.
The transition to Post-Quantum Cryptography is not a single technology deployment. It is a decade-scale transformation of trust infrastructure across the digital economy.
FAQs
-
Is a Business at Risk of a Cyber Security Attack Using Quantum Computing Technology Today?
Quantum Computing Technology Currently Does Not Present an Immediate Risk to Most Organizations, However If Attackers Gather Data That Will Eventually Be Deciphered When Quantum Computing Technology Is Incorporated, They May Put The Organization at Risk.
-
What Are Some Major Barriers To Developing Post-Quantum Crypto?
The Most Significant Barrier to Implementing Post-Quantum Crypto Is Establishing Where Cryptography Currently Exists within The Organization.
-
What Are Some Key Industries That Should Initiate Migration To Post-Quantum Crypto As Soon As Possible?
Areas such as Financial Services, Health Care, Governmental Agencies, Telecommunications, Defense, and Critical Infrastructures should prioritize their compliance with Post-Quantum Crypto Initiatives.
-
Will The Use Of Post-Quantum Crypto Make All Other Forms Of Crypto Obsolete?
The Will Not, Because Most Organizations Will Continue To Use Hybrid Forms Of Crypto, Therefore Post Quantum Crypto, And Current Cryptographic Solutions Will Co-Exist.
-
What Is The Initial Action That CISOs Should Take?
CISOs Need To Identify Where Cryptography Is Used Within Their Companies.
References
- National Institute of Standards and Technology (NIST). Post-Quantum Cryptography Standardization. (2024) NIST. Available at: https://www.nist.gov/cryptography/post-quantum-cryptography (Accessed: 11 May 2026).
- Medium. The Quantum Clock Is Ticking. Your Enterprise Data Is Already at Risk. (2025) Medium, by Activated Thinker. Available at: https://medium.com/activated-thinker/the-quantum-clock-is-ticking-your-enterprise-data-is-already-at-risk-96b31426b42e (Accessed: 11 May 2026).
- arXiv. Post-Quantum Cryptography and Enterprise Readiness. (2025) arXiv. Available at: https://arxiv.org/html/2509.01731v1 (Accessed: 11 May 2026).
🔒 Login or Register to continue reading