Third-party risk isn’t just a checkbox anymore in 2026. It’s your top target.
Security leaders across the country are struggling to keep up with an onslaught of AI-fueled identity attacks, SaaS sprawl, and non-human identities (NHIs) outpacing their human counterparts by a factor of 45-to-1 in cloud-native architectures.
At the same time, corporate boards are insisting on measurable cyber risk reporting, which forces CISOs to quantify their technical vulnerabilities into dollars and cents.
The Comcast breach and $117.5M lawsuit aren’t anomalies. They are warnings that third-party risk management isn’t built to last in today’s cybersecurity landscape.

Source: Creative Commons
With Cyber Tech Insights, you have the opportunity to pivot toward intelligent, unified risk management at scale.
The New Reality of Third-Party Risk in 2026
The Comcast breach reflects a broader shift in how attackers operate.
They are no longer breaching perimeters. They are entering through trusted relationships.
1. The Explosion of Non-Human Identities (NHIs)
Machine identities, service accounts, APIs, and automation scripts now dominate enterprise environments.
- NHIs outnumber human identities by up to 45:1.
- Over 60% of breaches in 2025–2026 involved compromised service accounts or API tokens.
- Most third-party vendors integrate via APIs with persistent, often overprivileged access.
Traditional vendor risk assessments do not account for identity sprawl at machine scale.
2. Speeding Up Attacks Using AI
Attackers are employing AI to:
- Automate credential gathering.
- Masquerade as genuine vendors.
- Spot incorrectly configured trust relationships.
Consequences are:
- More rapid attack implementation.
- Shorter detection intervals for hackers, greater MTTD for security teams.
- Higher probability of success in attacking supply chains.
Traditional software lacks the capability to address adaptive AI threats.
3. Cloud and SaaS Dependency Risks
Today’s typical organization utilizes:
- 150-300 SaaS apps.
- Dozens of external integrations per mission-critical process flow.
Every integration creates:
- Data leakage vectors.
- Identity trust dependencies.
- Configuration drift vulnerabilities.
Only a few companies have visibility into their vendors’ actions after onboarding.
4. Compliance Does Not Mean Security
Numerous organizations had successfully passed compliance audits prior to any data breach.
Why?
It’s because:
- Assessment is a snapshot.
- Controls are reported by the vendor.
- Monitoring is intermittent.
Comcast is a classic example of the distinction between compliance and security.
Fragmentation of the Security Stack Creates Gaps
Security professionals usually use:
- Endpoint detection solutions.
- Network monitoring solutions.
- Identity providers.
- Cloud security solutions.
However, such approaches do not allow:
- Contextualizing threat intelligence.
- Mapping vendor risk exposure to business risks.
- Ensuring end-to-end visibility.
This fragmentation is at the core of the delay problem.
NIST CSF 2.0 Govern Function in Reality
To solve these problems, the NIST Cybersecurity Framework 2.0 came up with the Govern function.
The Govern function elevates cybersecurity to an enterprise-wide risk management discipline, aligning security strategy with business objectives and accountability at the executive level.
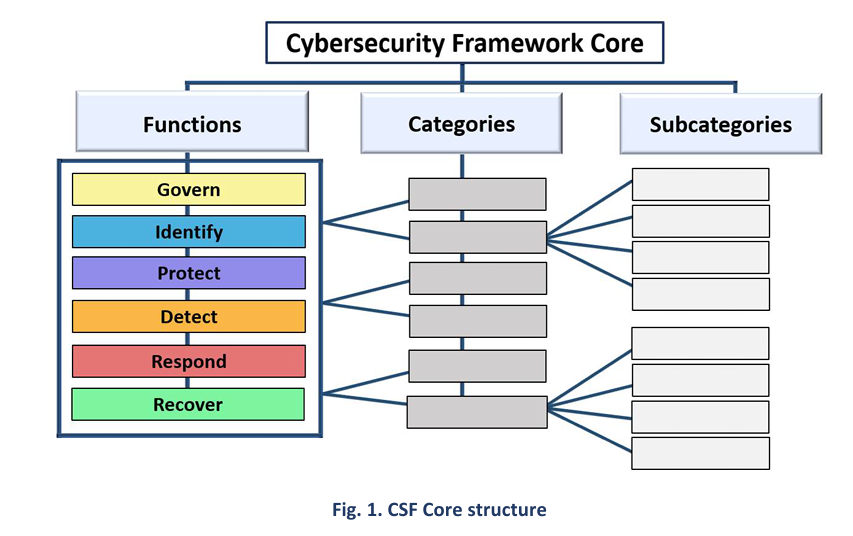
Source: NIST
Its key points include:
- Executive-level risk ownership.
- Risk assessment on an ongoing basis.
- Integrating cybersecurity with enterprise governance.
However, implementation is difficult for companies because of a lack of knowledge about it.
Traditional Vendor Limitations
1. Lack of Continuous Governance
The tools rely on periodic assessments rather than continuous scoring of risks.
2. Siloed Use of AI
The applications are limited to detecting attacks, but not in governing or managing risk.
3. Metrics Lack Business Relevance
They are security metrics and not related to business risk.
Case Study: Change Healthcare Ransomware Attack
In 2023, the US Department of Health and Human Services released a cybersecurity concept paper outlining an assertive national strategy for healthcare security.
While the initiative emphasized support for under-resourced hospitals, it also signaled a clear shift toward greater enforcement and accountability, including stricter investigation of HIPAA violations and increased financial penalties.
The ransomware attack on Change Healthcare was a cyberattack that occurred in February 2024, and the target was a major U.S. clearinghouse for healthcare payment and prescription processing.
The attack has been considered by many to be one of the most impactful attacks on the U.S. healthcare industry.
Background
Change Healthcare, which is a subsidiary of UnitedHealth Group, is the largest clearinghouse organization in the country, dealing with eligibility verification, claims processing, and payment of providers.
This makes Change Healthcare one of the key ‘single points of failures’ in the national landscape of administrative health-care operations.
The Attack
The perpetrators behind the incident, who were affiliated with ALPHV/BlackCat hackers, managed to gain entry via an infected account to the Citrix remote access portal, which did not have any multifactor authentication on February 12, 2024.
Afterward, they began their lateral movement through the network and proceeded to exfiltrate several terabytes of sensitive data, and then dropped the ransomware on February 21.
Its Effect on the U.S. Healthcare System
The breach caused a significant problem with electronic claims processing, remittance, and verification of patient eligibility for services and medications.
Many providers were unable to be reimbursed, and pharmacies could not verify insurance coverage for prescriptions. Patients would have had to pay cash for the medicine. Providers estimated their losses from the breach at around $100 million a day.
Data breach consequences and privacy concerns:
- The cyber attack resulted in a major breach of protected and personally identifiable health information.
- Estimates show that one-third to more than half of the country’s population may have been impacted by this breach.
This makes the event a record data breach for the healthcare sector in the United States.
Attackers exploited trusted third-party access to move laterally across critical systems. The same structural weakness appears in the Comcast breach.
It is the reason why this link is crucial for CISOs because in both instances, there is a change in how attackers operate.
Attackers are not penetrating anymore; rather, they are entering via trusted connections.
The weakness in the traditional vendor risk management program lies here because it validates the vendors during the onboarding process but fails to oversee their operations afterward.
Third-Party Risk Management
What failed was the end-to-end lifecycle of TPRM (third-party risk management)
1. Trust But Verify
Organizations continue to base third-party risk management on:
- Yearly assessments of vendor security postures.
- Static compliance certifications.
- Security control attestations provided by vendors themselves.
The risk profile changes constantly.
For example, a vendor that is compliant today may be at risk tomorrow from:
- Stolen credentials.
- Configuration errors.
- Supply chain weaknesses.
Without consistent verification, the enterprise runs into trouble.
2. The Attack Surface Is Now Identity
In both cases of the Comcast and Change Healthcare data breaches, the hackers didn’t have to breach any defenses.
They used:
- Legitimate credentials.
- APIs and web services.
- Validated, trusted integration points.
This marks a significant paradigm shift. The attack surface is no longer about infrastructure alone. It’s about identity, access, and trust relationships.
However, most organizations don’t:
- Track non-human identities.
- Monitor activity in real-time to correlate anomalies.
- Understand how vendors are using their permissions.
3. Fragmentation Is the Core Issue
Companies have made significant investments in security. But such investments are fragmented.
Common examples include:
- Endpoint detection solutions.
- Identity solutions.
- Cloud security solutions.
- GRC solutions.
They address part of the equation but lack end-to-end context.
Fragmentation results in:
- Late detection (long MTTD).
- Ineffective response (long MTTR).
- Insufficient risk visibility.
For Comcast, the problem wasn’t a lack of solutions. The problem was a lack of intelligence across them.
4. Compliance Created an Illusion of Security
Breached companies were often compliant prior to their attack. Included are companies victimized in recent supply chain attacks.
The difference is stark:
- Compliance addresses control existence.
- Security concerns control efficacy over time.
5. The Economics of Failure
The million-dollar settlement demonstrates the actual cost of failure when it comes to third-party risk management.
However, monetary fines are just one part of the story.
Other considerations include:
- Disruption.
- Loss of customer trust.
- Regulatory pressure.
- Brand reputation damage.
This shift in perspective transforms cybersecurity into a business risk discipline rather than a technical one.
Take the Next Step.
Schedule a CISO Briefing to evaluate your third-party risk posture
Rethinking Trust in a Connected Enterprise
This disconnect has grown to a size where conventional practices are inadequate in maintaining the balance. This is where risks become tangible enough to manifest in terms of monetary, operational, and reputational losses for organizations.
Leading security executives have already begun to make this shift in perspective. Rather than focusing on how to optimize vendor management, they now ponder how to develop a framework that ensures a dynamic, measurable, and enforceable state of trust within their vendor ecosystem.
It entails breaking away from disjointed solutions and embracing an integrated solution that evaluates identity, access, and behavior in relation to enterprise risk.
Start building prevention at scale. Before your next breach defines you.
FAQs
1. Why is third-party risk management failing today?
It relies on periodic assessments, not continuous monitoring, leaving real-time gaps that attackers exploit.
2. What did the Comcast breach reveal about vendor risk?
It showed that trusted third parties can become primary entry points without continuous oversight.
3. How should CISOs modernize third-party risk in 2026?
By adopting continuous governance, AI-driven risk scoring, and zero trust enforcement.
4. Why are non-human identities a growing risk?
They often have persistent, overprivileged access and are rarely monitored in real time.
5. How do you measure ROI in third-party risk management?
Through faster detection, reduced incidents, lower costs, and improved compliance readiness.
To participate in upcoming interviews, please reach out to our CyberTech Media Room at info@intentamplify.com.
🔒 Login or Register to continue reading