Most organizations already have endpoint security in place. Very few have endpoint visibility that actually reduces risk.
Benchmark Your Current Endpoint Security Maturity.
Download the EDR Benchmark Framework to assess where your organization stands today.
What is Endpoint Detection?
Endpoint Detection is the capability to identify abnormal and potentially malicious behavior at the device level by continuously analyzing system activity, rather than relying on predefined threat signatures.
It assumes that compromise is possible and focuses on detecting it early.
“Cybersecurity is part of how you protect your customers’ trust… A breach will also cost you your reputation.” – Allison Dunn, Legacy Founder and CEO at Deliberate Directions.
The Problem Most Security Teams Underestimate
EDR is often introduced as an upgrade. In reality, it exposes operational gaps.
Teams expect:
- Better detection.
- Faster response.
- Cleaner visibility.
What they encounter instead:
- Alert fatigue.
- Ambiguous signals.
- Slower decision cycles.
This is not a tooling issue. It is a maturity mismatch between technology and operations.
See How Mature Your Security Operations Really Are.
Access the SOC Readiness Checklist for EDR Adoption.
What EDR Actually Changes and What It Doesn’t
EDR does not prevent compromise. It assumes compromise.

More visibility does not automatically lead to better outcomes.
Without the ability to interpret signals, EDR becomes noise at scale.
Identify Gaps in Your Detection and Response Strategy.
Get the EDR Capability Gap Assessment Template.
Where Most EDR Implementations Break Down
There is a consistent pattern across enterprises.
1. Overestimating Automation
Response automation sounds efficient. In practice, it introduces risk.
Isolating an endpoint might stop an attack. It might also disrupt business-critical operations.
So teams hesitate. Automation becomes conditional. Speed is lost.
2. Underestimating Data Volume
EDR generates high-fidelity telemetry. It also generates volume.
Without prioritization:
- Analysts spend more time triaging than responding.
- Critical threats get buried in low-confidence alerts.
3. Ignoring Identity Context
EDR sees behavior. It doesn’t always understand identity.
Without integration with identity systems:
- Suspicious actions lack attribution.
- Response decisions become slower and less confident.
Learn How to Align EDR with Identity and Zero Trust.
Download the EDR and Identity Integration Blueprint.
EDR Vendor Comparison. CrowdStrike vs Microsoft
| Evaluation Criteria | CrowdStrike Falcon | Microsoft Defender for Endpoint |
| Deployment Model | Cloud-native, lightweight agent | Integrated within Microsoft ecosystem |
| Detection Approach | Behavioral AI + threat intelligence (Falcon platform) | Behavioral analytics + Microsoft threat graph |
| Ease of Deployment | Fast deployment, minimal infrastructure. | Easy if already using Microsoft stack, complex otherwise. |
| Visibility Depth | Strong endpoint telemetry and real-time visibility. | Deep visibility across endpoints, identity, and cloud. |
| Response Capabilities | Advanced response actions, strong automation workflows. | Tight integration with Microsoft security tools for response. |
| False Positive Management | High signal quality, lower noise. | Can generate higher alert volume without tuning. |
| Integration Flexibility | Open integrations with third-party tools. | Best within Microsoft ecosystem, limited outside. |
| SOC Efficiency Impact | Reduces triage time with strong signal prioritization. | Requires tuning to avoid alert fatigue. |
| Identity Context | Available via integrations (not native-first) | Native identity integration via Azure AD. |
| Scalability | Highly scalable across distributed environments. | Scales well in Microsoft-centric enterprises. |
| Best Fit For | Enterprises with diverse tech stacks and need for best-in-class detection. | Organizations heavily invested in Microsoft ecosystem. |
| Pricing Model | Premium pricing, modular licensing. | Often bundled, it is cost-effective for existing Microsoft customers. |
The Trade-Off You Need to Accept
You don’t get high visibility without operational complexity.
That’s the deal.
Organizations that succeed with EDR do one thing differently. They plan for the operational impact, not just the deployment.
This includes:
- Redefining SOC workflows.
- Investing in analyst capability.
- Prioritizing signal over volume.
Optimize Your SOC for EDR-Driven Operations.
Access the EDR Operating Model Playbook.
Where EDR Delivers Real Business Value
Not in dashboards. Not in feature lists.
Its value shows up in constrained moments:
- Containing lateral movement before escalation.
- Reducing the dwell time of attackers.
- Compressing investigation timelines.
These outcomes directly influence:
- Financial risk exposure.
- Regulatory impact.
- Brand reputation.
Quantify the Business Impact of EDR in Your Environment.
Use the EDR ROI and Risk Reduction Calculator
The Market Shift You Can’t Ignore
Global end-user spending on information security was projected to reach $212 billion in 2025, growing 15.1% year over year, reflecting accelerating enterprise investment in detection and response capabilities.
EDR is no longer a standalone category.
It is being absorbed into broader platforms:
- XDR ecosystems.
- Unified security operations platforms.
- Cloud-native security stacks.
Buying EDR today is not just about endpoint security. It is about future alignment with your security architecture.
Compare Leading EDR and XDR Platforms Side-by-Side.
Download the EDR Vendor Benchmark Report.
What Decision-Makers Should Actually Evaluate
Most vendor comparisons focus on features. That’s surface-level.
The real evaluation criteria are operational:
- Can your team interpret behavioral signals effectively?
- How quickly can you move from detection to action?
- What is your tolerance for false positives vs missed threats?
- How well does EDR integrate into your existing stack?
Use a Structured Evaluation Framework.
Get the EDR Vendor Scoring Matrix and Selection Checklist.
The Hard Truth About EDR
EDR will not make your organization secure.
It will:
- Expose gaps in your response capability.
- Increase visibility into real threats.
- Force operational discipline.
That’s where its value lies.
Move from Exploration to Execution
Most teams stay stuck in evaluation mode. Comparing vendors. Reviewing features. Delaying decisions.
Meanwhile, attackers don’t wait.
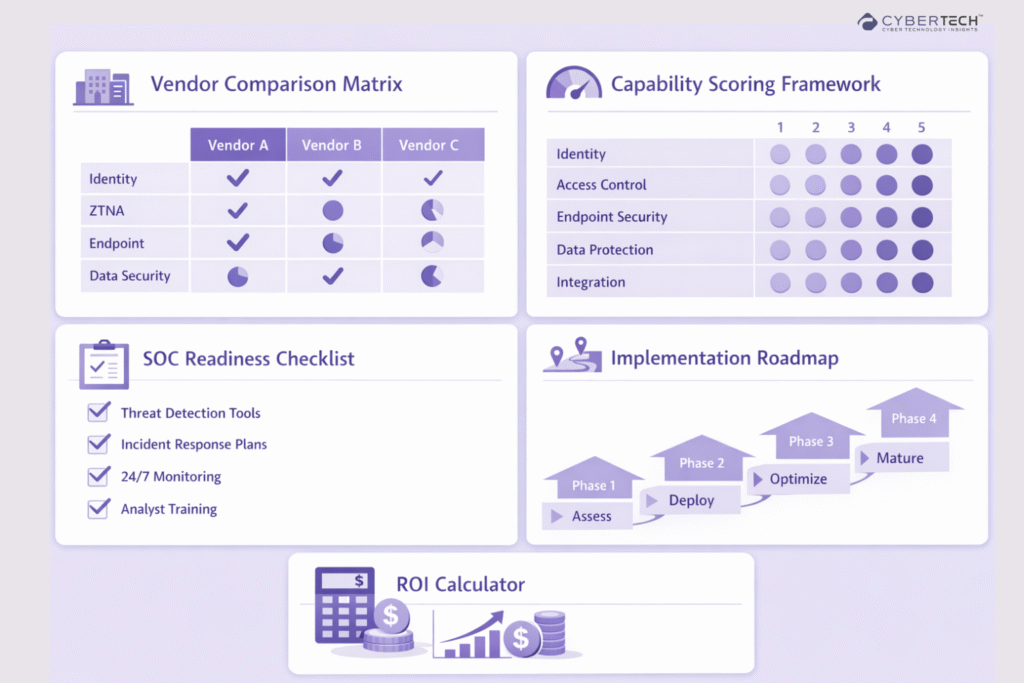
Download the Complete Endpoint Detection and Response Buyer’s Kit.
Includes:
- Vendor comparison matrix.
- Capability scoring framework.
- SOC readiness checklist.
- Implementation roadmap.
- ROI calculator.
Vendor comparisons create clarity. Execution exposes reality.
If your control layers are not aligned, adding more vendors will increase complexity, not reduce risk.
Get Your Zero Trust Vendor Shortlist Based on Your Architecture.
FAQs
1. What does EDR actually solve that traditional endpoint security cannot?
EDR detects behavior-based threats that bypass signature-based tools, including malware-free attacks.
2. Why are enterprises investing heavily in EDR and XDR platforms?
Attack speed and complexity have increased, reducing the window to detect and respond effectively.
3. What are the biggest challenges organizations face after deploying EDR?
High alert volumes and a lack of skilled analysts lead to alert fatigue and slower decisions. EDR often exposes gaps in SOC maturity rather than solving them.
4. Is EDR enough to stop modern cyberattacks?
EDR is a detection and response layer, not a complete security strategy. It must integrate with identity, cloud, and broader security systems to be effective.
5. How should decision-makers evaluate EDR vendors effectively?
Evaluation should focus on operational impact, like detection accuracy and response speed. The right choice depends on alignment with your existing architecture and team capability.
To participate in upcoming interviews, please reach out to our CyberTech Media Room at info@intentamplify.com
🔒 Login or Register to continue reading