Cloud Security Posture Management (CSPM) has become the difference between scalable cloud growth and invisible cloud risk.
Every new deployment, every permission granted, every configuration change adds speed to the business. It also adds exposure. Most of it goes unnoticed.
Across Amazon Web Services (AWS), Microsoft Azure, and Google Cloud Platform environments, risk does not appear as a single failure. It emerges as a chain. One that attackers are increasingly skilled at navigating.
CSPM exists to map that chain before it is exploited. To turn scattered signals into a clear understanding of where the business is actually vulnerable.
The Shift from Cloud Visibility to Business Accountability
Enterprises today operate across AWS, Microsoft Azure, and Google Cloud Platform, often with decentralized teams and rapidly changing configurations.
The result is not just complexity. It is unseen exposure.
- Infrastructure changes faster than security reviews.
- Identities accumulate permissions over time.
- Misconfigurations compound silently.
CSPM introduces a new model. One where cloud environments are continuously mapped, analyzed, and prioritized based on real-world exploitability, not theoretical risk.
See What Your Cloud Risk Actually Looks Like
Most organizations underestimate their exposure until it is too late.
Connect with Cyber Technology Insights to uncover hidden risk paths across your cloud environment and align security with business priorities.
What CSPM Actually Does Now and Why It Matters
CSPM in 2026 is not a scanner. It is an intelligence engine embedded across the cloud lifecycle.
Continuous Asset Intelligence
Every asset, across every account and region, is tracked in real time. This includes unmanaged and shadow resources that often go unnoticed.
Context-Driven Risk Prioritization
Instead of flagging thousands of issues, CSPM connects the dots. It identifies which combinations of misconfigurations, identities, and vulnerabilities can actually be exploited.
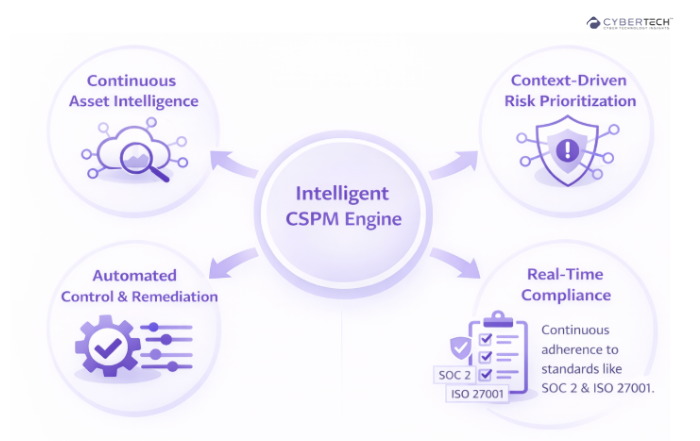
Automated Control and Remediation
Policies are enforced automatically. Misconfigurations are corrected before they can escalate into incidents.
Compliance That Operates in Real Time
Frameworks such as SOC 2 and ISO 27001 are no longer periodic checkpoints. They become continuous states of readiness.
CSPM as the Core of CNAPP: Where the Market Is Moving
CSPM has become foundational within Cloud-Native Application Protection Platforms. This is where security stops being fragmented and starts becoming connected.
Platforms from Palo Alto Networks, Wiz, and Check Point Software Technologies bring together posture, identity, and runtime protection into a single operational model.
The advantage is not consolidation alone. It is context continuity. Risk is no longer evaluated in isolation. It is understood as part of an evolving attack surface.
Unify Your Cloud Security Strategy
Disconnected tools create blind spots that attackers exploit.
Vendor Landscape: Who Is Defining CSPM in 2026
| Vendor | Category Position | Strength | CSPM Differentiation | Ideal Use Case |
| Wiz | CNAPP Innovator | Agentless architecture | Attack path visualization | Fast-moving cloud teams |
| Palo Alto Networks | Enterprise Platform | Full-stack coverage | Deep compliance + runtime integration | Large enterprises |
| Check Point Software Technologies | Hybrid Security Leader | Network + cloud integration | Layered threat prevention | Hybrid infrastructures |
| Microsoft Defender for Cloud | Cloud-Native | Native ecosystem advantage | Identity-integrated security | Azure-heavy environments |
| Orca Security | Agentless CSPM | Deep asset visibility | Data-centric risk insights | Rapid scaling organizations |
Frameworks That Turn CSPM into a Revenue Driver
Deploying CSPM is easy. Operationalizing it is where value is created.
1. Risk Correlation Framework
Connect assets, identities, and vulnerabilities into a single graph. Prioritize based on exploit paths, not isolated alerts.
2. Continuous Compliance Framework
Shift from audit cycles to real-time compliance. Ensure every configuration aligns with regulatory expectations at all times.
3. DevSecOps Alignment Framework
Embed CSPM into CI/CD pipelines. Ensure risks are identified before deployment, not after exposure.
4. Identity-Centric Security Framework
Treat identity as the primary attack surface. Enforce least privilege and continuously monitor access pathways.
Move from Tooling to Operational Maturity
Many organizations deploy CSPM but fail to extract value from it.
Partner with Cyber Technology Insights to implement frameworks that translate cloud security into measurable business outcomes.
DevSecOps Integration: Where Speed Meets Security
Security delays used to be the cost of doing things right. That trade-off no longer holds.
CSPM integrates directly into development workflows, allowing teams to:
- Identify risks during build stages.
- Eliminate rework post-deployment.
- Maintain velocity without compromising control.
This is where CSPM begins to influence time-to-market and competitive agility.
Identity Is the New Attack Surface
Attackers no longer need to break in. They log in, escalate privileges, and move laterally.
CSPM platforms now analyze:
- IAM roles and permissions.
- Privilege escalation paths.
- Cross-account access risks.
This shifts security from perimeter defense to access intelligence.
AI-Driven Context: The End of Alert Fatigue
The volume of alerts is no longer the problem. The lack of clarity is.
CSPM platforms now use AI to:
- Correlate signals across environments.
- Simulate real attack scenarios.
- Surface only the risks that matter.
Security teams move from reacting to alerts to making informed, prioritized decisions.
Turn Security Data into Business Intelligence
If your security stack generates noise instead of clarity, it is limiting your ability to act.
Engage Cyber Technology Insights to implement AI-driven CSPM strategies that deliver actionable insight at scale.
Business Impact: Where CSPM Delivers Real Value
CSPM’s value is not theoretical. It shows up in measurable business outcomes.
- Fewer breaches. Reduced financial and reputational damage.
- Faster compliance. Accelerated enterprise deal cycles.
- Higher uptime. Consistent customer experience.
- Stronger trust. Increased confidence among buyers and stakeholders.
Organizations that operationalize CSPM effectively do not just reduce risk. They increase their ability to scale securely and compete aggressively in cloud-first markets.
The Control Layer That Defines Cloud Maturity
The gap between cloud adoption and cloud control is where most organizations struggle.
CSPM closes that gap. It brings structure to complexity, context to risk, and clarity to decision-making.
In 2026, the organizations that lead are not the ones with the most advanced cloud environments. They are the ones who understand, control, and optimize them with precision.
FAQs
1. What is CSPM, and why is it critical in 2026?
CSPM (Cloud Security Posture Management) delivers continuous visibility into cloud configurations, identities, and risks. In 2026, it is critical because it links security posture directly to business impact, helping prevent misconfigurations that can lead to breaches, downtime, and revenue loss.
2. How does CSPM reduce cloud security risks in multi-cloud environments?
CSPM centralizes visibility across platforms like Amazon Web Services, Microsoft Azure, and Google Cloud Platform. It identifies misconfigurations, monitors identity permissions, and prioritizes risks based on exploitability, enabling faster and more effective remediation.
3. What is the difference between CSPM and CNAPP?
CSPM focuses on detecting and managing cloud misconfigurations and compliance gaps. CNAPP is a broader platform that includes CSPM along with workload protection and identity security, providing end-to-end coverage from development to runtime.
4. How does CSPM support compliance and regulatory requirements?
CSPM continuously maps cloud configurations to frameworks like SOC 2, HIPAA, and ISO 27001. It automates compliance checks, provides real-time scoring, and generates audit-ready reports, reducing manual effort and improving audit readiness.
5. What should enterprises look for when choosing a CSPM solution?
Enterprises should prioritize multi-cloud coverage, identity-aware risk analysis, automated remediation, DevSecOps integration, and alignment with CNAPP capabilities. Solutions from vendors like Wiz and Palo Alto Networks are often evaluated for their ability to provide contextual risk insights and scalability.
To participate in upcoming interviews, please reach out to our CyberTech Media Room at info@intentamplify.com
🔒 Login or Register to continue reading











