Introduction: The Rise of Voice as a Cybersecurity Battleground
Voice has emerged as one of the least protected and most exploited channels in enterprise security. For years, organizations have focused on securing email, endpoints, applications, and APIs. At the same time, voice communication has evolved into a high-risk attack surface. AI-driven voice fraud, caller ID spoofing, and impersonation attacks are scaling rapidly. Attackers are increasingly targeting customers and enterprises by mimicking trusted identities such as banks, enterprises, and government agencies. The result is measurable business impact, including declining answer rates, erosion of customer trust, and direct revenue loss. Traditional identity controls at the application layer are no longer sufficient. A structural shift is underway. Identity is moving from the application layer to the network layer. This shift is not incremental. It changes how trust is established, verified, and enforced across communication systems.
Executive Brief
- Voice is now a primary attack surface for fraud and impersonation
- Identity verification at the application layer is no longer sufficient
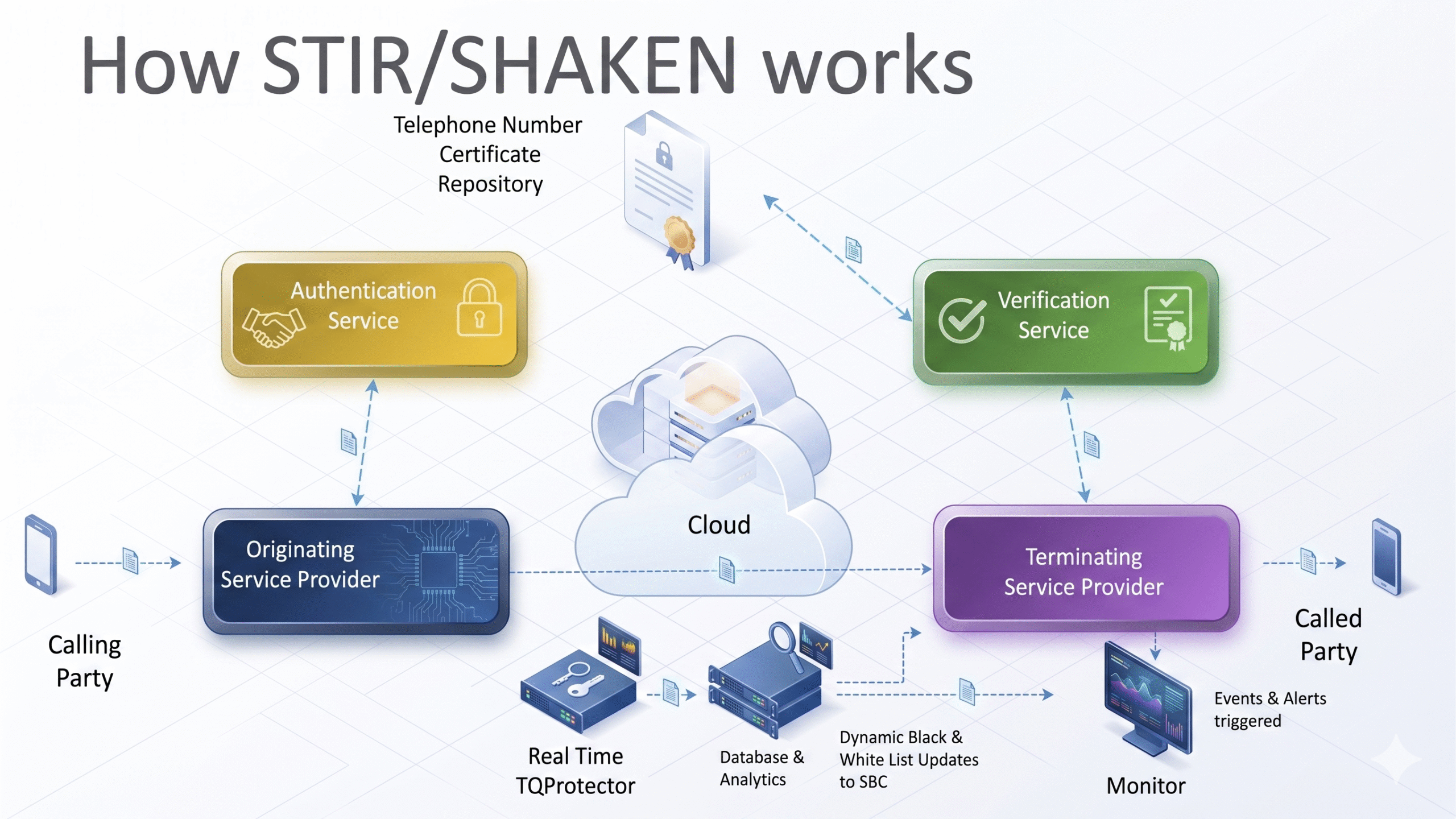
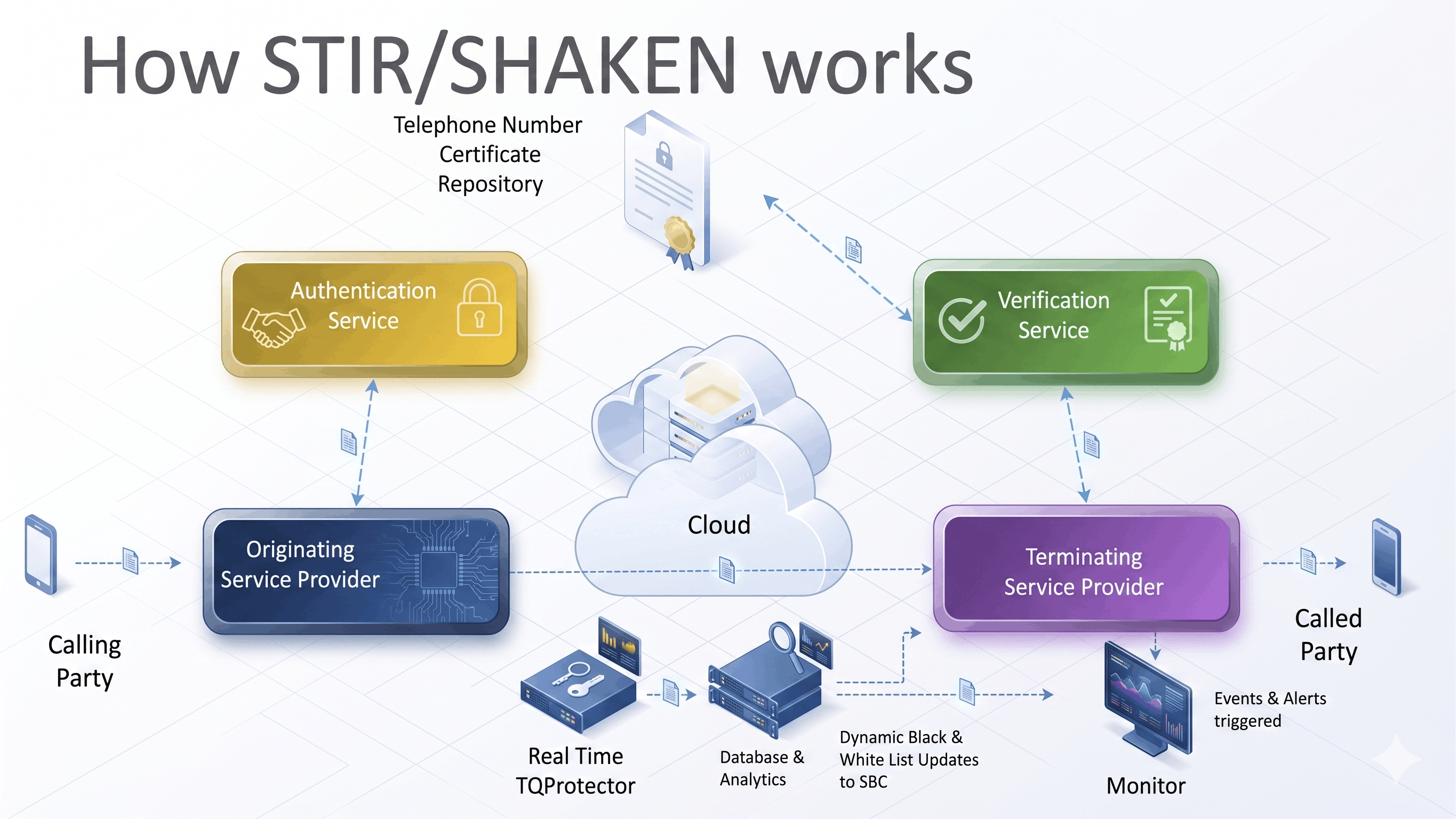
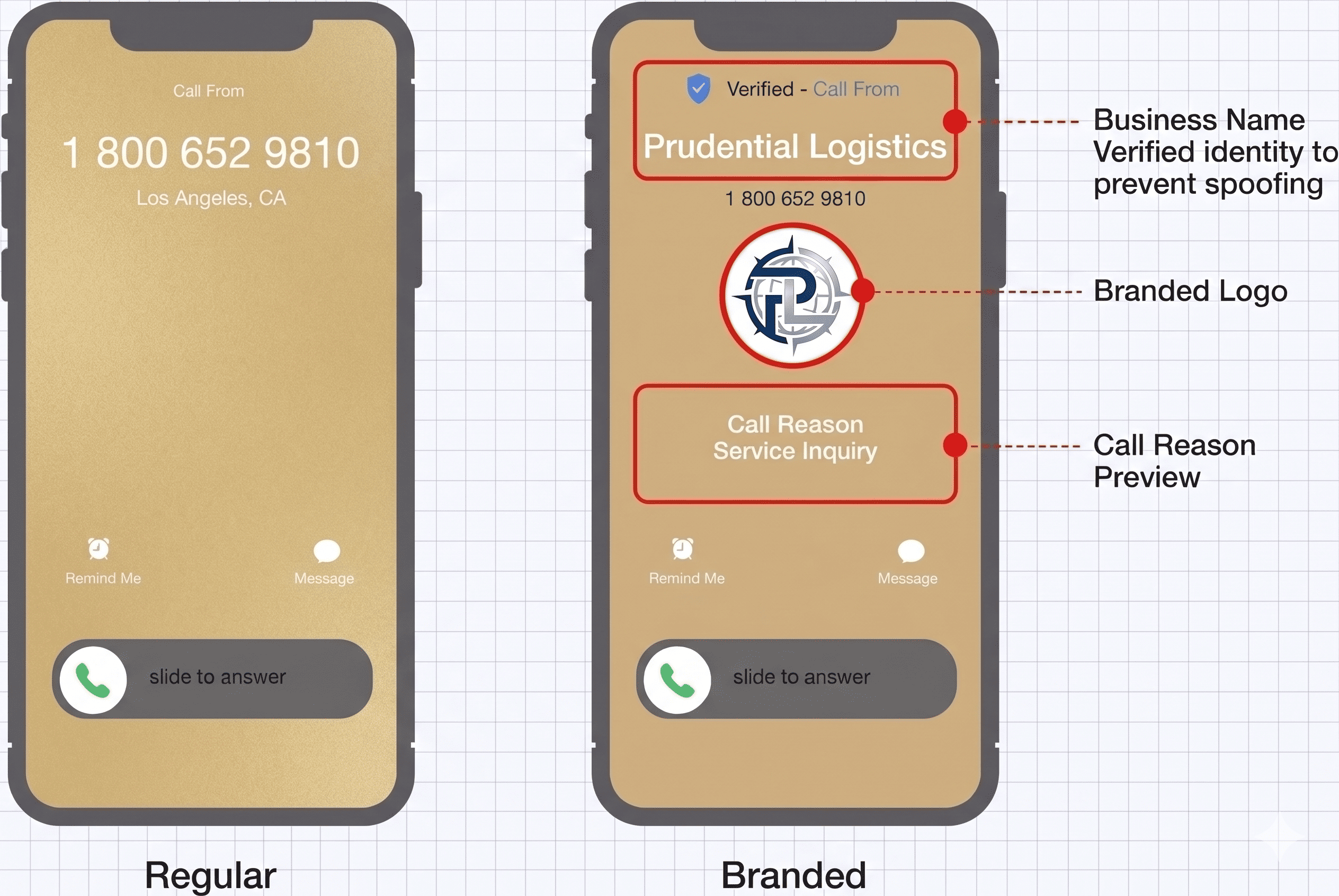
- SIP-based authentication enables pre-delivery trust validation
- Branding elements such as logos and caller identity are becoming security signals
- A new model is emerging: network-enforced Zero Trust identity
Cyber Threat Signals: Why This Shift Is Happening Now. Cyber threats are entering a new phase defined by speed, scale, and identity exploitation. AI-driven systems can identify and exploit vulnerabilities faster than defenders can respond. State-backed actors are leveraging infrastructure such as IoT and edge devices to build distributed attack platforms. Identity-driven breaches continue to generate the highest financial impact. This convergence signals a structural shift. Cyber risk is no longer confined to systems. It is embedded in identity, networks, and communication channels.
Cyber Threat Signals: Recent Attacks and Structural Trends
1. AI Is Compressing the Attack Window
AI-driven systems can identify and exploit vulnerabilities faster than defenders can respond. What previously took weeks or months is now happening in hours or minutes. Attackers are automating reconnaissance, vulnerability discovery, and exploitation at scale. This leads to:
- Discovery to exploitation cycles collapsing
- Patch windows becoming ineffective as a primary control
- Reactive security models becoming operationally obsolete
The gap between detection and exploitation is now a race condition. Attackers can continuously scan and test systems across infrastructure, identity layers, and communication channels. By the time a vulnerability is identified and prioritized, it may already be exploited. Security must shift toward:
- Pre-interaction verification
- Continuous validation of trust
- Infrastructure-level enforcement of identity
In this environment, speed is no longer an advantage. It is the attack vector.
2. State-Sponsored Attacks Are Scaling Through Infrastructure
Cyber actors are turning routers and IoT devices into covert botnets at scale. Recent campaigns have compromised hundreds of thousands of devices globally, including routers, smart devices, and edge infrastructure. Infrastructure is an attractive target because it is widely distributed, continuously active, and often lacks visibility. Once compromised, it enables persistent access and coordinated attack execution. The attack surface is no longer limited to enterprise systems. It now includes every connected endpoint in the network ecosystem. This creates new risks:
- Collapse of traditional security perimeters
- Unreliable network trust assumptions
- Attack execution within the communication fabric itself
For voice systems, this is critical. If the network layer is compromised, identity signals can be manipulated before reaching application-level controls. Security must extend beyond applications to include:
- Network-level identity verification
- Validation of communication paths
- Monitoring of infrastructure behavior
3. Cybercrime Ecosystems Are Industrializing
The hack-for-hire ecosystem has expanded into a structured, service-driven economy. Cybercrime now operates as a marketplace with specialized roles:
- Initial access brokers selling credentials
- Malware developers offering deployable tools
- Phishing kits packaged for non-technical actors
- Ransomware-as-a-service platforms
Attackers assemble capabilities rather than build them. This modular structure enables rapid scaling of attacks. Cyberattacks are no longer isolated operations. They are part of a global, service-driven economy. This introduces new challenges:
- Lower barriers to entry for attackers
- Rapid replication of attack techniques
- Simultaneous campaigns across industries
Defenders are no longer facing individual actors. They are facing an adaptive ecosystem. Security must evolve toward:
- Anticipating attack patterns
- Monitoring ecosystem-level signals
- Building resilience against repeatable attack models
4. Mobile and Identity-Based Threats Are Surging
Identity has become the primary attack surface. Stolen credentials can remain active for extended periods, allowing attackers to move laterally and escalate privileges. Identity-based breaches are consistently the most expensive form of cyber incident. Mobile devices play a central role:
- They serve as authentication endpoints
- They operate across multiple networks
- They often sit outside traditional controls
Once compromised, they enable attackers to operate as legitimate users. Mobile devices and identity systems are now primary entry points for cyberattacks. This changes the security model:
- Trust cannot rely on device or network location
- Authentication alone is insufficient
- Identity must be continuously validated
Security priorities must shift toward:
- Continuous identity verification
- Device integrity validation
- Behavioral monitoring
5. Enterprise Breaches Are Now Business Events
Cyber incidents are no longer technical failures. They are enterprise-level risk events. The average cost of a breach exceeds $4 million globally and is significantly higher in the United States. Impact includes:
- Revenue disruption
- Customer churn
- Regulatory penalties
- Long-term brand damage
Modern breaches are systemic. They affect multiple systems, workflows, and partners. Cyber incidents are material business events with direct financial impact. This requires:
- Integration of cybersecurity into enterprise risk strategy
- Alignment with business continuity and crisis management
- Board-level accountability
6. Supply Chain Attacks Are Targeting Trusted Systems
Supply chain attacks exploit the trust between organizations and their vendors. Major incidents such as the SolarWinds breach demonstrate how attackers insert malicious code into trusted software updates. These updates are then distributed to thousands of organizations, including government agencies. Recent vulnerabilities in widely used platforms have enabled attackers to gain persistent access through trusted software channels. Key patterns:
- Third-party vendors act as entry points
- Compromised updates bypass security controls
- Malicious activity appears legitimate
Attackers are no longer breaking systems. They are exploiting the systems enterprises already trust. Security must evolve toward:
- Continuous verification of software integrity
- Vendor risk monitoring
- Lifecycle-level trust validation
7. AI Is Reshaping Both Offense and Defense
Artificial intelligence is transforming both attack and defense capabilities. Attackers are using AI for:
- Automated reconnaissance
- Vulnerability discovery
- Phishing and impersonation
- Adaptive attack execution
At the same time, defenders are adopting AI for:
- Threat detection
- Automated response
- Predictive analysis
This creates a competitive dynamic where both sides are accelerating. Cybersecurity is entering an AI-driven arms race where speed defines advantage. Organizations must:
- Operate at machine speed
- Automate detection and response
- Continuously validate controls
What Just Happened: A Shift in Voice Security Architecture
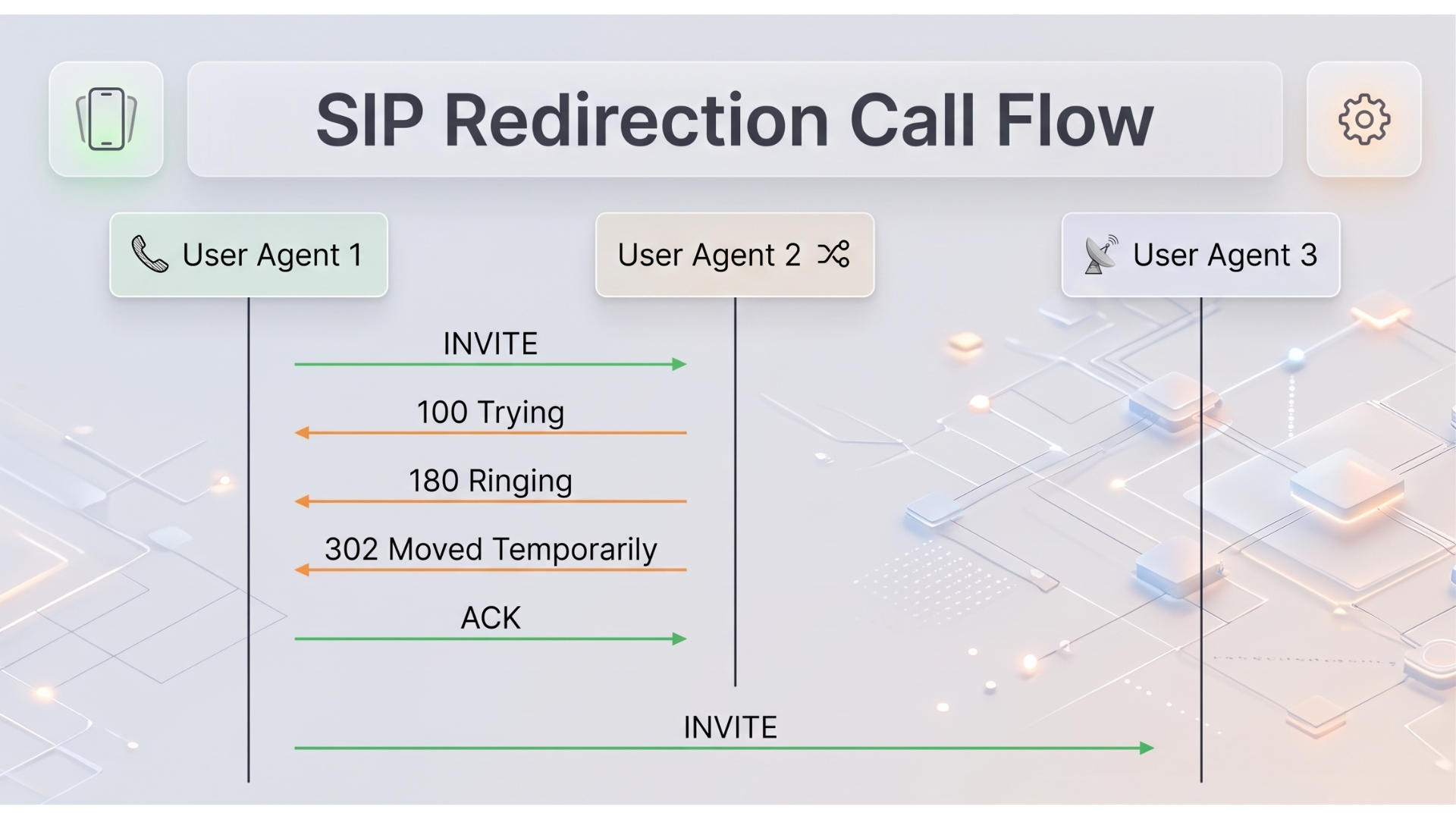
Key capabilities include:
- Pre-delivery authentication
- Validation of call integrity through signaling
- Controlled display of identity elements such as brand and intent
- Blocking or flagging of unverified calls
This approach integrates with enterprise platforms such as Microsoft Teams, Cisco, and Genesys. The significance lies in where identity is enforced. Trust is validated before interaction, not after. Business Impact: Why This Matters
- Higher answer rates from verified calls
- Reduced fraud exposure
- Improved customer trust
- Better compliance alignment
Voice is no longer a communication channel. It is a trust gateway to customer interaction and revenue.
CyberTech Intelligence POV: Network-Enforced Identity
A new security model is emerging. Network-Enforced Identity:
- Identity is verified before interaction
- Trust is enforced by infrastructure
- Communication channels act as security control planes
CyberTech Intelligence Framework: Voice Trust Enforcement Model
| Layer | Risk | Control |
| Identity | Caller spoofing | SIP-based validation |
| Delivery | Unverified routing | Pre-delivery authentication |
| Experience | Fake branding | Verified identity signals |
| Governance | Fragmented standards | Cross-network enforcement |
When Should You Act
Organizations should evaluate voice security if:
- Outbound calling is critical
- Answer rates are declining
- Customers report fraud
- Network-level identity validation is absent
Strategic Implications for Cybersecurity Leaders
- Expand threat models to include voice
- Align security with revenue and customer trust
- Prepare for multi-standard identity ecosystems
- Build cross-channel trust orchestration capabilities
The Future of Voice Identity
- Decline of anonymous calls
- Increased carrier-level enforcement
- Regulatory expansion
- Convergence of identity across channels
Final Thoughts: The Collapse of Implicit Trust
The future of communication security will not be defined by user authentication. It will be defined by whether communication channels can prove their identity before interaction begins. Voice is the first channel where this shift is visible and where failure to enforce trust is already impacting revenue, customer confidence, and brand integrity. Organizations that rely on application-layer identity will continue to secure interactions that should never have been trusted. This is a redefinition of where trust is established. The question is no longer: Can you verify your users? It is: Can your communication channels prove they deserve to be trusted before they reach your customers?
References
- Cybersecurity and Infrastructure Security Agency (2024) Cyber Threat Trends and AI Security Guidance
- Federal Communications Commission (2024) Robocall and Caller ID Spoofing Reports
- IBM Security (2024) Cost of a Data Breach Report
- SolarWinds (2020) Supply Chain Breach Incident Analysis
- National Institute of Standards and Technology (2024) Zero Trust Architecture Guidelines
🔒 Login or Register to continue reading