In today’s digitally interconnected world, protecting digital identities is important due to evolving cyber threats. Multi-Factor Authentication (MFA) is an essential security feature that offers effective protection against unauthorized access by requiring users to provide two or more verification factors to access a system. Since MFA adds layers of protection, it makes it much more difficult for attackers to break into accounts. To access resources like apps or online accounts, users must supply two or more authentication factors.
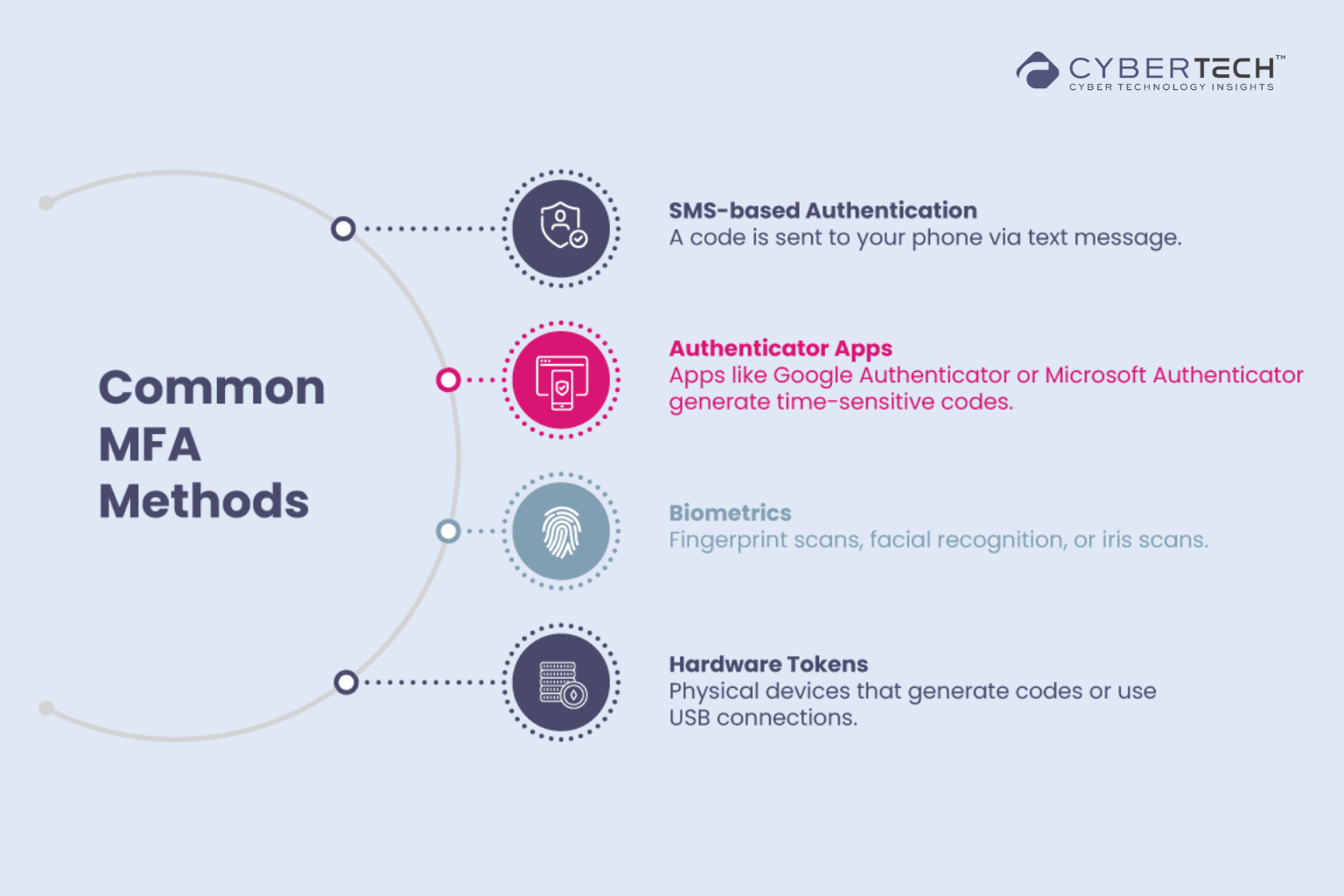
Furthermore, MFA overcomes common username and password limitations by integrating advanced authentication factors such as passwords, biometrics, or mobile devices. It reduces the risk of phishing attacks, protects accounts from data breaches, and alerts users to questionable login attempts. The primary goal of MFA is to enhance security measures and protect sensitive data from unauthorized access. MFA methods can be categorized into something you know (knowledge-based), something you have (possession-based), and something you are (inherence-based). Knowledge-based methods include passwords and security questions; possession-based methods involve OTPs and hardware tokens; and inherence-based methods use biometrics like fingerprints and facial recognition.
Recommended: Instantly Generate Spectrum Enterprise Fiber Contracts
Benefits of using MFA
Beyond only improving security, MFA is essential for adhering to industry standards that need robust authentication procedures. Additionally, by providing alerts for suspicious login attempts, MFA enhances organizational security responses while reducing the risks of human mistakes and lost credentials. In the end, MFA strengthens the dedication to data security by fostering trust among users and consumers in addition to protecting sensitive information.
Here are the key benefits of using MFA:
Enhanced Security: MFA enhances organizational security by requiring users to identify themselves through more than just a username and password, which are vulnerable to brute force attacks and theft. Enforcing MFA, such as using a thumbprint or hardware key, increases confidence in protecting against cybercriminals.
Mitigating Risks: MFA helps prevent password-related cyberattacks by requiring additional authentication methods, ensuring that even if a password is stolen, access remains restricted without the second authentication factor. It helps in keeping the system and data secure from the attacks.
Protection Against Phishing Attacks: MFA significantly bolsters security by demanding users present multiple verification factors, markedly reducing the success of cyberattacks and unauthorized access. By adding layers of security, MFA ensures that even if one factor, such as a password, is compromised, the attacker still needs to bypass additional verification methods.
Compliance: MFA helps organizations comply with industry regulations such as GDPR, HIPAA, and PCI-DSS, which often mandate strong authentication practices. Compliance can also extend to cyber insurance coverage, where MFA implementation may be a requirement.
Reduces Security Risks: MFA minimizes risks from human error, misplaced passwords, and lost devices. Moreover, it provides robust protection against phishing attacks. Since MFA often uses time-sensitive, non-reusable codes, it is less susceptible to phishing.
Recommended: Superna Integrates with CrowdStrike Falcon for Security
Improves Security Response: MFA reduces security risks stemming from human error, misplaced passwords, and lost devices. Companies can configure MFA systems to send alerts upon detecting suspicious login attempts, helping them respond faster to cyberattacks and minimize potential damage. In turn, implementing MFA instills a higher level of trust in users and customers, as they recognize their data is protected by advanced security measures.
Higher Level of Trust: Implementing MFA significantly boosts user and customer confidence, providing them with the assurance that their sensitive information is shielded by a robust, multi-layered security system. This fosters a stronger sense of security and reinforces trust in the organization’s commitment to data protection.
Maintaining Secure IT Infrastructure: MFA acts as a constant guardian of your IT environment. Continuous user identity verification strengthens the overall security posture and ensures a more resilient infrastructure by proactively reducing the risk of both internal and external threats.
MFA in 2025 and its Significance
MFA is poised to be a non-negotiable security measure for both businesses and individuals, playing a critical role in cybersecurity strategies. Some of the most prominent trends defining MFA in 2025 include a transition to cloudless authentication, Artificial Intelligence (AI) and Machine Learning integration, blockchain application for decentralized identity, and the emergence of cloud-first MFA solutions.
Here are MFA’s key trends in 2025:
Non-Negotiable Security Measure: MFA will be a standard security measure for businesses and individuals, significantly reducing unauthorized access.
Passwordless Authentication: Passwordless authentication methods, such as biometrics, knowledge factors (PINs), and hardware tokens, will gain prominence due to their enhanced security and user-friendliness. A majority of organizations are expected to shift to passwordless solutions as their default authentication method.
Recommended: CrowdStrike Unveils Charlotte AI for Advanced Cybersecurity
AI and Machine Learning Integration: MFA systems will incorporate AI and machine learning to customize authentication processes according to behavioral and contextual factors, improving security and reducing friction. MFA powered by AI will spot anomalies that point to possible dangers.
Blockchain and Decentralized Identity: Blockchain technology will support decentralized identity systems, giving users ownership of their virtual identities and reducing reliance on vulnerable centralized databases.
Cloud-First MFA Solutions: There will be a surge in demand for cloud-native MFA solutions that provide flexible and scalable authentication across remote and hybrid networks. Cloud-first MFA solutions will also see increased demand, offering flexible and scalable authentication across remote and hybrid networks.
Biometric Innovations: Biometric authentication will expand with innovations in facial recognition, iris scanning, voice authentication, and behavioral biometrics, making MFA more sophisticated. Blockchain technology will back decentralized identity systems, providing users with ownership of their virtual identities and reducing reliance on centralized databases.
Zero Trust Framework: There will be an increased adoption of the Zero Trust framework, mandating continuous monitoring of authenticated users to mitigate insider threats.
Overall, 2025 will see a significant revolution in MFA systems, with a shift towards passwordless mechanisms, improved biometric authentication, and the integration of AI and Machine Learning. MFA will also find major acceptance among Small and Medium Enterprises (SMEs) as technology advances and the cost of installation reduces.
Recommended: Wolf Richter named CEO of Security Research Labs
Conclusion
MFA is not merely an option but a necessity for robust digital identity protection. MFA considerably lowers the risk of unauthorized access by requiring two or more verification factors, lessening the impact of brute force assaults, phishing, and compromised credentials. It helps with regulatory compliance, builds user trust, and improves corporate security. MFA’s proactive strategy guarantees a robust IT infrastructure and protects sensitive data. Utilizing knowledge-based, possession-based, and inherence-based methods, MFA provides a multi-layered defense against evolving cyber threats. Embracing MFA is a strategic investment in a secure and trustworthy digital environment, essential for individuals and organizations alike. In 2025, MFA is set to become an essential security measure for both businesses and individuals, significantly enhancing cybersecurity frameworks. This evolution will be driven by several key trends that reflect the changing landscape of digital security.
To share your insights, please write to us at news@intentamplify.com
🔒 Login or Register to continue reading







