In an era where cyber threats are increasingly sophisticated, organizations must adopt robust strategies to safeguard their assets. Effective cyber risk management hinges on the implementation of robust Cybersecurity Frameworks (CSFs). Given the escalating sophistication and frequency of cyberattacks, the NIST CSF, CIS Controls, and ISO 27001 offer indispensable guidance for proactive risk mitigation. These widely accepted frameworks provide structured approaches for organizations to strengthen their security defenses. The adoption of these CSFs enables organizations to improve their security posture, simplify compliance processes, and cultivate a proactive risk management culture. Utilizing these frameworks allows businesses to effectively navigate the challenging cybersecurity environment and develop resilience against emerging threats.
These frameworks collectively facilitate regulatory compliance and foster a security-conscious environment throughout the organization. Their implementation allows for the systematic identification and remediation of vulnerabilities, improved incident response procedures, and ultimately, increased resilience against cyberattacks. CSFs are an indispensable tool for organizations seeking to effectively manage and reduce cyber risks.
Recommended: Cybersecurity Simplified: What is Cloud Infrastructure Security?
Overview of NIST CSF, CIS Controls, and ISO 27001
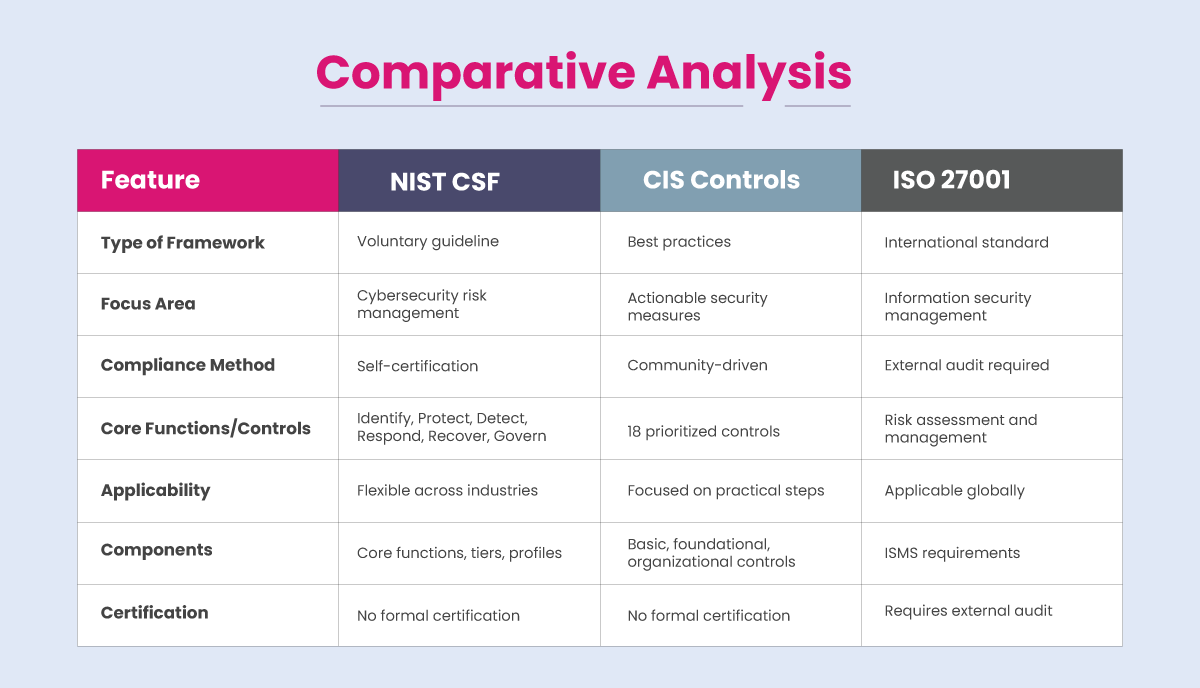
Organizations can strengthen their security posture using structured approaches provided by CSFs such as the NIST CSF, CIS Controls, and ISO 27001. These foundational frameworks offer distinct methodologies and focal points for building robust cybersecurity practices. The unique advantages and emphases of each framework collectively contribute to a comprehensive organizational cybersecurity strategy.
NIST Cybersecurity Framework (CSF)
Developed by the National Institute of Standards and Technology (NIST), the NIST CSF provides a flexible approach for organizations to manage and reduce cybersecurity risk. The framework consists of five core functions: Protect, Identify, Respond, Detect, and Recover, with the recent update in early 2024 (version 2.0) introducing a sixth function: Govern. This flexibility allows diverse organizations to tailor their cybersecurity strategies effectively. This framework emphasizes a risk-based approach to cybersecurity, allowing organizations to tailor their strategies based on specific threats and business needs. Its adaptability makes it suitable for various sectors, promoting continuous improvement in cybersecurity practices.
NIST CSF consists of three main components:
- Core: This outlines five key functions— Protect, Identify, Respond, Detect, Recover—which serve as a high-level taxonomy for managing cybersecurity risks.
- Implementation Tiers: These provide context regarding an organization’s cybersecurity risk management practices, ranging from Tier 1 (Partial) to Tier 4 (Adaptive).
- Profiles: These allow organizations to customize their approach based on specific risk profiles and needs.
Recommended: Cybersecurity Simplified: LLMjacking Attacks
Benefits:
- Improved Security Posture: By implementing the NIST CSF, organizations can systematically identify and address security gaps, enhancing their overall security posture.
- Flexibility: The framework allows organizations to tailor their cybersecurity strategies according to specific needs and risk profiles.
- Compliance Facilitation: While compliance is voluntary, aligning with NIST standards can help organizations meet various regulatory requirements.
CIS Controls
The CIS Controls are a collection of best practices developed by the Center for Internet Security (CIS) to reduce the most prevalent cyber threats. These controls give organizations a clear road map for improving their security posture since they are actionable and prioritized. These controls are based on actual data and are often modified to reflect current challenges. CIS Controls is frequently seen as a useful implementation manual that enhances frameworks like the NIST CSF by offering specific steps that companies can follow to improve their security.
The controls are divided into three categories:
- Basic Controls: Foundational measures that every organization should implement.
- Foundational Controls: Essential for building a strong security posture.
- Organizational Controls: Focus on governance and risk management.
Benefits:
- Prioritization of Security Measures: The CIS Controls help organizations focus on the most critical areas that can effectively reduce risk.
- Community-Driven Development: To ensure their applicability and efficacy, these controls are often updated in response to community input and real-world threat data.
Recommended: McAfee Introduces Cutting-Edge AI Scam Detector to Shield Users from Digital Deception
ISO 27001
The international standard ISO 27001 provides a framework for the creation, execution, upkeep, and ongoing enhancement of an Information Security Management System (ISMS). As an international standard for ISMS, ISO 27001 outlines a systematic approach to managing sensitive company information. It lays a strong emphasis on risk assessment and management, making sure that businesses put in place the right security measures to safeguard the availability, confidentiality, and integrity of data. For businesses looking to protect their information assets through a systematic approach to risk management and ongoing security practice improvement, ISO 27001 provides an essential foundation. ISO 27001 is widely recognized across industries and is often a prerequisite for doing business with large enterprises due to its rigorous compliance requirements. Certification under ISO 27001 demonstrates an organization’s commitment to maintaining high security standards.
Key features include:
- Risk-Based Approach: ISO 27001 emphasizes identifying and managing information security risks through a systematic process.
- Certification Requirement: Unlike NIST CSF, ISO 27001 requires organizations to undergo external audits by accredited bodies to achieve certification.
- Control Framework: The standard includes Annex A, which provides 14 control categories comprising 114 controls aimed at protecting information assets.
Benefits:
- Independent Certification: Achieving ISO 27001 certification involves an external audit process, which can enhance stakeholder confidence in an organization’s security practices.
- Comprehensive Risk Management: ISO 27001 offers a methodical framework for identifying, evaluating, and thoroughly addressing information security threats.
How can organizations leverage NIST CSF, CIS Controls, and ISO 27001 for enhanced cybersecurity?
Adoption of the NIST Cybersecurity Framework, CIS Controls, and ISO 27001 standards significantly improves an organization’s cybersecurity defenses. The combined application of these frameworks’ advantages allows the development of a robust and all-encompassing cybersecurity program. This program not only ensures compliance with regulations but also fortifies the organization’s ability to withstand emerging cyber threats.
Recommended: Top AI Security Tools for Financial Services Industry
Here’s how organizations can effectively integrate these frameworks:
Holistic Risk Management
Risk assessment and management are emphasized in both ISO 27001 and the NIST CSF. While implementing ISO 27001’s systematic approach to creating an ISMS into practice, organizations can use the NIST CSF to identify and prioritize risks. This combination guarantees a thorough comprehension of risks and the implementation of suitable controls.
Both ISO 27001 and the NIST CSF underscore the critical importance of risk assessment and mitigation. Organizations implementing ISO 27001’s Structured ISMS methodology can leverage the NIST CSF for effective risk identification and prioritization. This integrated strategy ensures a comprehensive understanding of risks and facilitates the deployment of appropriate safeguards.
Actionable Best Practices
The CIS Controls provide specific, actionable steps that organizations can implement to mitigate common cyber threats. Organizations can develop a strong security plan that tackles both short-term vulnerabilities and long-term security objectives by combining these controls with the more comprehensive NIST CSF recommendations and the methodical approach of ISO 27001.
Compliance and Certification
While the NIST CSF is voluntary and focuses on best practices, ISO 27001 requires formal certification through independent audits. After establishing fundamental security procedures with NIST CSF, organizations can move to ISO 27001 for official certification and compliance, which will increase their credibility with stakeholders.
Continuous Improvement
The significance of continuous monitoring and improvement is emphasized in all three CSFs. To ensure continuous compliance and improvement of their security measures, organizations can use ISO 27001’s audit procedures in conjunction with metrics and performance indicators based on the NIST CSF’s core functions.
Stakeholder Communication
Achieving ISO 27001 certification demonstrates a commitment to information security, which can enhance trust among clients and partners. Coupled with the practical guidelines from the NIST CSF and actionable measures from the CIS Controls, organizations can effectively communicate their cybersecurity efforts to stakeholders.
Recommended: Cyber Insurance: Risks and Trends 2025
Conclusion
The implementation of CSFs—ISO 27001, CIS Controls, and NIST CSF—has a major impact on an organization’s ability to manage cyber threats effectively. Each CSF has a distinct function in improving the cybersecurity of organizations. The CIS Controls offer concrete steps for immediate improvement, while the NIST CSF offers a thorough framework appropriate for a range of enterprises. ISO 27001 establishes a structured approach for managing information security that prioritizes certification and compliance. When combined, these frameworks strengthen an organization’s defenses against evolving cyber threats and guarantee adherence to pertinent laws. Organizations can develop a thorough CSF that not only reduces risk but also builds resilience against changing cyber threats by carefully combining the NIST CSF, CIS Controls, and ISO 27001. Integrating components from all three CSFs can help organizations strengthen their cybersecurity strategies.
To share your insights, please write to us at info@intentamplify.com
🔒 Login or Register to continue reading











