In Formula 1, races are no longer won on the track alone. They are won in the pit. Decisions made in under three seconds determine whether a driver gains position or loses the race.
A similar pattern is playing out across global enterprises.
When a major streaming platform experiences an outage or when an AI system produces a high-profile failure, the issue is rarely just the event itself.
The real damage comes from how long it takes to understand what’s happening and respond.
According to IBM Security, the mean breach lifecycle (MTTI + MTTC) exceeds 270 days, with the global average breach cost approaching $4.9 million.
This is not a detection failure. It is a failure to compress time-to-decision across the incident lifecycle. Security Operations Platforms (SecOps Platforms) are emerging to solve this.
What Are Security Operations Platforms?
Security Operations Platforms (SecOps Platforms) are integrated systems designed to unify, analyze, and operationalize security data across the enterprise.
They move beyond traditional point solutions like SIEM, SOAR, or EDR by acting as a central decision layer that connects detection, context, and response.
At their core, these platforms are built to answer one question: What action should be taken, and how quickly, to minimize risk?
#Core Function 1
Unified Data Ingestion and Normalization
Aggregates telemetry from endpoints, networks, cloud, and identity systems into a standardized format, enabling consistent analysis across environments.
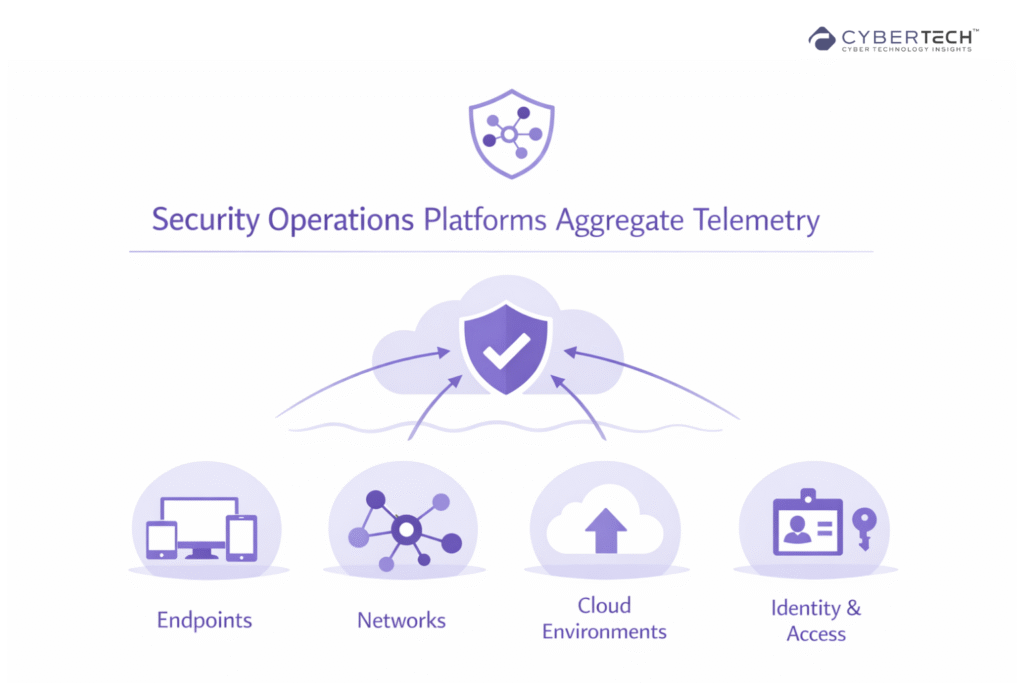
They normalize this data into a consistent structure, enabling cross-domain correlation.
Why It Matters
Without normalization, security teams operate across fragmented datasets, slowing investigations.
Business Impact
Faster data correlation reduces investigation time, directly improving MTTR and lowering incident response costs.
Organizations using AI-driven security analytics and automation shorten breach lifecycles by up to 80–100 days and reduce costs by nearly $2 million per incident, according to IBM.
#Core Function 2
Contextual Correlation and Signal Enrichment
Enhances raw alerts with asset, user, and threat intelligence context to convert isolated signals into prioritized, actionable incidents.
Platforms enrich raw alerts with:
- Asset criticality.
- User and identity context.
- Threat intelligence feeds.
This transforms isolated alerts into contextualized security incidents.
Why It Matters
Context determines priority.
Business Impact
Improved prioritization ensures teams focus on high-impact threats, reducing the likelihood of costly breaches.
#Core Function 3
Attack Path Analysis – Case Example
Capital One Breach (2019)
In 2019, Capital One experienced a breach affecting over 100 million customers, driven by a chain of cloud and identity misconfigurations.
Attack Path
- A misconfigured web application firewall exposed an entry point.
- An SSRF exploit enabled access to cloud metadata.
- The attacker obtained IAM credentials with excessive permissions.
- Lateral movement across cloud storage led to access to sensitive data.
Why It Matters
None of these issues alone were critical. Together, they formed a complete attack path to high-value assets.
Business Impact
Estimated $100M+ in breach-related costs, including fines, remediation, and legal settlements
Significant regulatory scrutiny and long-term compliance implications. Erosion of customer trust and brand credibility in a highly competitive market
#Core Function 4
Decision-Augmented Automation
Applies AI-driven triage and risk scoring to automate high-confidence actions while supporting faster, more accurate human decisions.
Security Operations Platforms integrate automation that supports decision-making through:
- AI-assisted triage.
- Risk-based alert scoring.
- Automated containment actions.
Why It Matters
Automation accelerates response only when it is context-aware.
Business Impact
Reduced manual effort lowers operational costs, while faster response times minimize downtime and financial impact.
Forrester reports that security automation can reduce manual investigation effort by up to 40%, enabling faster incident resolution and lower SOC operating costs.
#Core Function 5
Incident Orchestration and Response Management
Coordinates investigation, containment, and remediation workflows across tools and teams through a centralized control layer.
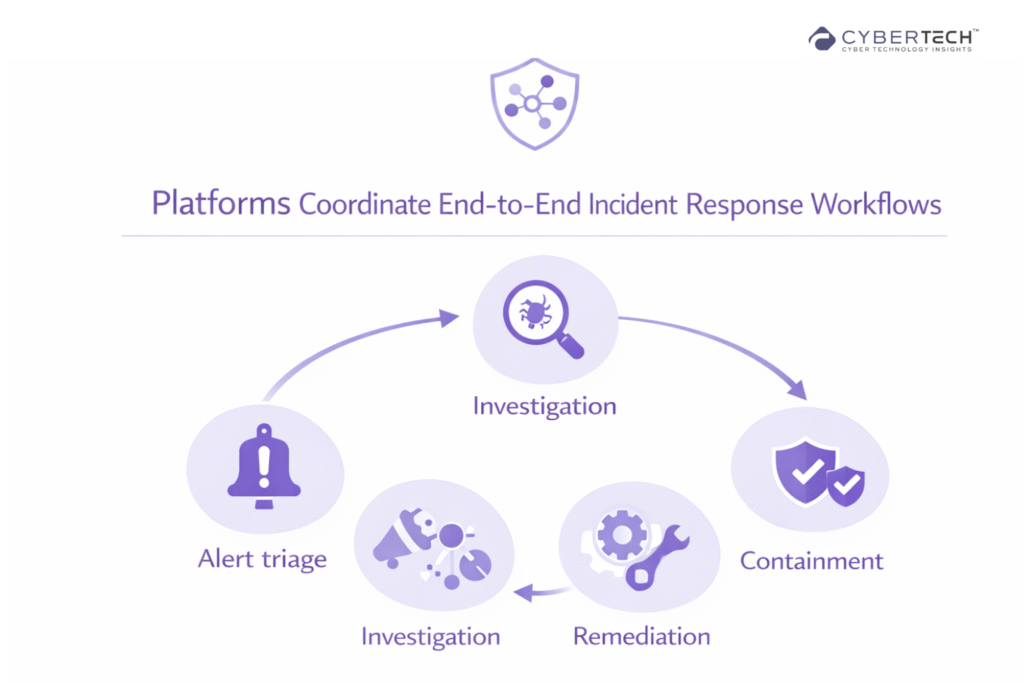
They provide a unified interface for managing incidents across tools and teams.
Why It Matters
Disjointed workflows create delays and inconsistencies.
Business Impact
Streamlined response processes improve operational efficiency and reduce breach lifecycle duration.

#Core Function 6
Risk Quantification and Reporting
Translates technical security data into business-aligned risk metrics and financial impact insights for executive visibility.
Security Operations Platforms translate technical signals into:
- Risk scores.
- Financial exposure estimates.
- Executive-level dashboards.
Why It Matters
Security must align with business priorities.
Business Impact
Quantified risk enables better budget allocation, board communication, and strategic decision-making.
Common Misconception: More Visibility Means Better Security
A persistent assumption in cybersecurity is that increased visibility directly improves security outcomes. This no longer holds true.
Modern security stacks. Including SIEM, XDR, and AI-driven detection systems. Already provides extensive telemetry across endpoints, networks, cloud, and identity layers.
Yet organizations continue to face:
- Alert fatigue driven by high-volume, low-fidelity detections.
- Extended MTTR due to manual triage and fragmented workflows.
- Escalating breach costs despite increased tooling investment.
The constraint is the inability to prioritize, correlate, and act on signals within the operational decision window.
How to Build a Decision-Intelligent Security Model
1. Unify and Enrich Security Data
Integrate telemetry across:
- Endpoints
- Cloud environments
- Identity systems
Enrich signals with context to enable faster, more accurate decisions.
2. Prioritize Based on Risk, Not Volume
Shift from vulnerability counts to exploitability and attack paths. This ensures focus on high-impact threats.
3. Implement Context-Aware Automation
Use AI to:
- Reduce manual triage.
- Accelerate response decisions.
- Improve consistency.
Ensure automation is continuously validated to avoid false confidence.
4. Measure Decision Speed as a KPI
Track:
- Time-to-decision.
- Time-to-containment.
- Decision accuracy.
These metrics provide a more accurate view of security effectiveness.
The Future of Security Operations
AI is rapidly transforming cybersecurity by automating threat detection, enhancing response capabilities, and enabling predictive security models.
According to McKinsey & Company, while organizations have improved their response times to cyber incidents, it still takes an average of 73 days to contain a breach, underscoring the persistent challenge of timely containment.
Over the next 24 months, leading organizations will:
- Shift to platform-based SecOps models.
- Use AI for decision support, not just detection.
- Quantify cyber risk in financial terms.
Key Takeaways
- Security performance is now defined by decision speed, not detection capability
- AI improves outcomes only when paired with decision intelligence
- Attack path visibility is critical for risk-based prioritization
- Automation must enhance decision accuracy, not just execution
- Security leaders must translate operations into business impact
Closing Insight
In modern security operations, advantage is not defined by who detects first, but by who decides and acts before the attack path is realized.
Organizations that fail to make this shift will continue to operate in a reactive model, where speed is lost to complexity.
Those who succeed will redefine security as a real-time risk management function, directly tied to resilience, revenue protection, and competitive advantage.
FAQs
1. What is a Security Operations Platform and how is it different from SIEM or SOAR?
A Security Operations Platform is a unified system that connects detection, context, and response into a single decision layer. Unlike SIEM, which focuses on log aggregation, or SOAR, which automates workflows, a SecOps platform prioritizes actions based on risk and business impact, enabling faster and more accurate decision-making.
2. Why are enterprises shifting from detection-focused security to decision intelligence?
Detection tools generate large volumes of alerts, but most organizations struggle to act on them quickly. Decision intelligence focuses on prioritizing, correlating, and responding to threats in real time, reducing response delays, lowering breach costs, and improving overall security effectiveness.
3. How do Security Operations Platforms reduce incident response time?
They reduce response time by unifying data across systems, enriching alerts with context, and applying AI-driven prioritization. This allows security teams to identify high-risk threats faster and automate appropriate responses, significantly improving time-to-containment.
4. What role does AI play in modern security operations?
AI enhances security operations by automating alert triage, identifying attack patterns, and supporting faster decision-making. When combined with contextual data, AI helps reduce manual workload, improve accuracy, and enable proactive threat response rather than reactive mitigation.
5. How should CISOs measure the effectiveness of their security operations?
Effectiveness should be measured using decision-centric metrics such as time-to-decision, time-to-containment, and response accuracy. These metrics provide a clearer view of operational performance than traditional measures like alert volume or detection rates.
To participate in upcoming interviews, please reach out to our CyberTech Media Room at info@intentamplify.com.
🔒 Login or Register to continue reading












