Zero trust architecture has evolved into an operational necessity for modern enterprises. It rejects the idea that anything inside a corporate network should be automatically trusted.
Every request, whether it originates from inside the network or outside, must be authenticated, authorized, and continuously validated before access is granted. That principle sounds straightforward. However, implementing it across distributed enterprise environments is not.
The shift toward zero trust architecture reflects a deeper structural change in how enterprise systems operate. Cloud infrastructure, SaaS ecosystems, hybrid workforces, and API-driven applications have dissolved the traditional network perimeter.
Security leaders are no longer protecting a clearly defined network boundary. They are securing a constantly shifting digital environment where users, workloads, and data move across multiple platforms.
Instead of defending a perimeter that no longer exists, the model focuses on verifying every interaction across the enterprise environment.
The Structural Drivers Behind Zero Trust Adoption
Zero Trust Architecture did not emerge simply because vendors needed a new marketing category. It emerged because enterprise infrastructure changed in ways that made traditional security models increasingly ineffective.
Three shifts in particular reshaped the threat landscape.
First, identity has become the dominant attack surface.
Modern attackers rarely attempt to break through hardened network defenses directly. Instead, they target credentials. Phishing campaigns, credential stuffing, and malware designed to harvest authentication tokens have become common entry points for breaches.
IBM’s Cost of a Data Breach Report continues to identify compromised credentials as one of the most frequent initial attack vectors in enterprise incidents.
Once attackers obtain valid credentials, traditional network security often fails to detect them. From a system perspective, the attacker appears to be a legitimate user.
Zero Trust attempts to mitigate this risk by continuously evaluating identity signals rather than granting persistent access based on a single authentication event.
Second, enterprise infrastructure has become inherently distributed.
Organizations no longer operate primarily inside corporate data centers. Applications run across multiple public cloud providers. Employees access systems remotely from unmanaged devices. Business processes depend on SaaS platforms hosted entirely outside the corporate network.
Security architectures designed for centralized infrastructure struggle in this environment. Visibility declines as workloads spread across platforms. Access control policies become harder to enforce consistently.
Zero Trust attempts to restore control by shifting security decisions closer to identity, application, and data layers.
Third, regulatory and government frameworks are reinforcing zero trust principles.
In the United States, federal agencies are required to adopt zero trust security models under national cybersecurity directives. Similar expectations are emerging in European regulatory frameworks such as the NIS2 directive.
These policies do not mandate specific technologies. They emphasize architectural principles. Continuous authentication. Least privilege access. Segmentation of critical systems.
Zero Trust Adoption Is Expanding, But Maturity Varies
Security leaders broadly agree that Zero trust represents the direction enterprise security must move. The challenge lies in translating theory into operational architecture.
In many environments, Zero trust appears as a collection of isolated controls:
- Multi-factor authentication deployed across employee accounts.
- Endpoint detection platforms evaluating device health.
- Cloud access policies restricting application access.
Individually, these technologies improve security posture. Collectively, they do not automatically form a Zero trust architecture.
True zero trust requires coordination across identity systems, network infrastructure, endpoint telemetry, and data governance frameworks.
That level of integration remains difficult.
Identity Is Becoming the Core Enforcement Layer
In most zero trust deployments, identity infrastructure becomes the central decision engine.
Every access request is evaluated based on identity signals such as user credentials, authentication strength, behavioral patterns, and device context.
This approach transforms identity platforms from simple authentication systems into security control planes.
Identity providers now enforce adaptive authentication policies. If a user attempts to access sensitive systems from an unfamiliar location or device, additional verification may be required.
Risk signals from endpoint monitoring platforms or behavioral analytics tools can trigger further restrictions.
These capabilities allow organizations to shift from static access permissions toward dynamic authorization decisions.
But identity-centric security also introduces new dependencies.
Identity infrastructure becomes mission-critical. Misconfigured policies can disrupt entire organizations. Outages within identity systems can cascade across enterprise applications.
Zero trust reduces certain risks while amplifying others.
The Network Perimeter Has Not Disappeared: It Has Fragmented.
Some discussions around zero trust suggest that networks no longer matter. That identity alone can secure enterprise environments.
Reality is more complicated.
Enterprise networks still exist. They simply span multiple environments simultaneously. On-premise infrastructure. Cloud platforms. SaaS providers. Edge locations. Partner networks.
Each environment introduces its own networking model, security controls, and visibility limitations.
Micro-segmentation emerged as a key technique for managing this complexity. Instead of relying on broad network zones, organizations isolate individual workloads or applications using granular access policies.
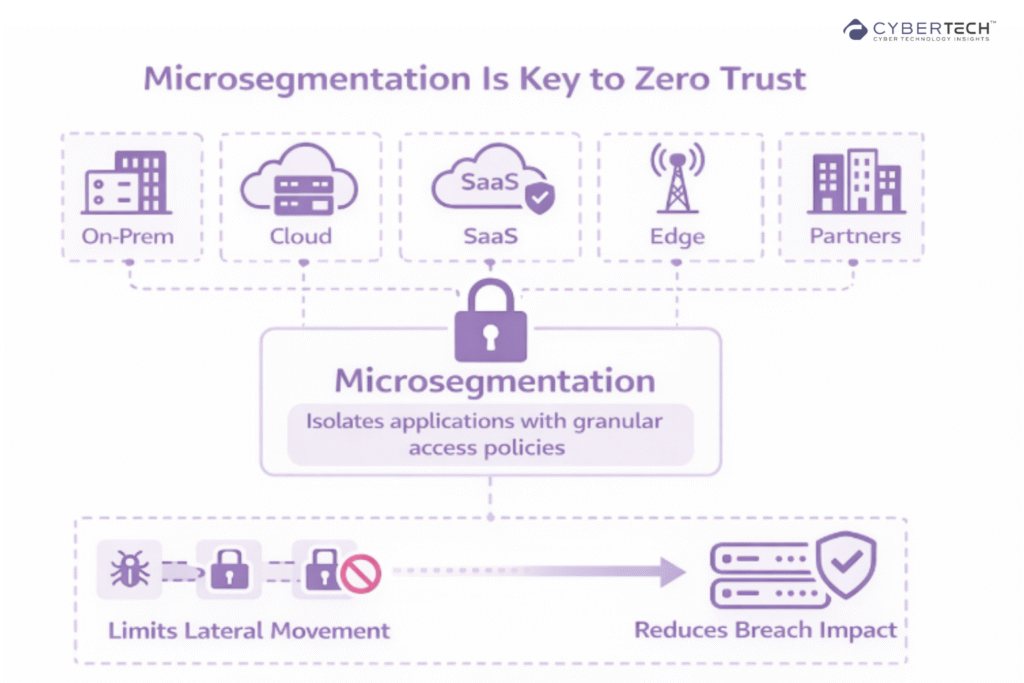
If attackers compromise one segment, their ability to move laterally across the environment becomes restricted.
Micro-segmentation can significantly reduce breach impact. But at scale, it introduces operational challenges. Policy management becomes complex.
Application dependencies must be mapped carefully to avoid disrupting legitimate traffic.
Segmentation improves security posture. It also increases architectural complexity.
Zero Trust Network Access Is Replacing VPNs
One of the most visible shifts within enterprise security architecture involves remote access infrastructure.
Traditional VPNs provide users with network-level access once authentication succeeds. This model assumes that internal networks are inherently trusted environments.
Zero trust network access platforms operate differently.
Instead of granting access to entire networks, ZTNA solutions connect users directly to specific applications. Authentication occurs at the application layer.
Access decisions consider multiple contextual signals, including device health, location, and behavioral risk indicators.
As a result, many enterprises operate hybrid environments where VPN and Zero Trust access systems coexist.
Security transformations rarely occur overnight.
Endpoint Security Is Becoming More Strategic
In a zero trust architecture, device posture plays a critical role in access decisions.
If compromised devices can access sensitive applications, identity verification alone is insufficient.
Endpoint data detection and response platforms therefore, supply telemetry used to evaluate device security posture. Systems that fail compliance checks may be restricted from accessing certain resources.
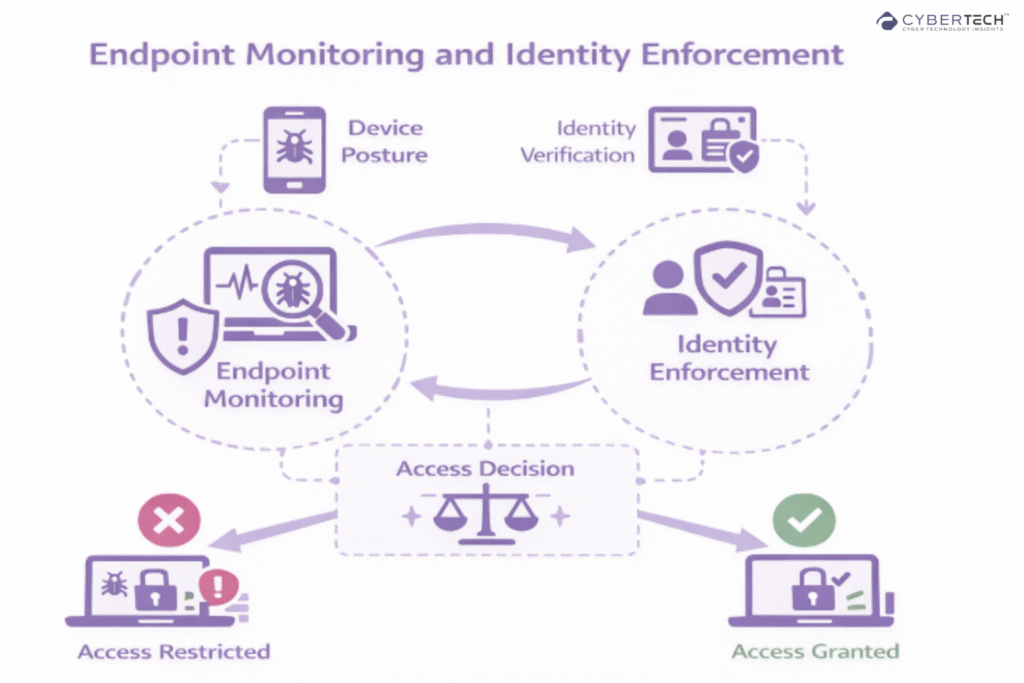
This integration between endpoint monitoring and identity enforcement allows security teams to respond dynamically to potential compromises.
The approach works well in theory. In practice, it requires tight integration between tools that historically operated independently.
Operational coordination becomes essential.
Data Governance Is Emerging as the Next Layer
Early zero trust implementations focused primarily on infrastructure controls. Identity, network segmentation, endpoint security.
Increasingly, attention is shifting toward data-centric zero trust models.
Gartner predicts that by 2028 roughly 50 percent of organizations will adopt zero trust-based data governance frameworks to address risks associated with unverified data sources and AI-generated content.
This evolution reflects the growing importance of data pipelines within modern enterprises.
Machine learning models rely on vast datasets. Business decisions increasingly depend on automated analytics platforms. Sensitive information flows across cloud platforms continuously.
Protecting infrastructure alone does not guarantee data integrity.
Zero trust principles applied to data governance emphasize verifying how data is accessed, transformed, and shared across digital environments.
Still a developing discipline.
Platform Consolidation Is Reshaping the Vendor Landscape
Another trend unfolding alongside zero trust adoption is the consolidation of enterprise security platforms.
Historically, organizations assembled complex security stacks composed of dozens of independent tools. Identity management systems, network firewalls, endpoint monitoring platforms and data protection solutions.
Operationally, this model proved difficult to sustain.
Security analysts often struggle to correlate alerts across disconnected systems. Visibility gaps appear where telemetry does not integrate.
Zero trust architectures rely heavily on contextual signals from multiple sources. Identity signals, device telemetry, network activity, behavioral analytics.
Integrated security platforms simplify this process by centralizing telemetry and policy enforcement.
Major vendors increasingly position themselves as providers of zero trust ecosystems rather than standalone tools.
This consolidation improves operational efficiency. It also increases the risk of vendor lock-in.
Security leaders must weigh both outcomes carefully.
Choosing the Right Community Platform for Enterprise Outcomes
Community platforms vary widely in how they support enterprise marketing, customer success, and product insight. Some prioritize deep CRM integration and analytics. Others focus on flexibility, ease of launch, or professional networking features.
Understanding those trade-offs is critical when communities are expected to influence retention, product adoption, or pipeline development.
Enterprise platforms like Higher Logic and Khoros are often chosen by organizations that need deep integration with CRM and support systems.
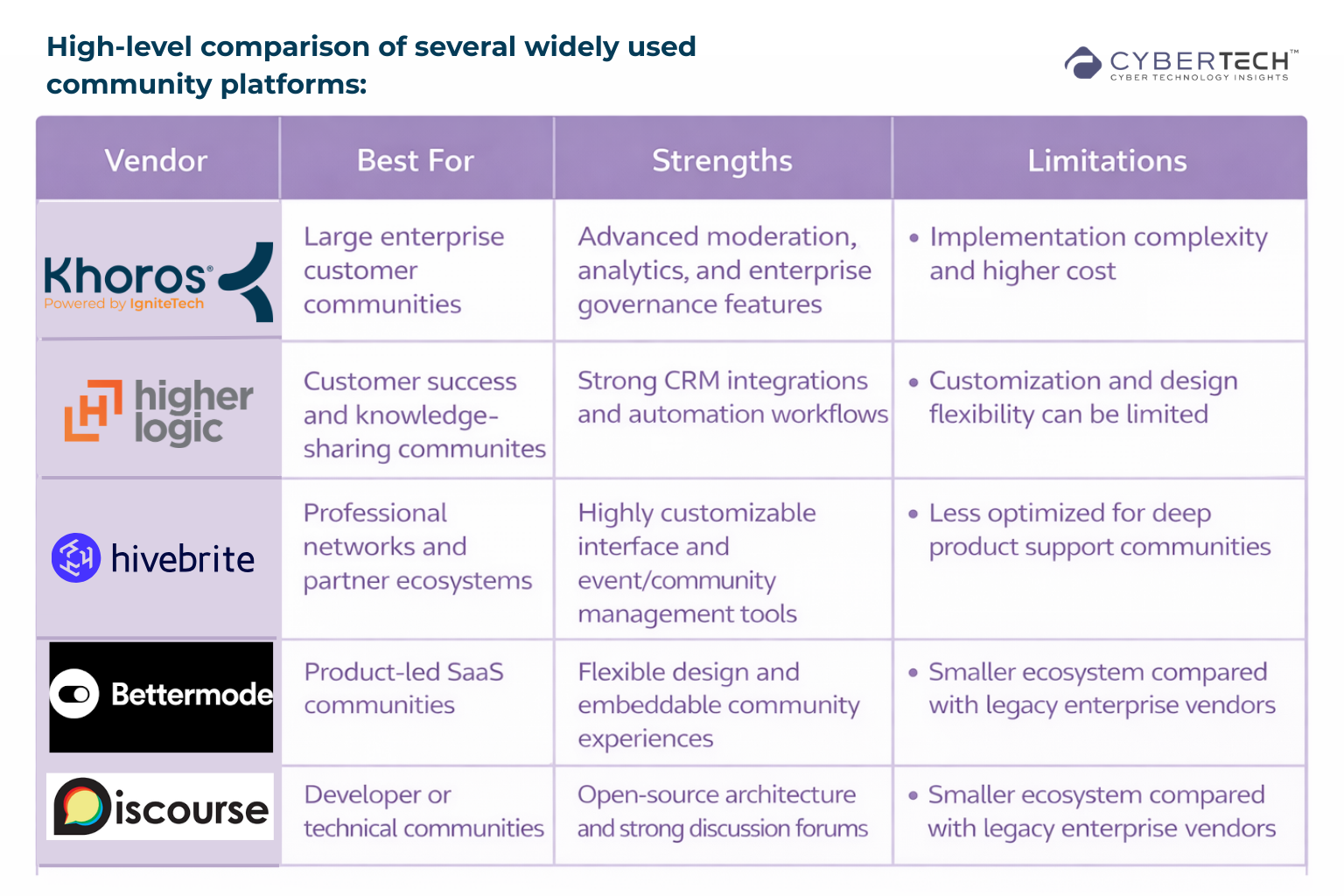
These platforms can act as hubs for customer insight and knowledge sharing across departments.
Newer platforms such as Bettermode or Hivebrite tend to emphasize customization and faster deployment, making them attractive for companies experimenting with community-led growth initiatives.
In practice, the “best” vendor is rarely universal. Companies prioritizing support deflection and product education often gravitate toward enterprise-grade platforms.
Organizations focused on networking, thought leadership, or partner ecosystems may prefer more flexible community tools.
AI is rapidly transforming cloud security. From real-time threat detection to identity intelligence, security operations are becoming increasingly automated and adaptive.
Read how AI is reshaping cloud security operations and enterprise defense strategies.
Zero Trust Is an Evolution, Not a Destination
Zero trust architecture continues to evolve as enterprise environments change.
Artificial intelligence will likely play a larger role in evaluating behavioral risk signals. Security platforms already analyze user activity patterns to detect anomalies that static policies might miss.
Meanwhile enterprise infrastructure continues expanding across cloud platforms, edge environments, and automated systems.
Security models built around implicit trust cannot keep pace with that complexity.
Zero trust architecture does not eliminate risk entirely. It reduces the assumptions attackers rely on.
In modern enterprise environments, reducing assumptions may be the most practical defense strategy available.
FAQs
1. What is zero trust architecture in enterprise security?
Zero trust architecture is a security model where no user, device, or system is trusted by default. Every access request must be continuously verified using identity, device health, and context.
2. Why are enterprises adopting zero trust security models?
Hybrid cloud, remote work, and identity-based attacks have expanded the enterprise attack surface. Zero trust limits lateral movement by enforcing strict identity verification and least-privilege access.
3. What are the core pillars of zero trust architecture?
The five core pillars include identity, devices, networks, applications, and data. Together, they enforce continuous verification and granular access control across enterprise systems.
4. How long does it take to implement zero trust in large enterprises?
Most large enterprises implement Zero trust gradually over two to five years. Deployment typically begins with identity security and expands to network segmentation and data protection.
5. How is zero trust different from traditional network security?
Traditional security trusts users once they enter the network. Zero trust continuously verifies access and restricts permissions regardless of location.
Discover expert analysis and real-world CyberTech strategies at CyberTechnology Insights.
To participate in upcoming interviews, please reach out to our CyberTech Media Room at info@intentamplify.com.







