Security Information and Event Management (SIEM) is a cybersecurity platform that collects, normalizes, correlates, and analyzes security data across an organization’s entire IT environment to detect threats and enable response.
At its core, SIEM turns fragmented signals into actionable intelligence.
It aggregates logs from systems like firewalls, endpoints, identity providers, and cloud platforms, then applies correlation and analytics to identify suspicious activity patterns.
How SIEM Architecture Works in Enterprise Environments
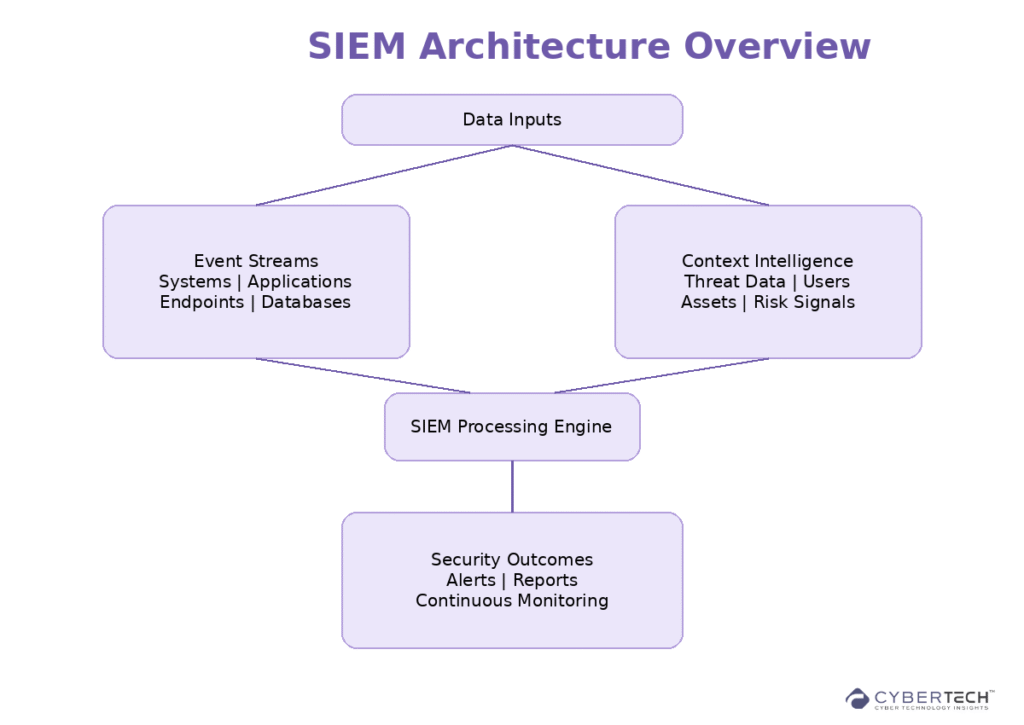
A modern SIEM architecture typically includes:
1. Data Ingestion Layer
Collects logs and telemetry from:
- Endpoints and servers.
- Firewalls and network devices.
- Cloud platforms (AWS, Azure, SaaS).
- Identity systems (IAM, Active Directory).
2. Normalization and Storage
Transforms diverse data formats into a standardized schema and stores them for real-time and historical analysis.
3. Correlation and Analytics Engine
This is where SIEM creates value:
- Rule-based correlation.
- Behavioral analytics (UEBA).
- Machine learning-driven anomaly detection.
SIEM systems process massive volumes of logs daily, often millions of events, to identify threats in real time.
4. Alerting and Prioritization
Flags suspicious activity and reduces noise using:
- Risk scoring.
- Alert enrichment.
- Contextual intelligence.
5. SOC Integration and Response
Feeds into Security Operations workflows:
- Incident investigation.
- Threat hunting.
- Automated or manual response.
Why SIEM Matters for Enterprise Security Buyers
SIEM adoption has shifted from compliance-driven to operations-driven security.
Modern SIEM platforms provide:
- Unified visibility across hybrid environments.
- Real-time threat detection and investigation.
- Faster incident response and remediation.
- Integrated compliance reporting and audit trails.
They effectively consolidate multiple security signals into a single operational layer, enabling proactive threat defense rather than reactive monitoring.
SIEM vs Traditional Security Tooling
SIEM represents a shift from fragmented, tool-specific security monitoring to a unified, intelligence-driven approach. Traditional security tools operate in isolation and rely heavily on signature-based detection, which limits visibility and slows investigation.
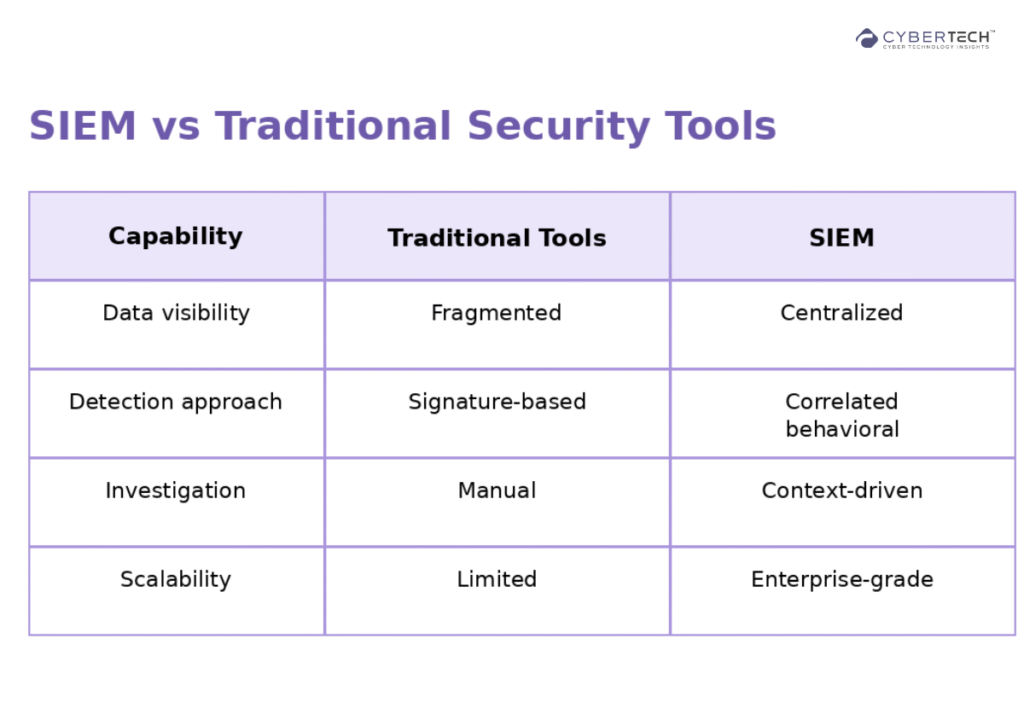
In contrast, SIEM platforms aggregate and correlate data across the environment, enabling context-rich detection, faster response, and scalable security operations aligned with modern enterprise needs.
Leading SIEM Vendors: Enterprise Comparison Snapshot
The SIEM market is dense, but a few platforms consistently show up in enterprise evaluations:
Tier 1 Enterprise Platforms
1. Splunk Enterprise Security
Strong analytics, large-scale data processing and widely adopted.
2. Microsoft Sentinel
Cloud-native, deeply integrated with the Azure ecosystem.
3. Google Security Operations (Chronicle)
High-speed analytics with large-scale data retention.
Cloud-Native and Modern SIEM
4. Sumo Logic
Elastic, cloud-first architecture with real-time analytics.
5. Panther
Detection-as-code approach, developer-friendly workflows.
Mid-Market / Cost-Optimized
6. ManageEngine Log360
Unified SIEM with compliance and threat detection capabilities.
7. Graylog
Open-source roots with flexible deployment models.
There is no “best” SIEM. Selection depends on data scale, team maturity, and cloud strategy.
SIEM Pricing Models: What Enterprises Should Expect
SIEM pricing is one of the biggest friction points in buying decisions.
Common Pricing Models
- Data ingestion-based (per GB/day).
- Events per second (EPS).
- Per user or node licensing.
- Per asset/device (managed SIEM).
Typical Cost Benchmarks
- Managed SIEM can start around $15 per asset per month.
- Entry enterprise tools may start around $1,000+ per month for smaller deployments.
- Large enterprise SIEM deployments often reach hundreds of thousands annually.
Hidden Costs to Watch
- Data storage expansion.
- Advanced analytics add-ons.
- Integration costs.
- SOC staffing and tuning overhead.
Many vendors use complex pricing structures, so the total cost of ownership must be evaluated carefully.
Enterprise SIEM Implementation Guidance
This is where most SIEM projects succeed or fail.
1. Define Use Cases First
Start with:
- Threat detection priorities.
- Compliance requirements.
- SOC workflows.
Avoid deploying SIEM as a “log dumping platform”.
2. Align with SOC Maturity
SIEM effectiveness depends heavily on:
- Skilled analysts.
- Detection engineering.
- Continuous tuning.
Understaffed teams often struggle with alert fatigue and misconfiguration.
3. Plan for Data Strategy
SIEM is fundamentally a data platform:
- Decide what logs to ingest.
- Optimize retention policies.
- Balance cost vs visibility.
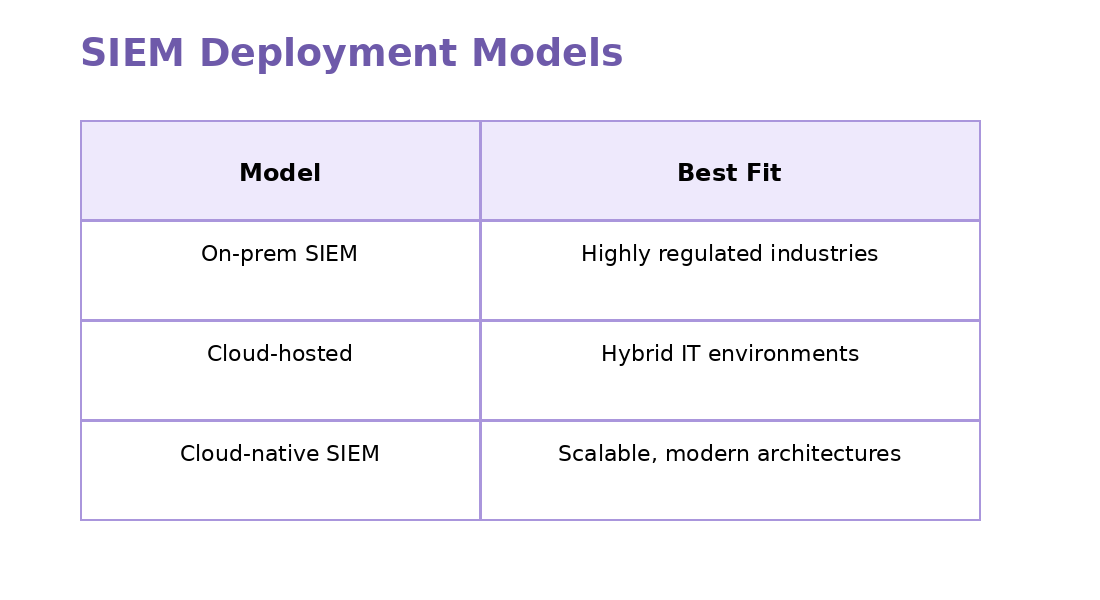
4. Choose Deployment Model Carefully
Cloud-native SIEMs reduce infrastructure overhead and scale automatically with data growth.
5. Prioritize Integration
Your SIEM should integrate with:
- EDR/XDR platforms.
- Identity systems.
- Cloud security tools.
- SOAR for automation.
Without integration, SIEM becomes another silo. Ironically.
Common SIEM Challenges and How to Solve Them
Alert Fatigue
Too many false positives
Solution: Use AI-driven correlation and tuning.
Complexity
High setup and maintenance overhead.
Solution: Consider managed SIEM or cloud-native options.
Cost Explosion
Data ingestion costs scale fast.
Solution: Filter logs and optimize ingestion strategy.
Skill Gap
Requires specialized expertise
Solution: Invest in detection engineering or MSSP support
Where SIEM Fits in the Modern Security Stack
SIEM is no longer standalone. It sits at the center of a broader ecosystem:
- EDR/XDR to Endpoint detection signals.
- SOAR to Automated response.
- Threat intelligence platforms for context enrichment.
- Identity security tools to Access monitoring.
Think of SIEM as the central nervous system of the SOC.
Internal Navigation for Cyber Tech Content Strategy
To align with an enterprise buyer journey, this pillar should connect to:
- SIEM vs XDR: Detection strategy comparison.
- SIEM vs SOAR: Automation vs analytics.
- Cloud SIEM solutions hub.
- Managed SIEM vendor landscape.
- Threat detection and response (TDIR) frameworks.
Final Take
SIEM has evolved beyond log management into a core decisioning layer for modern security operations.
Its real value lies in transforming fragmented security data into a clear, actionable context that enables teams to detect threats earlier, cut through operational noise, and respond with greater speed and precision.
For enterprise buyers, the conversation has moved past adoption. The real challenge is operationalizing SIEM in a way that aligns with SOC maturity, scales with data growth, and delivers measurable security outcomes without adding unnecessary complexity or cost.
When implemented effectively, SIEM becomes less of a tool and more of a strategic foundation for resilient, intelligence-driven security operations.
FAQs
1. What does a SIEM system actually do in an enterprise environment?
A SIEM platform centralizes security data from across systems, correlates events, and identifies threats in real time, enabling security teams to detect, investigate, and respond to incidents more efficiently.
2. How is SIEM different from XDR or EDR?
SIEM aggregates and analyzes data across the entire IT environment, while EDR focuses on endpoint-level threats and XDR extends detection across multiple security layers. SIEM acts as the central analysis and visibility layer.
3. How much does a SIEM solution cost in the U.S. market?
Costs vary based on data volume and deployment model. Entry-level deployments can start around $1,000 per month, while large enterprise implementations often scale to hundreds of thousands annually or more.
4. What are the key challenges of implementing SIEM?
Common challenges include high data ingestion costs, alert fatigue, integration complexity, and the need for skilled analysts to continuously tune detection rules and workflows.
5. When should an organization invest in SIEM?
Organizations should consider SIEM when they need centralized visibility, improved threat detection, compliance reporting, and the ability to scale security operations across hybrid or multi-cloud environments.
To participate in upcoming interviews, please reach out to our CyberTech Media Room at info@intentamplify.com
🔒 Login or Register to continue reading