ZTNA vs VPN. Which is more secure? From an attacker’s perspective, a VPN is often the hardest barrier to cross, and the most valuable foothold once breached.
ZTNA disrupts that advantage. Even with valid credentials, access is constrained, continuously evaluated, and limited to specific resources, making lateral movement significantly harder.
For security leaders, this shifts the focus from preventing entry to controlling impact.
ZTNA vs VPN: Why This Comparison Matters Now
Remote access is no longer a “remote workforce” issue. It is the default access model across cloud, SaaS, third-party ecosystems, and distributed teams.
At the same time, attackers have adapted:
- Credential theft is now the primary entry vector.
- Lateral movement determines breach impact.
- Identity has become the new perimeter.
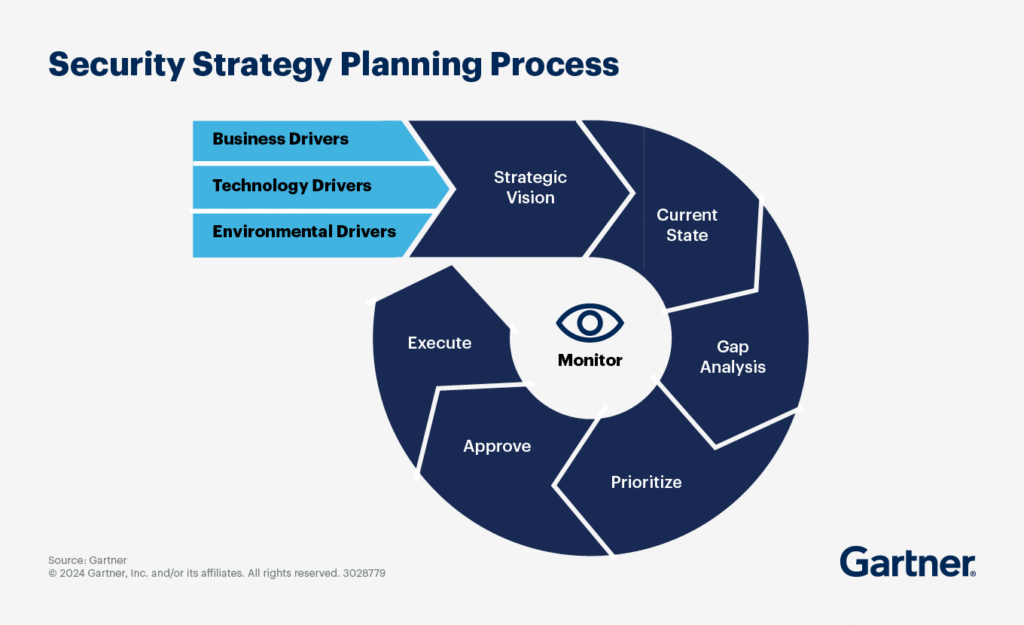
Gartner’s data verifies that security strategies are moving away from implicit trust and toward identity-based, context-aware access controls designed to limit lateral movement and continuously evaluate risk.
Against that backdrop, the traditional VPN model is being stress-tested and, increasingly, outgrown. The immediate priority for security leaders is clear.
Quantify your access risk today.
Identify which users, applications, and entry points expand your attack surface.
VPN Security: Strong Encryption, Weak Assumptions
VPNs still deliver what they were designed for. Secure, encrypted tunnels into corporate networks.
Recent data shows that 56% of organizations experienced cyberattacks exploiting VPN vulnerabilities, while 58% of ransomware incidents originated from compromised perimeter devices such as VPNs.

Source: Zscaler
Once authenticated, users are typically placed inside the network perimeter with broad access. This creates three systemic risks:
1. Overexposed Attack Surface
VPN concentrators remain publicly reachable infrastructure. That alone makes them a high-value target.
2. Lateral Movement by Design
VPNs were built to enable movement across systems. That same capability allows attackers to pivot once inside.
3. Static Trust Model
Authentication is largely point-in-time. Session trust persists even if risk conditions change.
This is why modern attack chains map so cleanly onto VPN environments. Gain access, move laterally, escalate privileges, exfiltrate data.
Audit your VPN exposure.
Map what users can access versus what they actually need.
ZTNA Security: Eliminating the Network as a Trust Boundary
ZTNA takes a fundamentally different approach. It removes the concept of “being on the network” altogether.
Instead, access is:
- Identity-driven.
- Application-specific.
- Continuously validated.
Users do not connect to a network. They connect to a specific resource, under specific conditions, for a specific duration.
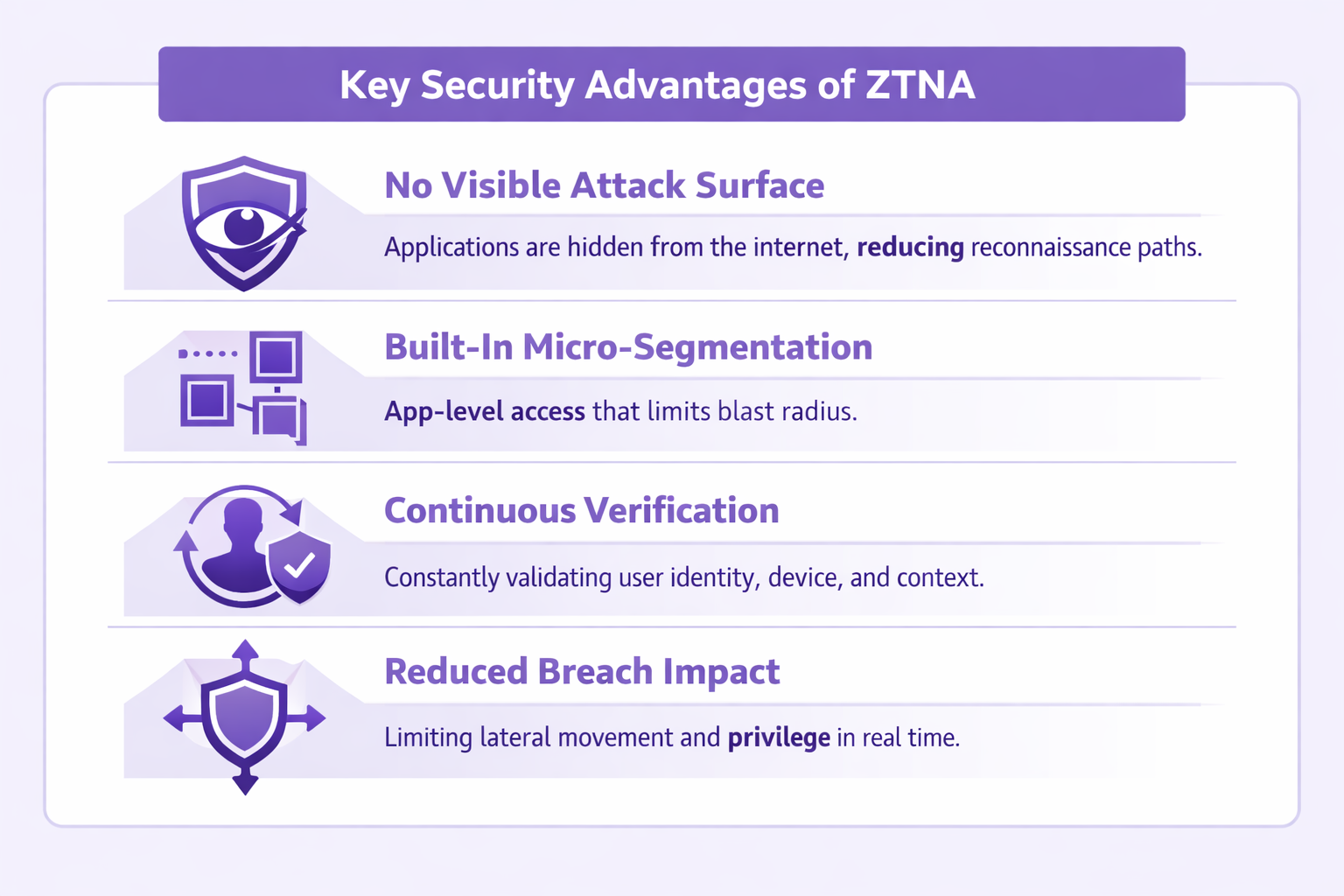
This shift introduces meaningful security advantages:
Start enforcing least-privilege access across critical applications to reduce breach impact immediately.
ZTNA Vendor Comparison: How Leading Platforms Differ
ZTNA adoption is not just an architectural shift. It is a platform decision that directly impacts how access is enforced, monitored, and scaled across the enterprise.
Vendors approach Zero Trust differently. Some lead with identity. Others with network security or data protection. Understanding these differences is critical for long-term success.
Leading ZTNA Vendors at a Glance:
| Vendor | Core Strength | Best Fit Use Case | Key Differentiator | Considerations |
| Zscaler (ZPA) | Cloud-native Zero Trust leader | Large enterprises, cloud-first environments | Fully proxy-based architecture with no inbound connections | Premium pricing, requires architectural alignment |
| Palo Alto Networks (Prisma Access) | Integrated SASE + ZTNA | Enterprises consolidating their security stack | Deep integration with NGFW and threat intelligence (Unit 42) | Can introduce operational complexity |
| Microsoft (Entra Private Access) | Identity-first access control | Microsoft-centric organizations | Native integration with Azure AD, Conditional Access, and endpoint signals | Best value tied to Microsoft ecosystem |
| Cloudflare (Zero Trust) | Performance + simplicity | Distributed teams, mid-to-large enterprises | Global edge network with fast deployment and low latency | Less depth in advanced enterprise policy controls |
| Netskope (ZTNA Next) | Data-centric security | Organizations prioritizing DLP and CASB | Strong integration between access control and data protection | Full value requires broader Netskope adoption |
| Akamai (Enterprise Application Access) | Application-layer security | App-heavy, distributed environments | Strong segmentation at the application layer | Limited visibility beyond application context |
Security Comparison That Actually Matters to CISOs
CISOs need to focus on how each model impacts risk, exposure, and breach containment in real-world environments.
The comparison below cuts through feature-level noise to highlight what actually influences security outcomes at scale.
| Dimension | VPN | ZTNA |
| Trust Model | Implicit after login | Continuous, contextual |
| Access Scope | Network-level | Application-level |
| Attack Surface | Exposed endpoints | Dark, non-routable apps |
| Lateral Movement | High risk | Structurally limited |
| Identity Enforcement | Static | Dynamic, policy-driven |
| Cloud Alignment | Limited | Native fit |
| Breach Containment | Weak | Strong |
From a risk perspective, ZTNA is not an incremental upgrade. It is a different control plane.
Evaluate ZTNA platforms based on how effectively they reduce risk, not just how they enable connectivity.
Why Enterprises Are Moving and Why Some Are Not
Despite the clear advantages, this is not a clean cutover.
Where ZTNA Is Winning
ZTNA is becoming the default for:
- SaaS and cloud application access.
- Third-party and contractor access.
- Hybrid and remote workforce environments.
- Identity-centric security architectures.
In these environments, VPN introduces unnecessary exposure.
Where VPN Still Persists
VPNs remain relevant in:
- Legacy infrastructure requiring network-level access.
- OT and industrial environments.
- Full administrative access scenarios.
- Organizations early in Zero Trust maturity.
In practice, most enterprises are operating a hybrid model, gradually shrinking the VPN footprint.
The Strategic Reality: This Is a Zero Trust Transition
One of the biggest misconceptions in the market is treating ZTNA as a VPN replacement product.
It is not.
ZTNA is an access paradigm shift, aligned with broader Zero Trust Architecture principles:
- Identity becomes the control plane.
- Access becomes granular and contextual.
- Trust becomes continuously evaluated.
This is why adoption is accelerating across both commercial and federal environments, where Zero Trust is increasingly tied to compliance frameworks and executive mandates.
What Decision-Makers Should Prioritize in 2026
For CISOs and security leaders, the conversation should move beyond “ZTNA vs VPN” and toward access architecture strategy:
1. Start With Identity Maturity
ZTNA is only as strong as your identity infrastructure. Weak IAM undermines Zero Trust.
2. Segment High-Risk Access First
Prioritize:
- Privileged users.
- Third-party access.
- Crown-jewel applications.
3. Reduce Network-Level Exposure
Every application moved behind ZTNA reduces the attack surface.
4. Plan for Coexistence
VPN will not disappear overnight. Architect for phased transition, not abrupt replacement.
Conduct a Zero Trust access assessment to identify gaps, reduce lateral movement risk, and build a phased transition roadmap.
Access Is the New Control Plane for Enterprise Security
As enterprises expand across cloud, SaaS, and third-party ecosystems, access has become the new control plane for security. What used to be a network decision is now a risk decision.
VPN still has a role. However, relying on it as the default access layer introduces structural exposure that modern attackers are actively exploiting.
ZTNA offers a different path. One that reduces implicit trust, limits lateral movement, and aligns security with how users, applications, and infrastructure actually operate today.
For security leaders, the next step is not immediate replacement. It is a deliberate transition.
Start by identifying where VPN introduces the most risk. Prioritize high-value applications, third-party access, and privileged users. Build around identity, enforce least privilege, and expand from there.
FAQs
1. What is the difference between ZTNA and VPN in enterprise security?
ZTNA provides application-level, identity-based access with continuous verification, while VPN grants network-level access after a one-time authentication. This makes ZTNA significantly more aligned with least-privilege and Zero Trust principles.
2. Why are organizations moving from VPN to Zero Trust (ZTNA)?
Organizations are shifting because VPNs create broad access and larger attack surfaces, while ZTNA limits exposure by granting access only to specific resources. This reduces risk, especially in cloud and hybrid environments.
3. Is VPN still secure enough for modern enterprise environments?
VPNs remain effective for encrypting traffic, but they are not sufficient on their own. Their reliance on implicit trust and network-level access makes them less effective against modern threats like credential compromise and lateral movement.
4. How does ZTNA reduce the risk of lateral movement compared to VPN?
ZTNA enforces least-privilege access at the application level, preventing users from accessing the broader network. This significantly limits an attacker’s ability to move across systems even if credentials are compromised.
5. Can ZTNA replace VPN completely in large enterprises?
Not entirely. Most enterprises adopt a hybrid approach, using ZTNA for user-to-application access and retaining VPN for legacy systems or full network access scenarios during transition phases.
To share your insights, please write to us at Info@intentamplify.com
🔒 Login or Register to continue reading