Zero Trust has moved beyond a security philosophy. It is now a strategic control model shaping how modern enterprises design, fund, and operationalize cybersecurity.
For security leaders, the conversation is no longer about whether to adopt Zero Trust. It is about how to align vendor capabilities, architecture decisions, and risk priorities into a cohesive operating model.
This shift has created a rapidly expanding vendor ecosystem, often fragmented, frequently overlapping, and increasingly platform-driven.
Market Dynamics: Growth Signals and Strategic Implications
The Zero Trust market reflects both urgency and structural change in enterprise security.
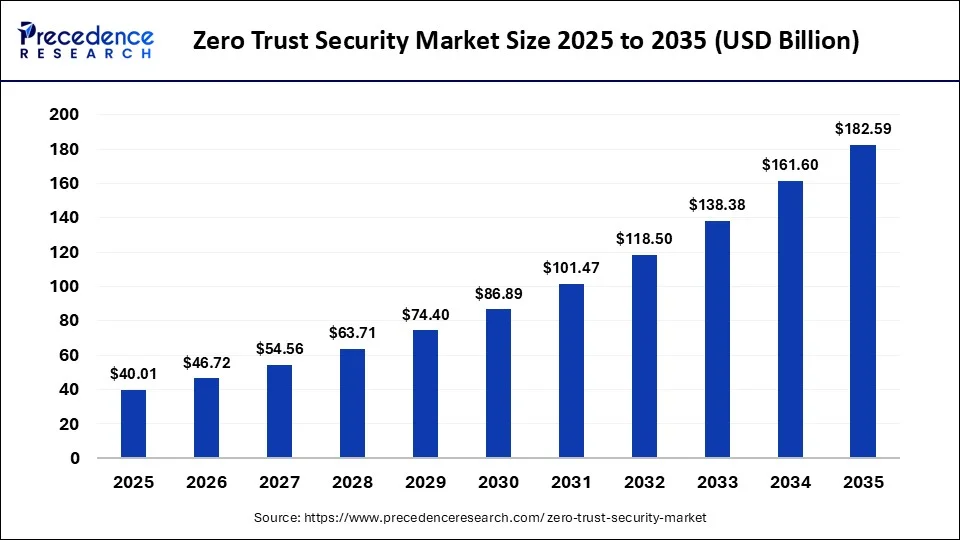
Market Size and Growth Trajectory
- The global Zero Trust market reached approximately $36.9B in 2024 and is projected to exceed $90B by 2030, growing at 16% CAGR.
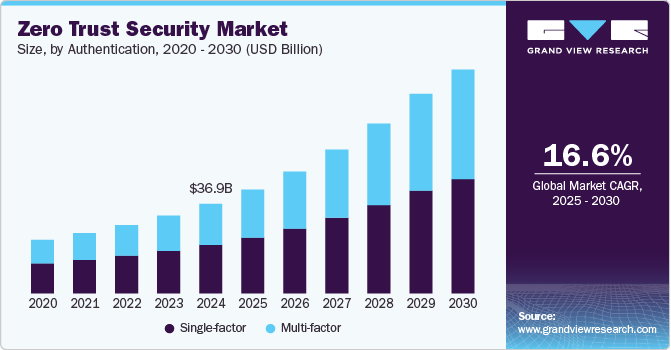
- Mid-term estimates place the market at $48B in 2026, with sustained double-digit expansion.
- Long-range projections suggest potential to cross $150B+ by the early 2030s.
Adoption and Maturity Signals
- 63% of organizations report partial or full Zero Trust implementation. However, most deployments remain narrow in scope, often limited to identity or access layers
- By 2028, Zero Trust principles are expected to extend into data governance, driven by AI-generated data risk.
Strategic Interpretation for Security Leaders
- Zero Trust is evolving from an architecture to an operating model.
- The market is shifting toward platform consolidation, particularly within SSE and SASE frameworks.
- The primary constraint is no longer tooling, but integration, policy alignment, and identity maturity.
Vendor Landscape: Capability Clusters, Not Categories
Zero Trust vendors should not be evaluated as isolated solutions. They represent control points within a distributed trust architecture.
Identity and Access as the Control Plane
- Okta
- Microsoft
- Ping Identity
Identity has become the decision engine for Zero Trust enforcement. All other controls are downstream of identity assurance and policy context.
Secure Access and ZTNA Providers
- Zscaler
- Cloudflare
- Palo Alto Networks
These vendors redefine access by shifting from network-level trust to application-level enforcement. ZTNA is now a primary replacement for legacy VPN architectures.
Endpoint and Device Trust Layer
- CrowdStrike
- SentinelOne
Endpoint telemetry is critical for real-time access decisions. Device posture increasingly influences conditional access policies.
Micro-segmentation and Workload Protection
- Illumio
- Cisco
These vendors address one of the most persistent enterprise risks. Lateral movement within compromised environments.
Data Security and SSE Platforms
- Netskope
- Forcepoint
As data becomes more distributed, these platforms enforce policy at the data interaction layer, not just access.
Vendor Strategy: Platform Consolidation vs Control Depth
A key decision for enterprise buyers is architectural, not vendor-specific.
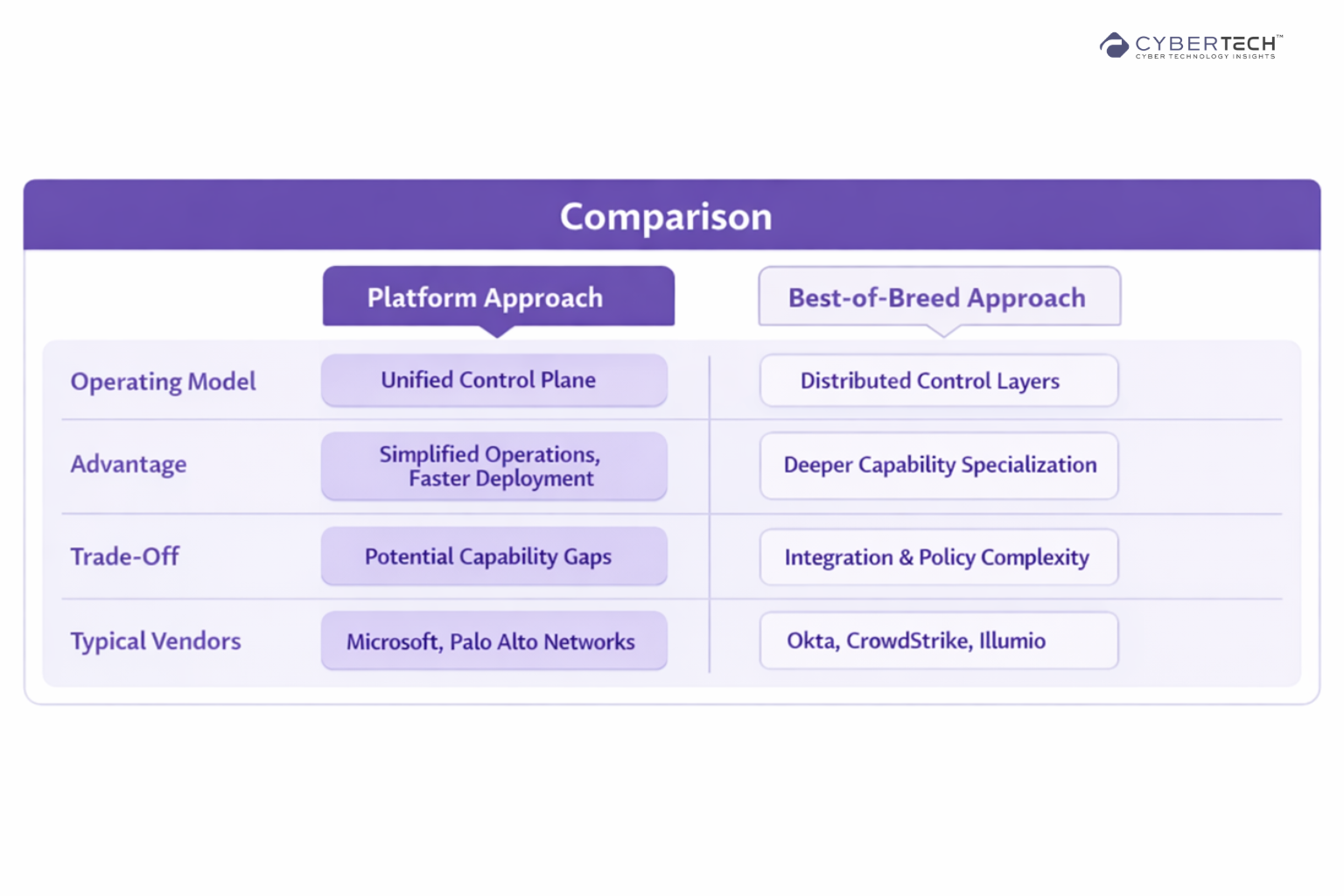
Cyber Tech Insights Analysis
- Platform strategies align with operational efficiency and cost control.
- Best-of-breed strategies align with risk-specific optimization and control depth.
- Most large enterprises operate in a hybrid model, whether intentional or not.
Reference Architecture: From Concept to Control Flow
Effective Zero Trust implementation relies on coordinated control points across the access lifecycle.
The following flow outlines how these controls interact to enforce continuous validation.
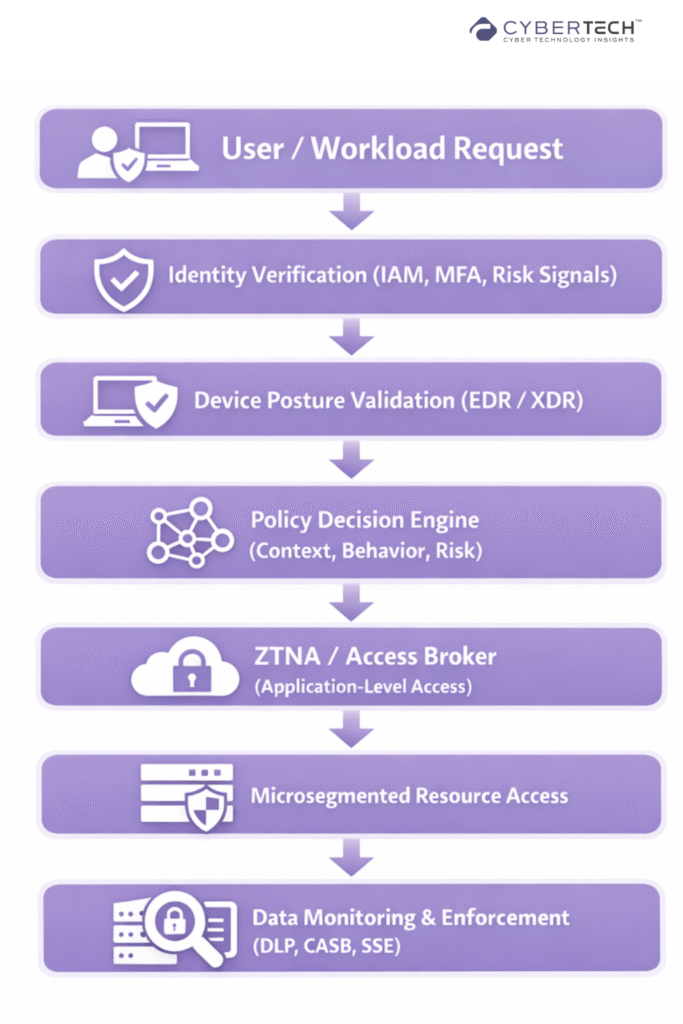
Key Architectural Principle
Trust is not granted. It is continuously evaluated based on:
- Identity assurance.
- Device integrity.
- Behavioral context.
- Data sensitivity.
High-Impact Use Cases for Enterprise Environments
Zero Trust is most effective when applied to high-risk, high-impact environments. The use cases below illustrate where it creates immediate and sustained value.
1. Workforce Transformation Without Expanding Risk
Hybrid work has dissolved traditional perimeters.
Zero Trust enables:
- Context-aware access without VPN dependency.
- Enforcement of device compliance at scale.
- Reduced exposure from unmanaged endpoints.
Outcome: Security posture improves without degrading user experience.
2. Securing Multi-Cloud and SaaS Ecosystems
Enterprises now operate across fragmented environments.
Zero Trust enables:
- Consistent access policies across cloud providers.
- Visibility into user behavior across SaaS platforms.
- Data-aware enforcement independent of location.
Outcome: Control consistency across the distributed infrastructure.
3. Ransomware Containment and Breach Limitation
Perimeter defenses fail. Containment becomes critical.
Zero Trust enables:
- Micro-segmentation to isolate workloads.
- Prevention of east-west movement post-compromise.
Outcome: Reduced blast radius and faster incident containment.
4. Third-Party and Supply Chain Access Control
Vendor access remains a major attack vector.
Zero Trust enables:
- Granular, application-specific access.
- Session-level monitoring and revocation.
Outcome: Reduced third-party risk without blocking business operations.
Enterprise Implementation: What Actually Works
Zero Trust initiatives often stall due to misalignment between architecture and execution.
Recommended Phased Approach
Phase 1. Establish Identity Authority
- Centralize identity providers.
- Enforce MFA and conditional access.
- Clean identity data and entitlements.
Phase 2. Redefine Access
- Deploy ZTNA for critical applications.
- Reduce reliance on network-based trust.
Phase 3. Integrate Device Intelligence
- Align endpoint telemetry with access decisions.
- Enforce posture-based policies.
Phase 4. Segment Critical Assets
- Apply micro-segmentation to high-value workloads.
- Prioritize based on risk exposure.
Phase 5. Operationalize Continuous Trust
- Implement behavioral analytics.
- Shift toward adaptive, risk-based access models.
Common Failure Points
- Treating Zero Trust as a product deployment instead of a transformation program.
- Underestimating the importance of identity governance and data quality.
- Fragmented policy enforcement across tools.
Pricing Considerations: Beyond Licensing
Zero Trust investments are often misunderstood as tooling costs. In reality, the primary cost driver is architectural complexity.
Pricing Models Across Vendors
- Per-user pricing (IAM, ZTNA)
- Per-endpoint pricing (EDR/XDR)
- Consumption-based pricing (SSE, traffic inspection)
- Workload-based pricing (micro-segmentation)
Cyber Tech Insights Analysis
- Platform consolidation reduces operational overhead, not necessarily licensing cost.
- Best-of-breed environments increase integration and management burden.
- ROI is driven by risk reduction and operational efficiency, not tool count reduction.
Where the Market Is Heading
Market momentum is being driven by convergence, identity centralization, and adaptive security models.
The following trends highlight the structural shifts influencing future adoption.
1. Convergence into SSE and SASE Platforms
Vendors are collapsing capabilities into unified delivery models.
2. Identity as the Core Security Layer
Identity is becoming the primary enforcement point, not the network.
3. AI-Driven Adaptive Access
Access decisions are increasingly behavioral and dynamic, not static.
4. Expansion into Data-Centric Zero Trust
Security is shifting from access control to data interaction control, particularly in AI-driven environments.
The New Standard for Enterprise Security
Zero Trust is a fundamental shift in how security is designed, governed, and operationalized across the enterprise.
Organizations that deliver measurable outcomes are not those that accumulate tools, but those that establish cohesion across identity, access, and data controls, embed telemetry into real-time decisioning, and engineer for continuous verification rather than periodic assurance.
FAQs
1. What is Zero Trust security, and why are enterprises adopting it?
Zero Trust is a security model that requires continuous verification of every user, device, and access request.
2. How do I choose the right Zero Trust security vendor?
The right vendor depends on your architecture priorities, not feature lists. Leaders evaluate vendors based on identity integration, policy enforcement capability, scalability, and alignment with the existing security stack.
3. What are the core components of a Zero Trust architecture?
A complete Zero Trust model includes identity and access management, device posture validation, ZTNA, micro-segmentation, and data security controls.
4. What is the difference between ZTNA and VPN?
ZTNA provides application-level access based on identity and context, while VPNs grant broad network access once authenticated.
5. What are the biggest challenges in implementing Zero Trust?
The primary challenges include fragmented identity systems, policy inconsistency, and integration complexity across tools.
To share your insights, please write to us at info@intentamplify.com