Oracle’s emergency patch for a critical Identity Manager vulnerability is a signal of a deeper shift in enterprise risk. The flaw enables unauthenticated remote code execution.
That means attackers can bypass traditional defenses entirely and operate inside the environment without needing valid credentials.
This reinforces a growing reality. Attackers are no longer breaking in. They are logging in or bypassing identity systems altogether.
Identity Is Now the Primary Entry Point
The Oracle incident aligns with a broader industry trend where identity systems are increasingly targeted as the fastest path to compromise.
According to Palo Alto Networks Unit 42:
- 90% of breaches involve identity-related weaknesses.
- 65% of attacks leverage identity for initial access.
- 99% of cloud identities are over-privileged.
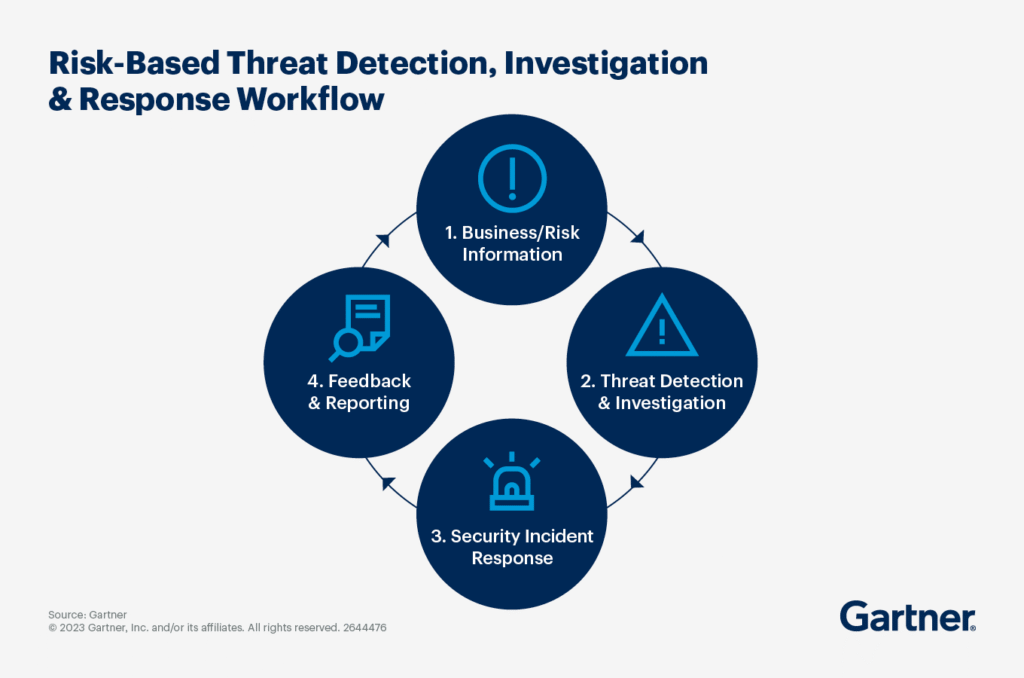
At the same time, Gartner highlights that modern cybersecurity challenges are being driven by expanding digital ecosystems and increasing complexity.
This combination is critical. More access points. Less visibility. Greater identity exposure.
Assess your current identity risk posture across cloud, SaaS, and hybrid environments.
Where Zero Trust Breaks Down
Zero Trust is built on a clear principle. Never trust, always verify.
However, that principle fails if the identity layer itself is compromised.
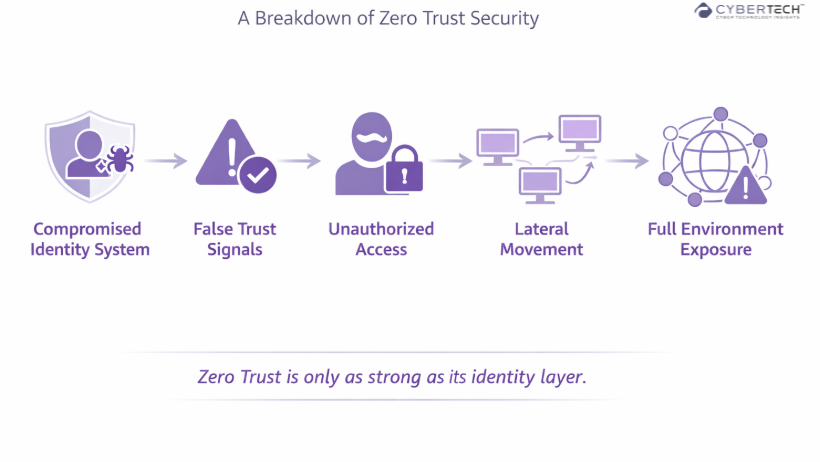
The Oracle vulnerability exposes a fundamental gap in many enterprise Zero Trust strategies:
- Identity systems are still implicitly trusted.
- Verification depends on systems that can be bypassed.
- Access controls become ineffective once identity is compromised.
This leads to a hard truth. Zero Trust does not fail at the policy layer. It fails at the identity layer.
Why This Changes the Security Conversation
Traditionally, security strategies focused on:
- Network perimeters
- Endpoint protection
- Detection and response
Today, the control plane has shifted.
Identity now sits at the center of every access decision across cloud, SaaS, and hybrid environments.
According to CrowdStrike’s 2026 Global Threat Report, attackers increasingly exploit gaps between identity, endpoint, and cloud systems rather than targeting a single control point.
This is why point solutions are no longer sufficient.
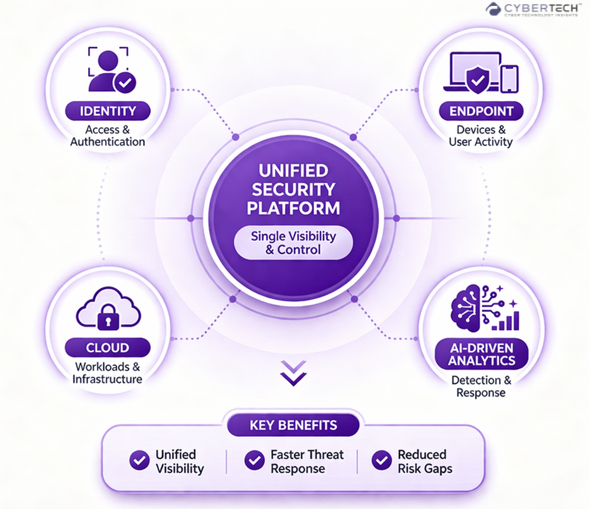
From Fragmented Security to Identity-First Architecture
The industry is moving toward unified platforms that integrate:
- Identity
- Endpoint
- Cloud
- AI-driven analytics
This shift is not about tool consolidation. It is about context correlation.
Security teams need to understand:
- Who is accessing it.
- What they are accessing.
- Whether that behavior is normal.
- And how quickly it deviates into risk.
Without this, even patched systems remain exposed.
Vendor Landscape. Identity-First Security Platforms
| Vendor | Core Strength | Identity Capabilities | Zero Trust Alignment | Best Fit For |
| Palo Alto Networks | Platformization across network, cloud, and SOC | Identity as a signal across Prisma + Cortex | Strong. Identity integrated into broader security fabric | Large enterprises seeking unified security |
| CrowdStrike | Endpoint + identity + threat intelligence | Identity threat detection (ITDR) integrated with EDR | Strong. Focus on identity-driven threat detection | Organizations prioritizing detection and response |
| Microsoft | Deep ecosystem integration | Azure AD (Entra), conditional access, identity governance | Very strong. Native Zero Trust architecture | Enterprises invested in Microsoft ecosystem |
| Okta | Identity-first architecture | IAM, SSO, adaptive MFA, lifecycle management | Strong. Identity at the center of Zero Trust | Identity-centric and SaaS-heavy environments |
| Zscaler | Secure access and ZTNA leadership | Identity-based access policies | Very strong. Zero Trust network access pioneer | Distributed workforce and cloud-first orgs |
| Ping Identity | Enterprise IAM and federation | Identity orchestration and decentralized identity | Strong. Flexible identity control layer | Complex enterprise identity environments |
Compare identity-first security platforms based on your architecture and risk profile.
What This Incident Exposes About Enterprise Risk
Beyond the immediate vulnerability, this incident exposes deeper patterns in enterprise security. These patterns are not isolated. They reflect how risk is evolving across identity, visibility, and response.
This event highlights three structural realities:

What True Zero Trust Requires Now
To close these gaps, organizations must evolve their approach:
Continuous Identity Verification
Authentication must be dynamic, not a one-time checkpoint.
Least Privilege at Scale
Over-permissioned identities remain one of the biggest risk multipliers.
Unified Security Telemetry
Identity, endpoint, and cloud signals must be correlated in real time.
Assume Identity Compromise
Security models must operate under the assumption that identity systems can fail.
Discover the gaps in your current Zero Trust architecture before they are exploited.
Identity Is the New Control Plane
The Oracle vulnerability is not just another patch cycle event. It is a clear signal that the foundations of enterprise security are being tested in real time.
What failed here was not just a system. It was an assumption. The assumption that identity infrastructure can be trusted by default.
In modern environments, identity is no longer a gateway to access. It is the control plane that governs every interaction across cloud, applications, and distributed systems. When that layer is compromised, every downstream control becomes irrelevant.
This is where most Zero Trust strategies are still incomplete. They enforce verification at the edge, but fail to continuously validate the integrity of the identity layer itself.
Organizations that continue to treat identity as static infrastructure will remain exposed.
Those who treat identity as a dynamic, continuously evaluated risk signal will not just reduce exposure. They will define the next standard for cyber resilience.
FAQs
1. Why are identity systems becoming the primary attack vector?
Identity systems now sit at the center of access across cloud, SaaS, and enterprise environments. Attackers target them because compromising identity allows direct, often undetected access without needing to breach traditional network defenses.
2. How does this Oracle vulnerability impact enterprise security strategy?
It highlights that identity infrastructure can no longer be implicitly trusted. Organizations must shift toward continuous verification and assume identity compromise as part of their threat model.
3. What does this incident reveal about Zero Trust adoption?
It shows that many Zero Trust implementations are incomplete. While access policies may be enforced, the underlying identity systems are still treated as trusted, creating a critical gap.
4. Why is reactive security no longer sufficient for modern threats?
Attackers operate faster than traditional detection and patching cycles. By the time a vulnerability is fixed, exploitation may already have occurred, making real-time detection and automated response essential.
5. What should enterprises prioritize to reduce identity-related risk?
Organizations should focus on continuous identity verification, least-privilege access, unified visibility across identity and endpoints, and AI-driven threat detection to respond in real time.
To share your insights, please write to us at Info@intentamplify.com
🔒 Login or Register to continue reading








