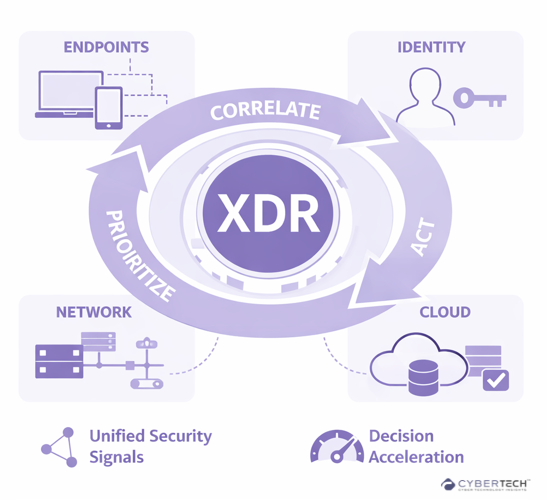
Extended Detection and Response (XDR) is redefining how security operations handle detection, investigation, and response across increasingly complex environments.
As signals expand across endpoints, identities, networks, and cloud workloads, XDR provides a unified approach to connecting and prioritizing what matters.
Its value lies not just in visibility, but in how effectively it transforms dispersed signals into actionable context. This allows security teams to reduce investigative friction, streamline workflows, and improve response precision.
This article explores how XDR functions within modern security operations, where it delivers measurable impact, how it compares with SIEM and EDR, and the factors shaping its adoption.
XDR Beyond the Vendor Definition
XDR is a detection and response control plane that sits across endpoint, identity, network, and cloud signals. It correlates them, prioritizes them, and increasingly, acts on them.
The real value of XDR is not visibility. It is context compression.
Speaking at the Gartner Security & Risk Management Summit, Alex Michaels, Senior Principal Analyst at Gartner, said, “Security and risk management (SRM) leaders face a mix of challenges and opportunities this year, with a goal to enable transformation and embed resilience.
Gartner positions XDR primarily around integration and cross-domain correlation, highlighting its role in unifying disparate security signals. That framing is directionally accurate, but incomplete.
The more significant shift is operational. XDR changes how decisions are made inside the SOC by compressing context and reducing investigative friction.
Explore how leading enterprises are redefining detection and response strategies beyond tool-centric approaches.
How XDR Works
Most explanations break XDR into neat stages. In reality, it behaves more like a loop that tightens over time.
Signal Ingestion: Where Most Platforms Already Look Similar
Telemetry comes from everywhere:
- Endpoint processes and behaviors.
- Identity systems and access anomalies.
- Network flows and lateral movement.
- Cloud workloads and API activity.
Correlation: Where XDR Either Delivers or Fails
This is the make-or-break layer.
Correlation isn’t just linking alerts. It’s deciding what matters. That requires:
- Entity mapping. Users, devices, sessions.
- Temporal alignment. What happened first, what followed.
- Behavioral baselining. What is normal for this environment.
Weak correlation turns XDR into noisy aggregation. Strong correlation turns it into decision support.
Most platforms claim the latter. Few consistently deliver it across hybrid environments.
Understand what separates effective correlation engines from surface-level aggregation in modern XDR platforms.
Detection: Less About AI, More About Signal Discipline
There’s a lot of talk about machine learning here. Some of it is justified. Most of it is overstated.
The real gain comes from combining weak signals across domains:
- A login anomaly on its own. Maybe nothing.
- A suspicious process on a device. Still unclear.
- Add lateral movement and data access. Now it’s a pattern.
XDR doesn’t magically detect unknown threats. It connects small anomalies into something actionable.
Break down how real-world detection strategies move beyond AI narratives toward signal quality and context.
Investigation: Where Time Actually Gets Saved
This is where analysts feel the difference.
Instead of pivoting across five tools, they get:
- A pre-built attack timeline.
- Linked entities and affected assets.
- Suggested root cause paths.
Context can still be incomplete. But it reduces the cognitive load.
Response: The Most Overpromised Capability
Yes, XDR can isolate endpoints. Disable accounts. Block indicators.
However, full automation is still uneven.
- Over-automation risks business disruption.
- Under-automation keeps the response slow.
- Playbooks need constant tuning.
The idea of “autonomous SOC” is still aspirational. What XDR actually delivers today is guided response with selective automation.
That’s a more realistic expectation.
Capability Mapping: Where XDR Collapses the Stack
| Layer | What Existed Before | What XDR Changes |
| Endpoint | EDR | Adds cross-domain context |
| Identity | IAM / ITDR | Links identity to behavior |
| Network | NDR | Connects traffic to user and device |
| Cloud | CSPM / CWPP | Brings workload signals into detection |
| SIEM | Log aggregation | Reduces dependency on manual correlation |
| SOAR | Workflow automation | Embeds response into detection layer |
This isn’t full consolidation. That narrative is misleading.
It’s operational convergence, not tool elimination.
Vendor Landscape: Where Strategy Matters More Than Features
| Vendor | Approach | Where It Works | Where It Struggles |
| Microsoft Defender XDR | Deep native integration | Microsoft-centric environments | Multi-vendor ecosystems |
| CrowdStrike Falcon XDR | Endpoint-first expansion | Threat hunting, endpoint visibility | Network depth |
| Palo Alto Cortex XDR | Network + endpoint fusion | Hybrid environments | Complexity of deployment |
| SentinelOne Singularity | Autonomous detection focus | Lean teams, automation-first SOCs | Maturity of integrations |
| Cisco XDR | Integration-heavy model | Network-led enterprises | Consistency across tools |
| Trend Micro Vision One | Cloud and email strength | Cloud-first orgs | Endpoint parity vs leaders |
A pattern shows up quickly.
No vendor is equally strong across all domains. Every XDR platform carries its origin bias.
Endpoint-native vendors expand outward. Network vendors build inward. Cloud vendors prioritize workloads. This shapes outcomes more than feature lists.
Native vs Open XDR: A Trade-Off That Doesn’t Get Resolved
| Model | Strength | Limitation |
| Native XDR | Tight integration, faster deployment | Vendor lock-in |
| Open XDR | Flexibility, broader coverage | Integration overhead |
Large enterprises lean toward open models because their environments are already fragmented. Mid-sized organizations often prefer native XDR because it works out of the box.
XDR vs SIEM vs EDR: The Positioning Is Still Evolving
| Capability | SIEM | EDR | XDR |
| Core Role | Data repository | Endpoint defense | Detection and response layer |
| Strength | Historical analysis | Deep endpoint telemetry | Cross-domain correlation |
| Weakness | Manual investigation | Limited scope | Still maturing in standardization |
XDR doesn’t replace SIEM. Not yet.
SIEM still owns compliance, long-term retention, and forensic depth. XDR owns real-time operational decisions.
Market Direction: What the Data Actually Suggests
Gartner positions XDR as a high-benefit investment for improving SOC productivity. That aligns with what teams are experiencing on the ground.
XDR adoption isn’t driven by feature appeal. It’s driven by operational necessity.
Another data point worth noting. Most enterprises still operate with fragmented tooling despite consolidation efforts. That suggests XDR is not eliminating complexity. It’s absorbing it into a different layer.
Where XDR Falls Short and Why That Matters
This is where most vendor narratives go quiet.
- Correlation quality varies significantly across environments.
- Integration claims often break under real-world heterogeneity.
- Automation requires continuous tuning, not “set and forget”.
- Skilled analysts are still essential. XDR doesn’t replace expertise.
Perhaps the biggest limitation. XDR is only as good as the data it sees.
Blind spots still exist. Especially in unmanaged assets, shadow AI, and third-party integrations.
Identify the operational gaps that XDR alone cannot address and how leading teams are compensating for them.
XDR as an Operational Shift, Not a Product Category
XDR is a recalibration of how security operations function day to day.
Its impact shows up in execution. How alerts are prioritized, how incidents are investigated, and how response decisions are made under pressure.
These are not incremental improvements. They reshape how the SOC operates at a practical level.
It does not simplify security in the way vendor narratives often suggest. The underlying complexity remains. What XDR does is reorganize that complexity into something more structured and navigable.
That distinction is critical.
Adopting XDR without rethinking workflows, escalation paths, and analyst responsibilities tends to produce familiar outcomes. The same inefficiencies surfaced through a more unified interface.
When implemented with operational alignment, however, the shift becomes visible.
Fewer fragmented alerts. Faster, more confident decisions. Clearer understanding of attack progression.
Not flawless. But materially more effective than the fragmented models it replaces.
FAQs
1. What problem does XDR actually solve in enterprise security operations?
XDR addresses fragmentation across security tools by connecting signals from endpoints, identities, networks, and cloud environments into a unified detection and response layer.
2. How is XDR different from SIEM and EDR in practical terms?
EDR focuses on endpoint-level detection. SIEM aggregates and stores logs for analysis and compliance. XDR sits between them as an operational layer, correlating cross-domain signals in real time to support faster detection and response without heavy manual investigation.
3. Is XDR a replacement for SIEM in modern security architectures?
XDR is not a full replacement for SIEM. SIEM remains essential for compliance, long-term data retention, and forensic analysis. XDR complements SIEM by improving real-time detection, investigation, and response efficiency within the SOC.
4. What should enterprises evaluate before adopting an XDR platform?
Key considerations include integration depth across existing tools, correlation quality, automation control, and alignment with current SOC workflows. Organizations should also assess whether a native or open XDR model better fits their operational complexity and vendor ecosystem.
5. What are the biggest limitations of XDR in real-world deployments?
XDR effectiveness depends on data quality and integration coverage. Gaps in visibility, inconsistent correlation, and the need for ongoing tuning can limit outcomes. It also does not eliminate the need for skilled analysts or fully automate security operations.
To participate in upcoming interviews, please reach out to our CyberTech Media Room at info@intentamplify.com
🔒 Login or Register to continue reading