In a city shaped by SXSW, new technology has always meant more connectivity, more integration, and more scale.
However, enterprise leaders are starting to question whether constant connectivity is still an advantage or whether it has quietly become the biggest source of risk.
So, where does this shift from constant connectivity to controlled isolation actually create impact?
Let’s explore the top five reasons why air-gapped networks matter in cybersecurity.
When Should You Consider Air-Gapping
In most enterprise environments, security architecture is optimized for visibility. Controls are designed to identify indicators of compromise, correlate signals, and trigger incident response workflows.
However, as attack velocity increases and dwell times shrink, this model becomes increasingly dependent on precision under pressure.
Air-gapping introduces a different evaluation lens. It forces a shift from monitoring threats within an exposed environment to eliminating exposure for systems where risk tolerance is minimal.
For CIOs and security leaders, this becomes a benchmarking exercise across critical assets, data flows, and trust boundaries.
The goal is to identify where traditional controls such as network segmentation, endpoint detection, and zero trust enforcement are still reliant on reachable infrastructure, and where that reachability itself becomes the primary risk.
Once reachability becomes the primary risk, the next step is clear. Identify where eliminating that reachability delivers the highest value.
The Five Reasons That Matter
Air-gapped networks are an architectural control that eliminates entire attack vectors by removing external reachability.
The following reasons highlight where isolation delivers measurable security advantage over traditional, always-connected models.
1. Attack Surface Reduction Through Non-Reachability
Air-gapped networks eliminate externally routable paths to critical systems, effectively removing them from the exploitable attack surface.
Unlike traditional controls that monitor exposed assets, isolation ensures there are no open ports, APIs, or endpoints available for reconnaissance or exploitation.
This directly reduces the risk of initial access, particularly in environments where automated scanning and exploit chaining are prevalent.

2. Deterministic Containment and Reduced Lateral Movement
Modern adversaries prioritize lateral movement post-compromise to escalate privileges and access high-value assets.
Data from McKinsey & Company confirms that organizations still take an average of 73 days to contain a cyber incident, highlighting the ongoing difficulty of limiting breach impact once attackers establish a foothold.
Air-gapped architectures enforce hard boundaries that prevent east-west traffic from propagating beyond the isolated environment.
This creates deterministic containment, where the blast radius is constrained by design rather than dependent on real-time detection and response.
3. Protection of Crown-Jewel Assets and Critical Infrastructure
Certain systems carry disproportionate business risk, including financial platforms, intellectual property repositories, and operational technology environments.
According to the World Economic Forum, around 60% of CISOs report discussing cybersecurity posture with the board three to four times per year, reflecting increasing board-level involvement.
Air-gapping provides a control layer that goes beyond segmentation and access management by ensuring these assets are not directly accessible from untrusted networks.
This is particularly relevant for sectors with strict regulatory requirements and low tolerance for compromise.
4. Resilience Against AI-Driven and Automated Threat Campaigns
AI-driven attacks are accelerating reconnaissance, vulnerability discovery, and exploitation at machine speed. Connected systems are continuously scanned and targeted, often within hours of exposure.
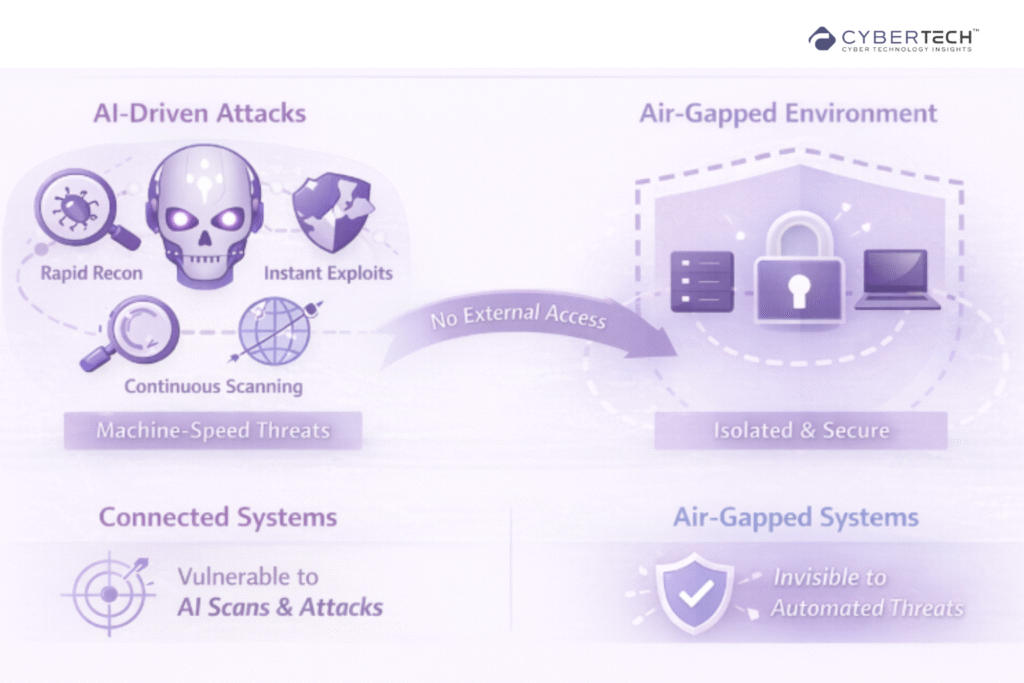
Air-gapped environments mitigate this risk by removing the ability for automated tools to identify and interact with isolated systems, effectively bypassing entire classes of AI-enabled attack vectors.
5. Reduced Dependency on Detection Fidelity and Human Response
Most modern security architectures rely heavily on detection accuracy, alert prioritization, and rapid incident response. This introduces operational risk, especially in high-volume environments with alert fatigue and limited resources.
Air-gapped networks reduce this dependency by minimizing exposure, allowing security teams to focus on controlled access, integrity assurance, and internal threat monitoring rather than constant external threat detection.
Strategic Analysis: Isolation as a Control for Attack Path Elimination
Air-gapped networks are a targeted response to a core limitation in modern security architecture.
Most enterprise defenses are built around visibility and detection, but they still operate on reachable systems. That reachability defines the attack surface.
In a landscape driven by automated reconnaissance and AI-led exploitation, exposed systems are continuously scanned and targeted.
Even mature controls like zero trust and EDR assume eventual access. Air-gapped architectures challenge that assumption by enforcing non-routable isolation, removing the pathways required for initial compromise.
This shifts the model from managing detection risk to reducing exploitability. Instead of containing threats after entry, air-gapping disrupts the attack path before it begins.
It also introduces deterministic containment, where boundaries are enforced by design rather than dependent on response speed.
This approach is the most effective when the business impact of compromise is high, and exposure cannot be justified.
In these environments, air-gapping functions as an architectural control that eliminates entire classes of external attack vectors.
Closing Perspective
Cybersecurity is moving beyond detection-led models. While visibility and response capabilities have improved, they have not reduced the fundamental issue of exposure.
Attackers continue to operate at increasing speed and scale, exploiting systems that remain accessible by design. Air-gapped networks represent a shift toward exposure-centric security, where the focus is on limiting adversary access rather than reacting to it.
They force a more deliberate approach to architecture, where critical systems are evaluated based on reachability, not just protection layers.
For CIOs, this is a strategic inflection point. Security maturity is no longer defined by how well threats are detected, but by how effectively exposure is reduced.

FAQs
1. When should an enterprise consider implementing air-gapped networks?
Enterprises should consider air-gapping when systems handle high-value assets, have a low tolerance for compromise, or where exposure cannot be mitigated through segmentation and detection alone.
2. How do air-gapped networks reduce cyber risk compared to zero trust architectures?
Zero trust limits access within connected environments, while air-gapped networks eliminate external reachability altogether, removing entire classes of remote attack vectors.
3. Are air-gapped networks practical for modern cloud and hybrid infrastructures?
They are not applied universally but are highly effective for isolating critical workloads, backup environments, and operational systems within broader hybrid architectures.
4. What risks do air-gapped networks not eliminate?
Air-gapped systems remain susceptible to insider threats, supply chain compromises, and risks introduced through controlled data transfer mechanisms.
5. How do air-gapped networks improve incident containment and resilience?
By enforcing physical and logical isolation, they prevent lateral movement and limit blast radius, enabling deterministic containment without relying on real-time detection.
To participate in upcoming interviews, please reach out to our CyberTech Media Room at info@intentamplify.com.
🔒 Login or Register to continue reading







