Texas consistently ranks among the top U.S. states for cybercrime impact, with thousands of breach incidents and extortion cases reported annually.
At the same time, statewide cybersecurity operations are blocking over a trillion malicious attempts each year, reflecting a threat environment operating at machine scale.
As a hub for AI, SaaS, and cloud-native companies. and home to leaders like CrowdStrike. The city represents both a cybersecurity innovation engine and a concentrated attack surface.
“CrowdStrike’s global workforce includes some of the best and brightest minds in security, all laser focused on breaking new ground to fulfill our mission of stopping breaches,” said J.C. Herrera, chief human resource officer at CrowdStrike.
The attack patterns reinforce that over 90% of malware is delivered via phishing, and according to Verizon, 68% of breaches involve human interaction.
At the same time, detection timelines still lag, while attackers move in minutes to hours.
This creates a structural imbalance.
Machine-speed attacks. Human-speed defense.
Economics of Delay: Why Response Time Defines Risk
According to IBM, the average cost of a data breach exceeds $4.4 million, with significantly higher impact in AI-driven environments.
Meanwhile,
- Attackers can establish footholds in under an hour.
- Lateral movement happens in minutes.
- Business impact begins before alerts are fully investigated.
Every minute of delay increases financial exposure, operational disruption, and regulatory risk. Yet most SOCs are still operating on manual triage, fragmented visibility, and analyst-dependent decisions.
Smart Threat Intelligence
Designed for How Attacks Actually Work
Modern threat campaigns are orchestrated across identity systems, cloud workloads, endpoints, and APIs, moving laterally through misconfigurations, credential abuse, and trust relationships.
Attack chains are multi-stage, often combining initial access vectors like phishing with privilege escalation, persistence mechanisms, and data exfiltration.
In this environment, visibility alone is insufficient. Security operations must evolve from monitoring discrete events to correlating behavioral signals, threat intelligence feeds, and telemetry across the entire attack surface in real time.
Smart threat intelligence integrates cross-domain telemetry, maps activity to frameworks like MITRE ATT&CK, applies contextual risk scoring, and enables automated response orchestration.
The objective is decisioning at machine speed, ensuring that threats are identified, prioritized, and contained before they translate into business impact.
$4.45 Million Average Breach Cost
Data from IBM’s Cost of a Data Breach Report reveals a structural failure in how most organizations approach cyber defense.
The average breach now costs $4.45 million, with nearly 277 days required to detect and contain an incident. During that time, attackers are not idle. They are moving laterally, escalating privileges, and extracting value from compromised environments.
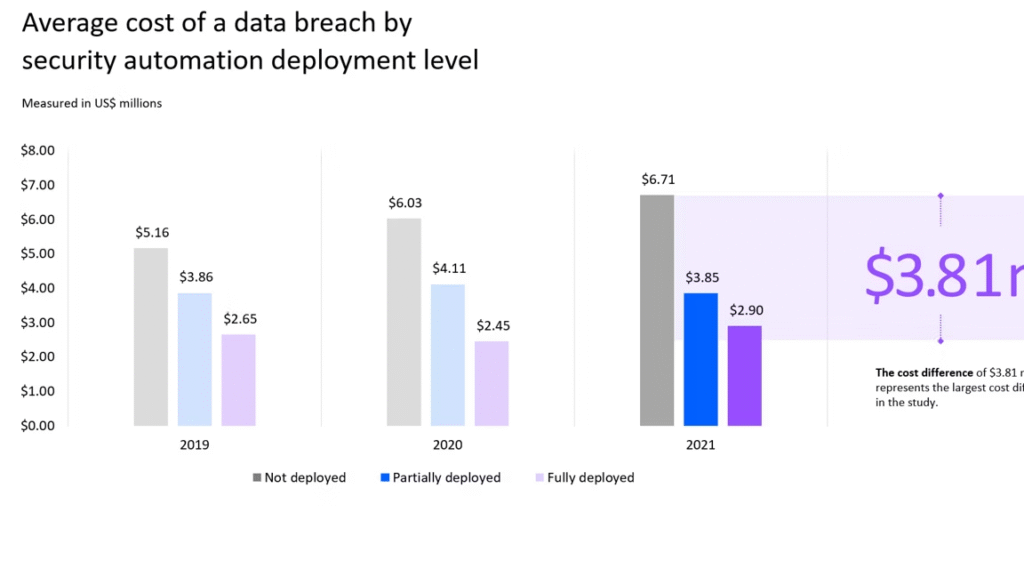
Source: IBM
At the same time, organizations that implemented security AI and automation reduced breach costs by $1.76 million on average. This is a direct reflection of faster detection, faster decision-making, and faster response.
The data also shows that 74% of breaches still involve human factors, reinforcing a critical limitation. Security operations that depend on manual analysis cannot scale against automated, AI-driven attacks.
The Shift Toward Externalized AI Security
What the Data Signals
Insights from McKinsey & Company indicate that more than 90% of AI capabilities in cybersecurity are expected to be delivered by third-party providers. This reflects a structural shift in how modern security is being built and scaled.
At a surface level, this suggests faster adoption of advanced capabilities such as threat detection, behavioral analytics, and automated response. However, the deeper implication is more significant.
Organizations are no longer competing on who can build security capabilities internally. They are competing on how effectively they can integrate, operationalize, and act on intelligence delivered through external platforms.
Automate Your Cyber Defense
From Capability to Control
Automation is the operational backbone required to defend modern environments. In high-velocity ecosystems where infrastructure scales across cloud, APIs, and AI-driven applications, the volume and speed of threats have already exceeded what human-led workflows can manage.
Security teams are not failing due to a lack of tools. They are constrained by decision latency. This is where automation becomes non-negotiable.
Not as rule-based scripting, but as intelligence-driven execution embedded into security operations.
What “Automation” Actually Means in Practice
Effective cyber defense automation is not about replacing analysts. It is about removing friction from critical decision paths.
This includes:
- Real-time correlation of telemetry across identity, endpoint, cloud, and network layers.
- Context-aware prioritization using asset criticality and threat intelligence.
- Automated response orchestration through predefined playbooks.
- Continuous adaptation based on evolving attacker behavior.
The result is a system that does not just detect threats. It acts on them immediately.
The Strategic Advantage: Speed, Consistency, and Scale
Organizations that operationalize intelligence-driven automation are not just improving efficiency. They are closing measurable gaps exposed by real-world breach data.
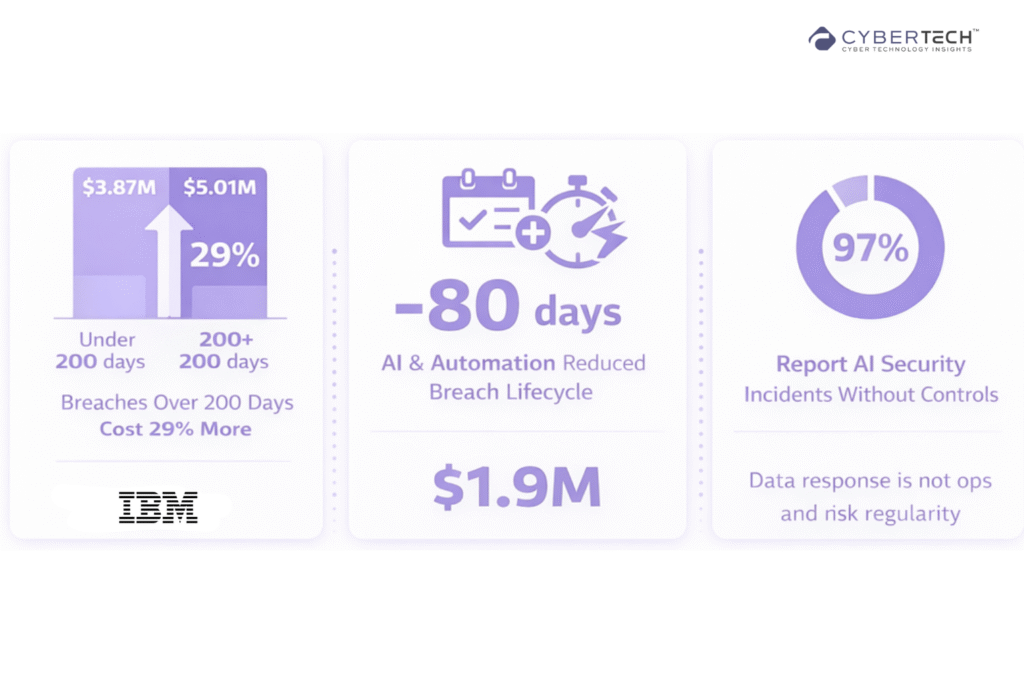
According to IBM, breaches contained in under 200 days cost $3.87M, while those exceeding that timeline rose to $5.01M, a 29% increase.
At the same time, organizations using security AI and automation reduce breach lifecycle by 80 days and save up to $1.9M per incident.
Faster response is not operational efficiency. It is a direct cost reduction and risk containment.
With 97% of organizations reporting AI-related security incidents without proper controls, variability in human-led decisions introduces systemic exposure.
Automation enforces deterministic, context-driven execution, ensuring that threat response is based on risk signals and behavioral patterns, not analyst fatigue or inconsistency under pressure.
Modern environments span hybrid and multi-cloud architectures, where breach costs rise to $5.05M in distributed environments vs $4.01M on-prem.
As telemetry volume grows exponentially, scaling human-led operations becomes economically and operationally unviable. Automation enables organizations to process high-volume signals, correlate threats, and execute response actions without linear increases in headcount.
Close the Gap Between Detection and Action
Attackers are operating at machine speed, executing multi-stage campaigns across identity, cloud, and application layers within compressed timelines.
At the same time, breach data from IBM and threat intelligence insights across the industry show that delays in detection and response continue to drive both financial impact and operational disruption.
This creates a clear structural reality. Organizations are not failing to detect threats. They are failing to act on them fast enough.
Final Perspective
In high-velocity environments, where digital infrastructure operates across distributed cloud, identity, and application layers in real time, delay is not an operational inefficiency. It is a direct expansion of the attack window.
Security leadership will no longer be defined by the breadth of visibility or the density of tooling. It will be defined by the ability to maintain decision control across the attack lifecycle.
This requires eliminating decision latency within SOC workflows, enabling intelligence-driven response orchestration, and sustaining deterministic execution under continuous, machine-speed adversarial activity.
In this landscape, advantage is no longer derived from detection capability alone. It is defined by the ability to translate telemetry into action with speed, accuracy, and confidence across the entire attack surface.
FAQs
1. How does automation improve cyber threat detection and response time?
Automation reduces the time between detection and response by enabling real-time correlation and execution. Organizations using AI and automation shorten breach lifecycles significantly and reduce overall impact, addressing the growing speed of attacks driven by AI.
2. Why are traditional security operations no longer effective against modern cyber threats?
Traditional SOC models rely on manual triage and fragmented tools, which cannot keep up with the scale and velocity of attacks. With AI accelerating attack execution and 72% of organizations reporting increased cyber risk, legacy approaches fail to respond in time.
3. What are the biggest cybersecurity risks organizations face today?
The most critical risks include phishing, credential theft, ransomware, and AI-driven attacks. Phishing alone accounts for a major share of incidents, while AI is amplifying both attack scale and sophistication across industries.
4. How does AI impact cybersecurity threats and defense strategies?
AI is transforming both sides of cybersecurity. Attackers use it to scale phishing, automate reconnaissance, and accelerate exploitation, while defenders use it for real-time threat detection and response. However, governance gaps remain, with many organizations lacking proper controls.
5. What should organizations evaluate before investing in automated cyber defense solutions?
Leaders should assess response speed, cross-domain visibility, integration with existing systems, and the ability to automate decision-making. With cybercrime costs projected to exceed $10.5 trillion annually, investments must directly reduce risk and operational delay.
Don’t let cyber attacks catch you off guard – discover expert analysis and real-world CyberTech strategies at CyberTechnology Insights.
To participate in upcoming interviews, please reach out to our CyberTech Media Room at info@intentamplify.com.
🔒 Login or Register to continue reading












