Zero Trust changed how organizations think about cybersecurity. It removed implicit trust from users, devices, and access. Every interaction is verified, monitored, and continuously evaluated.
However, one critical layer still operates on the very assumption Zero Trust was designed to eliminate. The network edge. The router, the device that connects everything, is still treated as trusted infrastructure in most environments.
Where Does Your Zero Trust Strategy Stop?
Before going further, pause on this:
- Are your routers part of your security monitoring stack?
- Do you validate traffic before it enters your network?
- Is your network edge included in your Zero Trust model?
If the answer is unclear, your Zero Trust implementation is incomplete.
Zero Trust Solved Access, Not Entry
Zero Trust has been highly effective where organizations have focused their investments.
Identity is verified. Endpoints are validated. Access is controlled.
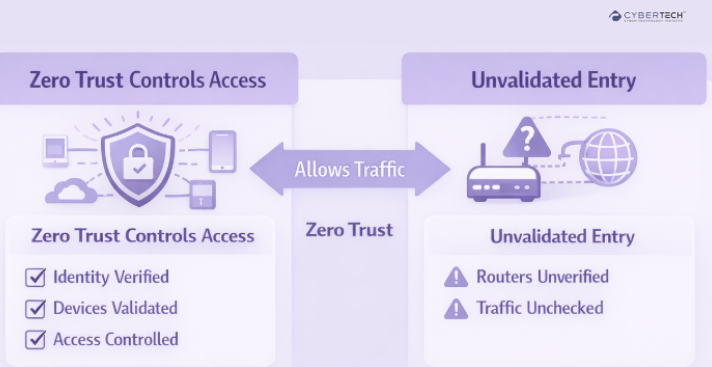
However, routers remain outside continuous verification models. Traffic is allowed in before it is fully validated.
Zero Trust verifies who is accessing your environment. It rarely verifies how that access begins.
Extend Zero Trust Beyond Access Control
Most Zero Trust strategies stop at identity.
Cyber Technology Insights helps organizations extend Zero Trust principles to the network edge, ensuring visibility, validation, and control from the moment traffic enters your environment.
Identify Your Entry-Point Risk
Before you can secure the network edge, you need a clear view of where your exposure begins.
Most organizations don’t have that visibility today.
- Evaluate your network edge exposure before it becomes an incident.
- Map all routers across your environment.
- Identify unmanaged or unmonitored devices.
- Assess where visibility drops off.
The Router Gap Is a Coverage Gap
Routers were built for connectivity, not security.
As a result, they sit outside the layers where most security investments are focused.
The Coverage Gap Framework
| Security Layer | Coverage Level | Router Inclusion |
| Identity & Access | High | None |
| Endpoint Security | High | None |
| Cloud Security | High | None |
| Network Detection | Medium | Partial |
| Network Edge (Routers) | Low | Minimal |
Security is strongest where visibility is highest. Routers sit where visibility is lowest.
Why Modern Security Stacks Still Miss This Layer
Organizations have invested in advanced platforms across their stack. But these tools were not designed to secure the network entry point.
Security Stack vs Router Coverage
| Solution Category | What It Secures | Where It Falls Short |
| CSPM | Cloud environments | Does not validate entry traffic |
| NDR | Network behavior | Limited visibility at edge |
| SASE | Access control | Assumes trusted infrastructure |
In environments powered by Microsoft Azure, CSPM ensures strong cloud posture. But it does not verify the integrity of incoming traffic.
Platforms like Darktrace and Vectra AI detect anomalies, but only where visibility exists.
Solutions such as Zscaler enforce secure access, but assume the network itself is not compromised.
You didn’t miss security investments. You missed where they don’t apply.
Vendor Context (Not Comparison, Coverage Insight)
Even the most advanced security platforms are designed around visibility. The network edge is where that visibility often breaks.
| Vendor | Category | Strength | Router Gap |
| Microsoft | CSPM / Cloud Security | Strong posture management | No edge validation |
| Darktrace | NDR | AI-based detection | Depends on visibility |
| Vectra AI | NDR | Threat detection | Limited edge coverage |
| Zscaler | SASE | Secure access | Assumes trusted network |
Close the Visibility Gap
If your tools don’t see the router, they can’t secure it.
- Integrate routers into monitoring systems.
- Extend telemetry to the network edge.
- Identify blind spots in detection coverage.
The FCC Signal and the Risk Leaders Must Own
Recent action by the Federal Communications Commission highlights rising concern around infrastructure-level risk.
But regulation addresses future procurement. Risk exists in the current infrastructure.
Threat groups like Volt Typhoon have already demonstrated how routers can be exploited for persistent access.
The risk is not what you plan to deploy. It is what you are already running.
Framework: From Assumed Trust to Verified Entry
Traditional Model
- Trust the network edge.
- Verify after entry.
Required Model
- Verify before entry.
- Monitor continuously at edge.
| Approach | Entry Validation | Risk Level |
| Traditional | No | High |
| Zero Trust (Current) | Partial | Medium |
| Zero Trust (Extended) | Yes | Reduced |
What “True Zero Trust” Requires Now
Zero Trust is not about controlling access alone. It is about eliminating unverified trust everywhere.
- Treat routers as security assets.
- Extend visibility to the network edge.
- Enforce policy at entry points.
- Align ownership across teams.
The Layer Security Leaders Overlook
You don’t need another security tool to reduce risk. You need to reassess where your strategy stops.
For most organizations, it stops at the router, and that is where attackers begin.
The router is not just infrastructure. It is an unmonitored control point sitting inside your network.
Until that layer is secured, every other investment operates with a blind spot.
FAQs
1. Why does Zero Trust fail at the network edge?
Zero Trust focuses on identity, devices, and access control, but often excludes the network entry point. Routers are typically trusted by default, creating a gap where traffic enters without full validation.
2. How do routers create gaps in Zero Trust architecture?
Routers sit outside, continuously monitoring and enforcing policies in many environments. This allows unverified traffic to enter the network before security controls are applied.
3. Are routers included in modern Zero Trust frameworks?
In most implementations, routers are not fully integrated into Zero Trust models. They are treated as infrastructure rather than active security control points.
4. Can existing security tools cover router-level risks?
Tools like CSPM, NDR, and SASE provide strong coverage across cloud, network, and access layers. However, they rely on visibility and often do not secure unmanaged or unmonitored routers directly.
5. What steps should organizations take to secure routers in Zero Trust?
Organizations should bring routers into monitoring systems, enforce security policies at entry points, maintain regular patching, and align network and security teams under shared ownership.
To participate in upcoming interviews, please reach out to our CyberTech Media Room at info@intentamplify.com
🔒 Login or Register to continue reading









