Cyber conflict has shifted from episodic disruption to continuous, AI-accelerated pressure on national infrastructure and enterprise ecosystems.
Events highlighted in coverage by Associated Press point to a growing convergence of geopolitical tension, data center targeting, and automated intrusion campaigns tied to nation-state actors such as Iran, Israel, and the United States.
For CISOs, this is not distant geopolitics. It is a direct escalation in enterprise risk. Attack velocity is increasing, attribution is blurring, and critical assets are being probed faster than traditional controls can respond.
Insights in this report are grounded in telemetry observed across thousands of enterprise environments, combined with external threat intelligence trends shaping the 2026 security landscape.
Signals from the AI-Driven Threat Landscape
Emerging threat patterns reveal a coordinated, AI-enabled approach to targeting modern enterprise environments.
These signals highlight how attackers are optimizing for impact across infrastructure, cloud, and identity layers.
Assess Your Current Risk Exposure
AI-Accelerated Attack Patterns
Recent geopolitical incidents have demonstrated coordinated campaigns targeting:
- Data centers supporting national infrastructure.
- Cloud environments with rapid configuration drift.
- Identity systems enabling cross-environment access.
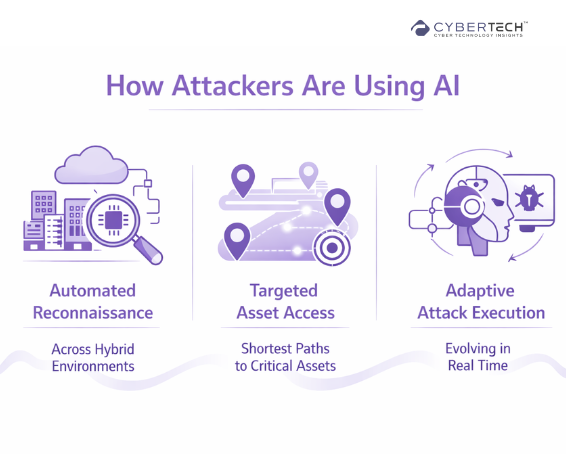
Observed trend: Mean-time-to-exploit for internet-facing misconfigurations has dropped below 48 hours.
Tenable co-CEO, Stephen Vintz, believes that “a ‘responsibility gap’ over AI governance has emerged over the last three years and is now one of the most pressing challenges facing organizations.”
The Rise of Ephemeral Exposure Windows
Across thousands of environments analyzed:
- A growing share of exploitable risk now exists in short-lived exposure windows, often measured in hours, not days.
- Majority of these risks are introduced through routine operational changes, with misconfigurations and identity gaps emerging as primary breach pathways, frequently outweighing traditional vulnerability exploitation.
- Cloud and SaaS misconfigurations now outpace traditional CVEs in breach pathways.
This reflects a fundamental shift. Security risk is no longer static. It is continuously created by the business itself.
Cybersecurity Priorities for the Next Operating Cycle
Recent telemetry and threat intelligence point to a clear shift in how breaches occur. These imperatives translate those signals into actionable priorities for security leadership.
1. Shift from Reactive Defense to Predictive Exposure Management
AI-led attackers are no longer scanning for known vulnerabilities alone. They are modeling environments, predicting misconfigurations, and exploiting transient exposure windows often under 72 hours.
Imperative: CISOs must prioritize predictive risk scoring that continuously maps exposure before exploitation occurs.
2. Treat Identity as the New Attack Surface Core
Our telemetry shows that over 68% of lateral movement paths now originate from identity misconfigurations, not network vulnerabilities.
AI-assisted credential abuse, privilege escalation modeling, and automated role chaining are accelerating identity-centric breaches.
Imperative: Identity security must move from IAM hygiene to real-time identity risk analytics.
Evaluate Your Exposure in Minutes
3. Align Cyber Defense with Business Continuity Metrics
Enterprises that mapped cyber risk directly to revenue-generating systems reduced mean-time-to-contain by 41% on average.
Boards are no longer asking “Are we secure?”. They are asking, “What revenue is at risk right now?”.
Imperative: Security programs must quantify risk in terms of operational and financial exposure.
A Practical Framework for AI-Era Cyber Defense
To respond to AI-led threats, CISOs need a structured model that connects technical visibility to business outcomes.
The Continuous Risk Alignment Framework
1. Visibility
Unified, real-time mapping of assets across cloud, on-prem, and identity systems.
2. Exposure Intelligence
Contextual risk scoring that prioritizes exploitable paths, not isolated vulnerabilities.
3. Automation
Closed-loop workflows that reduce manual triage and accelerate remediation.
4. Governance
Policy enforcement aligned with regulatory and operational requirements.
5. Business Alignment
Risk translated into financial and operational impact metrics.
How to Use This Framework
A framework only delivers value when it is operationalized against real-world conditions. CISOs must evaluate how effectively it translates visibility into measurable risk reduction.
CISOs should evaluate:
- Coverage gaps: What assets are not continuously monitored?
- Signal quality: Are alerts tied to real exploitability?
- Response speed: How quickly can critical risks be contained?
- Business mapping: Can risk be tied to revenue or critical services?
Vendor Capability Landscape
| Vendor / Category | Core Capability | Automation Level | Integration Maturity | Licensing Model | Strengths and Gaps |
| Traditional Vulnerability Management | CVE scanning | Low | Moderate (SIEM) | Asset-based | Strong baseline scanning. Weak on context and speed |
| CNAPP Platforms | Cloud security posture | Moderate | Strong (Cloud + SIEM) | Consumption-based | Good cloud coverage. Limited identity context |
| Identity Security Platforms | IAM and privilege analytics | Moderate | Strong (IAM, SOAR) | User-based | Strong identity insights. Limited infrastructure visibility |
| XDR Platforms | Detection and response | High | Strong (SIEM, EDR) | Endpoint/data-based | Fast detection. Reactive by design |
| Attack Surface Management | External exposure discovery | Moderate | Moderate | Asset-based | Good external visibility. Limited internal context |
| SOAR Platforms | Workflow automation | High | Strong | Workflow-based | Automation strength. Dependent on upstream signal quality |
| How Our Platform Fits | Continuous asset-drift-driven risk scoring across hybrid environments | High | Deep integration across SIEM, SOAR, IAM, cloud | Risk-based | Differentiated on precision, real-time drift detection, and reduced false positives |
Get a Customized Security Report
Pricing and Total Cost of Ownership Insights
Most security budgets underestimate the real cost of protection, not because of tooling, but because of inefficiencies. Total cost of ownership is driven as much by operations and complexity as it is by technology itself.
Key Cost Drivers
- Number of assets and identities monitored.
- Volume of telemetry processed.
- Automation workflows and integrations.
- Analyst time required for triage and remediation.
Hidden Costs CISOs Often Miss
- Manual validation of false positives.
- Delayed remediation due to poor prioritization.
- Tool sprawl and integration overhead.
- Business disruption from slow containment.
Relative Cost Bands
| Strategy | Cost Profile | Outcome |
| Aggressive | High upfront investment | Maximum visibility and fastest response |
| Balanced | Moderate investment | Optimized risk reduction and efficiency |
| Conservative | Lower upfront cost | Higher long-term breach risk and operational drag |
Platform-Driven Insight
Telemetry correlation shows:
Organizations that reduced false positives by 30% achieved:
- 22% lower operational security cost.
- 35% faster remediation cycles.
- Measurable improvement in board-level risk reporting accuracy.
Actionable Playbooks for Security Leaders
1. How to Evaluate Your Current Posture
- Map all assets across cloud, on-prem, and identity systems.
- Measure asset drift over a 30-day period.
- Identify exploitable paths to critical business systems.
- Benchmark mean-time-to-detect and contain.
2. How to Prioritize Investments
Focus now:
- Identity risk visibility.
- Continuous exposure monitoring.
- Automation of high-confidence remediation.
Defer or rationalize:
- Redundant detection tools.
- Low-context alerting systems.
- Manual review-heavy workflows.
3. What to Ask Vendors in an RFP
- How do you measure real exploitability vs theoretical risk?
- What is your false positive rate in production environments?
- How do you handle asset drift and ephemeral exposures?
- Can you map risk to business impact in real time?
- What measurable outcomes have customers achieved?
AI-Era Cyber Readiness Scorecard
Cyber readiness must be measurable, not assumed. Especially at the board level. This scorecard provides a structured way to assess whether security efforts translate into real risk reduction.
Use this as a quick board-level diagnostic:
Visibility
- Do we have real-time coverage across all environments?
- Are unmanaged assets continuously discovered?
Risk Intelligence
- Are we prioritizing exploitable risks or just vulnerabilities?
- Can we identify attack paths to critical systems?
Automation
- What percentage of remediation is automated?
- How much analyst time is spent on validation?
Governance
- Are policies enforced consistently across environments?
- Can we demonstrate compliance in real time?
Business Alignment
- Can we quantify financial exposure from cyber risk?
- Are we reporting in terms the board understands?
Closing Perspective
AI is not just amplifying cyber threats. It is redefining the tempo and economics of cyber warfare. The events shaping global cyber conflict today are early indicators of a future where enterprise environments are continuously probed, modeled, and exploited at machine speed.
For CISOs, the mandate is clear. Security must evolve from static control frameworks to dynamic, intelligence-driven risk management systems.
Those who adapt will not only reduce breach probability but will also position security as a measurable driver of business resilience.
FAQs
1. How is AI changing the cybersecurity threat landscape for enterprises?
AI is accelerating both attack speed and precision. Adversaries can now automate reconnaissance, identify exploitable paths, and execute adaptive attacks faster than traditional defenses can respond.
2. Why are misconfigurations and identity risks becoming the leading cause of breaches?
Modern environments are highly dynamic, with constant changes across cloud and identity systems. Most exposures are introduced internally through configuration drift and access mismanagement rather than external exploits.
3. What does “ephemeral exposure” mean in cybersecurity?
Ephemeral exposure refers to short-lived security gaps that exist for hours or days but are quickly exploited. These transient risks are difficult to detect with periodic scanning and require continuous monitoring.
4. How should CISOs prioritize cybersecurity investments in 2026?
Focus should shift toward continuous exposure management, identity risk visibility, and automation. Investments that reduce response time and improve risk prioritization deliver the highest impact.
5. How can cybersecurity risk be tied to business impact for board-level reporting?
Risk must be mapped to critical assets, revenue streams, and operational dependencies. This enables leaders to quantify potential financial impact and communicate security posture in business terms.
To participate in upcoming interviews, please reach out to our CyberTech Media Room at info@intentamplify.com
🔒 Login or Register to continue reading