Industrial cyber attacks are no longer isolated disruptions. They are becoming systemic, faster, and more coordinated across IT and OT environments.
According to CrowdStrike’s 2025 Global Threat Report, targeted attacks on industrial and critical sectors have surged by up to 300%, driven by nation-state activity and increasingly sophisticated adversaries.
At the same time, AI-enabled attacks are accelerating execution timelines, with breakout times dropping to as little as minutes or even seconds .
This is not just an escalation. It is a fundamental change in how cyber threats operate.
Stay ahead of industrial cyber threats with real-time intelligence insights
Explore expert analysis on Cyber Technology Insights
Attack Surface Is Expanding Faster Than Security Can Adapt
Industrial environments were never designed for today’s threat landscape.
The convergence of IT and OT, combined with cloud adoption and connected infrastructure, has created:
- Expanded attack surfaces across supply chains
- Increased exposure of legacy systems
- Interdependencies that amplify risk across ecosystems
The World Economic Forum reports that 72% of organizations saw an increase in cyber risk in the past year, with supply chain vulnerabilities and interconnected systems driving complexity.
Identify Hidden Vulnerabilities Across Your Attack Surface
Start Your Exposure Assessment Now
Threat Intelligence Reveals the Real Problem: Speed
The defining characteristic of modern industrial attacks is not sophistication alone. It is speed.
- AI-enabled adversaries increased attacks by 89% year-over-year.
- Average breakout time dropped to 29 minutes, with some attacks executing in seconds.
- 79% of initial access attacks are now malware-free, exploiting identity and trusted access.
According to Microsoft’s Digital Defense Report, most attacks are financially motivated, with ransomware and data theft dominating modern campaigns.
This creates a critical reality:
By the time an attack is detected, it is often already in motion.
From Detection to Preemption: Gartner’s Strategic Shift
This is where Gartner’s concept of preemptive cybersecurity becomes essential.
Gartner argues that security must evolve beyond detection and response toward:
- Deny– Reduce attack surface and eliminate entry points.
- Disrupt– Stop attacks in early stages.
- Deceive– Mislead adversaries through controlled environments.
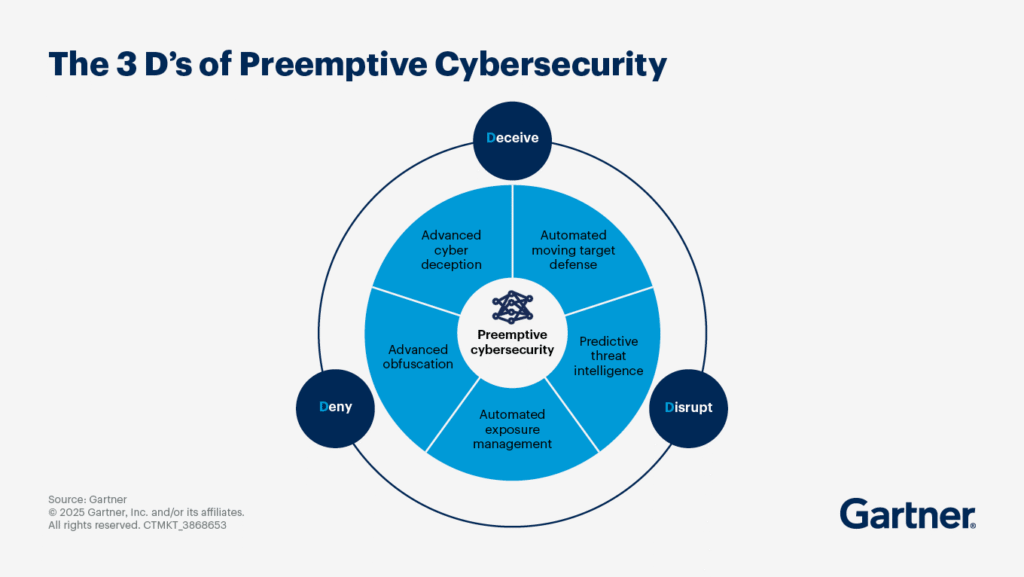
This aligns directly with what threat intelligence is revealing.
Modern attacks are:
- Faster than human response cycles.
- Distributed across identity, cloud, and endpoint layers.
- Designed to evade traditional detection systems.
Preemptive security operationalizes threat intelligence into real-time prevention.
Secure Your Critical Systems Before Attackers Exploit Them
Discover OT & ICS Protection Solutions
Leading Cybersecurity Vendors: A Strategic Comparison
| Capability | CrowdStrike Falcon Platform | Palo Alto Networks Cortex XDR | Microsoft Defender XDR | SentinelOne Singularity Platform |
| Core Strength | Threat intelligence & endpoint protection | Network + endpoint + cloud integration | Deep enterprise integration (Microsoft ecosystem) | Autonomous AI-driven response |
| Detection Approach | Cloud-native, intelligence-led detection | AI/ML behavioral analytics across layers | Integrated telemetry across identity, endpoint, cloud | Autonomous, agent-based detection |
| Response Capability | Managed threat hunting + response | Automated response with full-stack visibility | Automated investigation & remediation | Fully autonomous response (no human dependency) |
| Identity Security | Strong (identity threat detection) | Integrated across platform | Very strong (Azure AD, identity-first model) | Moderate, improving |
| Multi-Surface Coverage | Endpoint-heavy, expanding to cloud | Endpoint + network + cloud (XDR) | Endpoint + identity + cloud apps | Endpoint + cloud + identity (via integrations) |
| AI & Automation | AI-assisted threat hunting | AI-driven correlation & analytics | AI + security graph integration | Autonomous AI response engine |
| Ideal Use Case | Enterprises needing deep threat intelligence | Organizations with hybrid infrastructure | Microsoft-centric enterprises | Teams prioritizing automation & speed |
| Market Position | Leader in endpoint security | Platform consolidation leader | Enterprise ecosystem leader | Challenger with strong AI differentiation |
The Industrialization of Cyber Attacks
Cyber threats themselves are becoming industrialized.
Recent threat analysis shows:
- AI is enabling automated reconnaissance, phishing, and exploitation at scale.
- Cybercrime-as-a-Service models are lowering entry barriers for attackers.
- Identity-based attacks and multi-vector intrusions are now dominant.
This mirrors industrial production models. Scalable, repeatable, optimized.
Why Industrial Sectors Are Prime Targets
Industrial and critical infrastructure sectors are uniquely vulnerable because they combine:
- High operational impact.
- Legacy infrastructure.
- Limited downtime tolerance.
- Increasing digital integration.
Threat actors understand this.
Ransomware targeting critical infrastructure is expected to increase in both frequency and severity, with attackers applying greater pressure tactics to force payment .
The result is a shift from opportunistic attacks to strategic disruption campaigns.
Protect critical infrastructure with intelligence-led defense
Connect with cybersecurity leaders on Cyber Technology Insights
Threat Intelligence as the Decision Layer
Threat intelligence is no longer a supporting function. It is becoming the central decision layer of cybersecurity.
Modern organizations are using threat intelligence to:
- Predict attacker behavior before execution.
- Map adversary infrastructure and intent.
- Prioritize vulnerabilities based on exploit likelihood.
- Enable automated, real-time defensive actions.
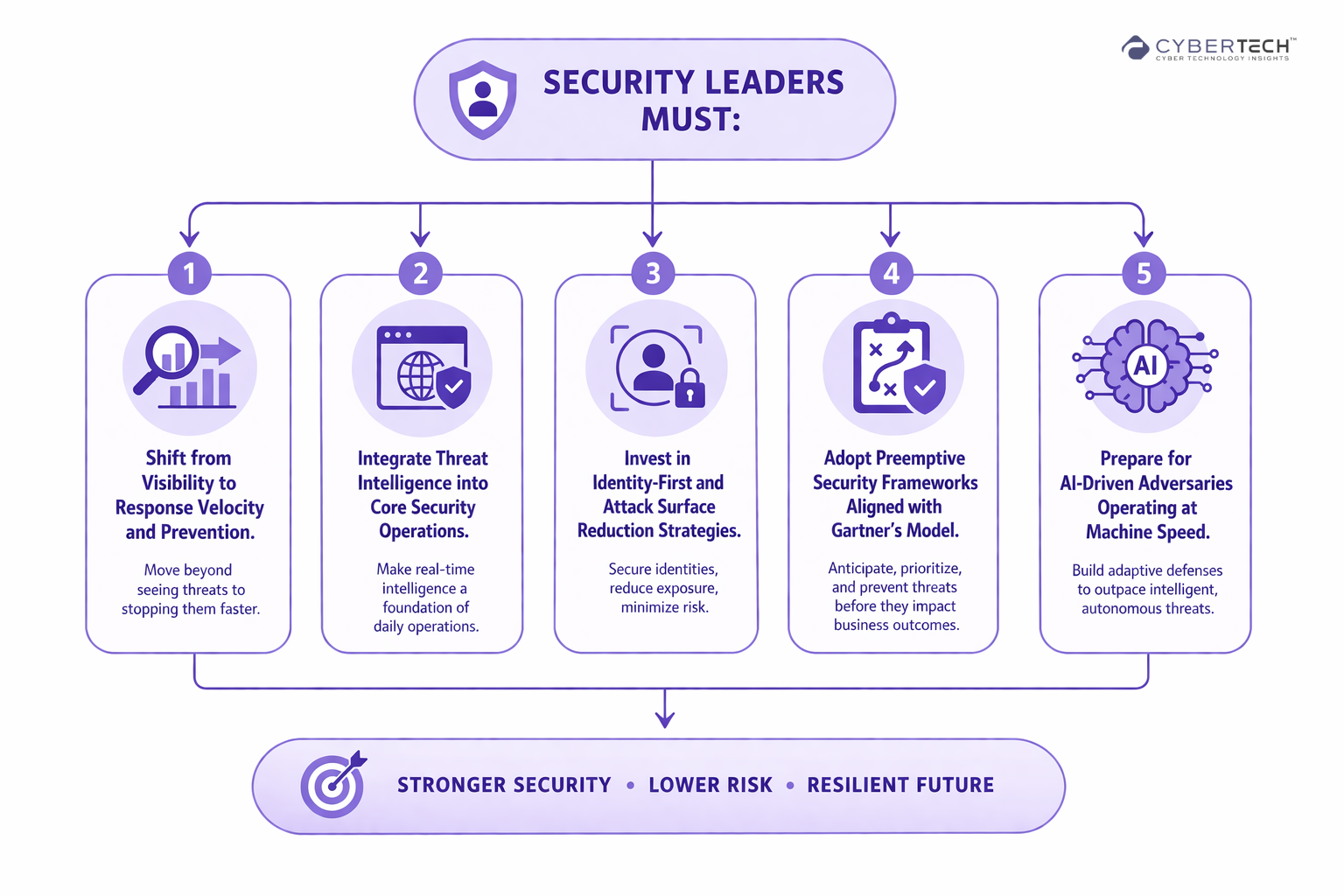
What Leaders Must Do Next
The surge in industrial cyber attacks is not a temporary spike. It is a structural transformation of the threat landscape.
Turn threat intelligence into competitive advantage
Stay informed with expert-led insights on Cyber Technology Insights
The Future is Preemptive
Industrial cyber attacks are evolving into high-speed, intelligence-driven operations.
The organizations that succeed will not be the ones that respond faster. They will be the ones that prevent attacks before they begin.
Threat intelligence provides visibility. Preemptive cybersecurity provides the action.
Together, they define the future of industrial security.
FAQs
1. How are industrial cyber attacks evolving in 2025–2026?
Industrial cyber attacks are becoming faster, more coordinated, and AI-driven. Attackers now execute breaches in minutes or seconds, shifting from isolated incidents to systemic, large-scale operations across IT and OT environments.
2. Why is threat intelligence becoming critical for enterprise security strategy?
Threat intelligence is evolving into a core decision layer. It enables organizations to predict attacker behavior, prioritize high-risk vulnerabilities, and take proactive action before attacks are executed.
3. What is driving the rapid expansion of the industrial attack surface?
The convergence of IT and OT systems, increased cloud adoption, and interconnected supply chains are expanding attack surfaces. Legacy systems and ecosystem dependencies further amplify exposure and risk.
4. What does “preemptive cybersecurity” mean for modern enterprises?
Preemptive cybersecurity focuses on stopping attacks before they start. It emphasizes reducing entry points, disrupting early attack stages, and deceiving adversaries, rather than relying solely on detection and response.
5. Why are industrial and critical infrastructure sectors prime targets for cyberattacks?
These sectors combine high operational impact, outdated infrastructure, and low tolerance for downtime. This makes them attractive targets for ransomware and strategic disruption campaigns aimed at maximum leverage.
To participate in upcoming interviews, please reach out to our CyberTech Media Room at info@intentamplify.com
🔒 Login or Register to continue reading