Cybersecurity is no longer defined by how well organizations defend. It is defined by how fast they can respond. Threat intelligence insights from Microsoft, CrowdStrike, Google Cloud, and SANS Institute point to a structural shift in the threat landscape.
The time between vulnerability discovery and exploitation has collapsed. What once unfolded over weeks now occurs within hours. In many cases, even minutes.
This is a systemic change in how attacks are designed, deployed, and scaled.
The New Reality: Attacks Are Measured in Minutes
Source: CISCO
Across telemetry and threat research:
- The fastest recorded eCrime breakout time has dropped to 27 seconds.
- Lateral movement can begin in under 5 minutes.
- Exploitation often occurs on the same day as disclosure.
- Internet-wide scanning begins within minutes of exposure.
Stay ahead of attacks that move faster than your defenses.
Explore real-time threat intelligence insights on Cyber Technology Insights.
Signals from GreyNoise and Team Cymru confirm continuous background scanning across global infrastructure, while incident analysis from SANS Institute shows exploitation patterns emerging almost immediately after vulnerabilities surface.
“Mass exploitation isn’t just about zero-days — it’s about attackers industrializing vulnerability exploitation at scale,” said Andrew Morris, Founder and Chief Architect at GreyNoise. “They care less about CVSS scores or KEV lists. They scan the entire internet.”
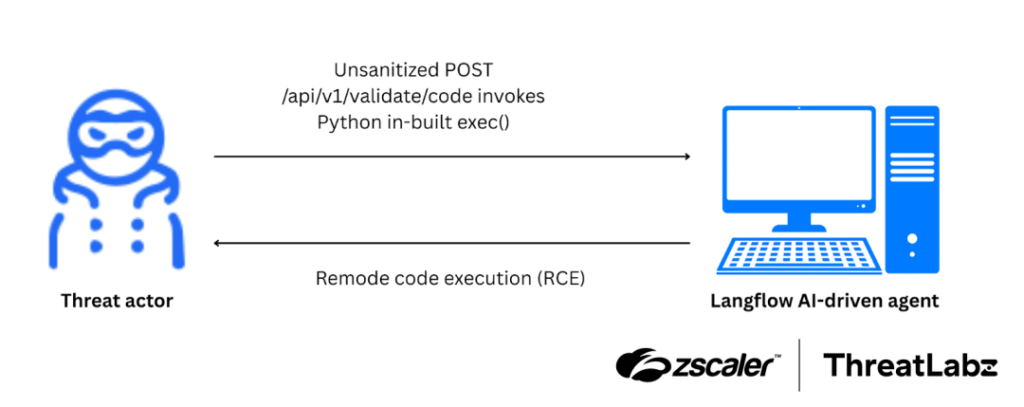
The 2025 Langflow RCE incident, widely reported across security intelligence feeds, demonstrated exploitation activity within hours of disclosure.
The attacker’s advantage is no longer stealth or sophistication. It is speed at scale.
The Compression of the Attack Lifecycle
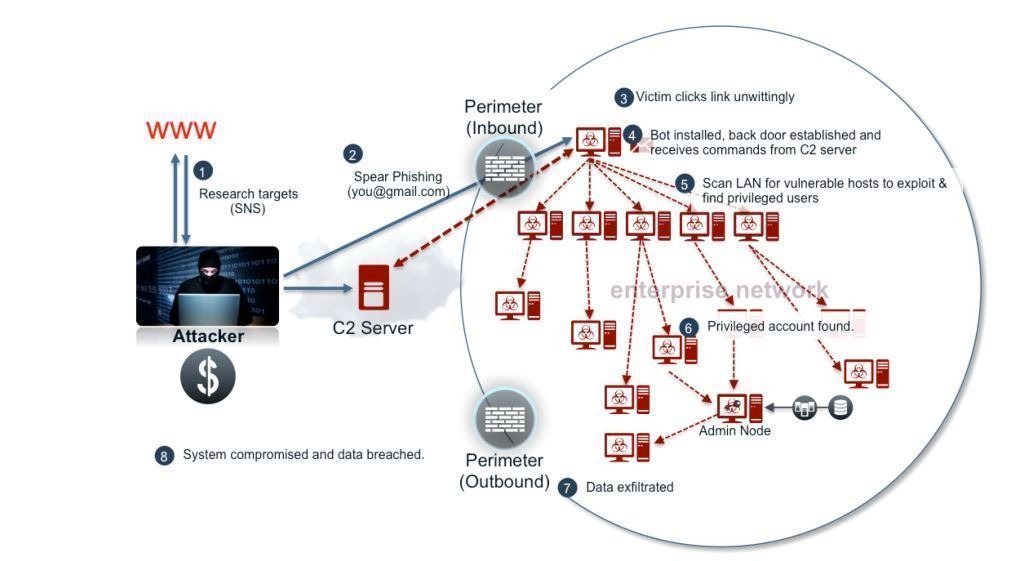
The modern attack lifecycle is no longer sequential. It is compressed and automated.
| Phase | Legacy Model | Current Reality |
| Reconnaissance | Manual, targeted | Continuous, automated |
| Exploit Development | Days to weeks | Hours or less |
| Initial Access | Selective | Opportunistic at scale |
| Lateral Movement | Hours to days | Minutes |
Insights from Microsoft threat intelligence reporting and Google’s security engineering blogs show that attackers now operate on pre-built playbooks, enabling near-instant transition from discovery to execution.
What’s Driving This Shift
The acceleration of modern cyberattacks is not incidental. It is driven by structural changes in how attacks are built and executed.
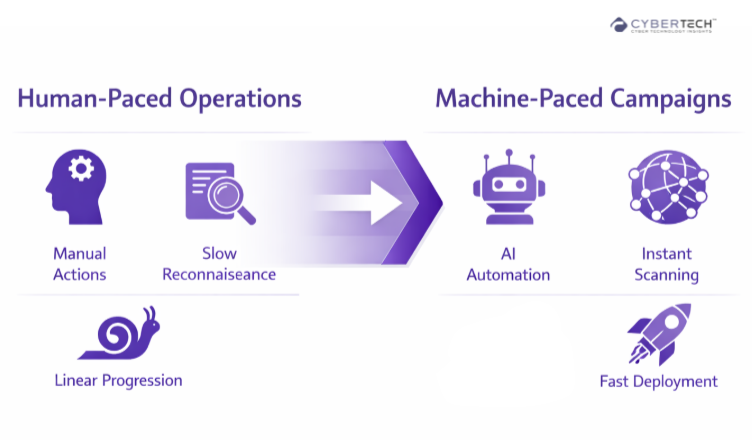
1. AI-Augmented Attack Execution
Research and field observations from Google and RSA indicate that AI is compressing the attack lifecycle by:
- Accelerating exploit development.
- Automating reconnaissance across large attack surfaces.
- Dynamically adapting payloads to evade detection.
This marks a shift from:
Human-paced operations to Machine-paced campaigns.
2. Industrialized Exploitation Ecosystems
Threat intelligence platforms such as Cyware and analysis from Optiv highlight the rise of:
- Exploit-as-a-service models.
- Pre-weaponized vulnerability kits.
- Shared attacker infrastructure.
Attackers are no longer building capabilities. They are assembling them.
3. Persistent Global Scanning
Telemetry from GreyNoise and Team Cymru shows:
- Continuous internet-wide scanning.
- Immediate targeting of exposed services.
- Opportunistic exploitation at scale.
This eliminates the concept of delayed exposure.
If an asset is reachable, it is already being tested.
Why Traditional Security Models Are Failing
Legacy security strategies were built on time buffers that no longer exist.
| Control Layer | Assumption | Reality |
| Patch Management | Days to deploy | Exploits in hours |
| Detection Systems | Early warning | Often post-compromise |
| SOC Operations | Human-led triage | Outpaced by automation |
Research from the World Economic Forum and McKinsey & Company reinforces that cyber risk is increasingly defined by response latency and systemic exposure, not just control gaps.
Check if your security model can keep up with today’s attack speed.
Or if it’s already operating on timelines attackers have outgrown.
Threat Intelligence Framework: The Speed-to-Breach Model
The speed at which modern attacks unfold has created a new way to understand cyber risk. Not as isolated events, but as a rapidly progressing timeline where each minute increases impact.
Modern Attack Timeline
| Stage | Timeframe | Impact |
| Vulnerability Disclosure | 0 hour | Low |
| Global Scanning | Minutes | Rising |
| Exploit Weaponization | < 24 hours | High |
| Initial Access | Hours | Critical |
| Lateral Movement | Minutes | Severe |
| Data Exfiltration | < 1 hour | Catastrophic |
This model, reflected across reporting from Microsoft, Google Cloud, and SANS Institute, highlights a single truth:
Security outcomes are now determined in the first hour, not the first week.
Assess your real-time threat response readiness.
Find out if you can keep up with modern attacks.
Vendor Intelligence Comparison
Security leaders are no longer evaluating vendors based only on features. They are assessing how effectively each platform enables speed, scale, and real-time response.
| Capability | Microsoft | CrowdStrike | Google Cloud |
| Core Strength | Identity and cloud telemetry | Adversary tracking | AI-driven detection |
| Intelligence Scale | Billions of signals daily | Real-time threat actor mapping | Global infrastructure visibility |
| Speed Focus | Identity-based attack detection | Breakout time metrics | Automated anomaly detection |
| Strategic Gap | Edge visibility | Supply chain depth | Multi-cloud complexity |
Strategic Implications for Security Leaders
Security leadership is no longer about managing vulnerabilities in isolation. It is about understanding how quickly those vulnerabilities can be exploited in real-world conditions.
Time Is the New Attack Surface
Threat intelligence across Microsoft, Google Cloud, and SANS Institute consistently shows that risk is no longer tied solely to vulnerabilities.
It is tied to:
How long those vulnerabilities remain exploitable.
Detection Alone Is No Longer Sufficient
With:
- Breakout times under 30 minutes.
- Exploitation within hours.
Detection without an automated response creates a gap attackers can consistently exploit.
Threat Intelligence Must Become Operational
Insights from Cyware and Optiv emphasize that intelligence must:
- Feed directly into response systems.
- Trigger automated actions.
- Prioritize threats based on active exploitation.
Intelligence Without Speed Is Irrelevance
Across threat intelligence reporting from Microsoft, Google Cloud, SANS Institute, GreyNoise, and Team Cymru, one pattern is clear. Attacks no longer unfold in stages. They execute in continuous motion.
Exposure is detected in minutes. Exploitation follows within hours. At-scale scanning often begins before defenders are even aware.
This is not a trend. It is a structural shift driven by AI-enabled execution, industrialized attack models, and persistent global scanning.
In this reality, threat intelligence cannot remain observational. It must become operational and trigger action in real time, in the narrow window where outcomes are still controllable.
Cyber risk is no longer defined by what organizations know. It is defined by how fast they act on what they know.
As attack timelines collapse, one conclusion becomes unavoidable. The value of intelligence is no longer measured in insight. It is measured in speed.
FAQs
1. Why are cyberattacks happening faster today?
Cyberattacks are accelerating due to AI-driven automation, pre-built exploit kits, and continuous internet-wide scanning. Attackers no longer operate manually. They execute at machine speed, reducing time from vulnerability discovery to exploitation to hours or minutes.
2. What is breakout time in cybersecurity, and why does it matter?
Breakout time refers to how quickly an attacker moves laterally after initial access. Shorter breakout times, often under 30 minutes, mean organizations have very limited time to detect and contain threats before significant damage occurs.
3. How does threat intelligence improve real-time security response?
Threat intelligence enables organizations to identify active threats, prioritize vulnerabilities based on exploitation, and automate response actions. When operationalized, it reduces response time and helps prevent breaches before escalation.
4. Why is traditional patch management no longer sufficient?
Traditional patch cycles are too slow for modern threats. Vulnerabilities are often exploited within hours of disclosure, making delayed patching ineffective. Organizations must prioritize real-time risk-based patching and exposure reduction.
5. What should CISOs prioritize to defend against fast-moving attacks?
CISOs should focus on real-time threat intelligence integration, automated response systems, identity security, and continuous attack surface monitoring. Speed of response is now more critical than breadth of controls.
To participate in upcoming interviews, please reach out to our CyberTech Media Room at info@intentamplify.com
🔒 Login or Register to continue reading











