Cloud security is defined as the set of policies, controls, and technologies used to protect cloud-based systems, data, and infrastructure. Accurate, but incomplete. It suggests containment. Control. Stability.
Cloud environments offer none of those by default.
They are dynamic. Distributed. Often opaque.
Security in this context becomes less about building defenses and more about continuously interpreting what is happening across systems that were never designed to be fully visible in the first place.
Why Cloud Architecture Creates Systemic Security Risks
Cloud security became critical because enterprise architecture changed faster than security models could adapt.
Three shifts are driving most of the friction.
First, infrastructure is no longer centralized. Workloads run across multiple cloud providers. SaaS platforms operate outside enterprise control.
Data moves constantly between environments. Visibility fragments quickly.
Second, configuration has replaced hardware as the primary control surface. Security is now defined by how systems are configured, not where they are located.
A single misconfigured storage bucket or overly permissive IAM role can expose critical assets instantly.
Third, ownership is distributed. Security decisions are made by developers, platform teams, DevOps engineers, and sometimes automated pipelines. Not just security teams.
Cloud security failures are rarely caused by missing tools. They emerge from misaligned responsibility across these layers.
The Shared Responsibility Model
Cloud providers position the shared responsibility model as a foundational principle, and it is. However, it creates a false sense of clarity.
Providers secure the underlying infrastructure. Customers secure everything they deploy on top of it.
That boundary sounds clean. It isn’t.
In IaaS environments, customers retain significant control. Operating systems, applications, data, identity policies. The attack surface is broad but visible.
Move to PaaS or serverless, and abstraction increases. Control decreases. Visibility often declines faster than responsibility.
Security teams still need to validate configurations they no longer fully manage.
This is where breakdowns occur. Not because responsibilities are unclear on paper, but because they are difficult to operationalize across rapidly changing environments.
Identity and Access Management
In cloud environments, identity is not just a security layer. It is the enforcement mechanism.
Every interaction. User access. Service communication. API calls. All mediated through identity systems.
Yet IAM remains one of the least mature areas in most enterprises.
Permissions accumulate over time. Roles expand to accommodate edge cases. Temporary access becomes permanent. Very few organizations maintain strict least-privilege models beyond initial deployment.
The result is predictable. Identity sprawl.
An attacker does not need to exploit infrastructure if valid credentials already provide access to sensitive systems.
Cloud platforms offer advanced IAM capabilities. Conditional access. Role-based policies. Context-aware authentication. But these features require continuous tuning.
Static IAM configurations in dynamic environments create silent exposure.
Data Protection and Encryption
Encryption is widely implemented across cloud platforms.
The important question is not whether data is encrypted. It is who controls the encryption.
Cloud providers offer managed key services that simplify implementation. But they centralize trust within the provider’s ecosystem.
Customer-managed keys introduce more control. They also introduce complexity. Key rotation, access policies, storage decisions. Mismanagement here can lead to both exposure and data loss.
Data protection in cloud environments extends beyond encryption. Data classification, tokenization, and access governance matter just as much.
Most enterprises encrypt everything. Few understand where their most sensitive data actually resides.
Network and Infrastructure Security
Cloud networks create the appearance of isolation. Virtual networks. Subnets. Security groups.
But these constructs are logical. Not physical.
A misconfigured rule can expose internal services externally within minutes. There is no hardware boundary to fail safely.
Traditional network monitoring approaches struggle in this model. Traffic is distributed. East-west movement is harder to track. Logging exists, but it is fragmented across services and providers.
Microsegmentation has emerged as a response. Granular isolation of workloads to limit lateral movement.
Effective in theory. Operationally complex.
Policies must account for application dependencies that are not always well understood. Over-segmentation can break legitimate workflows. Under-segmentation leaves exposure paths open.
DevSecOps and Application Security
Cloud environments accelerate development cycles. Infrastructure is defined in code. Deployments happen continuously.
Security is expected to integrate into this process without slowing it down.
DevSecOps attempts to embed security into development pipelines. Automated checks. Policy enforcement. Vulnerability scanning before deployment.
The model works when security aligns with developer workflows.
It fails when it introduces friction.
Developers will bypass controls that delay releases. Security tools that generate excessive false positives are ignored. Overly rigid policies are disabled.
The challenge is not tooling. It is alignment.
Security must operate at the same speed as development without becoming invisible.
Governance, Risk, and Compliance
Compliance frameworks were designed for relatively stable environments. Cloud infrastructure is anything but stable.
Resources are created and destroyed continuously. Configurations change frequently. Data flows across regions and services.
Point-in-time audits are insufficient.
Continuous compliance monitoring is becoming standard. Automated checks against policy baselines. Real-time alerts for drift.
But compliance does not equal security.
Organizations can meet regulatory requirements while still exposing critical assets through configuration gaps or excessive permissions.
Risk management in cloud environments requires context. Understanding which assets matter most, how they are accessed, and what exposure actually means in business terms.
That level of contextual awareness is still developing in most enterprises.
The Core Pillars of Cloud Security
Across different frameworks and vendors, cloud security consistently converges around five foundational pillars.
Identity
The primary control layer. Governs who and what can access systems.
Data
The asset under protection. Often poorly classified and widely distributed.
Network
The connective layer. Defines how systems communicate, but lacks physical enforcement.
Governance
The policy framework. Aligns security with regulatory and business requirements.
Response
The operational layer. Detects, investigates, and remediates incidents.
These pillars are interdependent. Weakness in one propagates across the others.
Vendor Landscape: Integration vs Visibility
Enterprises evaluating cloud security platforms often face a familiar decision. Rely on cloud-native security tools or adopt third-party platforms.
Cloud-native offerings from AWS, Azure, and Google Cloud provide deep integration with their respective environments. They offer native visibility, lower latency, and simpler deployment.
But they are inherently limited in multi-cloud environments. Visibility becomes fragmented across providers.
Third-party platforms such as Wiz, Palo Alto Networks Prisma Cloud, and CrowdStrike Falcon Cloud Security attempt to unify this visibility.
Wiz has gained attention for its agentless architecture and graph-based risk analysis. It prioritizes speed and broad visibility across environments.
Prisma Cloud offers deeper policy control and more mature enterprise features, particularly in complex deployments.
CrowdStrike extends its endpoint detection capabilities into cloud workloads, emphasizing threat detection over configuration posture.
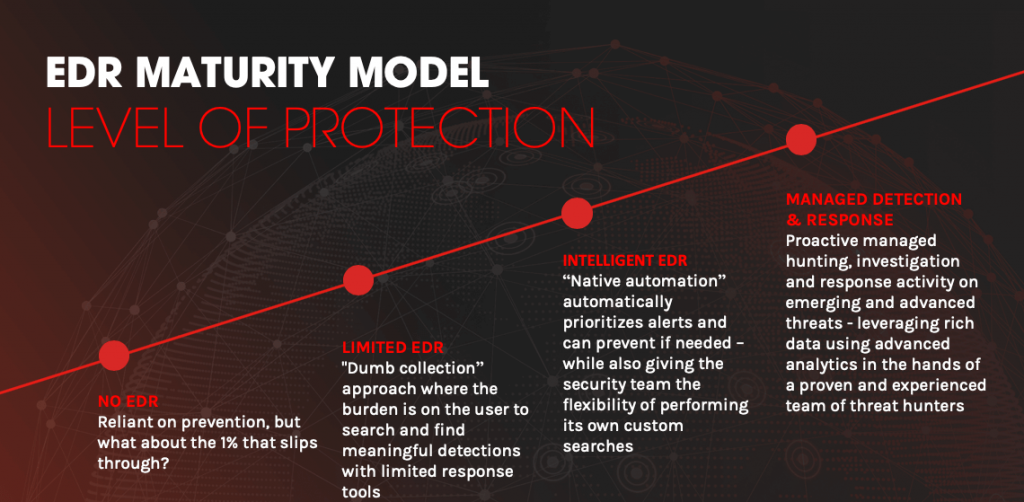
Source: CrowdStrike
No platform fully solves the problem. Each introduces trade-offs between depth, coverage, and operational complexity.
Platform consolidation is becoming more common. Enterprises prefer fewer tools with broader capabilities. But this increases dependency on specific vendors.
Pricing Realities: Where Strategy Meets Budget
Cloud security pricing is rarely straightforward.
Cloud-native tools are often bundled or appear low-cost initially. Costs emerge through usage patterns. Logging, data storage, API calls.
Third-party platforms typically follow subscription models. Pricing scales with workloads, assets, or data volume.
Broadly:
Cloud-native tools reduce upfront investment but introduce variable operational costs.
Third-party platforms require higher initial spend but offer more predictable pricing structures.
The larger cost risk is not tooling. It is exposure.
Misconfigurations can lead to breaches that far exceed the cost of any security platform.
Cloud Security Is an Ongoing Interpretation Problem
Cloud security is often approached as a deployment milestone. Something to implement and move past.
That model does not hold.
Cloud environments change continuously. New services, new integrations and new access patterns.
Security becomes an ongoing process of interpretation. Understanding signals across identity systems, configurations, network activity, and data flows.
There is no fixed perimeter to defend. No stable baseline to maintain.
Only a continuously shifting system that requires constant adjustment.
Most enterprises are still adapting to that reality.
FAQs
1. What are the core components of cloud security for enterprises?
Cloud security is built around identity, data protection, network controls, governance, and incident response. Most enterprise risk concentrates in identity and configuration layers rather than infrastructure itself.
2. Who is responsible for security in cloud environments?
Responsibility is shared between the cloud provider and the customer. Providers secure the underlying infrastructure, while enterprises are accountable for configurations, access control, data protection, and application security.
3. What are the biggest cloud security risks for large organizations?
Misconfigurations, excessive IAM permissions, exposed storage, and lack of visibility across multi-cloud environments. Most breaches originate from internal control gaps rather than external attacks.
4. How do enterprises secure multi-cloud environments effectively?
By centralizing visibility across providers, standardizing IAM policies, and using unified security platforms or abstraction layers to reduce fragmentation and policy drift.
5. What is the role of microsegmentation in cloud security?
Microsegmentation limits lateral movement by isolating workloads at a granular level. It reduces breach impact, but increases operational complexity and requires deep understanding of application dependencies.
To share your insights, please write to us at news@intentamplify.com








