The White House has released President Trump’s 2026 Cyber Strategy for America. It outlines how the administration intends to strengthen the country’s cyber posture at a time when digital threats increasingly intersect with national security, economic stability, and geopolitical competition.
The strategy is accompanied by a new executive order targeting cybercrime, fraud, and digital schemes affecting American businesses and critical infrastructure. Together, the two actions signal a renewed attempt to reposition cybersecurity as a strategic domain rather than a technical policy issue.
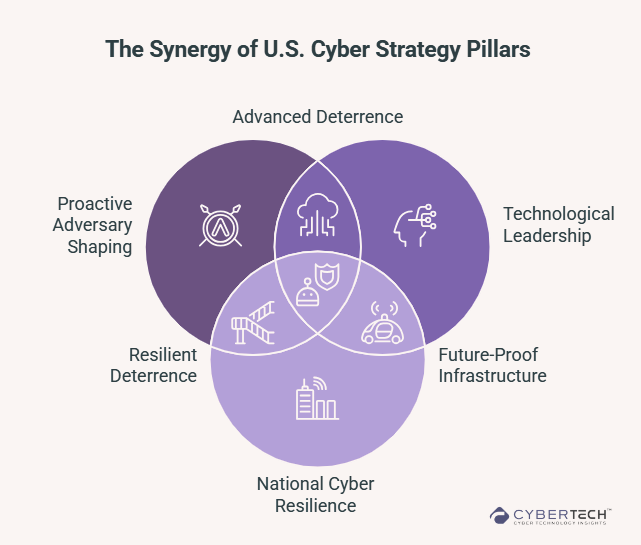
The framework introduces six policy pillars that will guide federal cybersecurity investments and operations. While the document sets the direction, detailed implementation guidance, funding priorities, and operational mandates are expected through follow-on policy actions in the coming months.
For cybersecurity leaders, the release raises two central questions. First, whether the strategy reflects a meaningful shift in how the United States approaches cyber defense.
Second, whether the federal government can translate strategic intent into operational execution across a threat landscape that evolves far faster than policy.
The Doctrine Taking Shape in the U.S. Cyber Policy
While the strategy is presented through six policy pillars, the framework ultimately converges around three broader priorities. Deterrence, technological advantage, and national resilience.
First, the strategy places greater emphasis on shaping adversary behavior rather than simply responding to cyber incidents. The document signals a willingness to deploy the full range of U.S. cyber capabilities, from intelligence and defensive operations to offensive disruption, with the goal of raising the operational and financial costs of cyber aggression.
Second, the strategy frames technological leadership as a core security requirement. Artificial intelligence, quantum computing, and advanced cryptography are treated not just as innovation priorities but as strategic assets that must be secured.
Modernizing federal networks with zero-trust architecture, AI-enabled cyber defense, and post-quantum cryptography reflects a broader effort to maintain technological superiority in an increasingly contested digital environment.
Finally, the strategy focuses on strengthening national cyber resilience across critical infrastructure and supply chains. Since most infrastructure systems in the United States are privately operated, the framework emphasizes deeper coordination between government, industry, and state and local authorities to reduce systemic vulnerabilities.
The question now is how this vision translates into operational reality. Industry leaders across the cybersecurity ecosystem see opportunity in the strategy’s direction, but also significant challenges in its execution.
Cybersecurity Moves to the Center of National Security Policy
One of the most significant signals in the strategy is structural rather than technical. Cybersecurity is being treated as a standalone national security priority instead of a supporting component of defense or technology policy.
Dave Gerry, CEO of Bugcrowd, views that distinction as more than symbolic.
“Anytime that an administration is publicly prioritizing cybersecurity at a very strategic level is a positive sign for the industry and for broader national security implications. It’s a meaningful first step,” Gerry said.
Separating cyber policy into its own strategic framework elevates the issue within national security planning.
“Seeing that cyber is being broken out into its own distinct national security strategy document elevates it to a first order national security issue, not just a piece of a broader defense or technology policy.”
The priorities outlined in the strategy broadly align with concerns long raised by the cybersecurity community. They include strengthening cyber deterrence, modernizing federal networks, reforming regulatory requirements, protecting critical infrastructure, and expanding the cybersecurity workforce.
Yet Gerry also points to a familiar limitation of strategic policy documents. They often describe the destination without specifying the path.
“The challenge with the document is the vagueness. It reads more like a high-level messaging document, which while aligned to the needs of the Nation and industry, lacks the specificity needed to make decisions.”
The success of the strategy will therefore depend less on the framework itself and more on how quickly it is translated into operational programs.
Cybersecurity at Machine Speed
The strategy also reflects a growing recognition that cyber threats now operate at speeds that traditional human-led security operations struggle to match.
Marcus Fowler, CEO of Darktrace Federal, describes the evolving cybersecurity environment:
“The Administration’s new cyber strategy reflects a growing recognition that the cybersecurity landscape is evolving at machine speed.”
Automation and artificial intelligence are increasingly used by attackers to scale operations and identify vulnerabilities across global networks.
“As adversaries increasingly leverage automation and artificial intelligence to scale their operations, defending critical infrastructure and federal networks will require equally advanced capabilities.”
For that reason, Fowler believes artificial intelligence must become a core component of national cyber defense.
“AI-powered cybersecurity solutions must become a core component of our national defense posture.”
The growing convergence of digital and physical infrastructure further complicates the challenge.
“The reality is that IT and OT are not converging – they are already converged.”
Critical infrastructure systems now operate as cyber-physical environments in which digital networks directly influence physical processes. Securing those systems requires continuous visibility across both domains.
Cyber Defense Beyond Government Systems
Another defining feature of the strategy is its recognition that defending national cyber interests requires protecting infrastructure that largely sits outside federal control.
In the United States, the majority of critical infrastructure is privately owned. Energy grids, telecommunications networks, transportation systems, and healthcare infrastructure are primarily operated by commercial organizations.
John Watters, CEO and Managing Partner at cyber risk intelligence firm iCOUNTER, believes the strategy acknowledges this structural reality more directly than previous cyber policies:
“The Cyber Strategy for America, and accompanying Executive Order, cover common objectives of prior administrations with one bold and important difference,” Watters said.
“President Trump makes it clear that the Government will now lean in to help protect the entirety of our national interests, not just government infrastructure.”
That distinction matters because roughly 90 percent of U.S. critical infrastructure is operated by the private sector.
“In a country where 90% of our critical infrastructure is in commercial hands, this is a game changer,” Watters explained.
Historically, private infrastructure operators have carried much of the responsibility for defending their networks without access to the full intelligence and operational capabilities available to federal cyber agencies.
“The commercial sector has owned cyber risk without the tools or authorities required to defend forward.”
If federal cyber capabilities embedded within agencies such as U.S. Cyber Command and the National Security Agency are increasingly used to support the defense of private infrastructure, the deterrence dynamics could change significantly.
“If our national cyber capabilities embedded in Cyber Command, NSA, and other Government agencies are tasked with defending our commercial sector, it changes the risk calculus for attackers.”
Translating Strategy Into Operational Priorities
Strategic vision alone does not secure networks. Implementation requires difficult choices about where resources should be concentrated and which systems demand the highest protection.
Matthew Hartman, Chief Strategy Officer at Merlin Group, argues that the strategy represents an important step toward aligning federal cyber policy with the complexity of modern threats.
“The National Cyber Strategy represents an important step in aligning federal cyber policy with the scale and complexity of today’s threats,” Hartman said.
However, the most difficult phase begins after the strategy is published.
“The hard work begins now, and that’s translating the vision into ambitious yet achievable operational outcomes.”
Cyber defense resources are finite, and not every system can receive the same level of protection. Hartman emphasizes the need for consequence-based prioritization, focusing attention on infrastructure whose disruption would have the greatest national impact.
“Consequence-based prioritization will be essential to ensure finite federal and private-sector resources are focused on the systems where disruption would have the greatest national impact.”
The strategy also presents an opportunity to clarify how responsibility for cyber resilience is divided between government and industry.
“If implemented effectively, the strategy can help drive coordinated action across government and strengthen resilience across the infrastructure that underpins the U.S. economy and national security.”
Cyber Deterrence and the Shift Toward Proactive Defense
Another major theme within the strategy is the move toward more proactive forms of cyber defense. For many security professionals, this shift reflects the growing recognition that traditional reactive security models are insufficient against advanced threats.
Kevin Greene, Chief Cybersecurity Technologist for the public sector at BeyondTrust, believes the strategy will require an evolution in how security architectures are implemented across federal systems.
“The new cyber strategy from the White House will necessitate a Zero Trust 2.0 approach that builds upon its foundational principles while incorporating deterrence and disruption concepts,” Greene said.
Historically, cybersecurity programs have focused heavily on detection and response after attackers have already gained access to systems. Greene argues that the approach allows adversaries to maintain strategic initiative.
“Our cybersecurity posture has been reactive which has enabled our adversaries with the ability to preposition and gain meaningful control.”
Under a Zero Trust 2.0 model, defensive architecture becomes part of a broader cyber deterrence framework designed to constrain adversary operations before they can escalate.
“Zero Trust must evolve to become the core engine for cyber deterrence.”
Technology Modernization Across Federal Cyber Infrastructure
The strategy also emphasizes the modernization of federal cybersecurity capabilities through emerging technologies.
Bruce Jenkins, Chief Information Security Officer at Black Duck, notes that the strategy places a stronger emphasis on operational effectiveness than on compliance-driven security frameworks.
“President Trump’s Cyber Strategy for America puts operational effect ahead of compliance theater,” Jenkins said.
The document highlights several technology priorities, including Zero Trust architectures, post-quantum cryptography, and artificial intelligence-enabled cybersecurity platforms.
“From a practitioner’s perspective, the emphasis on modernizing federal systems with zero trust, post quantum cryptography, and AI enabled defense—while streamlining duplicative regulation—is directionally appropriate.”
Yet modernization programs within government environments have historically faced procurement and integration challenges.
“The real test will be in execution,” Jenkins said. “Translating these pillars into clear requirements, faster procurement, and measurable risk reduction across government and the defense industrial base.”
The Implementation Gap
Despite broad support for the direction of the strategy, cybersecurity leaders consistently return to one challenge. Speed.
Dave Gerry argues that the fundamental gap between attackers and defenders lies not in strategy but in operational tempo.
“Today, the biggest gap in the U.S. government’s approach to disrupting global cybercrime operations is speed,” Gerry said.
“Adversaries today are operating at machine speed and the Government is operating at bureaucracy speed.”
Much of federal cybersecurity policy remains focused on compliance frameworks and post-incident response rather than proactive vulnerability discovery.
“The majority of federal cybersecurity policy is based on compliance frameworks and post-breach policy instead of proactive vulnerability discovery to avoid the issue before it happens.”
Until governments close that gap, attackers will continue to exploit the asymmetry.
The Real Test for the Strategy
The 2026 Cyber Strategy for America reflects an evolving understanding of cybersecurity as a strategic competition involving governments, industries, and technologically sophisticated adversaries.
It expands the scope of federal cyber defense, emphasizes modernization through advanced technologies, and signals stronger collaboration between government and private infrastructure operators.
However, strategy alone rarely determines outcomes.
Implementation will.
Execution speed, operational coordination across agencies, and the ability to deploy advanced cybersecurity capabilities across both federal and commercial infrastructure will ultimately determine whether the strategy strengthens U.S. cyber resilience or remains largely aspirational.
Cyber conflict is accelerating. Policy will have to move faster if it hopes to keep pace.
FAQs
1. What is the purpose of the 2026 Cyber Strategy for America?
The strategy outlines how the U.S. government plans to strengthen national cyber defense by combining deterrence, infrastructure protection, technological leadership, and public–private collaboration to counter evolving cyber threats.
2. How does the strategy change the role of government in cybersecurity?
The framework signals a more active federal role in defending national cyber interests, including closer coordination with private infrastructure operators and greater use of offensive and defensive cyber capabilities to deter adversaries.
3. Why is critical infrastructure central to the U.S. cyber strategy?
Most U.S. critical infrastructure systems are privately operated, making collaboration between government agencies and industry essential to protect sectors such as energy, telecommunications, healthcare, and finance from cyber disruption.
4. What technologies are prioritized in the new U.S. cyber strategy?
The strategy highlights artificial intelligence, zero-trust architecture, post-quantum cryptography, and secure supply chains as foundational technologies for strengthening national cyber resilience and maintaining technological leadership.
5. What challenges could affect the implementation of the cyber strategy?
Execution will depend on faster government procurement, clearer regulatory alignment, stronger public-private cooperation, and addressing the ongoing shortage of skilled cybersecurity professionals.
Discover expert analysis and real-world CyberTech strategies at CyberTechnology Insights.
To participate in upcoming interviews, please reach out to our CyberTech Media Room at info@intentamplify.com.
🔒 Login or Register to continue reading












