With cybercrime expected to cost the world economy more than $10.5 trillion every year. Millions of users access these networks daily.
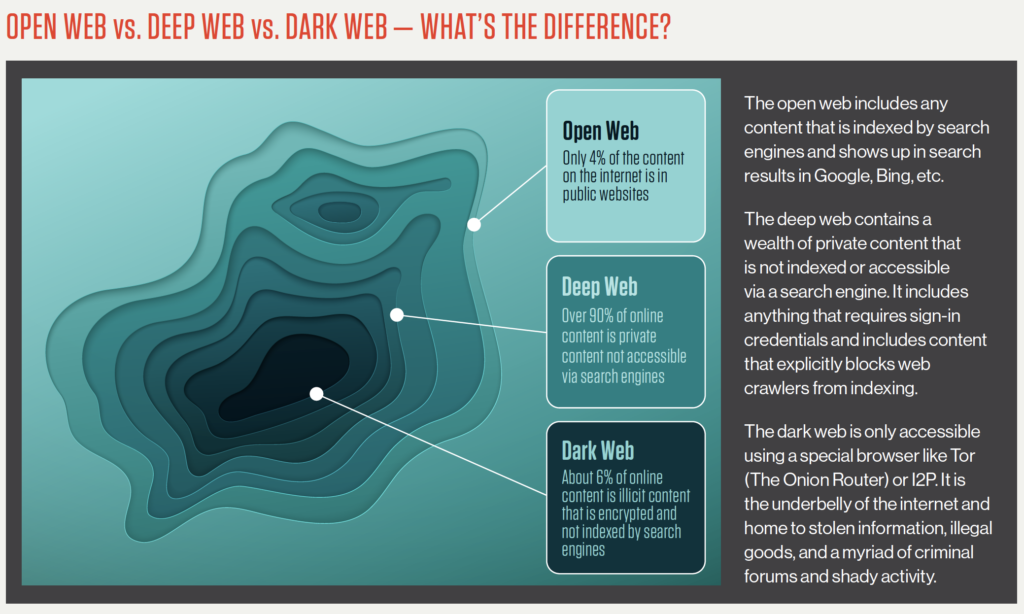
The Cisco Security Intelligence Operations (SIO) estimates that more than 80% of the Web is “dark,” or uncategorized by legacy URL-filtering databases. Cisco refers to this as the Dark Web.
The dark web allows use of encrypted networks and anonymous browsing, which makes it nearly impossible to monitor activity and take any intervention measures after it commences.
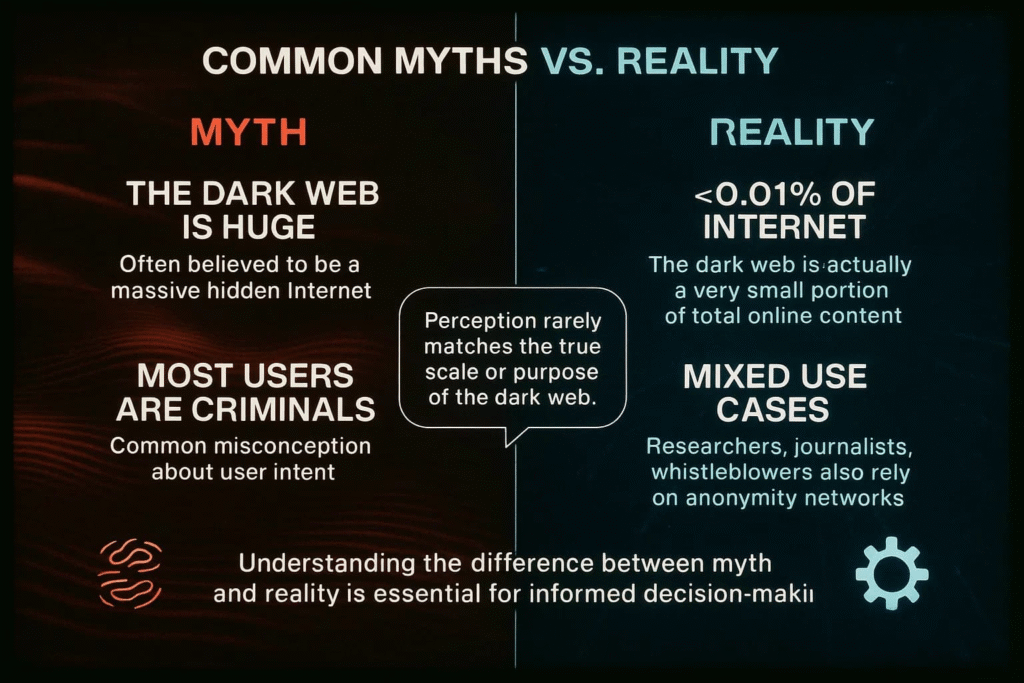
What Security Leaders Often Get Wrong About the Dark Web
Despite growing awareness, the dark web is still widely misunderstood at the leadership level. Misconceptions around anonymity, scale, and impact often lead to gaps in risk assessment and security strategy.
1. Anonymity is Not Absolute
The dark web enables strong privacy, but it is not impenetrable. Operational mistakes and advanced investigation techniques regularly expose threat actors, making it a monitored, but visible environment.
2. A Structured, Ongoing Threat Environment
Illicit activity dominates, but the ecosystem is structured and persistent. It operates alongside limited legitimate use cases, reinforcing its role as a stable, long-term risk layer.
3. Risk is Not Limited to Large Enterprises
Any exposed credential or data set can be monetized. Attackers frequently target smaller organizations, vendors, and employees as entry points into larger ecosystems.
Source: Deepstrike
The Dark Web is the Engine Behind Modern Cybercrime
The dark web sits outside your control but directly impacts your exposure. It is where access to your systems can be traded without your awareness.
It is an active marketplace where cybercrime is coordinated, optimized, and scaled.
What Powers This Ecosystem
Cybercriminals buy and sell:
- Stolen credentials and enterprise access
- Initial access to corporate networks
- Malware, exploits, and ransomware kits (RaaS)
- Phishing kits and attack infrastructure
- Financial data and personally identifiable information (PII)
- Session cookies and authentication tokens
- Botnets and DDoS-for-hire services
- Insider data and breach databases
- Deepfake and social engineering tools
- Bulletproof hosting and crypto laundering services
Entire attack chains are assembled through these transactions, enabling attackers to move from access to execution with speed and efficiency.
Industries Most Affected
Cybercriminals focus where the payoff is fastest. Data-rich, access-heavy, and operationally critical sectors consistently attract the highest level of attack activity.
The most impacted sectors are:
Technology and SaaS
High-value credentials, APIs, and cloud access make them prime targets.
Financial Services
Direct monetization through fraud, account takeover, and transaction manipulation.
Healthcare
Sensitive patient data and operational urgency increase ransom success rates.
Retail and E-commerce
Payment data, customer identities, and high transaction volumes.
Manufacturing and Critical Infrastructure
Vulnerable OT environments and high downtime costs.
Professional Services and Vendors
Often targeted as entry points into larger enterprises.
Dark Web Intelligence Is Becoming Essential
As the cybercrime marketplace grows, so does the value of dark web intelligence.
Organizations are increasingly using it to:
- Detect leaked credentials before they are exploited
- Monitor threat actor discussions about their brand
- Identify emerging attack patterns and tools
- Track ransomware group activity
Source: CrowdStrike
This represents a shift from reactive security to proactive threat intelligence. Instead of waiting for an attack to happen, organizations can identify signals early and act before damage occurs.
In many cases, the first indication of a potential breach is not inside your network. It is on the dark web.
Make Threat Intelligence a Strategic Advantage
FAQs
1. What is the cybercrime market on the dark web?
The cybercrime market on the dark web is a structured ecosystem where threat actors buy and sell data, access, and attack tools. It operates like a digital marketplace, enabling attackers to scale operations without building capabilities from scratch.
2. Why is dark web intelligence critical for enterprise security?
Dark web intelligence provides early visibility into leaked credentials, planned attacks, and threat actor activity. This allows organizations to act proactively, reducing the risk of breaches before they impact operations.
3. How are modern cyberattacks leveraging the dark web?
Attackers use the dark web to purchase stolen credentials, ransomware kits, and exploit tools. This reduces the time needed to launch attacks and increases success rates through pre-built, proven methods.
4. Why are identity-based attacks increasing in the U.S. enterprise landscape?
Identity-based attacks are rising because stolen credentials are widely available and easier to exploit than traditional vulnerabilities. With remote work and cloud adoption, identity has become the most accessible entry point for attackers.
5. How can organizations reduce risk from dark web threats?
Organizations can reduce risk by implementing continuous dark web monitoring, strengthening identity security, and adopting AI-driven threat intelligence to detect and respond to risks in real time.
To participate in upcoming interviews, please reach out to our CyberTech Media Room at info@intentamplify.com.
🔒 Login or Register to continue reading












