If Tony Stark were building an enterprise today, he would not struggle with innovation.
He would definitely struggle with control. The modern enterprise looks a lot like Stark’s lab. Always evolving, connected, and constantly integrating new systems, tools, and devices in real time.
The difference is that in today’s environment, every connected endpoint is not just a capability. It is a potential entry point. Unlike fiction, adversaries do not need genius-level tech to exploit it. They just need access.
What Is Endpoint Security Architecture?
Endpoint security architecture is the structured design of controls, policies, and technologies used to secure all endpoint devices across an enterprise environment.
It goes beyond individual tools like EDR or antivirus. Instead, it defines how endpoints are governed across identity, access, execution, and communication layers.
In modern enterprises, endpoints include laptops, servers, mobile devices, virtual machines, and cloud workloads. Each of these interacts with critical systems, data, and users.
This makes them one of the most exposed and frequently targeted layers in cybersecurity.
A well-defined endpoint security architecture ensures that every endpoint operates within controlled boundaries. It enforces who can access what, what can execute, how systems communicate, and how threats are detected and contained.

Why Endpoint Security Architecture Is a Strategic Priority Now
Endpoint security is no longer a tactical control. It is a primary determinant of enterprise risk exposure.
As organizations expand across hybrid environments, endpoints have become the most active interface between users, applications, and critical systems.
They are where identities are validated, data is accessed, and workloads are executed. This makes them the most consistent entry point for attackers.
Industry data reinforces this reality. According to Verizon’s Data Breach Investigations Report, endpoints play a central role in the majority of initial access scenarios, particularly through phishing, credential compromise, and malware delivery.
At the same time, the nature of attacks is evolving. Adversaries are increasingly leveraging fileless techniques, living-off-the-land binaries, and credential abuse to operate within trusted environments.
This allows them to bypass traditional signature-based defenses and remain undetected for longer periods. This shift exposes a structural gap.
Most organizations have strong visibility into endpoint activity. Visibility alone does not prevent compromise. It does not stop unauthorized execution. It does not enforce control over how endpoints behave once accessed.
This is why endpoint security architecture is moving into strategic focus.
A Practical Benchmark
How Mature Is Your Endpoint Security Architecture
Most organizations assess endpoint security maturity based on tool deployment.
But maturity is not defined by how many solutions are in place. It is defined by how effectively those controls reduce exposure across the endpoint lifecycle.
In many environments, endpoint security remains reactive. Systems are monitored, alerts are generated, and response workflows are triggered after suspicious activity is detected.
While this improves visibility, it does not eliminate the conditions that allow compromise to occur.
A more mature architecture shifts the focus toward control and enforceability.
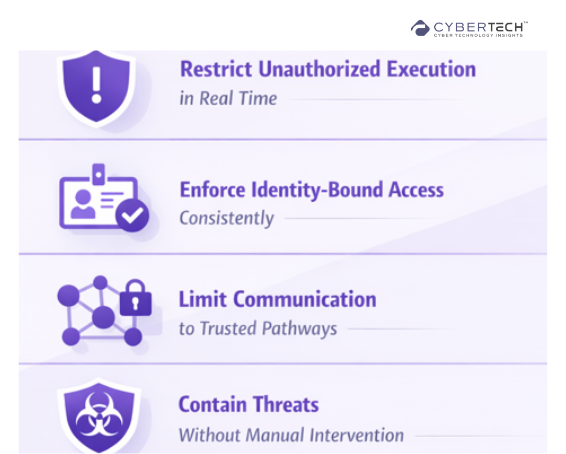
It evaluates whether endpoints can:
- Restrict unauthorized execution in real time.
- Enforce identity-bound access consistently.
- Limit communication to trusted pathways.
- Contain threats without reliance on manual intervention.
If these controls depend on detection timing or analyst response, the architecture remains vulnerable to fast-moving attacks.
If they are enforced at the system level, the architecture becomes inherently more resilient.
Where Endpoint Security Architecture Delivers Measurable Risk Reduction
Endpoint security architecture creates impact where control directly reduces exploitability.
In most enterprise environments, endpoints remain inherently reachable and highly interactive. They execute code, handle credentials, and communicate across multiple systems. This makes them ideal targets for initial access and attack propagation.
A well-defined architecture changes this dynamic.
By enforcing execution control, identity validation, and communication boundaries at the endpoint level, it reduces the conditions required for compromise. Instead of relying solely on detection, it limits what an attacker can do even if access is gained.
This has a direct effect on risk across three critical areas.
First, it lowers the probability of initial compromise by restricting unauthorized execution and enforcing least-privilege access.
Second, it constrains lateral movement by limiting how endpoints communicate within the environment.
Third, it improves containment by enabling rapid isolation without dependence on manual intervention.
The result is not just better visibility, but reduced attacker opportunity. For CIOs, this is the distinction that matters.
Security investments often increase monitoring capability. Endpoint security architecture, when designed correctly, reduces the likelihood and impact of attacks at the source.
Conclusion
Security operations can no longer function as a fragmented set of tools reacting to alerts. The scale, speed, and sophistication of modern threats demand a more unified and execution-driven approach.
Security Operations Platforms represent that shift. They move organizations from isolated detection capabilities to integrated, real-time security execution.
By bringing together visibility, intelligence, and response within a single operational layer, they reduce complexity while improving the speed and precision of decision-making.
For enterprise leaders, the value is not just operational efficiency. It is measurable risk reduction. When detection, analysis, and response are tightly aligned, organizations can contain threats faster, limit exposure, and maintain business continuity with greater confidence.
Ultimately, the effectiveness of security operations will not be defined by how much data is collected. It will be defined by how effectively that data is translated into action.
FAQs
1. What is a Security Operations Platform, and why does it matter?
A Security Operations Platform is an integrated system that centralizes threat detection, investigation, and response. It matters because it reduces operational silos and enables faster, coordinated action across security teams.
2. How is a Security Operations Platform different from SIEM or SOAR?
SIEM focuses on log aggregation and detection, while SOAR emphasizes automation and response workflows. A Security Operations Platform unifies both, combining visibility, intelligence, and execution in a single operational layer.
3. What core functions define an effective Security Operations Platform?
Key functions include continuous monitoring, threat detection, automated response, incident management, and intelligence correlation. These capabilities ensure faster detection and reduced response times across environments.
4. How do Security Operations Platforms improve incident response time?
They streamline workflows by automating repetitive tasks, correlating alerts in real time, and enabling faster decision-making. This reduces the time between detection and containment significantly.
5. What should enterprises evaluate before adopting a Security Operations Platform?
Decision-makers should assess integration capabilities, scalability, automation maturity, and how well the platform aligns with their existing security architecture and risk priorities.
To participate in upcoming interviews, please reach out to our CyberTech Media Room at info@intentamplify.com.
🔒 Login or Register to continue reading












