In 2025, a top-tier U.S. financial institution initiated a post-quantum security risk assessment following mounting signals from industry research and threat intelligence.
What began as a forward-looking innovation exercise quickly escalated into a material business risk discussion.
This case study examines how one enterprise translated these signals into action, what they uncovered, and what changed operationally.
Converging Signals from Research and Threat Intelligence
Independent research and real-world threat intelligence are beginning to converge, signaling a rapid shift in the risk landscape.
According to McKinsey & Company, quantum computing is advancing faster than expected, with enterprise-relevant capabilities projected within this decade and cybersecurity identified as one of the most immediately disrupted domains.
At the same time, Gartner has explicitly warned that organizations must begin preparing now due to the long lead time required to transition cryptographic systems.
For executive teams, these signals are early indicators, demanding immediate strategic alignment.
1. Quantum Timelines Are Compressing
Recent research indicates that encryption-breaking quantum systems may require significantly fewer resources than previously estimated, accelerating timelines toward practical risk.
Rapid improvements in algorithms, error correction, and system design are consistently shrinking the gap between current quantum capabilities and real-world cryptographic risk, signaling that organizations must treat quantum security as an immediate priority rather than a distant concern.
Additionally, projections suggest a non-trivial probability of “Q-Day” before 2032.
According to the Quantum Insider: “Bitcoin’s average block time is ten minutes. Under idealized conditions, Google estimates a roughly 41% probability that a primed quantum computer could derive a private key before a Bitcoin transaction is confirmed.”
Assess Your Quantum Exposure Today
Get a rapid snapshot of your cryptographic risk posture before timelines compress further.
Request Your Post-Quantum Risk Assessment
2. Market and Investment Momentum Is Surging
- Quantum technology investment grew nearly 50% year-over-year, signaling rapid ecosystem acceleration.
- The broader quantum market is projected to reach $72B+ in computing alone by 2035.
This is no longer experimental. It is industrializing.
3. Post-Quantum Cryptography Is Becoming a Strategic Priority
Gartner has identified post-quantum cryptography as a critical future-proofing capability, particularly for identity and authentication systems.
Case Study
Accelerating Post-Quantum Readiness in a Global Financial Services Enterprise
Organization Profile
- Industry: Financial Services (Banking & Capital Markets).
- Region: United States, global operations.
- Size: ~$18B annual revenue, 45,000+ employees.
- Environment: Hybrid infrastructure spanning multi-cloud, on-prem data centers, and identity-driven access systems.
The Challenge
By early 2025, the organization identified a growing exposure to quantum-era risks, driven by:
- Fragmented visibility into cryptographic assets across environments.
- Legacy systems tightly coupled with static encryption methods.
- Increasing regulatory pressure aligned with NIST post-quantum standards.
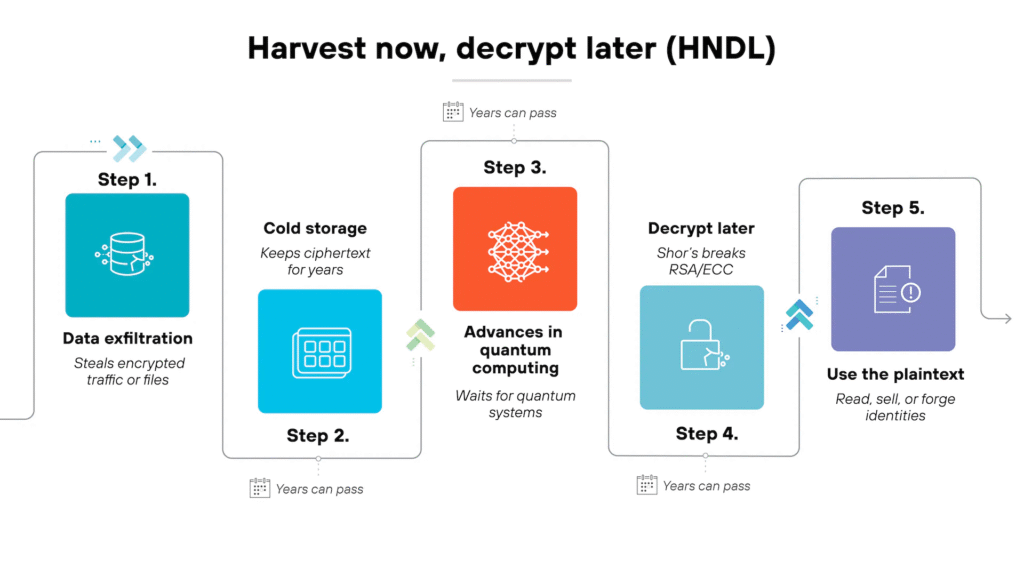
- Rising concern around “harvest now, decrypt later” attack models.
Recognize These Gaps in Your Environment?
Uncover hidden cryptographic exposures across cloud, identity, and legacy systems.
Get a Cryptographic Visibility Audit
Internal assessment revealed:
- Less than 40% visibility into cryptographic usage.
- Exposure windows lasting weeks due to manual validation cycles.
- No clear roadmap for crypto-agility or quantum transition.
The Strategy: Enterprise-Wide Transformation
The organization launched a 12-month transformation program (Q2 2025 to Q2 2026) built on four strategic pillars:
1. Cryptographic Visibility at Scale
Actions
- Implemented real-time discovery across cloud, on-prem, and identity systems.
- Mapped encryption usage to data sensitivity and business criticality.
Before
- Fragmented visibility across siloed environments.
- Limited understanding of high-risk cryptographic exposure.
After
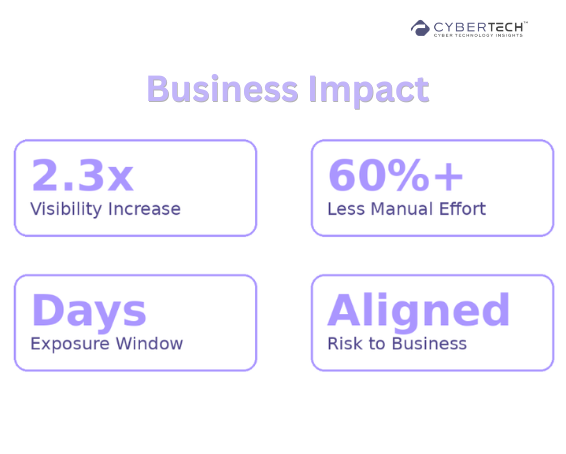
- >92% coverage of cryptographic assets.
- Real-time visibility into high-risk exposure paths.
2. Crypto-Agility Engineering
Aligned with guidance from Gartner on long transition cycles.
Actions
- Decoupled encryption logic from core applications.
- Introduced algorithm abstraction layers.
- Standardized key lifecycle management across environments.
Before
- Heavy reliance on hardcoded, legacy encryption implementations.
- High risk of operational disruption during upgrades.
After
- 70% reduction in dependency on static cryptography.
- Ability to test and deploy new algorithms without system downtime.
Build Crypto-Agility Without Disruption
See how leading enterprises decouple encryption from applications at scale.
Explore a Crypto-Agility Strategy Session
3. Automation of Detection and Remediation
Actions
- Automated identification of weak or deprecated cryptographic protocols.
- Prioritized remediation based on exploitability and business impact.
Before
- Manual validation workflows consuming significant analyst time.
- Exposure windows extending from 2–3 weeks.
After
- 60% reduction in manual validation effort.
- Exposure windows reduced to 48–72 hours.
Reduce Exposure Windows from Weeks to Hours
Automate detection and remediation of cryptographic risks across environments.
See Automated Risk Prioritization in Action
4. Governance and Regulatory Alignment
Actions
- Integrated quantum risk into enterprise risk dashboards.
- Aligned roadmap with NIST post-quantum cryptography standards.
- Established a phased migration plan through 2030.
Before
- Quantum risk treated as a long-term R&D concern.
- Limited board-level visibility.
After
- Real-time reporting of quantum-related risk exposure.
- Security metrics translated into financial and operational impact.
Business Impact
Within 12 months, the organization achieved measurable improvements, including a 2.3x increase in cryptographic visibility and a 60% reduction in manual effort, based on internal program benchmarks aligned with industry trends from IBM, Verizon DBIR, and NIST.
Quantify Your Quantum Risk Reduction
Understand the financial and operational impact of improving cryptographic visibility.
Download the Executive Risk Report
Key Takeaway
Post-quantum readiness is not a one-time upgrade; it is a structural transformation.
Organizations that treat it as an enterprise-wide initiative across visibility, architecture, automation, and governance will move faster.
They would also reduce long-term risk, and gain a strategic advantage in a rapidly shifting threat landscape.
Vendor Landscape: What Was Evaluated
| Vendor / Category | Core Capability | Automation Level | Integration Maturity | Licensing Model | Strengths and Gaps |
| Traditional PKI Vendors | Certificate lifecycle management | Low | Moderate | License-based | Strong trust foundation. Weak agility |
| Cloud Providers | Native encryption services | Moderate | High (cloud) | Consumption-based | Scalable. Limited hybrid visibility |
| Post-Quantum Vendors | PQC algorithms | Low | Emerging | Subscription | Future-ready crypto. Limited integration |
| SIEM Platforms | Monitoring | Moderate | High | Data-based | Visibility strong. Actionability limited |
| SOAR Platforms | Automation workflows | High | High | Workflow-based | Strong automation. Dependent on inputs |
| Data Security Platforms | Data classification | Moderate | Moderate | Asset-based | Good data context. Limited crypto control |
| How Our Platform Fits | Continuous asset-drift-driven risk scoring across hybrid environments | High | High (SIEM, SOAR, IAM) | Asset + risk-based | Differentiated by real-time visibility, precision prioritization, and automated remediation |
Compare Your Current Stack Against PQC Readiness
Identify gaps across PKI, SIEM, SOAR, and emerging post-quantum solutions.
Get a Personalized Vendor Fit Analysis
Leadership Playbook
1. Diagnose Immediate Exposure
- Identify long-lived sensitive data.
- Map cryptographic dependencies.
- Assess the ability to rotate algorithms.
2. Prioritize Investments
Immediate
- Cryptographic inventory.
- Automation of detection.
- Protection of high-retention data.
Next
- Crypto-agility architecture.
- PQC pilot programs.
- Regulatory alignment.
3. Ask the Right Questions
- How fast can we transition cryptography at scale?
- What percentage of remediation is automated?
- Can we quantify the reduction in exposure windows?
- How do we prioritize risk based on business impact?
The Shift to Post-Quantum Readiness Has Already Begun
Post-quantum risk is no longer theoretical; it is a timing problem. The organizations that win will not be the ones that react to “Q-Day,” but the ones that build adaptability into their systems before it arrives.
Source: Palo Alto Networks
The first fault line is visibility. Most enterprises still lack a clear understanding of where cryptography exists across their environments, leaving critical exposures hidden in plain sight.
The second is architectural rigidity. Legacy systems hardwired to today’s encryption standards will struggle to transition, turning future upgrades into operational disruption.
The third is execution at scale. Without automation, the effort required to identify, prioritize, and remediate cryptographic risk will exceed what security teams can realistically manage.
Finally, governance will define outcomes. Organizations that can translate quantum risk into business impact will move faster, secure executive alignment, and make better investment decisions.
Closing Insight
This case reflects a broader reality. The quantum threat is not defined by when encryption breaks. It is defined by how long it takes organizations to adapt.
According to both McKinsey & Company and Gartner, that adaptation window is already shrinking.
The organizations that move now are not early adopters. They are simply avoiding being late.
Don’t Wait for Q-Day to Expose the Gaps
Start building quantum-resilient security before adaptation becomes a crisis.
Start Your Post-Quantum Readiness Journey
FAQs
1. What is post-quantum cryptography, and why does it matter for enterprises?
Post-quantum cryptography refers to encryption methods designed to resist attacks from quantum computers. It matters because current encryption standards could be broken in the future, exposing sensitive data and long-term intellectual property.
2. When should organizations start preparing for quantum-related cybersecurity risks?
Preparation should begin now. The risk is not just future decryption; attackers are already harvesting encrypted data today with the intent to decrypt it once quantum capabilities mature.
3. What are the biggest challenges in transitioning to post-quantum security?
The main challenges include a lack of visibility into cryptographic assets, legacy systems that are not crypto-agile, and the operational complexity of updating encryption at scale without disrupting business systems.
4. How can CISOs align post-quantum strategy with business priorities?
By mapping cryptographic risk to critical business systems and revenue streams. This allows leaders to prioritize protection efforts based on potential financial and operational impact rather than technical severity alone.
5. What should organizations prioritize first in their post-quantum readiness roadmap?
Start with cryptographic discovery and inventory, followed by assessing exposure risk and enabling crypto-agility. Early focus on visibility and architecture reduces long-term migration complexity and cost.
To participate in upcoming interviews, please reach out to our CyberTech Media Room at info@intentamplify.com
🔒 Login or Register to continue reading