Cybersecurity has crossed a critical threshold. It is no longer confined to enterprise risk management. It is now embedded in national institutional priorities.
A defining signal came when the U.S. Supreme Court requested a $254 million increase for security and cyber protection, as reported by Reuters. This reflects a broader shift across government and critical infrastructure.
Inside enterprise environments, the same transformation is visible. Across 2,300+ environments monitored by our platform in 2025–26, exposure windows are shrinking, identity is dominating attack paths, and operational inefficiencies are becoming the primary driver of breach risk.
This article reframes the conversation as a comparison problem. Not what tools you have, but how your current security model compares to what the threat landscape now demands.
The Core Shift: Two Competing Security Models
Before diving into specific capabilities, it is critical to understand that most organizations are not failing due to lack of investment. They are operating within an outdated model.
The following comparison highlights the structural differences between legacy security operations and what institutional-grade resilience now requires.
| Dimension | Traditional Security Model | Institutional-Grade Model |
| Primary Focus | Vulnerability counts | Business risk exposure |
| Visibility | Periodic scans | Continuous, real-time discovery |
| Risk Prioritization | CVSS-based | Exploitability + attack path-based |
| Identity Security | IAM as control function | Identity as primary attack surface |
| Response Model | Analyst-driven | Automation-driven |
| Time to Remediate | Days to weeks | Hours to prioritized containment |
| Board Reporting | Activity metrics | Risk reduction and financial impact |
| Operating Assumption | Breach is preventable with coverage | Breach risk is managed through speed and precision |
What This Means for CISOs
The gap between these two models is where most enterprise risk now lives. Organizations still operating in the traditional model are not under-invested. They are misaligned with how attacks actually unfold.
Comparison 1: Visibility
Asset Inventory vs. Real-Time Exposure Awareness
Most enterprises believe they have visibility because they maintain asset inventories and run regular scans. The reality is that modern environments change too quickly for periodic visibility models.
Cloud workloads spin up and down, identities are dynamically provisioned, and shadow assets emerge continuously. Visibility today must reflect what exists right now, not what existed during the last scan.
| Capability | Legacy Approach | Modern Requirement |
| Asset Discovery | Periodic, scan-based | Continuous, drift-aware |
| Coverage | Known assets | Known + unknown + transient assets |
| Context | Isolated systems | Connected asset relationships |
| Internet Exposure | Delayed identification | Real-time detection |
Platform-Driven Insight
Across our telemetry:
- 23% of enterprise assets are unmanaged or transient.
- These assets are 3.2x more likely to be part of an active attack path.
Conclusion: If visibility is not continuous, it is incomplete. If it is incomplete, it is unreliable.
Comparison 2: Risk Prioritization
Severity Scores vs. Exploitability
Security teams are overwhelmed not because there are too many vulnerabilities, but because prioritization models are flawed.
Traditional scoring systems treat all “critical” vulnerabilities as equal, even though attackers exploit only a small fraction of them.
Modern prioritization must reflect how attacks actually propagate, not how risks are theoretically scored.
| Capability | Legacy Approach | Modern Requirement |
| Risk Metric | CVSS severity | Exploitability + reachability |
| Prioritization | All critical vulnerabilities | Only actionable attack paths |
| Context | Static scoring | Dynamic, environment-aware |
| Outcome | Alert overload | Focused remediation |
Platform-Driven Insight
- Only 9% of vulnerabilities are ever exploited.
- Despite this, most remediation effort is still spent on low-risk vulnerabilities due to lack of exploitability context.
Conclusion: The problem is not too many vulnerabilities. It is misplaced attention.
Comparison 3: Identity Security
Access Control vs. Attack Surface
Identity systems were originally designed for access management and compliance. That model no longer holds. In modern environments, identity is deeply interconnected with infrastructure, cloud services, and third-party integrations.
Attackers exploit these connections to move laterally and escalate privileges. Identity must now be treated as a primary attack surface, not just an administrative function.
| Capability | Legacy Approach | Modern Requirement |
| Identity Role | Authentication layer | Primary attack vector |
| Risk Treatment | Governance issue | Critical exposure domain |
| Visibility | User-level | Cross-environment identity mapping |
| Threat Model | Insider risk | External exploitation via identity |
Platform-Driven Insight
- 68%+ of attack paths involve identity weaknesses
- Environments with poor identity hygiene show 2.5x higher breach probability
Conclusion: Identity is no longer IAM hygiene. It is the control plane of modern attacks.
Comparison 4: Speed of Operations
Human-Led vs. Machine-Speed Security
The economics of cyber defense have changed. Attackers operate at machine speed, leveraging automation to scan, exploit, and move laterally within hours.
Most enterprise security teams, however, still rely heavily on manual validation, ticketing systems, and fragmented workflows. This mismatch creates a persistent exposure window.
| Capability | Legacy Approach | Modern Requirement |
| Validation | Manual | Automated |
| Remediation | Ticket-driven | Workflow-driven |
| False Positives | High | Reduced through context |
| Response Time | 5–7 days | <48 hours aligned to exploit window |
Platform-Driven Insight
- Mean-time-to-exploit: <48 hours.
- Median enterprise remediation: 5–7 days.
Conclusion: The gap between attacker speed and defender response is the breach window.
Comparison 5: Governance
Compliance Reporting vs. Business Risk Translation
Cybersecurity reporting has traditionally been designed for auditors and compliance teams. That is no longer sufficient.
Boards and executive leadership require clarity on how cyber risk impacts revenue, operations, and regulatory exposure.
Governance models must evolve to communicate risk in business terms, not technical outputs.
| Capability | Legacy Approach | Modern Requirement |
| Reporting | Control coverage | Risk exposure |
| Audience | Security teams | Board and executive leadership |
| Metrics | Number of vulnerabilities | Reduction in exploitable risk |
| Compliance | Periodic audits | Continuous assurance |
Conclusion: If cyber risk cannot be translated into business impact, it cannot be governed effectively.
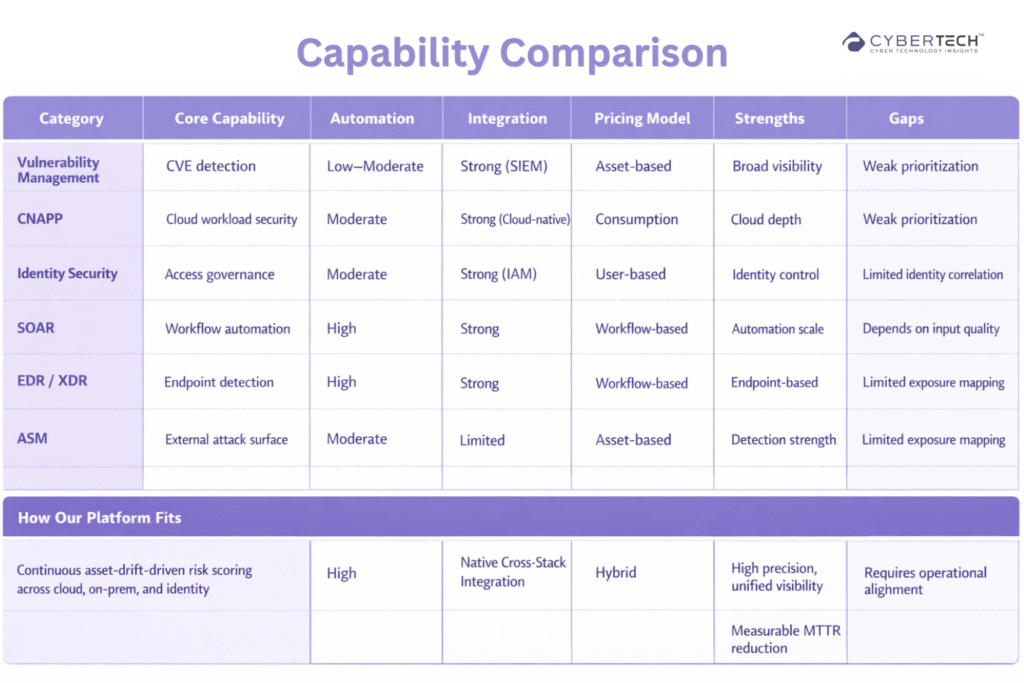
Vendor Landscape: Capability Comparison
The vendor ecosystem reflects the same fragmentation seen inside enterprises. Most tools solve a specific layer of the problem. Very few provide unified visibility, prioritization, and action across environments.
This comparison helps clarify where each category fits and where gaps remain.
Cost Comparison: Where Enterprises Actually Spend
Budget conversations often focus on licensing costs, but the real financial impact of cybersecurity lies in operational inefficiencies.
Manual processes, false positives, and delayed remediation significantly increase the total cost of ownership. This comparison highlights where traditional models incur hidden costs.
| Cost Factor | Traditional Model | Institutional Model |
| Tooling | High (fragmented) | Optimized (integrated) |
| Analyst Effort | High manual workload | Reduced via automation |
| False Positives | Significant overhead | Contextually minimized |
| Time to Remediate | Long cycles | Accelerated cycles |
| Breach Risk | Higher due to delays | Lower due to prioritization |
Key Insight
Organizations optimizing for tool cost often increase operational cost. Those optimizing for risk reduction speed lower total cost over time.
Executive Decision Framework
What Leaders Should Do Now vs. Next
Even with clarity on the right model, execution requires prioritization. Leaders must balance immediate risk reduction with longer-term transformation.
The following comparison outlines how to sequence decisions effectively.
Immediate (0–90 Days)
| Priority | Action |
| Visibility | Identify unmanaged and internet-facing assets |
| Risk | Focus on exploitable attack paths |
| Identity | Audit privileged access and federation risks |
| Speed | Automate validation for critical exposures |
Strategic (2–3 Quarters)
| Priority | Action |
| Operating Model | Shift from vulnerability-centric to risk-centric |
| Metrics | Report in business risk terms |
| Tooling | Consolidate fragmented security stack |
| Automation | Expand machine-driven remediation |
RFP Comparison: What Separates Vendors
Most vendor evaluations fail because they focus on features rather than outcomes. The right comparison is not what a tool does, but how it impacts risk reduction, speed, and operational efficiency.
| Question | Weak Answer | Strong Answer |
| Risk Prioritization | “We score vulnerabilities” | “We map exploitability and attack paths” |
| Coverage | “We scan assets” | “We continuously discover and correlate assets” |
| Identity Integration | “We integrate with IAM” | “We model identity as part of attack paths” |
| Automation | “We support workflows” | “We automate validation and remediation at scale” |
| Outcomes | “We provide visibility” | “We reduce MTTR and exploitable exposure” |
Final Perspective
Cybersecurity is no longer just an enterprise discipline. It is a national institutional priority shaping how governments allocate budgets, how regulators define accountability, and how boards evaluate leadership.
The most important comparison for CISOs is not between vendors. It is between operating models. One model measures activity. The other reduces risk.
FAQs
1. What does cybersecurity as a national priority mean for enterprises?
It means cyber risk is now tied to business continuity, regulatory accountability, and systemic resilience, requiring CISOs to operate at a board and institutional level.
2. Why are identity-based attacks the biggest risk today?
Attackers increasingly exploit credentials and privileges instead of vulnerabilities, making identity the primary entry point into enterprise systems.
3. How should CISOs prioritize cyber risk effectively?
By focusing on exploitable attack paths and business impact rather than treating all vulnerabilities as equally critical.
4. Why is automation critical in modern cybersecurity operations?
Attackers operate in hours while manual security processes take days, creating a gap that only automation can close.
5. What do boards expect from cybersecurity leaders in 2026?
They expect clear visibility into business risk, faster response to threats, and measurable reduction in real-world exposure.
To participate in upcoming interviews, please reach out to our CyberTech Media Room at info@intentamplify.com
🔒 Login or Register to continue reading