Cloud security platforms are becoming the operational center of enterprise security.
This is less about market evolution and more about structural necessity. Modern environments are distributed across multi-cloud, SaaS, containers, and AI-driven workloads, where risk no longer appears in isolation.
Most organizations already have visibility. What they lack is context.
A misconfiguration, an over-permissioned identity, and an exposed workload are often treated separately. In reality, they form a single attack path.
Cloud security platforms address this by acting as a unifying layer, connecting signals across infrastructure, identity, and data.
Market Signals: Why Platforms Are Becoming the Default
The shift toward cloud security platforms is not theoretical. It is already visible in how enterprises are consolidating security investments.
- Gartner projects that by 2027, over 50% of enterprises will adopt CNAPP solutions, up from low double digits today, as organizations consolidate fragmented cloud security tooling.
- Deloitte, in collaboration with Red Hat, highlights that multi-cloud adoption introduces significant interoperability and operational challenges, with security fragmentation emerging as a primary risk driver.
- McKinsey & Company estimates that cloud could generate up to $3 trillion in EBITDA value by 2030, but identifies security and complexity as leading barriers to value realization.
- McKinsey also highlights that cloud adoption, accelerated by COVID-19, builds on decades of evolution and now enables greater agility through modular, independently scalable application architectures.
There is a pattern here.
Cloud adoption scales faster than governance. Security teams respond by adding tools. Over time, those tools become the source of operational friction they were meant to reduce.
Cloud security platforms are, in many ways, a correction to that cycle.
Explore how leading enterprises are consolidating cloud security into unified platforms. See what this shift looks like in practice.
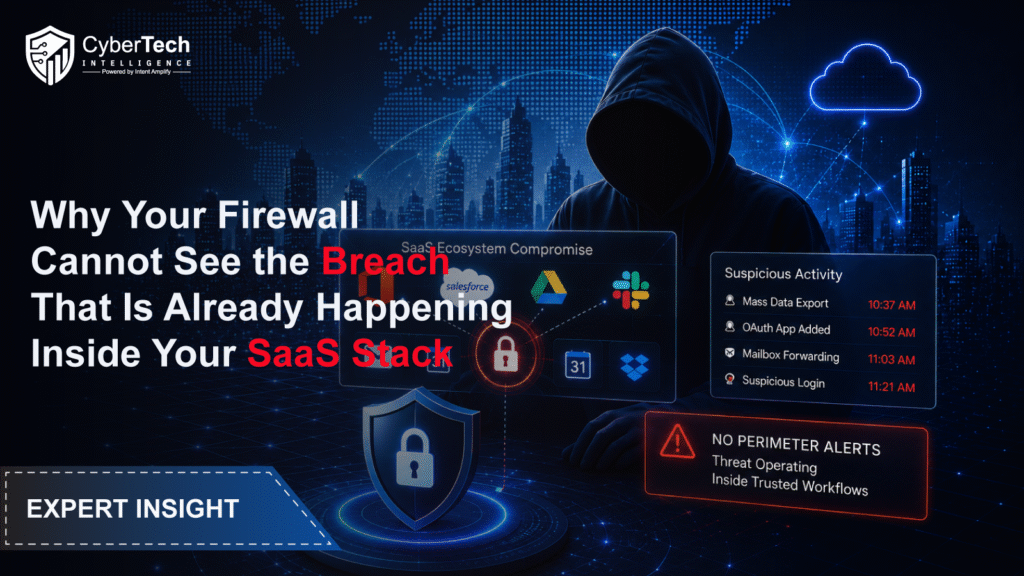
Signals Are Abundant, Context Is Not
Most enterprises already have visibility. Telemetry from cloud providers, endpoint tools, identity systems, network logs, and runtime signals. The issue is not collection. It is interpretation.

A misconfigured storage bucket might raise a signal. So might an over-permissioned identity or a vulnerable workload. On their own, they rarely demand immediate action. In combination, they create a clear path to exploitation.
Traditional tooling does not connect these dots in a way that reflects how attacks actually happen. It fragments risk into categories that are convenient for tools, not useful for decision-making.
How Cloud Security Platforms Map to Security Frameworks
Cloud security platforms translate static framework requirements into continuously enforced controls across dynamic environments. They bridge the gap between defined policies and real-world execution, where drift and misalignment are constant.
| Framework | What It Defines | Where Platforms Fit | What Changes in Practice |
| NIST CSF | Identify, Protect, Detect, Respond, Recover | Continuous monitoring across cloud assets, identities, and workloads | Moves from periodic assessment to continuous control validation |
| CSA CCM | Cloud-specific control requirements | Automated posture checks across configurations and services | Reduces manual compliance overhead, and exposes drift in real time |
| ISO 27001 | Governance and risk management standards | Policy enforcement and audit evidence generation | Shifts compliance from documentation-heavy to evidence-driven |
| MITRE ATT&CK (Cloud) | Adversary tactics and techniques | Detection mapping and behavior-based analytics | Improves threat context beyond static rule-based alerts |
| Zero Trust Architecture | Continuous verification, and least privilege | Identity-centric access analysis and enforcement (CIEM) | Translates principle into enforceable, measurable controls |
Assess how effectively your organization operationalizes NIST, ISO, and Zero Trust principles in dynamic cloud environments.
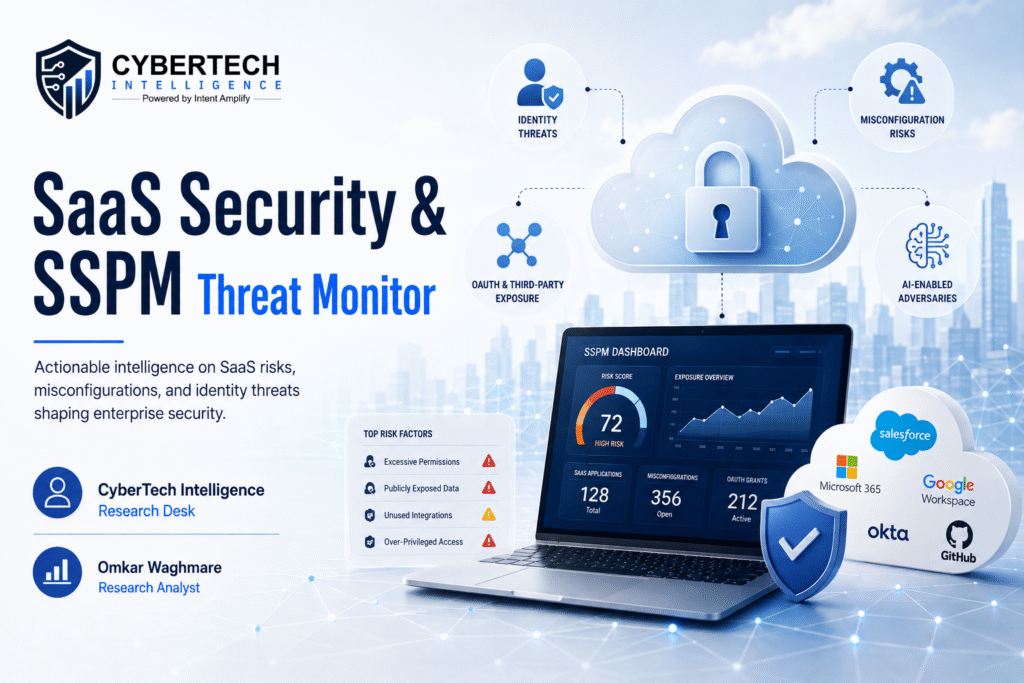
CNAPP Reflects Reality: Not Reinvention
The industry likes neat categories.
- Cloud Security Posture Management (CSPM)
- Cloud Workload Protection Platform (CWPP)
- Cloud Infrastructure Entitlement Management (CIEM)
- Data Security Posture Management (DSPM)
Each one justified at some point. Each one is still relevant in isolation.
A cloud-native application protection platform (CNAPP) reflects a broader shift. One where the industry moves beyond boundaries that were never aligned with how risk actually manifests.
In practice, no security team evaluates misconfigurations separately from identity exposure or runtime risk. They evaluate scenarios. What can be exploited, how easily, and what it leads to.
Vendors are converging because customers already have.
That said, the consolidation narrative is cleaner on paper than in deployment.
Most platforms still have uneven depth. Strong posture management, weaker identity analytics. Good visibility, limited response automation. Agentless convenience, but with trade-offs in runtime fidelity.
Identity Is Now the Real Attack Surface
There is a tendency to say identity is the new perimeter. That undersells it.
Identity is not just a boundary. It is the execution layer of cloud security.
Every meaningful cloud action is mediated through identity. API calls, service interactions, privilege escalations. Even misconfigurations are only dangerous when coupled with identity paths that can exploit them.
Most organizations still do not have a clear model of their effective permissions. Not assigned permissions. Effective ones. Inherited, chained, and often unintentionally granted.
Cloud security platforms attempt to map this. CIEM capabilities, graph-based analysis, and access path modeling.
Identity is contextual, time-bound, and increasingly automated. Any model that treats it as fixed will drift out of accuracy almost immediately.
If identity is your execution layer, visibility into effective permissions is non-negotiable. Evaluate your current identity risk model.
The Hidden Cost of Deeper Security
There is a quiet tension in how these platforms are designed.
Agentless approaches have gained traction for a reason. Fast deployment. Broad coverage. Minimal operational overhead. Especially attractive for organizations already fatigued by tooling complexity.
However, agentless visibility has limits. It infers runtime behavior rather than observing it directly. That is fine for posture and exposure analysis. Less reliable for detecting nuanced runtime threats.
Agent-based models provide deeper telemetry. Better runtime protection. More precise detection.
They also introduce friction. Deployment overhead. Performance considerations. Coordination with engineering teams who are not always aligned with security priorities.
Most enterprises end up in a hybrid state, whether intentionally or not.
This is not a temporary phase. It is a structural trade-off.
Multi-Cloud Complexity Is Manageable, Ownership Isn’t
Multi-cloud is often framed as a technical challenge. It is also an organizational one.
Different teams, different expertise, different operating models across AWS, Azure, GCP. Security policies drift not just because of technical gaps, but because ownership is unclear.
85% of organizations are using or planning to use multi-cloud, but face integration challenges and operational inefficiencies
Deloitte’s multi-cloud research reinforces the pattern. Adoption is high, but so are integration challenges and operational inefficiencies.
The issue is not access to multiple clouds. It is the lack of a unified operating model across them.
Cloud security platforms promise unification. A single view across environments.
In practice, they standardize visibility faster than they standardize accountability.
You can see the same misconfiguration across three clouds. Fixing it still depends on three different teams, priorities, and timelines.
AI in Cloud Security
There is a growing expectation that AI will solve alert fatigue, automate response, and even predict attacks.
Some of that is happening. Quietly.
AI is effective at pattern recognition across large telemetry sets. It helps surface anomalies that would otherwise go unnoticed. It can cluster related signals. Suggest prioritization.
What it does not do well is understand business context.
An anomalous API call may be malicious. It may also be a new deployment pattern. AI can flag it. It cannot reliably interpret intent without additional context.
So the real value is not autonomous security. It is an assisted analysis.
The organizations seeing results are not replacing analysts. They are augmenting them. Reducing cognitive load, not eliminating it.
Vendor Selection Is About Operating Model Alignment
Feature comparisons are becoming less relevant at the top end of the market. Most leading platforms cover the core domains.
The real differentiation is architectural philosophy.
| Dimension | Option 1 | Option 2 | Strategic Implication |
| Deployment Model | Agentless | Agent-based | Speed and ease vs. depth and runtime visibility |
| Architecture Alignment | Cloud-native | Hybrid-oriented | Optimized for modern workloads vs. broader legacy support |
| Capability Focus | Depth | Speed of deployment | Comprehensive coverage vs. faster time-to-value |
| Ecosystem Strategy | Integrated with existing stack | Platform-independent | Leverages current investments vs. flexibility across environments |
A Microsoft-centric organization will derive disproportionate value from Defender for Cloud. Not because it is objectively superior, but because identity, endpoint, and cloud signals already converge within that ecosystem.
A cloud-native company scaling rapidly may prioritize Wiz or Orca for speed and simplicity, accepting trade-offs in certain areas.
Large enterprises with complex requirements often gravitate toward platforms like Prisma Cloud, where breadth and integration outweigh ease of deployment.
There is no neutral choice. Every selection reinforces an operating model.
What Cloud Security Platforms Actually Change
Cloud security platforms do not eliminate misconfigurations. They do not fix broken processes or replace the need for skilled analysts.
A large enterprise using platforms like Prisma Cloud by Palo Alto Networks or Wiz, for example, does not just see thousands of isolated alerts across cloud accounts.
It sees how a publicly exposed workload, combined with excessive IAM permissions and access to sensitive data, forms a viable attack path.
Once risk is framed as a connected system rather than isolated findings, prioritization becomes more defensible. Conversations with the business become clearer. Trade-offs become explicit instead of implicit.
Beyond Tooling: This Is About How Security Functions
Cloud security platforms are often evaluated as products. That framing is incomplete.
They are an operational layer that sits between raw telemetry and decision-making. Their value is not in what they detect, but in how they construct meaning from fragmented signals.
Enterprises are not adopting these platforms because they are more feature-rich. They are adopting them because existing approaches do not scale with the speed and complexity of cloud environments.
The shift is already underway.
Security is moving from alert management to risk modeling. From isolated findings to attack path analysis. From visibility to context.
Organizations that continue to operate in fragmented models will accumulate signals faster than they can interpret them.
Those who invest in contextual, platform-driven approaches will not eliminate risk. They will understand it well enough to act decisively.
At scale, that difference becomes a competitive advantage.
FAQs
1. What is a cloud security platform, and how is it different from traditional tools?
A cloud security platform unifies posture management, identity governance, workload protection, and data security into a single control layer. Unlike traditional tools that operate in silos, it correlates risks across domains to provide contextual prioritization.
2. Why are enterprises consolidating into CNAPP-based security architectures?
Enterprises are consolidating to reduce tool sprawl and improve risk visibility. CNAPP platforms connect misconfigurations, identities, and runtime signals, enabling teams to prioritize exploitable risks instead of managing isolated alerts.
3. How do cloud security platforms improve risk prioritization?
They model relationships between assets, identities, and exposures to identify attack paths. This allows security teams to focus on risks that are both reachable and impactful, rather than responding to alert volume.
4. What are the key factors CISOs should evaluate when selecting a cloud security platform?
CISOs should assess architectural fit (agentless vs. agent-based), integration with existing ecosystems, depth of runtime protection, identity visibility, and the platform’s ability to correlate risk across environments.
5. Do cloud security platforms reduce operational complexity or add to it?
They reduce complexity at the visibility and analysis layer but may expose underlying organizational gaps. While platforms unify insights, remediation still depends on ownership, processes, and cross-team coordination.
To share your insights, please write to us at Info@intentamplify.com
🔒 Login or Register to continue reading