Mazda Motor Corporation has disclosed a cybersecurity incident involving unauthorized external access to an internal warehouse management system, potentially exposing 692 personal data records belonging to employees, group company staff, and business partners. The incident highlights growing cybersecurity risks within automotive supply chains and enterprise operational systems.
The breach was first detected internally in mid-December 2025, with the company issuing a formal public disclosure on March 19, 2026. According to Mazda, the compromised system was used to manage warehouse operations for automotive parts sourced from Thailand. An external threat actor exploited unpatched security vulnerabilities within the platform to gain unauthorized access.
Following the discovery, Mazda reported the incident to Japan’s Personal Information Protection Commission and initiated a comprehensive investigation in collaboration with an external cybersecurity firm. The delay in public disclosure aligns with regulatory requirements under Japan’s Act on the Protection of Personal Information (APPI), allowing time for forensic analysis and risk assessment.
The breach impacted a total of 692 records, with exposed data including company-issued user IDs, full names, corporate email addresses, company affiliations, and business partner identifiers. Importantly, Mazda confirmed that no customer personal data was stored in the affected system, significantly limiting broader consumer risk.
However, the nature of the exposed information presents potential downstream threats. Cybersecurity experts warn that such data can be leveraged for targeted phishing attacks, business email compromise (BEC), and social engineering campaigns. Mazda has advised affected individuals to remain vigilant, avoid suspicious communications, and refrain from clicking unknown links or downloading attachments.
The root cause of the incident was traced to unpatched system vulnerabilities, though the company has not disclosed the exact technical exploit involved. Possible attack vectors could include common vulnerabilities such as SQL injection, authentication bypass, or remote code execution. The incident underscores the importance of timely patch management and proactive vulnerability assessments in enterprise IT environments.
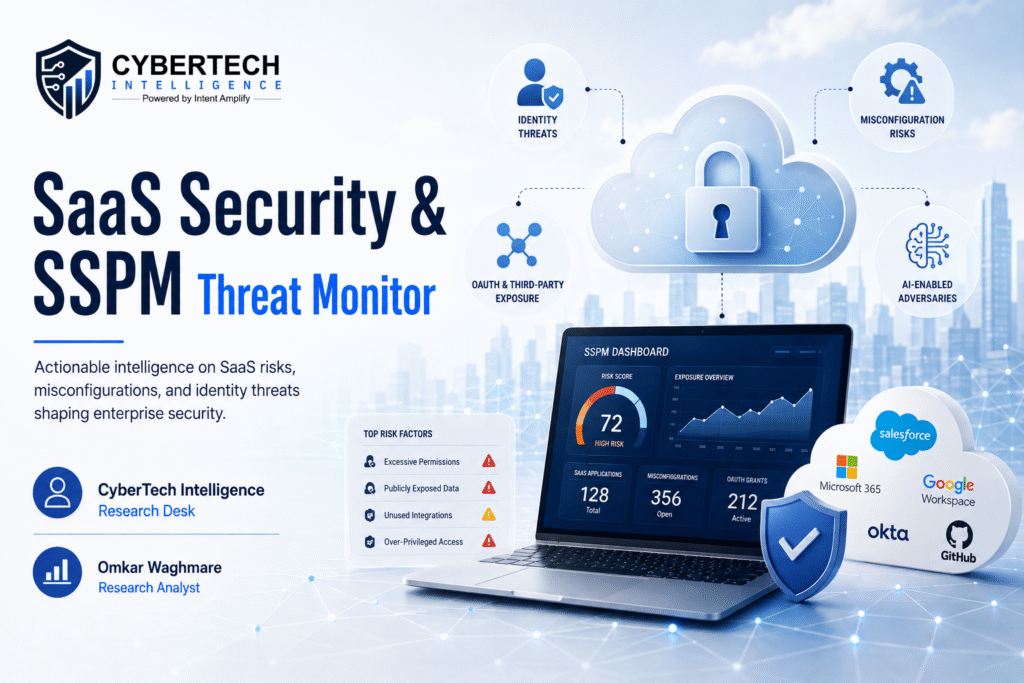
In response, Mazda has implemented a series of remediation measures to strengthen its cybersecurity posture. These include revising system architecture to reduce internet exposure, restricting access through controlled IP ranges, applying pending security patches, and enhancing monitoring systems to detect anomalous activity in real time.
Additionally, the company plans to extend these security enhancements across similar operational systems within its infrastructure to prevent future incidents. While no evidence of further misuse of the compromised data has been reported, Mazda emphasized its commitment to continuous improvement in data protection and risk mitigation.
This incident serves as a reminder that even internal operational systems, such as warehouse management platforms, can become critical attack surfaces in today’s threat landscape. As cyber threats continue to evolve, organizations must prioritize robust security frameworks, continuous monitoring, and rapid incident response strategies to safeguard sensitive business and personnel data.
Recommended Cyber News :
- Most Vendor Assessments Miss Critical Security Risks, According to Info-Tech Research Group
- Glasswall Launches Foresight AI to Predict and Stop File-Based Cyber Threats
- ZipID Launches Revolutionary Platform to Modernize Form I-9 Compliance with Identity Authentication
To participate in our interviews, please write to our CyberTech Media Room at info@intentamplify.com
🔒 Login or Register to continue reading