Endpoint security has moved from a tactical control to a strategic priority.
In modern enterprises, the network perimeter is no longer fixed. Remote work, BYOD policies, SaaS adoption, and distributed infrastructure have dissolved traditional boundaries. What remains constant is this.
Every device is now a potential entry point.
Endpoints are involved in a significant share of cyber incidents, often acting as the initial foothold for attackers before lateral movement across systems.
This makes endpoint security not just a control layer, but a foundational pillar of enterprise cyber resilience.
What is Endpoint Security?
Endpoint security is a cybersecurity approach focused on protecting endpoint devices such as laptops, desktops, mobile devices, servers, and IoT systems from cyber threats.
It combines multiple technologies, policies, and monitoring capabilities to:
- Prevent unauthorized access.
- Detect malicious activity.
- Respond to threats in real time.
- Ensure device compliance across the network.
At its core, endpoint security treats every device as a security boundary that must be continuously validated and protected.
Why Endpoint Security Matters for Enterprises
As the number of connected devices grows, so does the potential attack surface. Endpoint security plays a central role in safeguarding enterprise systems, data, and user access.
1. Endpoints Are the Primary Attack Vector
Attackers increasingly target endpoints because they are easier to exploit than hardened network infrastructure.
- Phishing: compromised user device.
- Malware: endpoint execution.
- Credential theft: endpoint access.
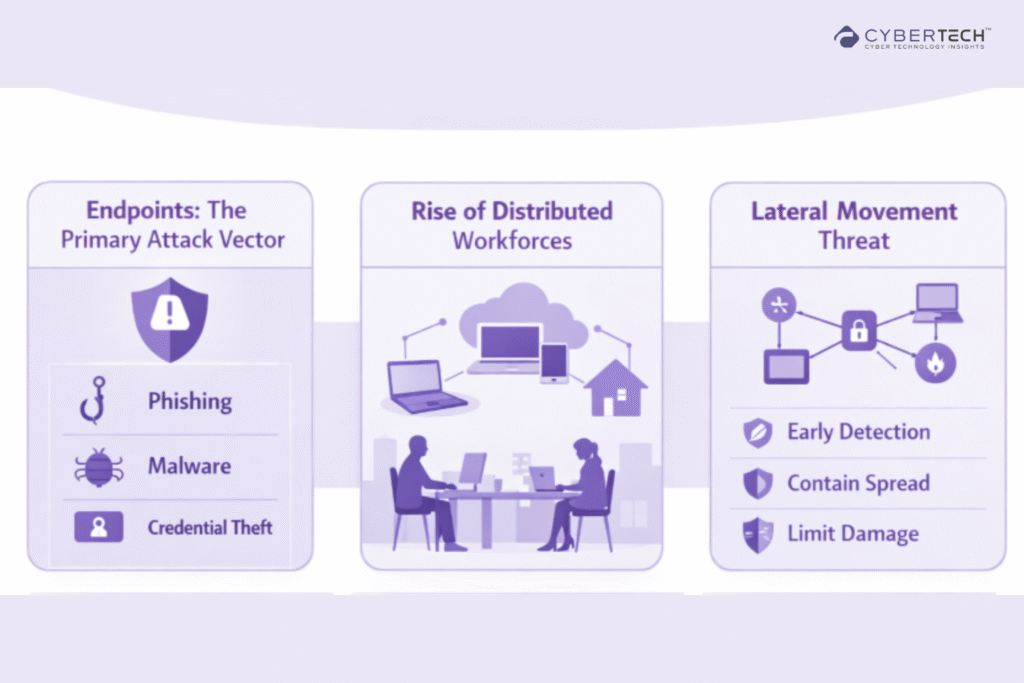
2. The Rise of Distributed Workforces
Hybrid work has multiplied unmanaged and semi-managed devices. Traditional perimeter security no longer applies.
3. Lateral Movement Starts at the Endpoint
Once inside, attackers pivot across systems. Endpoint security is critical to:
- Detect early-stage compromise.
- Contain spread.
- Reduce blast radius.
Core Components of Modern Endpoint Security
Endpoint security today is built on integration, not isolation. Each component plays a specific role in ensuring continuous protection, real-time visibility, and fast incident response.
Endpoint Protection Platform (EPP)
- Signature-based and behavioral detection.
- Malware prevention, firewall and device control.
- First line of defense.
Gartner defines EPP as a solution designed to protect endpoints from known and unknown attacks using multiple detection techniques.
Endpoint Detection and Response (EDR)
- Continuous monitoring of endpoint activity.
- Detects anomalies and advanced threats.
- Enables investigation and remediation.
EDR provides real-time visibility and response capabilities across endpoints.
Extended Detection and Response (XDR)
- Correlates data across endpoints, cloud, email, and network.
- Unified threat visibility.
- Reduces tool fragmentation.
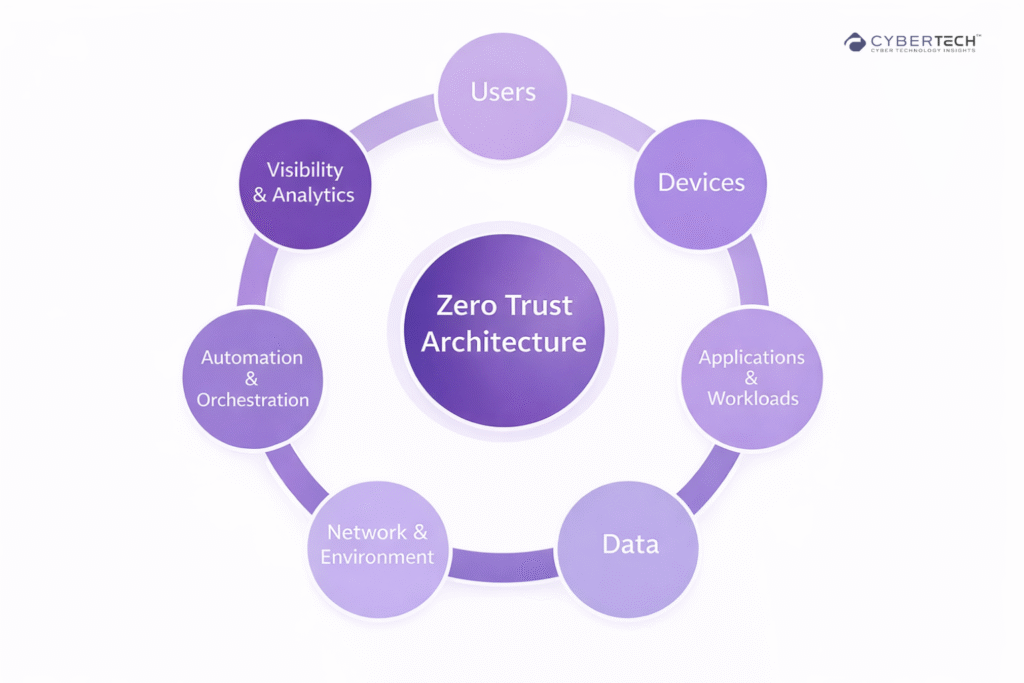
Zero Trust Enforcement
- Continuous device validation.
- Least-privilege access.
- Device posture checks before granting access.
Endpoint Security Architecture (Enterprise View)
A typical enterprise endpoint security architecture includes:
1. Endpoint Agent Layer
- Installed on every device.
- Collects telemetry and enforces policies.
2. Data and Analytics Layer
- Behavioral analysis.
- AI/ML-based threat detection.
3. Control Plane
- Centralized management console.
- Policy orchestration.
4. Response Layer
- Automated containment (isolate device, kill process).
- Incident response workflows.
5. Integration Layer
- SIEM, SOAR, identity systems and cloud security tools.
This architecture reflects a shift from prevention-only models to continuous detection and response systems.
How Endpoint Security Protects Devices (Step-by-Step)
1. Device connects to the enterprise network
The endpoint initiates access to corporate systems, triggering initial identity and device verification checks.
2. Endpoint agent validates device posture
The security agent assesses compliance factors such as patch levels, configurations, and security controls before granting access.
3. Continuous monitoring begins (processes, files, behavior)
The system tracks real-time endpoint activity, analyzing processes, file changes, and behavioral patterns for anomalies.
4. Suspicious activity is flagged using analytics
Advanced analytics and behavioral models identify deviations from normal activity, signaling potential threats.
5. Automated response is triggered:
Isolate device
The compromised endpoint is removed from the network to prevent lateral movement.
Block execution
Malicious files or processes are terminated or prevented from running.
Alert SOC
Security teams are notified with contextual threat intelligence for further investigation.
6. Incident is investigated and remediated
Security teams analyze the incident, remove threats, and restore the endpoint to a secure and compliant state.
This lifecycle ensures threats are stopped before escalation or lateral movement.
Vendor Landscape: Key Endpoint Security Platforms
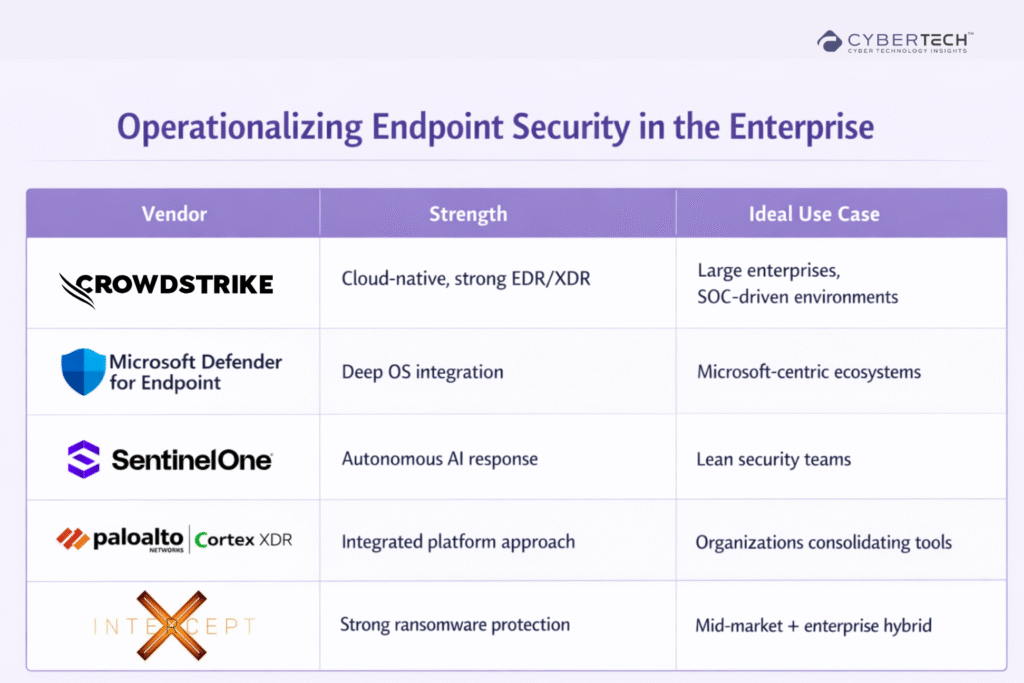
Strategic Takeaways for Buyers
- Platform consolidation is accelerating (EDR to XDR).
- AI-driven detection is now the baseline, not the differentiator.
- Integration with identity and cloud security is critical.
Pricing Insights (Enterprise Reality Check)
Pricing varies, based on:
- EPP vs EDR vs XDR scope.
- Managed services (MDR inclusion).
- Deployment scale.
- Add-ons (threat intel, identity protection).
Enterprise buyers should evaluate the total cost of ownership, not just the license cost:
- Operational overhead.
- Integration costs.
- SOC efficiency gains.
Implementing Endpoint Security at Scale
1. Start with Visibility, Not Just Prevention
Deploy EDR/XDR early to gain telemetry across endpoints.
2. Align with Zero Trust Strategy
Endpoint security should integrate with:
- Identity and access management.
- Device posture enforcement.
- Conditional access policies.
3. Integrate with Existing Security Stack
Ensure compatibility with:
- SIEM
- SOAR
- Cloud security tools
4. Prioritize Automation
Manual response does not scale.
Look for:
- Automated containment.
- Playbook-driven response.
- AI-assisted triage.
5. Segment Endpoints by Risk
Not all endpoints are equal:
- High-value assets (servers, exec devices).
- Standard user devices.
- Unmanaged endpoints.
Apply tiered security policies.
Common Challenges in Endpoint Security
- Alert fatigue from EDR tools.
- Tool sprawl and integration complexity.
- Managing remote and unmanaged devices.
- Balancing security with user experience.
Modern XDR platforms aim to reduce these challenges through centralized visibility and automation.
Endpoint Security in the Broader Cybersecurity Stack
Endpoint security does not operate in isolation. It connects with:
- Identity security
- Network security
- Cloud workload protection
- Threat intelligence platforms
This convergence is driving the shift toward unified security platforms.
Endpoint Security as a Strategic Control Layer
Endpoint security is no longer just about antivirus or device protection.
It is about controlling the first point of entry, detecting threats before escalation, and enabling real-time response at scale.
For enterprise security leaders, the question is no longer whether to invest in endpoint security.
It is how to architect it as part of a broader, integrated security strategy.
FAQs
1. When should a leader stop pushing a strategy and pivot instead?
Leaders should pivot when data consistently contradict assumptions, team alignment drops, and outcomes fail to improve despite repeated effort.
2. How does ego impact leadership decision-making?
Ego can distort judgment, delay course correction, and reduce collaboration. Leaders who prioritize being right over getting it right often weaken trust and decision quality.
3. What are the signs that a business strategy is failing, but leadership is in denial?
Common signs include ignoring negative data, extending timelines without clear justification, over-defending past decisions, and declining team confidence.
4. Why is accepting failure early considered a leadership strength?
Early acceptance accelerates decision-making, conserves resources, and enables faster adaptation. It creates more agile and resilient organizations.
5. How can leaders balance persistence with adaptability?
Effective leaders anchor persistence in purpose, not attachment to a specific plan. They reassess outcomes continuously and adjust direction without losing long-term focus.
To participate in upcoming interviews, please reach out to our CyberTech Media Room at info@intentamplify.com
🔒 Login or Register to continue reading







