In the digital age, protecting sensitive information and data has become crucial for organizations handling sensitive information of users. With technological advancements and sophisticated cyberattacks, Multi-Factor Authentication (MFA) stands at the forefront of cybersecurity strategies. MFA enhances security by requiring users to provide multiple forms of verification before gaining access to systems. MFA is undergoing a revolution facilitated by the use of Artificial Intelligence (AI) and Machine Learning (ML), which makes the method more efficient and approachable. AI systems can increase the precision of biometric authentication, identify fraudulent activity, and modify security protocols in response to real-time risk assessments.
AI’s ability to evaluate enormous amounts of data allows it to improve fraud detection and provide enhanced personalized authentication experiences. In addition to enhancing security, this proactive strategy reduces user annoyance during login.
The integration of AI and MFA presents an enhanced and effective defense against data breaches and unauthorized access as cyber threats evolve. MFA’s future depends on its ability to use AI-driven insights for adaptive security measures and continuous authentication, which will enable businesses to successfully safeguard their digital identities in a threat landscape that is becoming more complicated by the day.
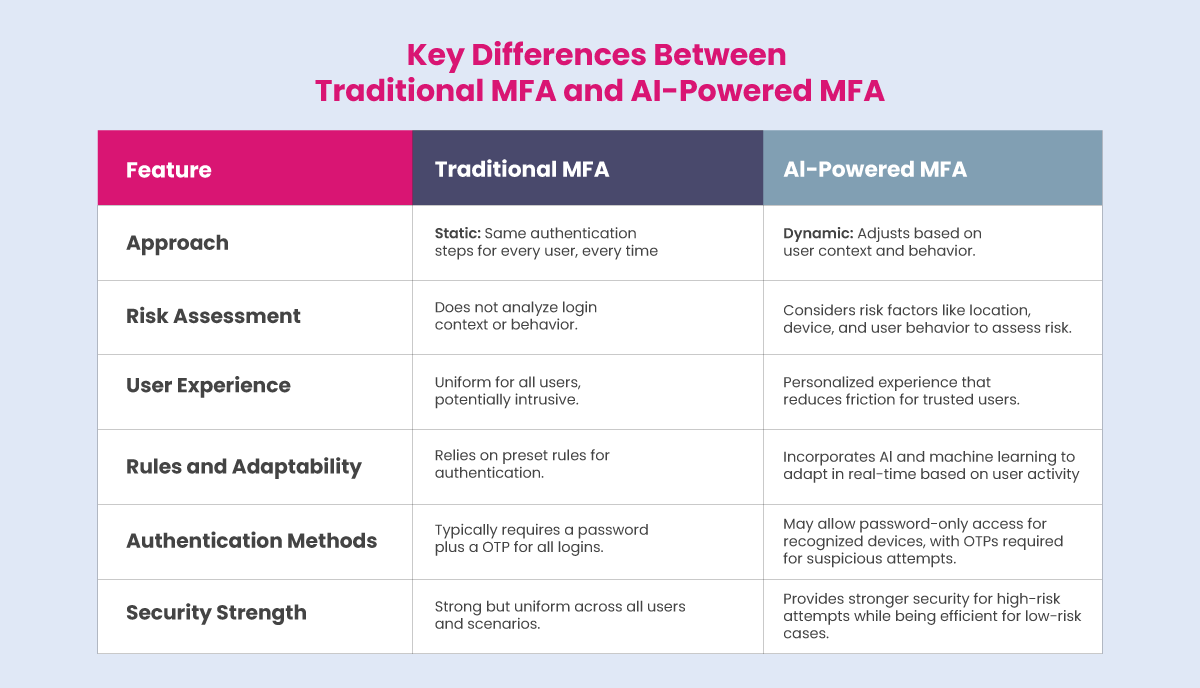
This transformation is characterized by several key advancements, which we highlight below. Additionally, we also highlighted the key differences and additional insights between traditional MFA and AI-powered MFA.
Recommended: Top AI Security Tools for Financial Services Industry
Key Differences and Insights: Traditional MFA Vs. AI-powered MFA
MFA has evolved significantly, with traditional methods being enhanced by AI. Compared to the traditional MFA technology, AI-powered MFA offers a more flexible, secure, and user-friendly approach, which makes it better suited to handle the challenges posed by modern cybersecurity threats.
Here are the key differences between traditional MFA and AI-powered MFA:
- Biometric Enhancements: AI-powered MFA often utilizes cutting-edge biometric authentication techniques, which enhance accuracy and counterfeit resistance by continuously learning from user data patterns.
- Behavioral Biometrics: AI-driven systems can evaluate behavioral biometrics, including typing speed and mouse movements, to generate a unique user profile, which improves security without requiring extra user work, in contrast to conventional approaches that only use static credentials.
- Fraud Detection: Through real-time login attempt analysis and the detection of anomalies that might point to unlawful access—something that standard MFA might overlook—AI improves the ability to detect fraudulent behavior.
- Adaptability to Threats: Unlike traditional methods that might not adapt as swiftly, AI can use global cybersecurity trends to dynamically adjust MFA policies, ensuring that security measures are responsive to evolving threats.
Enhanced Security Features
Compared to traditional MFA approaches, AI-powered MFA offers several types of improved security features that significantly improve the user experience. Moreover, it allows users a much more user-friendly authentication method and enhances the security of their sensitive data.
Here are the key ways in which AI improves the user experience in MFA:
1. Continuous Authentication
AI allows continuous authentication rather than confirming a user’s identity only at the time of login. This approach involves monitoring user actions during the session, including mouse movements and typing speed, to make sure the person remains who they claim they are. This smooth method improves security without interfering with user functionality.
Recommended: Cyber Threat Intelligence: How to Predict and Prevent Cyberattacks?
2. Risk-Based Authentication
The AI system analyzes contextual factors including device, location, and user behavior to determine the risk level of each login attempt. As a result, authentication requirements can be dynamically adjusted to demand higher levels of verification for suspicious activities.
3. Frictionless Authentication
AI-enabled passwordless login systems that leverage biometric data, including fingerprints, facial recognition, or one-time tokens sent to users’ devices. The user experience will be smoother and more intuitive if there are no complicated passwords to remember or several verification procedures to complete.
4. Personalized User Experience
AI-powered MFA systems can generate a customized authentication experience by utilizing ML to adapt to the unique behaviors of each user. This makes the authentication process more user-friendly and less complicated because the system can learn how a particular user interacts with their device and modify security measures accordingly.
5. Anomaly Detection
AI enhances security by proactively detecting potential threats in real time. AI can identify irregularities that could indicate unauthorized access attempts by examining trends and behaviors. While reducing disturbances for authorized users, this feature enables prompt reactions to questionable activities. AI systems offer an extra degree of security by spotting odd patterns that can point to fraudulent activity, including unauthorized access attempts.
All these enhanced security features make AI-powered MFA a reliable, secure system, enhancing the user experience. In addition to enhancing security through adaptive measures, AI-powered MFA significantly enhances the user experience by making the login process less invasive and more straightforward.
Improved User Experience
AI and ML are significantly enhancing the MFA user experience by accelerating the authentication process while maintaining robust security.
Following are the key areas in which AI-powered MFA offers an improved user experience:
- Personalized Authentication: Through personalized AI, the MFA system seamlessly accommodates user-specific actions, minimizing disruptions and ensuring robust security.
- Real-Time Adaptation: AI systems that analyze user behavior in real time can dynamically modify security measures to improve security and usability.
- Risk-Based Authentication: Adaptive security protocols, driven by artificial intelligence, dynamically adjust authentication measures based on assessed login risk. Consequently, access may be granted with reduced verification steps when logins originate from recognized devices and geographic locations, thereby enhancing user convenience.
AI and machine learning are revolutionizing MFA by establishing a balance between better user experience and increased security, resulting in safer and more effective digital transactions.
Recommended: Cybersecurity Simplified: What is Cloud Infrastructure Security?
Advanced Technologies
Integrating AI and ML into MFA revolutionizes cybersecurity by enhancing security measures, streamlining user experiences, and adapting to emerging threats.
The future of AI in MFA is positioned to include developing technologies that will significantly expand its capabilities:
- Biometric Authentication: AI improves the accuracy of biometric systems such as facial recognition and fingerprint scanning by learning from variations in user data, making these systems more resistant to spoofing attacks.
- Predictive Threat Intelligence: Organizations can modify their MFA rules and proactively defend against emerging threats by using AI to forecast potential threats based on global cybersecurity trends.
Challenges and Drawbacks
While AI-powered MFA systems offer significant advantages over traditional MFA, such as enhanced security and user experience, they also come with potential drawbacks and challenges that organizations must consider before implementing in their system.
Here are some of the key challenges associated with AI-powered MFA:
1. Complexity and Usability Issues: AI-powered MFA can introduce complexity into the authentication process. Users may find the additional steps cumbersome, leading to frustration and decreased satisfaction. The learning curve associated with new technologies can hinder user adoption.
2. Cost of Implementation: It can be expensive to implement AI-powered MFA solutions, particularly for small and medium organizations. It can be costly and taxing on limited funds to buy state-of-the-art technology, license software, and integrate with existing systems.
3. Technical Complexity: The deployment and maintenance of AI-powered MFA systems often require specialized knowledge and skills. Organizations lacking expertise in network security or identity management may face challenges in effectively implementing and managing these systems. Additionally, implementing AI solutions requires ensuring compatibility with existing systems, which can be complex and resource-intensive.
4. False Positives and Negatives: AI systems are not ideal; they can generate false positives (incorrectly classifying legitimate users as threats) or false negatives (failing to detect true threats). This can result in user lockouts or overlooked security breaches, weakening confidence in the system.
5. Bias in AI Systems: Depending on the data they are educated on, AI systems may exhibit bias. Certain demographic groups may be disproportionately impacted by this prejudice, which could lead to unfair or discriminatory outcomes in authentication procedures.
Recommended: Cybersecurity Simplified: LLMjacking Attacks
6. Dependency on Devices: AI-powered MFA often relies on devices such as smartphones or security tokens for authentication. If users lose these devices or encounter technical issues, they may be unable to access their accounts, leading to frustration and downtime.
7. Privacy Concerns: Users may be concerned about their privacy if the use of AI in MFA necessitates access to private data, including biometric information. Reluctance to share this information may make it more challenging to comply with MFA regulations. Concerns regarding privacy and regulatory compliance are brought up by the gathering and analysis of user behavior data.
8. Single Points of Failure: AI systems can create single points of failure; if the authentication server experiences downtime or issues in the event of cyberattacks, users may be locked out entirely, causing significant inconvenience.
While AI-powered MFA improves security and the user experience, companies must carefully evaluate these potential downsides before implementing them. Addressing these issues proactively can assist in ensuring a successful deployment that balances security requirements and user happiness.
Conclusion
The way organizations protect their digital assets has changed completely with the integration of AI and ML in MFA. These advanced technologies improve security with personalized authentication experiences and real-time suspicious activity detection by utilizing sophisticated algorithms. The risk of unauthorized access has been significantly reduced by AI-powered adaptive MFA, which evaluates contextual data to dynamically modify security measures based on user behavior. Additionally, removing the requirement for conventional passwords has improved the user experience while lowering the risk of credential theft. As technology advances, the use of AI in MFA will become crucial in building a strong defense against ever-more-sophisticated attacks as cyber threats continue to change, ensuring organizations can successfully safeguard sensitive data.
The landscape of MFA is undergoing a dramatic transformation driven by AI and ML. These technologies raise the bar for cybersecurity by improving the user experience and strengthening security through adaptive measures and ongoing verification. Organizations should anticipate a stronger defense against cyber threats and unauthorized access as they use AI-powered MFA solutions more often. Future developments in these technologies indicate that safe authentication will only become more user-friendly and efficient.
To share your insights, please write to us at news@intentamplify.com
🔒 Login or Register to continue reading